- Password. Authentication Protocol (PAP)
- Challenge. Handshake Authentication Protocol (CHAP)
- Microsoft's. implementation of CHAP (MS-CHAP)
- Updated. version of MS-CHAP (MS-CHAP2)
- Extensible. Authentication Protocol/Transport Layer Security (EAP/TLS)
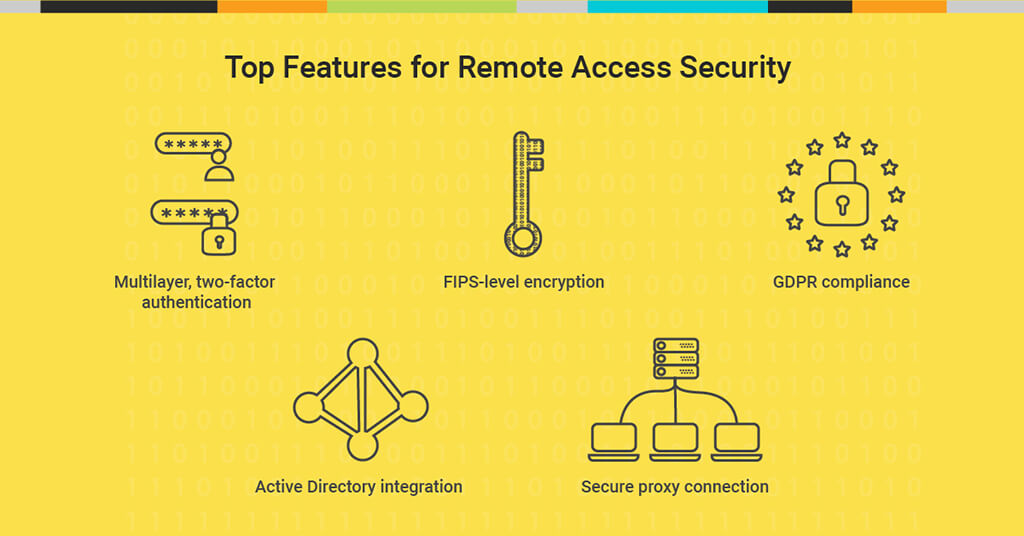
What are the best practices for securing remote access?
Best Practices for Securing Remote Access. RAS: The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network ... IPSec: IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect ...
What authentication methods are supported by OpenWindows remote access servers?
Windows remote access servers support the following set of authentication methods: Extensible Authentication Protocol/Transport Layer Security (EAP/TLS) For security purposes, PAP can be excluded as a viable option for most businesses because it sends passwords across the phone line or Internet in plain text.
What is a remote authentication protocol?
The acronym is actually fairly descriptive of what it does: The worker will remotely authenticate for access to that remote network. I have previously mentioned that I like to map protocols before to the OSI Reference Model. This helps one visualize just what protocols belong where in the grand scheme of things.
What are the different types of remote access authentication?
Remote access authentication options. Remote access servers can be configured as dial-in servers or VPN servers. Dial-in servers use the Point-to-Point Protocol (PPP) or in the case of some older servers, the Serial Line Internet Protocol (SLIP) as the link layer protocol.
Why is authentication important?
What is face authentication?
Why is SMS code so frustrating?
What happens if your authentication process takes too long?
Why are passwords not secure?
What happens if a customer doesn't have security authentication?
Does authentication compromise privacy?
See more
About this website
What is the best remote access authentication?
Extensible Authentication Protocol-Transport Level Security is the most secure remote authentication protocol. It uses certificates on both the client and the server to provide mutual authentication, data integrity, and data confidentiality.
Which method of remote access is the most secure?
Implement a Secure Connection for Remote Network AccessWired Connection: A wired connection is the most secure method for remote network access.Home Wi-Fi: The second most secure network connection is using a secured home Wi-Fi connection.More items...•
What is the strongest method of authentication?
Experts believe that U2F/WebAuthn Security Keys are the most secure method of authentication. Security keys that support biometrics combine the Possession Factor (what you have) with the Inherence Factor (who you are) to create a very secure method of verifying user identities.
What are the 3 authentication methods?
Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.
Who is more secure protocol for remote login?
While Remote Desktop is more secure than remote administration tools such as VNC that do not encrypt the entire session, any time Administrator access to a system is granted remotely there are risks. The following tips will help to secure Remote Desktop access to both desktops and servers that you support.
What are two types of remote access servers?
Remote Access Methods1- Remote Access Server: It's one server in organization network that it is the destination of all remote access connections.2- Remote Access Client: All computers that remote connect to network, called remote access client or remote computer.More items...•
Which two-factor authentication is best?
Duo Mobile The most powerful authentication apps for Android devices have been given to us by Duo Security LLC. Duo Mobile is designed to keep your login safe and secure. It comes with a two-factor authentication service that you may use with any app or website.
What is more secure than MFA?
2FA uses two factors and multi-factor uses more. Multi-factor is becoming more popular today, because it is inherently more secure. It can still be implemented poorly. There are more things to consider, of course, than just security.
What are the five 5 authentication methods?
5 Common Authentication TypesPassword-based authentication. Passwords are the most common methods of authentication. ... Multi-factor authentication. ... Certificate-based authentication. ... Biometric authentication. ... Token-based authentication.
What are the 4 general forms of authentication?
Four-factor authentication (4FA) is the use of four types of identity-confirming credentials, typically categorized as knowledge, possession, inherence and location factors.
What are the most common digital authentication methods?
Biometric authentication. Fingerprints and facial recognition are two popular methods used today. Other methods include hand geometry, retina and iris scans, voice recognition and signature-based analysis.
What is 3 step verification method?
Three-factor authentication (3FA) is the use of identity-confirming credentials from three separate categories of authentication factors – typically, the knowledge, possession and inherence categories. Multifactor authentication dramatically improves security.
What is secure remote access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
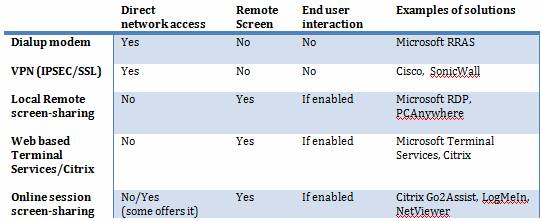
What are the remote access methods?
The primary remote access protocols in use today are the Serial Line Internet Protocol (SLIP), Point-to-Point Protocol (PPP), Point-to-Point Protocol over Ethernet (PPPoE), Point-to-Point Tunneling Protocol (PPTP), Remote Access Services (RAS), and Remote Desktop Protocol (RDP).
What is the technology used in remote access?
virtual private network (VPN) technologyRemote access software is usually accomplished using a virtual private network (VPN) technology. This type of method is more available compared to others since it is a more secure remote access software that connects the user and the enterprise's networks through an internet connection.
Why is remote authentication important?
MFA is important for remote workers for not only preventing unauthorized access, but in improving your organization's overall security posture. This is thanks to one of the great features of MFA: when an attempt is made to get into someone's account from an unauthorized device, the user will get a notification.
What is remote access server?
Remote access servers can be configured as dial-in servers or VPN servers. Dial-in servers use the Point-to-Point Protocol (PPP) or in the case of some older servers, the Serial Line Internet Protocol (SLIP) as the link layer protocol. VPN servers can use the Point-to-Point Tunneling Protocol (PPTP), Layer 2 Tunneling Protocol (L2TP), or IPSec tunnel mode to establish a secure "tunnel" over the Internet. Windows remote access servers support the following set of authentication methods: 1 Password Authentication Protocol (PAP) 2 Challenge Handshake Authentication Protocol (CHAP) 3 Microsoft's implementation of CHAP (MS-CHAP) 4 Updated version of MS-CHAP (MS-CHAP2) 5 Extensible Authentication Protocol/Transport Layer Security (EAP/TLS)
What does authenticator do?
The authenticator also calculates the hash value and compares the client's response with its own calculation. If the values match, the connection is established.
What is EAP TLS?
EAP/TLS provides for use of more secure authentication methods such as smart cards, Kerberos, and digital certificates, which are much more secure than the user name/password authentication methods above. It's defined in RFC 2716.
Why is it important to verify identity?
The ability to verify identity (authentication) is even more important for remote users than for those who are on-site, since without a secure authentication scheme anyone could get into the network and view, copy, change or even destroy important data. The choices you make have implications for ease of administration and security as your network ...
What is the protocol used for dial in VPN?
Dial-in servers use the Point-to-Point Protocol (PPP) or in the case of some older servers, the Serial Line Internet Protocol (SLIP) as the link layer protocol. VPN servers can use the Point-to-Point Tunneling Protocol (PPTP), Layer 2 Tunneling Protocol (L2TP), or IPSec tunnel mode to establish a secure "tunnel" over the Internet. ...
What is a RADIUS authorization?
Authorization refers to granting specific services to users based on their authenticated identity; restrictions can be imposed on certain users. Accounting refers to tracking the use of the network by users and can be done for billing, management, or security purposes. RADIUS is defined in RFCs 2865 and 2866.
Is MS-CHAP v2 secure?
Version 2 adds such features as mutual (two-way) authentication of both client and server, as well as stronger encryption keys. MS-CHAP v2 is more secure than CHAP for Windows systems.
What is the first thing that’s required to ensure smooth remote access via a VPN?
The first thing that’s required to ensure smooth remote access via a VPN is to plan out a comprehensive network security policy.
What is remote access VPN?
The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network (VPDN) due to its early adoption on dial-up internet.
Why is IPSEC used?
This allows IPSec to protect data transmission in a variety of ways. IPSec is used to connect a remote user to an entire network. This gives the user access to all IP based applications. The VPN gateway is located at the perimeter of the network, and the firewall too is setup right at the gateway.
What is IPSEC encryption?
IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect data flows between hosts and security gateways.
Why use two factor authentication for VPN?
Adopting two-factor authentication for remote access through VPN further boosts your network security. Now let’s take a look at why you should choose a particular VPN type as a secure connection methodology instead of the alternatives.
What is the line of defense for remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly.
Why do devices have administrator rights?
To ensure that no unauthorized software is able to install itself, or by a user, and cause a virus, worm, Trojan or malware infection on a device, each device must deny administrator rights to the user of that particular device or all the employees in general. This ensures protection against Distributed Denial of Service (DDoS) attacks.
Why is it important to consider which authentication method suits your use case?
It’s important to consider which authentication method suits your use case, taking security, usability, convenience, reassurance, completion rates, and privacy into consideration.
Why do we need authentication?
It’s most commonly used when logging into an account or authorizing a financial transaction remotely, for example. Ultimately, authentication is needed to restrict and allow access to personal information and accounts. As the demand for remote services grows, and cybercrime increases, so does the demand for secure authentication online.
What is fingerprint authentication?
Fingerprint authentication compares a user’s fingerprint to a stored template to validate a user’s identity. Fingerprints are complex and unique, which makes them impossible to guess. They are also convenient to use on a smartphone or other device that has the capability to read a fingerprint.
What is genuine presence assurance?
Genuine presence assurance: To deliver secure biometric face authentication, you must be able to establish that an online user is the right person, a real person, and that they are authenticating right now. Genuine presence assurance detects digital injected attacks, as well as artifact and imposter attacks.
Why is SMS code so frustrating?
SMS codes can add complexity and additional steps to the authentication process. If customers are using a computer to complete a task online and are asked to find their mobile device to retrieve an SMS code, it can be frustrating and potentially cause the user to drop off and abandon the transaction.
What happens if your authentication process takes too long?
Completion rates: If your authentication process asks the user to follow too many instructions, or if it takes too long, or it needs repeated attempts before it succeeds, there’s a high risk of drop-offs and lost business. This impacts any organization, whether it’s a retailer dealing with abandoned baskets or citizens failing to return to access online government services.
Why are passwords not secure?
In recent years organizations have started to move away from knowledge-based authentication. Passwords are not secure, because they can be shared, guessed or stolen. Passwords also cause user frustration, because they are easily forgotten. This ultimately leads to drop-off and poor completion rates. You can read more about the end of passwords here.
What is an access challenge?
Access-Challenge: where the server sends a challenge and the user must respond.
Why is telecommuting important?
One of the most desired advantages has been for some workers to have the ability to work from home. These telecommuters are one of the recent changes that have affected the workforce and much to the benefit of the worker. The ability to telecommute has greatly affected employee morale for the better. The problem is that these workers must also be able to communicate with the corporate network both remotely and securely. It is of little surprise that these concerns have been addressed in a variety of ways that all work quite well.
What port does XTACACS use?
This protocol is also an application layer protocol and observes the client/server model. Since TACACS+ is also a well known protocol, it stands to reason that there is also a well known port associated with this activity, which is TCP Port 49. That being said, XTACACS uses UDP. There is always the exception to the rule!
Can you use PPP on a Radius router?
Notably, you can use PPP, PAP, and CHAP to name most of them. If you are familiar with Cisco Systems gear or are in charge of supporting the routers and switches from them, then you are no doubt familiar with the various authentication methods offered by RADIUS.
Does RADIUS use UDP?
Based on the above access controls, the user is either authenticated or rejected. RADIUS itself, as mentioned earlier, uses UDP as its transport protocol, which was decided during the initial design considerations for RADIUS. Using UDP has its advantages, notably there being less overhead and speed.
Author: Haris Khan
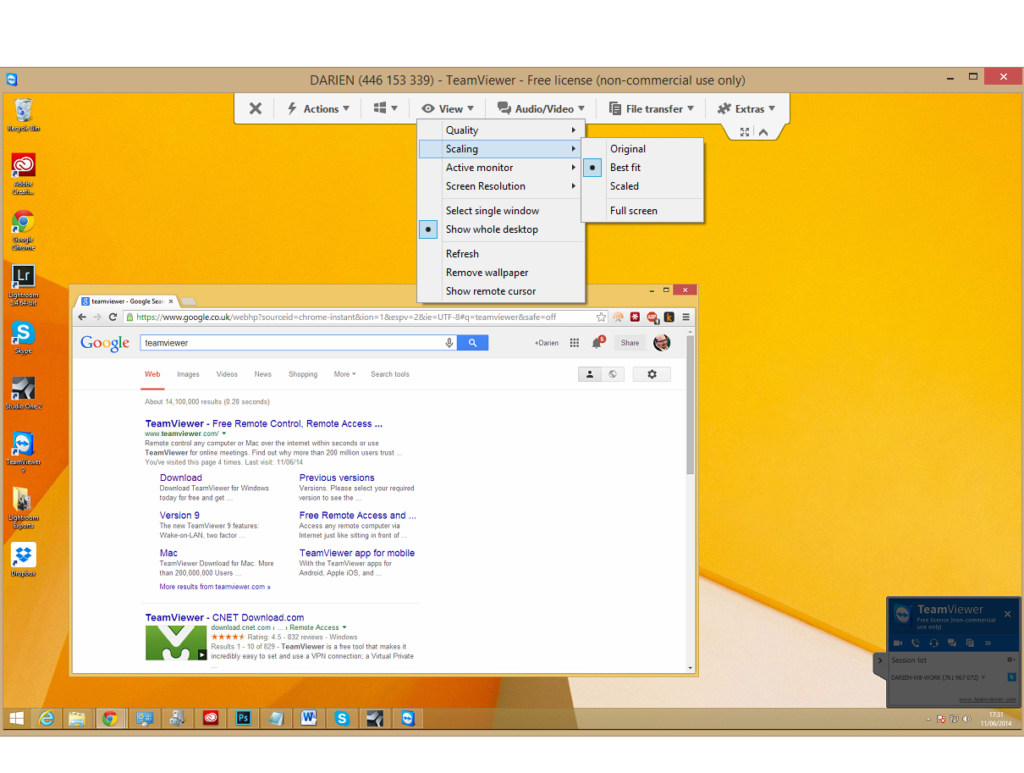
Remote work is the new normal for IT teams around the globe, and there is no surprise as to why remote work is becoming so increasingly popular for organizations. The modern employee workforce is no longer restricted to one physical location.
What is secure remote access?
Secure remote access refers to the technology used for securely accessing a system or application remotely. Cybercriminals and malicious actors are consistently looking out for vulnerabilities and loopholes in remote work infrastructures to exploit and plan cyber attacks.
Which technologies are used for remote work access?
Secure remote access can be effectively implemented by utilizing a collection of highly innovative, secure, and flexible technologies while accessing a system or application from a remote location A few prominent examples of such technologies are listed below:
10 Best Practices for Secure Remote Work Access
Some of the best practices that you can adopt to improvise remote access security in your organization are described below:
Why cloud desktops are an optimal choice for secure remote access?
Cloud desktop solutions offer greater flexibility and ease of access as all of your files, applications and desktop reside on the cloud. Cloud desktops are one of the most resilient and secure forms of remote access.
All-In-One Secure Remote Access with V2 Cloud
As the organizational trend keeps transitioning to remote work, it’s crucial to comprehend the numerous cybersecurity risks and threats that are associated with remote access security. Remote work has become an increasingly viable option with tons of advantages.
What is biometric authentication?
Common biometric authentication methods include fingerprint identification, voice recognition, retinal and iris scans, and face scanning and recognition.
What is a token for a hacker?
Common forms include a dongle, card, or RFID chip. A token makes it more difficult for a hacker to access an account since they must have long credentials and the tangible device itself, which is much harder for a hacker to obtain. Advantage: Similar to a biometric, a token is difficult to fake. The specific digital identity ...
Can biometrics be used to authenticate?
The use of biometrics to authenticate you as an authorized user. It’s commonly accepted that conventional authentication protocols and password protection are too weak, with today’s hackers easily using sophisticated tools that can hack passwords and get into your system and the data stored on it.
Is OOB easy to implement?
Advantage: Just like MFA, OOB is common and low-cost to implement. As one of the most popular methods of authentication for anything from email accounts to online banking, OOB is relatively easy to roll out with staff members.
Can you use more complex passwords?
So, while you could simply try to use more complex passwords (and likely forget them), there’s a better way to protect your network — add a secondary authentication method.
Is a set it and forget it authentication method dependent on the user?
That means it has a “set it and forget it” quality when compared to other methods that put the onus on the user.
Can hackers hack passwords?
It’s commonly accepted that conventional authentication protocols and password protection are too weak, with today’s hackers easily using sophisticated tools that can hack passwords and get into your system and the data stored on it.
Why is authentication important?
Ultimately, authentication is needed to restrict and allow access to personal information and accounts.
What is face authentication?
Facial authentication uses a face scan done by a human on any device with a front-facing camera to prove they are who they say they are. For face authentication to be secure, it needs to verify that the user is the right person, a real person, and that they are authenticating right now. This is what iProov’s Genuine Presence Assurance technology delivers.
Why is SMS code so frustrating?
SMS codes can add complexity and additional steps to the authentication process. If customers are using a computer to complete a task online and are asked to find their mobile device to retrieve an SMS code, it can be frustrating and potentially cause the user to drop off and abandon the transaction.
What happens if your authentication process takes too long?
Completion rates: If your authentication process asks the user to follow too many instructions, or if it takes too long, or it needs repeated attempts before it succeeds, there’s a high risk of drop-offs and lost business. This impacts any organization, whether it’s a retailer dealing with abandoned baskets or citizens failing to return to access online government services.
Why are passwords not secure?
In recent years organizations have started to move away from knowledge-based authentication. Passwords are not secure, because they can be shared, guessed or stolen. Passwords also cause user frustration, because they are easily forgotten. This ultimately leads to drop-off and poor completion rates.
What happens if a customer doesn't have security authentication?
If a customer is making a large payment and doesn’t experience any sort of security authentication, they may be unnerved, which could cause them to distrust your company.
Does authentication compromise privacy?
Privacy: The authentication method should not compromise a user’s privacy. For instance, a commuter on a train wanting to complete a transaction on their mobile device may not appreciate needing to speak out loud with voice recognition.