- OSSEC.
- Zeek.
- Suricata.
- Sagan.
- Security Onion.
- AIDE.
- Fail2Ban.
- Samhain.
Which is the Best Antivirus for remote access trojan detection?
Remote Access Trojan Detection 1 Avast 2 AVG 3 Avira 4 Bitdefender 5 Kaspersky 6 Malwarebytes 7 McAfee 8 Microsoft Windows Defender 9 Norton 10 PC Matic 11 Sophos 12 Trend Micro More ...
What is the best Trojan removal tool?
5 Best Trojan Removal Tools. #1: MalwareFox. MalwareFox is a complete anti-malware solution. It is always ready for modern malware attacks. It combines the best malware detection, ... #2: Spybot – Search & Destroy. #3: SUPERAntiSpyware. #4: Malwarebytes. #5: Emsisoft Emergency Kit.
What are some examples of remote access trojan?
Remote Access Trojan Examples 1 Back Orifice. Back Orifice (BO) rootkit is one of the best-known examples of a RAT. ... 2 Sakula. Sakula, also known as Sakurel and VIPER, is another remote access trojan that first surfaced in November 2012. 3 Sub7. Sub7, also known as SubSeven or Sub7Server, is a RAT botnet. ... 4 PoisonIvy. ... 5 DarkComet. ...
How do I check if a trojan is installed on my computer?
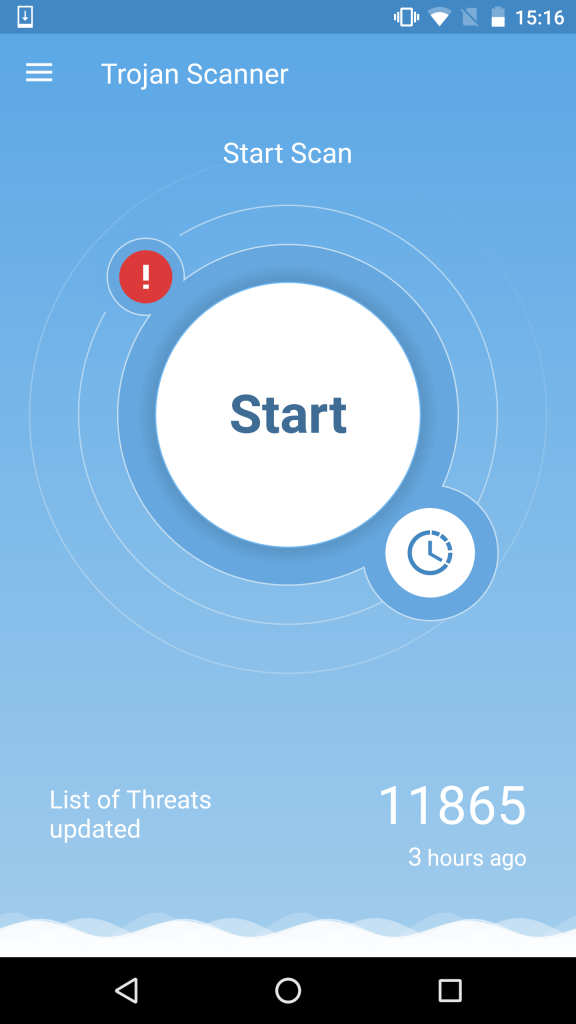
Click the “Scan” button and the Trojan scanner quickly checks your device. Download and install the Malwarebytes’ free Trojan scanner software. Click the “Scan” button and the Trojan scanner quickly checks your device.
What is intrusion detection?
Can antivirus be used to get rid of a RAT?
Can a Remote Access Trojan be installed to BIOS?

What is the best remote access Trojan?
10 Best Remote Access Software (Remote Control Software) In 2022Comparison of Top Remote Access Tools.#1) NinjaOne (Formerly NinjaRMM)#2) SolarWinds Dameware Remote Support.#3) Atera.#4) Supremo.#5) ManageEngine Remote Access Plus.#6) RemotePC.#7) TeamViewer.More items...•
What are the variant of remote access Trojan?
There are a large number of Remote Access Trojans. Some are more well-known than others. SubSeven, Back Orifice, ProRat, Turkojan, and Poison-Ivy are established programs. Others, such as CyberGate, DarkComet, Optix, Shark, and VorteX Rat have a smaller distribution and utilization.
Is remote access Trojan a malware?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Can Norton detect RATs?
Antivirus software like Bitdefender, Kaspersky, Webroot, or Norton, can detect RATs and other types of malware if they infect your devices.
Is remote access Trojan illegal?
Law enforcement officials say that simply possessing a remote-access tool isn't illegal. In fact, remote-access tools are often used for IT support purposes in corporate environments.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
Can Kaspersky detect remote access Trojan?
Put a good antivirus on your smartphone. For example, Kaspersky Internet Security for Android not only finds and removes Trojans, but also blocks websites with malware and mobile subscriptions.
Is TeamViewer a RAT?
The JS script then launches the malware, which installs a version of TeamViewer, a remote administration tool (RAT), modified by the attackers. As in earlier attacks, the attackers use a malicious DLL library to hide the graphical user interface in order to control the infected system without the user's knowledge.
Is someone using my computer remotely?
Open your Task Manager or Activity Monitor. These utilities can help you determine what is currently running on your computer. Windows – Press Ctrl + Shift + Esc. Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
Can Norton remove a Trojan?
Resolution. Norton Antivirus detects and removes Trojan horses. Via LiveUpdate, administrators can download to a computer the latest virus definitions, which contain information that the scan engine needs to find existing and emerging threats on a system.
Can antivirus detect Trojan?
An effective antivirus program searches for valid trust and app behavior, as well as trojan signatures in files in order to detect, isolate and then promptly remove them.
Can Trojan hide from antivirus?
Rootkit technologies – that are generally employed by Trojan viruses – can intercept and substitute system functions, in order to make the infected file invisible to the operating system and antivirus programs. Sometimes even the registry branches – where the Trojan is registered – and other system files are hidden.
What are the main features of a remote access Trojan?
RAT (remote access Trojan)Monitoring user behavior through keyloggers or other spyware.Accessing confidential information, such as credit card and social security numbers.Activating a system's webcam and recording video.Taking screenshots.Distributing viruses and other malware.Formatting drives.More items...
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
Are PUPs malware?
Type and source of infection. Detections categorized as PUPs are not considered as malicious as other forms of malware, and may even be regarded by some as useful. Malwarebytes detects potentially unwanted programs for several reasons, including: They may have been installed without the user's consent.
What types of ports do successful Trojan programs commonly use?
What types of ports do successful Trojan programs commonly use? A good software or hardware firewall would most likely identify traffic that's using unfamiliar ports, but Trojan programs that use common ports, such as TCP port 80 (HTTP) or UDP port 53 (DNS), are more difficult to detect.
Can a Remote Access Trojan be installed to BIOS?
Access to the BIOS has been known to the world’s hackers since 2015. Many believe that the NSA was planting RATs and trackers on BIOS even earlier.
How is a Remote Access Trojan RAT different from a regular Trojan horse?
A Trojan is a virus that gets onto a victim computer by passing itself off as a legitimate piece of software. A RAT is a Trojan that the hacker can...
What is the Sakula Remote Access Trojan RAT?
Sakula is a RAT that is used to intrude on IT systems serving government departments and agencies, healthcare facilities, and other large organizat...
What is a Trojan?
Even in 2021, Trojans are still using deception and social engineering to trick unsuspecting users into running seemingly benign computer programs...
Do you need anti-Trojan software?
If you’re wondering how to get rid of a Trojan, it’s highly recommended you use anti-Trojan software to protect your devices. It’s far easier to pr...
Are Trojans considered viruses?
You might assume a Trojan is a type of virus or a worm, but it’s really neither. It’s actually a delivery mechanism for infecting your device with...
How do Trojans spread?
Trojans can infect your computer in any number of ways: they can look like free software and music to browser ads to seemingly legitimate apps. How...
Top five remote access trojans - Infosec Resources
Sources. October 2018’s Most Wanted Malware: For The First Time, Remote Access Trojan Reaches Top 10 Threats, Check Point; FlawedAmmyy Malware Information, Trend Micro; QuasarRAT, GitHub; androrat, GitHub; RATs Come to Android: It’s Scary, But You’re (Probably) Safe, PC Magazine
[Tutorial] What’s Remote Access Trojan & How to Detect/Remove It?
Remote Access Trojan Examples. Since spam RAT comes into being, there have existing lots of types of it.. 1. Back Orifice. Back Orifice (BO) rootkit is one of the best-known examples of a RAT. It was made by a hacker group named the Cult of the Dead Cow (cDc) to show the security deficiencies of Microsoft’s Windows 9X series of operating systems (OS).
What is remote access trojan?
Like most other forms of malware, Remote Access Trojans are often attached to files appearing to be legitimate, like emails or software bundles. However, what makes Remote Access Trojans particularly insidious is they can often mimic above-board remote access programs.
What happens if you install remote access Trojans?
If hackers manage to install Remote Access Trojans in important infrastructural areas—such as power stations, traffic control systems, or telephone networks—they can wreak havoc across neighborhoods, cities, and even entire nations.
How does Snort intrusion detection work?
The intrusion detection mode operates by applying threat intelligence policies to the data it collects, and Snort has predefined rules available on their website, where you can also download policies generated by the Snort user community. You can also create your own policies or tweak the ones Snort provides. These include both anomaly- and signature-based policies, making the application’s scope fairly broad and inclusive. Snort’s base policies can flag several potential security threats, including OS fingerprinting, SMB probes, and stealth port scanning.
What is the best way to detect malware?
The best option, especially for larger organizations, is to employ an intrusion detection system, which can be host-based or network-based. Host-based intrusion detection systems (HIDSs), which are installed on a specific device, monitor log files and application data for signs of malicious activity; network-based intrusion detection systems (NIDSs), on the other hand, track network traffic in real time, on the lookout for suspicious behavior. When used together, HIDSs and NIDSs create a security information and event management (SIEM) system. SIEM is an incredibly beneficial part of a strong security regimen and can help to block software intrusions which have slipped past firewalls, antivirus software, and other security countermeasures.
How do remote access Trojans evade live data analysis?
One way in which Remote Access Trojans can evade the live data analysis NIDSs provide is by dividing the command messaging sent through the malware across multiple data packets. NIDSs like Zeek, which focus more on application layers, are better able to detect split command messaging by running analyses across multiple data packets. This is one advantage Zeek has over Snort.
What is APT in computer security?
The practice of stealthy, ongoing hacking seeking to accumulate data over time, as opposed to causing damage to information or systems, is known as an advanced persistent threat (APT ). Remote Access Trojans are a powerful tool in this type of attack, because they do not slow down a computer’s performance or automatically begin deleting files once installed—and because they’re so adaptable.
Can a Trojan use a keylogger?
A Remote Access Trojan paired with a keylogger, for instance, can easily acquire login information for bank and credit card accounts. Used together, these approaches can discreetly turn on a computer’s camera or microphone, or access sensitive photos and documents. They can even use your home network as a sort of proxy server, through which a hacker can commit crimes anonymously and, for the most part, with impunity.
How to clean up a Trojan infection?
The best way to clean up a Trojan infection is using a security protection solution like Malwarebytes’ free trojan scanner. Malwarebytes will initiate a scan for Trojans and then remove Trojans so they can’t cause further damage.
What happens when you give a Trojan remover an ok?
When you give the ok, the Trojan remover will clean up threats so your device, files, and privacy are secure. When you give the ok, the Trojan remover will clean up threats so your device, files, and privacy are secure.
What is the difference between Malwarebytes and Trojan?
There is a difference, though, between the free Trojan scanner our Malwarebytes Premium solution. The free Trojan scanner removes existing Trojans whereas Malwarebytes Premium proactively scans your device for Trojans to prevent them from doing harm.
What happens after malwarebytes scan?
After the scan, Malwarebytes reports on any threats that were found and asks if you want to remove them . After the scan, Malwarebytes reports on any threats that were found and asks if you want to remove them. When you give the ok, the Trojan remover will clean up threats so your device, files, and privacy are secure.
What are the threats of Trojans in 2021?
Trojans can download code or software that looks legitimate but, in reality, it will take control of your device and install malicious threats including malware, ransomware, and spyware.
What is a Trojan 2021?
What is a Trojan? Even in 2021, Troj ans are still using deception and social engineering to trick unsuspecting users into running seemingly benign computer programs that hide malevolent ulterior motives.
Can a Trojan download malware?
Trojans can download code or software that looks legitimate but, in reality, it will take control of your device and install malicious threats including malware, ransomware, and spyware. Trojans aren’t limited to Windows laptops and desktop computers; they can also impact Macs and mobile devices.
What is a Trojan Virus?
A Trojan virus is a type of malicious software that aims to mislead the users. It is also known as Trojan Horse or simply, Trojan. This word comes from the wooden horse which deceptively led to the fall of the city of Troy.
Why are Trojans so important?
Then, it can allow hackers to take full control of your computer. Additionally, Trojans may collect system information to uncover vulnerabilities. The data collected is used to develop ransomware, viruses, and other malicious software. Trojan viruses are virtually undetectable in most systems.
What is the first threat that will try to penetrate your operating system?
Trojan viruses are the first threat that will try to penetrate your operating system. It relies on the ability to fool you from installing it on your system. Some legitimate applications may even come bundled with Trojan Horse. Toolbars and other add-ons may also occur with potent versions of Trojan viruses .
How does a Trojan horse affect your computer?
Trojan Horses increases your system’s vulnerability a hundredfold. It can create wider backdoors and security holes. More menacing applications such as viruses, ransomware, and rootkits. Protecting your computer from Trojan viruses should be one of the first layers of protection.
What is super antispyware?
SUPERAntiSpyware presents various options to the user. Just like Spybot, it is also an industry veteran. It aims to give you control for effective spyware, adware, trojan and other malware detection and removal. Its installation is quite fast and easy.
Is a Trojan virus undetectable?
Trojan viruses are virtually undetectable in most systems. That is why it is crucial to install anti-malware tools for protection.
Does Malwarefox protect against ransomware?
Its Ransomware protection from ever infiltrating your system. Unlike other malicious applications, there’s no turning back when ransomware gets a hold of your order. MalwareFox’s Zero-Day Attack protection ensures that your system is protected even from unknown new threats. Get MalwareFox.
What Does A Remote Access Trojan Do?
Malware developers use Remote Access Trojan (RAT) tools to gain full access and control over a user’s computer, including mouse and keyboard control, file access, and network resources.
How Is A Remote Access Trojan Executed?
An attacker uses a Trojan to execute a program file on a system. Once the user attempts to open the file, the Trojan is executed, and some dangerous actions are taken. A remote access Trojan program uses a backdoor to control the target machine with administrative privileges.
How Do I Scan My Computer For Trojans?
You can remove malicious software from Microsoft Windows by downloading and running the program…
Can You Get A Virus From Remote Access?
Viruses and malware are not always detected by remote access software solutions. The hacker could easily install malware on your business’s servers and spread to all machines in your office if your home or work PC has been infected and you are using it remotely to access your office network.
How Do I Remove Trojans From My Computer?
The best way to remove trojans is to install and use a reputable antivirus program. In order to detect, isolate and remove trojan signatures, effective antivirus programs search for valid trust and app behavior as well as trojan signatures in files.
Can Windows Defender Remove Trojans?
Microsoft Defender, which was first introduced with Windows XP, is a free antimalware program that protects Windows users from viruses, malware, and other harmful programs. Windows 10 users can use it to detect and remove Trojan horses.
What Is An Example Of A Trojan Virus?
A number of trojans are known to be malicious in government, including the Swiss MiniPanzer and MegaPanzer, as well as the German “state trojan” nicknamed R2D2. Governmentware in Germany exploits security gaps that are unknown to the general public and accesses smartphone data before it is encrypted.
Why are remote access Trojans important?
Remote Access Trojans fulfill an important function for hackers. Most attack vectors, like phishing, are ideal for delivering a payload to a machine but don’t provide the hacker with the ability to explore and interact with the target environment. RATs are designed to create a foothold on the target machine that provides the hacker with the necessary level of control over their target machine.
What is ICS malware?
Malware targeting industrial control systems (ICS) is nothing new, with big names like Stuxnet and Industroyer designed to cause physical damage. However, some ICS-focused malware is targeted at controlling critical infrastructure.
Do remote access Trojans exist?
Many different Remote Access Trojans exist, and some hackers will modify existing ones or develop their own to be better suited to their preferences. Different RATs are also designed for different purposes, especially with RATs geared specifically to each potential target (desktop versus mobile, Windows versus Apple and so on).
How to protect yourself from remote access trojans?
Just like protecting yourself from other network malware threats, for remote access trojan protection, in general, you need to avoid downloading unknown items; keep antimalware and firewall up to date, change your usernames and passwords regularly; (for administrative perspective) block unused ports, turn off unused services, and monitor outgoing traffic.
What is a RAT trojan?
RAT trojan is typically installed on a computer without its owner’s knowledge and often as a trojan horse or payload. For example, it is usually downloaded invisibly with an email attachment, torrent files, weblinks, or a user-desired program like a game. While targeted attacks by a motivated attacker may deceive desired targets into installing RAT ...
Why do RATs use a randomized filename?
It is kind of difficult. RATs are covert by nature and may make use of a randomized filename or file path structure to try to prevent identification of itself. Commonly, a RAT worm virus does not show up in the lists of running programs or tasks and its actions are similar to those of legal programs.
How to check if my computer is safe?
Open the command prompt better as administrator, type “ system.ini ”, and press Enter. Then, a notepad will pop up showing you a few details of your system. Take a look at the drivers section, if it looks brief as what the below picture shows, you are safe. if there are some other odd characters, there may be some remote devices accessing your system via some of your network ports.
Can a RAT remote access trojan be used on a computer?
Since RAT remote access trojan will probably utilize the legitimate apps on your computer, you’d better upgrade those apps to their latest versions. Those programs include your browsers, chat apps, games, email servers, video/audio/photo/screenshot tools, work applications…
What is the best remote desktop software?
RemotePC is the best remote desktop software right now. RemotePC is another stellar product from the team at iDrive (we also recommend its excellent cloud storage solution). RemotePC uses top-notch cloud tech to deliver class-leading remote access. Web, desktop, and mobile apps provide the access.
What is remote PC?
RemotePC is a hugely-popular remote computer access application that’s suitable for both home and—in particular—for business users. It uses cloud technology to deliver class-leading remote access solutions through an intuitive web application and native desktop and mobile apps. It also includes collaboration features such as voice chat.
What is remote desktop manager?
Remote Desktop Manager is a powerful remote computer access program offering scalable solutions for large businesses. It’s compatible with both Android and iOS devices and comes with a selection of impressive security features.
How long does it take to set up a remote access?
Using remote access software is simple. They generally take no more than a few minutes to set up, and you will usually have to install the software on the computer or other device you want to access the remote computer with.
Is Chrome Remote Desktop free?
Chrome Remote Desktop is a free remote access program that’s available on Windows, Mac, Linux, iOS, and Android devices . It's extremely limited when compared to some of the paid options on this list, but it’s the best free software we’ve come across and is a great option for personal use.
Is remote desktop software better than third party software?
Some versions of Windows come with built-in remote desktop software, but third-party tools often perform much better and come with significantly more features. This could be especially important if you’re planning on using the software regularly. There are a few other popular uses for the best remote desktop software.
Is Logmein Pro good for remote desktop?
LogMeIn Pro is one of the most popular remote desktop access programs available, and it’s a great choice for large businesses. It is a little expensive, but it comes with a great range of tools designed for enterprise users.
How to protect your privacy on a computer?
There are many other ways security software can protect your computer and your privacy. Backup is, in a way, the ultimate security for your important files. Even if a piece of space junk smashes your computer to smithereens, you still have your backed-up files. Cleaning up exposed data on your system, stuff that could reveal your habits, is another way to protect privacy. Password management helps you attain the goal of using a strong, unique password for every website. Most security companies offer a higher-level suite that adds many more security-related features. We call these feature-packed products mega-suites, to distinguish them from the basic, entry-level suites.
Why do we use antivirus?
Because viruses were first, we still use the name antivirus for software that protects against all kinds of malware. A virus spreads when someone launches the infected program; a worm spreads without any help. Worms have been around longer than the internet, with the first one, Creeper, hitting Arpanet in 1971.
Does McAfee Total Protection have a VPN?
McAfee Total Protection offers security and password management for all your devices. The no-limits VPN is an enticing extra, and identity monitoring is icing on the cake.
Is there an end to the cat and mouse game between malware coders and antivirus researchers?
But is there an end to the cat-and-mouse game between malware coders and antivirus researchers? Yes, quite possibly there is. The very definition of malware is software that performs some type of malicious action. Behavior-based detection systems don't check programs against a list of known offenders. Instead, they watch all unknown programs for malicious behaviors. This kind of detection works against any malware attack, even a brand-new zero-day exploit.
What is intrusion detection?
Intrusion detection systems are important tools for blocking software intrusion that can evade detection by antivirus software and firewall utilities. The SolarWinds Security Event Manager is a Host-based Intrusion Detection System. However, there is a section of the tool that works as a Network-based Intrusion Detection System. This is the Snort Log Analyzer. You can read more about Snort below, however, you should know here that it is a widely used packet sniffer. By employing Snort as a data collector to feed into the Snort Log Analyzer, you get both real-time and historic data analysis out of the Security Event Manager.
Can antivirus be used to get rid of a RAT?
Antivirus systems don’t do very well against RATs. Often the infection of a computer or network goes undetected for years. The obfuscation methods used by parallel programs to cloak the RAT procedures make them very difficult to spot. Persistence modules that use rootkit techniques mean that RATs are very difficult to get rid of. Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system.
Can a Remote Access Trojan be installed to BIOS?
Access to the BIOS has been known to the world’s hackers since 2015. Many believe that the NSA was planting RATs and trackers on BIOS even earlier.
