Can people see what you're doing on Remote Desktop?
Again as with RDP, no one will actually see you working on the files or see them open, however once your have save them to the correct location using VPN, only those who have the correct security permissions will have access to your files.
Is giving remote access safe?
Remote access solutions could leave you vulnerable. If you don't have proper security solutions in place, remote connections could act as a gateway for cybercriminals to access your devices and data. Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular.
What does allow remote access do?
When you allow remote connections to your PC, you can use another device to connect to your PC and have access to all of your apps, files, and network resources as if you were sitting at your desk.
How do I stop remote access to my computer?
How to Disable Remote Access in Windows 10Type “remote settings” into the Cortana search box. Select “Allow remote access to your computer”. ... Check “Don't Allow Remote Connections” to this Computer. You've now disabled remote access to your computer.
How do I know if someone is accessing my computer remotely?
You can try any of these for confirmation.Way 1: Disconnect Your Computer From the Internet.Way 2. ... Way 3: Check Your Browser History on The Computer.Way 4: Check Recently Modified Files.Way 5: Check Your computer's Login Events.Way 6: Use the Task Manager to Detect Remote Access.Way 7: Check Your Firewall Settings.More items...•
Does Remote Desktop show screen on host?
From the remote computer, the user is prompted to enter the IP address of the host. Then, the user is prompted to enter the login credentials of the host. At this point, the remote screen displays information from the host computer, allowing the user to interact with it like normal, even if the computer is miles away.
What is a remote access device?
Remote access (or remote desktop) is the ability to access a computer or device from another device, at any time, and from anywhere.
What does IT mean when you call someone and IT says please enter your remote access code?
What is a remote access code? It is a code or a password that a user enters to gain access to a private network or server. It is a form of authentication that either permits or blocks an access attempt from entering a corporate system.
Is Microsoft Remote Assistance safe?
Yes, the tool is safe.
Is HP Remote access safe?
Remote access from HP is legitimate ie if you are sure you had called in to HP support and an agent there had taken control by having you log in to hp.com/123. Normally if any drivers or devices are uninstalled or reinstalled a system reboot would be required so I do not see anything wrong in that.
What are some security risk associated with remote assistance?
Many remote access security risks abound, but below is a list of the ones that jump out.Lack of information. ... Password sharing. ... Software. ... Personal devices. ... Patching. ... Vulnerable backups. ... Device hygiene. ... Phishing attacks.
How secure is RemotePC?
Yes, RemotePC by IDrive is considered secure. Communications between remote and local computers are protected with industry-standard TLS version 1.2 and AES-256 encryption. RemotePC also utilizes personal keys as a secondary password to access each computer and two-step verification with a time-based OTP authenticator.
What is remote computer access?
Many people take their laptops with them to do things like finish a business presentation while waiting for a flight at the airport. But a lot of those laptops may not have bigger, important files on them. You might leave those files at work or at home on your desktop computer.
How does TeamViewer work?
Here’s how it works. You’ll need to create an account, and then download and install TeamViewer software onto both your home computer and your remote computer or device. TeamViewer can be installed on Windows, Mac OS, Linux, and Chrome OS. It also has apps for Windows Phone, Blackberry, iOS, and Android. LogMeIn.
What is UltraVNC on Linux?
UltraVNC or TightVNC (available on Linux). These are screen-sharing clients that enable you to connect from a Windows computer to a Mac computer
How to protect remote desktop from hackers?
Use a secure Virtual Private Network (VPN). If you set up a VPN, your remote desktop server won’t be connected directly to the internet. It will only be exposed on your local network, which could leave it less vulnerable to hackers.
How to protect your network from remote access?
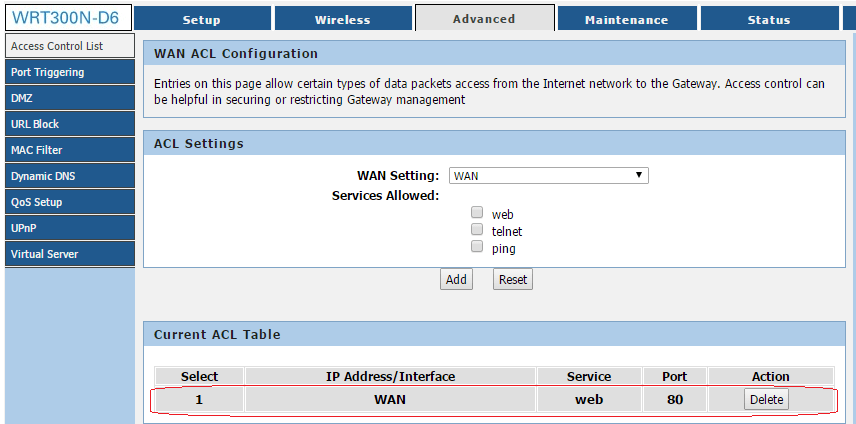
You should set up firewalls to restrict access using software or hardware or both.
What is remote access software?
Remote computer access software lets you access networks and computers remotely. It can enable file sharing. It’s like having a remote control for a computer or system that isn’t near you. You’ll be able to remotely download files and applications from your desktop or another person’s computer onto your laptop or your cell phone. Remote access also gives you control over that remote device
Why is it important to limit the number of users who can log in?
Remote computer access can help businesses, individuals, and families in a variety of ways. But it’s important to make remote access secure .
What is a RAS gateway?
RAS Gateway - Multitenant. You can deploy RAS Gateway as a multitenant, software-based edge gateway and router when you are using Hyper-V Network Virtualization or you have VM networks deployed with virtual Local Area Networks (VLANs). With the RAS Gateway, Cloud Service Providers (CSPs) and Enterprises can enable datacenter and cloud network traffic routing between virtual and physical networks, including the Internet. With the RAS Gateway, your tenants can use point-so-site VPN connections to access their VM network resources in the datacenter from anywhere. You can also provide tenants with site-to-site VPN connections between their remote sites and your CSP datacenter. In addition, you can configure the RAS Gateway with BGP for dynamic routing, and you can enable Network Address Translation (NAT) to provide Internet access for VMs on VM networks.
How to install Remote Access as a LAN router?
To install Remote Access as a LAN router, either use the Add Roles and Features Wizard in Server Manager and select the Remote Access server role and the Routing role service; or type the following command at a Windows PowerShell prompt, and then press ENTER. Install-RemoteAccess -VpnType RoutingOnly.
What is always on VPN?
Always On VPN enables remote users to securely access shared resources, intranet Web sites, and applications on an internal network without connecting to a VPN. For more information, see RAS Gateway and Border Gateway Protocol (BGP).
What is web application proxy?
Web Application Proxy provides reverse proxy functionality for web applications inside your corporate network to allow users on any device to access them from outside the corporate network. Web Application Proxy pre-authenticates access to web applications using Active Directory Federation Services (AD FS), and also functions as an AD FS proxy.
What is Remote Access Guide?
The Remote Access guide provides you with an overview of the Remote Access server role in Windows Server 2016, and covers the following subjects:
Can you use remote access in Azure?
Using Remote Access in Microsoft Azure is not supported. You cannot use Remote Access in an Azure VM to deploy VPN, DirectAccess, or any other Remote Access feature in Windows Server 2016 or earlier versions of Windows Server. For more information, see Microsoft server software support for Microsoft Azure virtual machines.
How to know if malware has been removed?
Monitor your computer after removing any malware. If your antivirus and/or Anti-Malware found malicious programs, you may have successfully removed the infection, but you'll need to keep a close eye on your computer to ensure that the infection hasn't remained hidden.
What to do if your computer is compromised?
Change all of your passwords . If your computer was compromised, then there’s a possibility that all of your passwords have been recorded with a keylogger. If you’re sure the infection is gone, change the passwords for all of your various accounts. You should avoid using the same password for multiple services.
How to install antivirus on another computer?
If you don't have an antivirus, download an installer on another computer and transfer it to your computer via USB. Install the antivirus and then run a scan with it.
Why does Windows Defender automatically deactivate?
Windows Defender will automatically deactivate if you install another antivirus program. 2. Make sure your firewall is properly configured. If you're not running a web server or running some other program that requires remote access to your computer, there is no reason to have any ports open.
How to scan for malware on Windows 10?
If you're using Windows 10, you can use the built-in scanning tools in Settings > Update & Security > Windows Security to check for rogue applications. If you're using a Mac, check out How to Scan a Mac for Malware to learn how to use Mac-based scanning tools.
How to stop someone from accessing my computer?
This includes removing any Ethernet cables and turning off your Wi-Fi connections.
Why is public Wi-Fi so dangerous?
Try to avoid public Wi-Fi spots. Public Wi-Fi spots are risky because you have zero control over the network. You can't know if someone else using the spot is monitoring traffic to and from your computer. By doing this, they could gain access to your open browser session or worse. You can mitigate this risk by using a VPN whenever you are connected to a public Wi-Fi spot, which will encrypt your transfers.
How Do I Know If Someone is Accessing My Computer Remotely?
Figuring out whether someone is remotely viewing your computer or not is not a tough job, but you need to be a little cautious and clear your doubts right away .
How to check history on Firefox?
Open Mozilla Firefox on your computer. Click the icon that looks like a row of books and says "View history, saved bookmarks and more" on the menu bar. Click on "History" and check the browsing activities on this browser.
How to tell if someone is spying on my computer?
Checking your browser history is also a way to tell if someone is spying on your computer. Regardless of what browser you use, you can check it’s brsowing history. Below we will guide you the detailed steps to do that on some mainstream browsers on a computer.
How to get rid of a computer?
Way 1: Disconnect Your Computer From the Internet. Everything is possible because of the internet. No internet means no one can remotely view your PC; if you doubt that someone is using your PC the same as you, immediately disconnect your internet. Disconnecting the internet from the taskbar might not be enough because it can easily connect on its ...
What is Task Manager on Mac?
It is an ideal way to check on secret remote viewers. On Windows computer, it is called Task Manager, and On Mac computer, it is called Activity Monitor.
What does it mean when a program moves past the firewall?
If you notice that a program has moved past your Firewall without asking you, this could indicate that a programmer has empowered far off access. If so, quickly eliminate any recent progressions to your firewall, restart your PC, and run the antivirus present in your PC, so no risk factors stay behind.
How to open a document folder?
Open the file explorer window, and open the document folder.
What is Zoho Assist?
Zoho Assist is yet another remote access tool that has a free edition for both personal and commercial use. You can share screens and files, and chat remotely with the other user through a unique session ID and password.
How to access remote computer?
There are a couple of ways to access the remote computer. If you logged in to your account in the host program, then you have permanent access which means you can visit the link below to log in to the same account in a web browser to access the other computer.
How to connect to a host browser?
To connect to the host browser, sign on to Chrome Remote Desktop through another web browser using the same Google credentials or using a temporary access code generated by the host computer.
How to enable remote desktop access to a computer?
To enable connections to a computer with Windows Remote Desktop, you must open the System Properties settings (accessible via Settings (W11) or Control Panel) and allow remote connections via a particular Windows user.
How does remote utility work?
It works by pairing two remote computers together with an Internet ID. Control a total of 10 computers with Remote Utilities.
What is the other program in a host?
The other program, called Viewer, is installed for the client to connect to the host. Once the host computer has produced an ID, the client should enter it from the Connect by ID option in the Connection menu to establish a remote connection to the other computer.
What is the easiest program to use for remote access?
AeroAdmin is probably the easiest program to use for free remote access. There are hardly any settings, and everything is quick and to the point, which is perfect for spontaneous support.
What is a remote desktop sandbox?
You are wondering what kind of "sandbox" your remote desktop software is in, and what permissions it has on your home system. The idea is that a program, or a vm, or remote desktop window is only allowed to play in its sandbox. It cannot break out and do creepy things.
What is separate work and personal computing?
This means a separate desktop/laptop if you can afford it, or a virtual workstation that doesn't share much or any data with your personal files.
What does "assume anything you do on work computing resources is being audited in case we want to?
Assume anything you do on work computing resources is being audited in case we want to snoop later. This means emails, what files you've copied up/down from your remote workstation, what sites you've browsed to on company resources, etc.
Is remote desktop good?
With remote desktop you are good but with VPNs they could log things if it is internally setup. I'd recommend always separating work from personal by having different computers. Expense out a work computer when you work from home in the home office.
What happens if you are shady?
In general - if you are being shady, expect the overall behavior that comes with it - idleness, evasiveness, low productivity - to trigger your boss to look deeper . I've known far too many people who took a quick call and forgot to mute the video game in the background. The last guy was looking for a new job less than a week later.
What is a work ensuring?
Ensure you are working during work hours.
Can remote workers see your email?
However, as the IT person who usually sets up and supports the infrastructure used for remote working, that they can, if they desire, see things like what you named your workstation (I’ve seen some real... interesting... workstation names). They can read your work email (keep private email out of work.) Lastly, if you are running remote/published software, keep your personal web browsing out of the work hosted web browser. Yes, Karen, I can see you reading that romance site when you aren’t on calls. That’s why I’m cleaning malware out of your profile. Don’t clutch your pearls and say you have no clue while I can see that you just closed a tab.
Is It Possible To Spy On A Cell Phone Without Having It?
The only time it is legal to spy on a cell phone is with the phone owner’s knowledge. In the case of spy apps like PhoneSpector, you can spy on a cell phone with their knowledge. This is specifically true for parents tracking their child’s phone use and businesses tracking company-owned devices.
What is the most basic method by which to can access someone’s phone without their knowledge?
Password peeking is the most basic method by which to can access someone’s phone without their knowledge. This involves watching when they unlock their phone or asking them to open their phone for some reason while making sure you can view their password.
What is the hacking method?
An unconventional method for the average person is hacking someone’s cell phone to gain access to it. If you do not know how to do this, there are experts for hire online that can accomplish such tasks (which we do not recommend doing). Methods they may use to hack the target user include Wi-Fi networks, phishing, and malware.
How does OTA work?
Using the OTA (over-the-air) link, you can remotely download the app and monitor the target phone without having it in your possession. Once a remote connection is established, Auto Forward continuously uploads activity from the target phone to your secure online account.
What is a keylogger?
Keylogger: Captures and records all keystroke entries performed on the phone.
What is an OTA link?
OTA (over-the-air) link: Enables remote downloading for quick and easy monitoring of any cell phone.
When did auto forward spy come out?
Auto Forward Spy was introduced in 2012 and has been a market leader ever since. Over the years, the app has been improved with remote access and the ability to monitor a phone without having it in your possession. They also have an option to “clone a phone” which shows you how to create an exact copy of one phone to another.
