
Yes, it is possible to remote into someone's system, but they first have to allow you in, whether they realize it or not. A certain virus attached to a download, or a phishing email that opens a backdoor into their PC, these things will gain the hacker access to that computer.
Is it possible to be hacked through remote access?
But of course, with all things tech — there is the possibility of being hacked. The most widely-used remote access software uses the Remote Desktop Protocol (RDP), which, if abused, can allow hackers to tap into networks. How Do Hackers Gain Access?
How can you hack into someone's computer?
Recommend Level: Another way you can hack into someone's computer is by installing or getting the users to install TeamViewer software, this software gives you the ability to literally take over a computer and control it from your device which is acting as a remote control, giving you access to all the data on the target computer.
How can I prevent hackers from accessing my computer remotely?
This helps prevent hackers from accessing your computer remotely, which prevents them from installing malware on your device remotely. Another option is to check the Windows Event Viewer app to look for any unfamiliar remote access. This app shows a log of application use and system messages, including error messages, with timestamps.
How do I prevent remote access to my PC?
To prevent remote access to your PC: 1 Click on the Windows Start button 2 Type in "Allow Remote Assistance invitations to be sent to this computer" in the search bar 3 Uncheck the box next to "Allow Remote Assistance connections to this computer" 4 Click Apply More ...
Can remote access be hacked?
Remote Desktop Protocol (RDP) has been known since 2016 as a way to attack some computers and networks. Malicious cyber actors, hackers, have developed methods of identifying and exploiting vulnerable RDP sessions via the Internet to steal identities, login credentials and install and launch ransomeware attacks.
Can someone remotely access my computer without me knowing?
"Can someone access my computer remotely without me knowing?" The answer is "Yes!". This could happen when you are connected to the internet on your device.
Can you remotely access someones computer?
You can use a computer or mobile device to access files and applications on another computer over the Internet with Chrome Remote Desktop. Chrome Remote Desktop is available on the web on your computer. To use your mobile device for remote access, you need to download the Chrome Remote Desktop app.
What happens if you give someone remote access to your computer?
This can be even worse than just conning you out of money, as undetected malware can allow hackers to steal your identity, including your passwords and financial information, over and over again, even if you get new passwords and account numbers.
How can I tell if my computer is being monitored at work 2022?
Open task manager by right-clicking on the taskbar and choosing Task Manager. If there's a suspicious process, that's the monitoring app. Question: Can my company see what I do on my computer? Answer: Your company can see your device activities and track them if they provide you with that computer.
Can someone remotely access my computer with my IP address?
Someone can use your IP to hack your device The internet uses ports as well as your IP address to connect. There are thousands of ports for every IP address, and a hacker who has your IP can try all of those ports to brute-force a connection, taking over your phone for example and stealing your information.
How do you know if your PC is being monitored?
How to Check If Your Computer Is Being MonitoredLook for Suspicious Processes. Suspicious processes may indicate that your computer is being monitored. ... Run Antivirus Software. Antivirus software can reveal whether or not your computer is being monitored. ... Evaluate Ports. Another tip is to evaluate your network's ports.
Is remote PC safe?
What should I do? Is RemotePC private and safe? Yes, RemotePC offers secure and optimized solutions for accessing remote computers. RemotePC uses TLS v 1.2/AES-256 encryption for transferring user authentication data between remote computer and local computer.
How do I trace remote access?
1:132:22How to trace remote access logs VPN access - YouTubeYouTubeStart of suggested clipEnd of suggested clipAnd run. And I'm just gonna type in C colon backslash Windows backslash tracing and that's gonnaMoreAnd run. And I'm just gonna type in C colon backslash Windows backslash tracing and that's gonna open up my tracing directory.
How I know if my computer is hacked?
If your computer is hacked, you might notice some of the following symptoms: Frequent pop-up windows, especially the ones that encourage you to visit unusual sites, or download antivirus or other software. Changes to your home page. Mass emails being sent from your email account.
How do I trace remote access?
1:132:22How to trace remote access logs VPN access - YouTubeYouTubeStart of suggested clipEnd of suggested clipAnd run. And I'm just gonna type in C colon backslash Windows backslash tracing and that's gonnaMoreAnd run. And I'm just gonna type in C colon backslash Windows backslash tracing and that's gonna open up my tracing directory.
Is my PC being monitored?
How to Check If Your Computer Is Being MonitoredLook for Suspicious Processes. Suspicious processes may indicate that your computer is being monitored. ... Run Antivirus Software. Antivirus software can reveal whether or not your computer is being monitored. ... Evaluate Ports. Another tip is to evaluate your network's ports.
How can you tell if your monitor is being monitored?
Here are 7 different ways to confirm if your computer is free from being monitored or not.Monitoring processes from Windows Task Manager. ... Monitoring Open Ports using netstat. ... Periodic Antivirus scans. ... Investigating Recent Files. ... Investigating Browser History. ... Auditing Login Event Viewer. ... Identifying Corporate Monitoring.
How do I Remotely Access Another Computer without Permission?
you will need to either know how to using some technical techniques or you will have to install a hacking app on the target device to get around knowing how to hack someone's computer remotely.
What is a virus that attaches itself to a downloadable file or a link within a?
A virus, which attaches itself to a downloadable file or a link within a phishing email , unravels the road into someone's personal computer, letting you attain access to the contents contained within it.
Can you hack a computer if you are not an administrator?
However, if you are not an administrator, it is still possible to gain access but you will need to use professional hacking steps to do so.
Can you hack someone's computer with Monivisor?
After reading the introduction and the steps on how to hack someone's computer with MoniVisor, we can know that this is an App suitable for everyone. Indeed, there are other 2 ways to hack a computer without the help of such ind of professional software, but you have to be equipped with good basis of technology. Check these ways below.
Can you hack a computer if it is not locked?
This method, however, can prove to backfire if the user catches onto what is happening, as the software is clearly visible on the target computer, they can clearly know what are you doing if the screen is not locked. You also need to have the same version and a stable and fast connection on both sides in order for this method to work effectively, a stable internet connection is not possible all the time making hacking and monitoring limited to only when the target computer is connected to LAN or Wi-Fi.
Is It Possible to Hack Into Someone's Computer Remotely?
Although not necessarily easy, it is definitely possible to remotely enter into someone's computer. To break into someone's system, you must gain their permission to do so, and it is important they do not realize that they have given it to you. A virus, which attaches itself to a downloadable file or a link within a phishing email, unravels the road into someone's personal computer, letting you attain access to the contents contained within it. A much simpler and safer method, though, is to simply use an invisible third-party hacking tool such as MoniVisor by ClevGuard in order to not get caught or waste too much time.
How to check if you have RDP enabled?
First thing is to know if you have RDP enabled. That’s easy to check from your Control Panel under System > Remote Settings > Remote Desktop (under Windows 7, other operating systems vary).
What can RDP intruders do?
What can RDP intruders do? If you have administrative privileges assigned to the user they login as, they can take your computer for an unfettered spin around the block, ranging from turning it off, rebooting it, installing software (including malware), or just having a look around to find documents of files with your critical personal information in them like banking, accounting, or other information and then spirit them off across the network to their own computers for nefarious purposes.
Is a strong password good for a password?
Speaking of protection, aside from not using easily guessed usernames, a strong password would also go a long ways toward protecting the account. If hackers can programmatically “guess” your password because it’s based on a simple word – they will quite quickly. On the other hand, if it’s complex, meaning a combination of upper and lower case letters, numbers, and symbols (the longer the better), their task becomes much more daunting.
Can a remote attacker access my computer as administrator?
When remote attackers come calling this could pose problems for an unwitting user who is logged in as Administrator. Very likely the bad guys will be looking to gain elevated access, and logging in as Administrator is a quick way to do that. If they can pair that valid User with an easy-to-guess password, they’ve got the keys to your computer’s crown jewels.
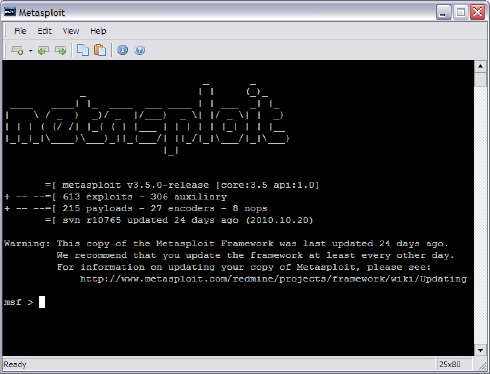
Can malware be installed via RDP?
Lately, we’ve seen an increase in reports of malware being installed via Remote Desktop Protocol (RDP). This is the powerful protocol which has been letting you view a Windows desktop “over the wire” on the other side of the globe (or back at your home from the office) for over a decade now. Sadly, while RDP can serve a variety of useful purposes ranging from remote “hands-on” support to configuring and running servers, in the wrong hands it can be a remote control weapon that enables bad actors to zombify your computer and have it do their bidding.
How Do Hackers Gain Access?
There are several ways hackers can gain access to a network remotely using this software: lack of governance for installing remote access software and weak remote access account passwords. If a company’s employees are unaware that they’ve installed remote access software on company devices, then there is potential for abuse as it increases the risk of hackers finding a backdoor.
What is remote access software?
Remote access software allows a computer’s desktop environment to be run remotely on one system while being displayed on a separate client device. Many organizations find remote access software extremely useful.
Why is it important to choose a strong password for remote access?
It’s extremely important for businesses to choose a strong password for their remote access accounts. If the RDP is exposed to the Internet, a simple network engine can allow hackers to poke around the network and use various methods like brute force attacks to try and guess the password. Once inside the system, it’s only a matter of time before they acquire access information needed to infiltrate other critical systems.
What is fileless attack?
Previously, we discussed fileless attacks, an increasingly popular method used by hackers to spread ransomware that sometimes involves exploiting the macro functionality in Microsoft Office documents. Now, it appears that another exploitable entry point has been on the rise: remote access software.
Why were the WannaCry and NotPetya attacks successful?
Both the WannaCry and NotPetya attacks, for example, were successful because hackers used leaked NSA exploits to infect older computer operating systems.
What is RDP hacking?
Hackers are getting more and more creative in their hacking methods, and using the RDP is one way they can make their way into a company’s network. In fact, Naked Security recently reported on a growing trend of hackers spreading ransomware by accessing computer systems through the RDP.
How do hackers sneak into a network?
Hackers typically sneak remotely into the networks of their victims by setting up phishing scams and duping users into downloading malware-ridden files, which are then executed to commence a cyberattack like ransomware. They may also look for vulnerabilities in computer systems to attempt to get into a network.
Why is remote access important?
Remote access is a great feature for certain industries and employers, because it helps to connect employees to necessary servers and storage devices via their internet connection. Beyond workplace settings, however, there are limited cases in which you would want to access your device remotely.
How to check if someone accessed my PC?
Another option is to check the Windows Event Viewer app to look for any unfamiliar remote access. This app shows a log of application use and system messages, including error messages, with timestamps. If you don’t recognize a particular action at a time that you were on your device, then it is likely that someone accessed your PC. You can find this app in the Windows search bar by searching for "Event Viewer."
How often do hackers attack people?
There is no doubt that hacking and cybercrime are on the rise. In fact, it is estimated that hackers attack someone online every 32 seconds. While many of them target companies and organizations, others go after private individuals in an attempt to steal personal information from computers, cell phones, and tablets.
How to stay ahead of hackers?
You can stay ahead of hackers by keeping an eye on your online accounts to see if there are any recent changes. It’s easy to overlook this step, especially if you don’t use a particular account often or you don’t look at your own page frequently, in Facebook for example.
How to prevent identity theft?
Also, disconnect any credit cards or other financial information tied to your account settings. This will help prevent further identity theft and ensure that your sensitive data does not fall into the wrong hands.
How to know if someone logged into my account?
Most major online accounts will allow you to see when someone has logged into your account and from what location or IP address (click here to learn how to find your IP address). If you do not recognize the login attempt, then you should immediately change your password and notify the company that your account was compromised.
What to do if you fall victim to a Trojan attack?
If you fall victim to a Trojan attack, there are steps you can take to mitigate it. First, you need to format your hard drive, which may be painful if you haven’t backed up your important data. For those who may not be up to date with this critical maintenance task, check out our list of the best Windows backup softwareto be prepared.
How to enable remote desktop on Windows 10?
Step 1: From the Windows button, go to the “Start” menu. Step 2: Click on the gear icon which symbolizes the “Settings”. Step 3: Click on “System” and then on “Remote Desktop”. Step 4: Switch on “Enable Remote Desktop”. If you are using the older version of Windows, you need to follow the steps given below.
Can you access someone else's computer?
You can access others’ computer from almost any device with a stable internet connection.
Can you remotely control another computer?
Once you have followed the above steps, you can use cmd to remotely control on another computer to access their computer system. Here are the steps to know how to remotely access another computer without permission using cmd.
Can you key in your computer's IP address?
Instead of “computername” you can even key in your computer system’s public IP address. If you do not know the IP address of the target’s computer, you can search for “What’s my IP” on Google through target’s browser. 3. The Limitations of Using CMD To Hack a Computer.
Can you hack into a remote desktop?
1. If the target’s computer have not earlier configured a remote desktop computer system, you cannot hack into the system using this method. 2. For this method to work, the target’s computer needs to be on and not in sleep or hibernation mode. 3.
Can you hack a turned off machine?
Hacking a turned-off machine is extremely unlikely. Two things have to line up for it to happen.
Can a computer be hacked?
In order for a turned-off computer to be hacked, it must first somehow be remotely powered on, either by the “Wake on LAN” feature (which is normally disabled) or if standby mode resumes unexpectedly. Then the computer must also be vulnerable in some way while it’s running. As long as you follow common security best practices, the risk is small.
Can a computer be hacked remotely?
The other condition is nothing more than a lack of security. If the PC turned on remotely did not have appropriate security software installed and was not behind a firewall, then it is conceivable the PC could be hacked remote ly.
How to protect yourself from hackers?
Here are some ways you can protect yourself online: Install Reliable Anti-Malware Software. Once someone successfully hacks into your computer, it may be too late for you to protect your sensitive information.
What are some techniques hackers use?
Some of the common techniques hackers use: Ads and download links with malware. Stealing cookies (usernames, passwords and browsing history) through unencrypted sites. Emails with infected attachments and links.
What happens if you don't turn off the network adapter?
Basically in this scenario, if you do not completely turn off the network adapter for the computer, the unit can receive specific instructions on waking up. Such feature can be activated if you enable certain computer settings on BIOS such as “wake on LAN” or “wake on USB.”
Can a computer be remotely accessed?
A special signal can be sent to the computer over a shared network, allowing the hacker to power it back on and access any data they’d need. Without appropriate security software installed, such as anti-malware tools like Auslogics Anti-Malware, it is possible for hackers to access the computer remotely even if it is turned off.
Can a computer be hacked if it is turned off?
If your computer is turned off, it cannot be booted and hacked even if you leave it connected to the power source and the Internet.
Can a hacker access my Gmail account?
Take advantage of the 2-factor authentication process offered by certain services such as Gmail or LinkedIn. In this way, even if malware has compromised your password, there is another step a hacker should take before they can access your information. In most cases, when someone attempts to log into your account, you will be sent a secret code via SMS.
Can you manually hunt down malware?
Of course, you can manually hunt down the malware, but this will take too much time and before you know it, your data have been exposed or leaked. So, it is best to use a high-grade anti-malware tool such as Auslogics Anti-Malware which automatically detects threats and effectively quarantines or eliminates them.
How to install antivirus on another computer?
If you don't have an antivirus, download an installer on another computer and transfer it to your computer via USB. Install the antivirus and then run a scan with it.
What to do if your computer is compromised?
Change all of your passwords . If your computer was compromised, then there’s a possibility that all of your passwords have been recorded with a keylogger. If you’re sure the infection is gone, change the passwords for all of your various accounts. You should avoid using the same password for multiple services.
How to know if malware has been removed?
Monitor your computer after removing any malware. If your antivirus and/or Anti-Malware found malicious programs, you may have successfully removed the infection, but you'll need to keep a close eye on your computer to ensure that the infection hasn't remained hidden.
How to scan for malware on Windows 10?
If you're using Windows 10, you can use the built-in scanning tools in Settings > Update & Security > Windows Security to check for rogue applications. If you're using a Mac, check out How to Scan a Mac for Malware to learn how to use Mac-based scanning tools.
How to stop someone from accessing my computer?
This includes removing any Ethernet cables and turning off your Wi-Fi connections.
Why is public Wi-Fi so dangerous?
Try to avoid public Wi-Fi spots. Public Wi-Fi spots are risky because you have zero control over the network. You can't know if someone else using the spot is monitoring traffic to and from your computer. By doing this, they could gain access to your open browser session or worse. You can mitigate this risk by using a VPN whenever you are connected to a public Wi-Fi spot, which will encrypt your transfers.
What to do if you can't get rid of intrusion?
If you're still experiencing intrusions, or are concerned that you may still be infected, the only way to be sure is to completely wipe your system and reinstall your operating system.
