What can a remote access Trojan do?
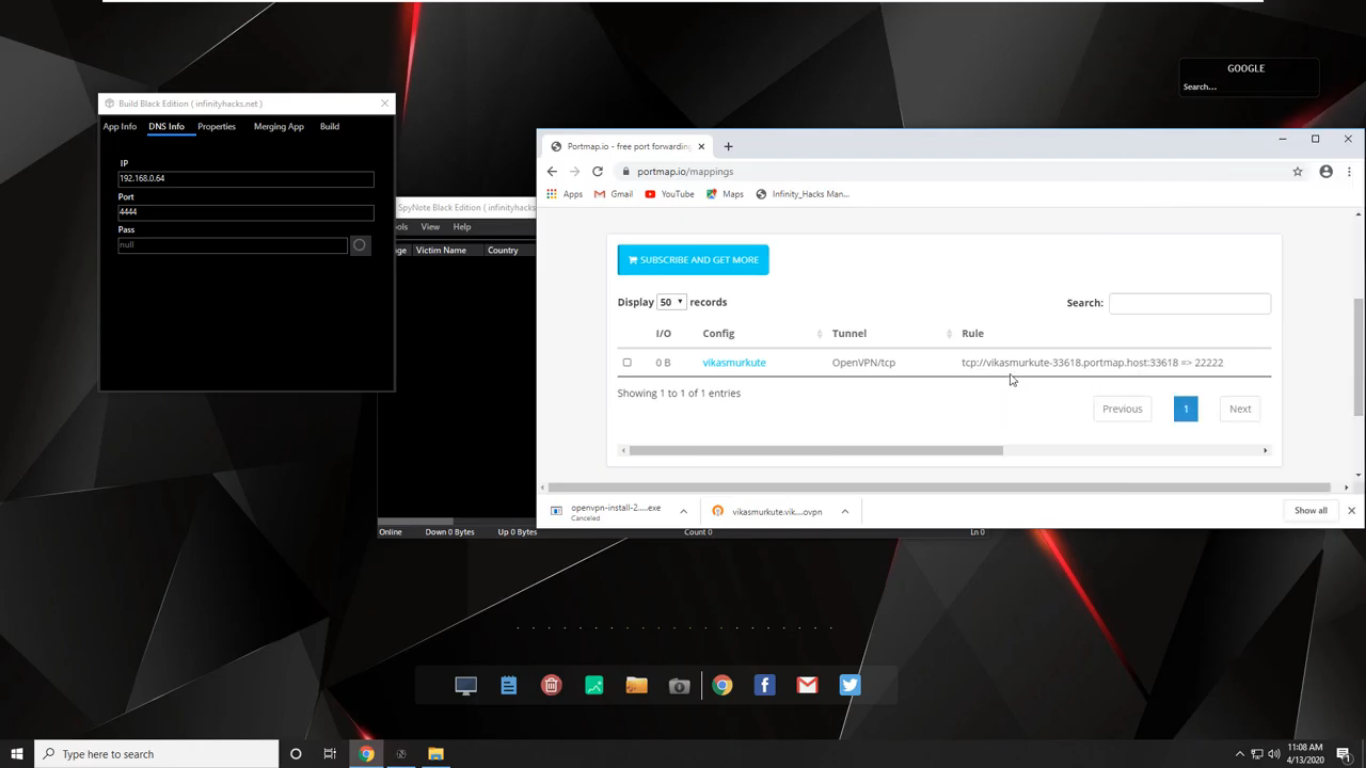
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
What is a computer remote access tool RAT?
A remote access Trojan (RAT) is a malware program that includes a back door for administrative control over the target computer. RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment.
Is someone using my computer remotely?
Open your Task Manager or Activity Monitor. These utilities can help you determine what is currently running on your computer. Windows – Press Ctrl + Shift + Esc. Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
Who uses remote access tool?
Remote access is used by support technicians and professionals who remotely configure data centers and other industrial applications. There are two major categories of remote desktop software: operating-system-based and third-party solutions.
Is remote access Trojan illegal?
Law enforcement officials say that simply possessing a remote-access tool isn't illegal. In fact, remote-access tools are often used for IT support purposes in corporate environments.
How do I use remote admin tools?
Setting Up RSATOpen the Start menu, and search for Settings.Once within Settings, go to Apps.Click Manage Optional Features.Click Add a feature.Scroll down to the RSAT features you would like installed.Click to install the selected RSAT feature.More items...•
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
Is a backdoor malware?
A backdoor is a malware type that negates normal authentication procedures to access a system. As a result, remote access is granted to resources within an application, such as databases and file servers, giving perpetrators the ability to remotely issue system commands and update malware.
What are the variant of remote access Trojan?
There are a large number of Remote Access Trojans. Some are more well-known than others. SubSeven, Back Orifice, ProRat, Turkojan, and Poison-Ivy are established programs. Others, such as CyberGate, DarkComet, Optix, Shark, and VorteX Rat have a smaller distribution and utilization.
Is remote access Trojan illegal?
Law enforcement officials say that simply possessing a remote-access tool isn't illegal. In fact, remote-access tools are often used for IT support purposes in corporate environments.