- From the Check Point Gateway tree, select VPN Clients > Remote Access.
- Select Support Visitor Mode. In Machine's Interface, keep All Interfaces selected. Optional - Select the Visitor Mode...
Full Answer
How to setup a remote access VPN?
Use a VPN Router with the built-in VPN server capability
- Launch a browser window from your PC connected to the routers’ network
- Enter the router IP address in the search to login into your router
- Enter the username and password of your router and login into it.
- Go to the Settings page and select VPN Service or setup page.
- Enable the VPN service by selecting the checkbox and apply
How to speed up VPN remote access?
How to speed up a VPN
- Choose another server. Connecting to your nearest server will usually offer the best performance, but there are occasional exceptions.
- Refresh your system. If speeds are notably worse than unusual with several servers, the problem could be closer to home. ...
- Switch protocol. ...
- Tweak protocol settings. ...
- Use a wired connection. ...
- Try split tunneling. ...
How to activate open VPN?
- Right-click the Start button.
- Click Settings. Source: Windows Central
- Click Network & Internet.
- Click VPN. Source: Windows Central
- Click Add a VPN connection.
- Click the dropdown menu below VPN provider. Source: Windows Central
- Click Windows (built-in).
- Click the Connection name field. ...
- Type a name for the VPN connection. ...
- Click the Server name or address field. ...
Can connect to VPN, cannot access remote resources?
If you cannot access some resources using only the VPN (e.g., it’s behind a departmental firewall), Millward said you should connect to the GlobalProtect client first to verify your identity, then use your preferred remote access management client.
See more

What is remote access VPN checkpoint?
Provide users with secure, seamless remote access to corporate networks and resources when traveling or working remotely. Privacy and integrity of sensitive information is ensured through multi-factor authentication, endpoint system compliance scanning and encryption of all transmitted data.
Can I use a VPN for remote access?
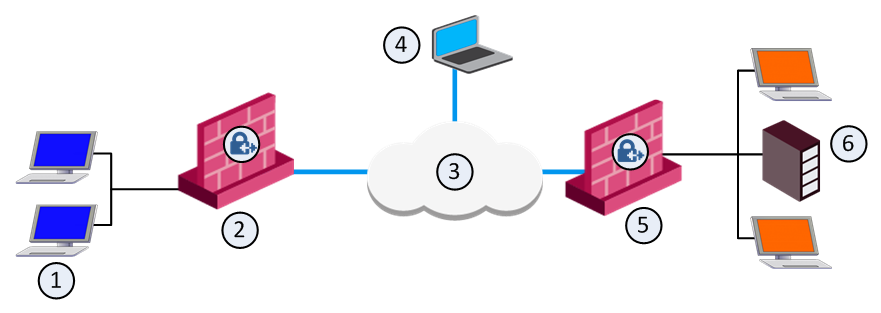
A remote access virtual private network (VPN) enables users who are working remotely to securely access and use applications and data that reside in the corporate data center and headquarters, encrypting all traffic the users send and receive.
How do I connect to Checkpoint VPN?
Configuration - Check Point security gatewayOpen SmartConsole > Security Policies > Access Tools > VPN Communities.Click Star Community. ... Enter an Object Name for the VPN Community.In the Center Gateways area, click the plus sign to add a Check Point Security Gateway object for the center of the community.More items...•
What is mobile checkpoint VPN?
Check Point Mobile VPN for Android devices is an L3 VPN client. It supplies secure connectivity and access to corporate resources using the L3 IPSec/SSL VPN Tunnel. The application is available in the Google Play Store: https://play.google.com/store/apps/details? id=com.checkpoint.VPN&hl=en.
Which VPN is best for remote access?
Best Remote Access VPNs for business.Perimeter 81 – Best all-round business VPN.GoodAccess – Security Strategy Options.ExpressVPN – Lightning Fast VPN.Windscribe – VPN with Enterprise-Friendly Features.VyprVPN – Secure VPN with Business Packages.NordVPN – Security-first VPN.More items...•
What is the difference between VPN and remote access?
A VPN is a smaller private network that runs on top of a larger public network, while Remote Desktop is a type of software that allows users to remotely control a computer. 2. Remote Desktop allows access and control to a specific computer, while VPN only allows access to shared network resources.
What is remote secure access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
How do I configure checkpoint site to site VPN?
Getting Started with Site-to-Site VPNCreate the Security Gateway. Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. ... Create the Trusted Communication (SIC. ... Enable the IPsec VPN Software Blade. ... Click OK.
How does Checkpoint endpoint security work?
Endpoint protection works via a combination of network and device-level defenses. At the network level, the organization may restrict access to the enterprise network based on a device's compliance with corporate security policies and least privilege.
How do I use checkpoint mobile VPN?
5:5410:30Check Point Remote Access VPN Setup and Config - YouTubeYouTubeStart of suggested clipEnd of suggested clipUp. We click trust. And continue then it's going to ask you what vpn client you're going to use theMoreUp. We click trust. And continue then it's going to ask you what vpn client you're going to use the default. One we're going to use a username and password. And then we click finish.
What is Check Point mobile Access?
Check Point Mobile Access is the safe and easy solution to securely connect to corporate applications over the Internet with your Smartphone, tablet or personal computer (PC). Mobile Access allows remote and mobile workers to simply and securely connect to email, calendar, contacts and corporate applications.
What is a VPN endpoint?
VPN goes between a computer and a network (client-to-server), or a LAN and a network using two routers (server-to-server). Each end of the connection is an VPN "endpoint", the connection between them is a "VPN tunnel".
Why do companies use VPN for remote work?
A VPN allows remote employees to become an extension of the network as if they're in the office with the same security and connectivity benefits. Think of it as a secure network line from a user to applications, whether those applications reside in a private data center or on a public network.
What are the disadvantages of using a VPN?
The 10 biggest VPN disadvantages are:A VPN won't give you complete anonymity: Read more.Your privacy isn't always guaranteed: Read more.Using a VPN is illegal in some countries: Read more.A safe, top-quality VPN will cost you money: Read more.VPNs almost always slow your connection speed: Read more.More items...•
Does a work VPN expose my home network to my employer?
When you use the corporate VPN provided by your employer, it's a little different. It still creates the encrypted tunnel, and still routes your traffic to a server. People on the same network as you and your ISP are still blind.
How do I setup a VPN between home and office?
In Windows, go to Control Panel, Network and Sharing, Create a New Connection, VPN. For a Mac, you'll go to System Preferences, Network, +, VPN. At this point, you'll be prompted to enter your office's IP address. If your ISP has given you a static IP address, go ahead and enter it and test the connection.
What is check point security?
Check Point enables organizations to meet NIST remote access security standards and more while easily managing least privilege access to internal resources with real-time, intelligent trust decisions based on defined policies and contextual data. Check Point’s zero trust architecture also restricts user access to authorized resources so that the right people have access to the right resources at the right time, without the need for a VPN.
What is check point?
Check Point provides several secure remote access options for remote workers including VPN Replacement, Third-party Access, Developer Access and Privileged Access Management (PAM) as well as application. database and remote desktop access that meets or exceeds NIST security controls.
Why is remote access important?
The security of remote access servers is particularly important because they provide a way for external hosts to gain access to internal resources, as well as a secured, isolated telework environment for organization-issued, third-party-controlled, and BYOD client devices.
What decisions should organizations make about remote access?
Organizations should make risk-based decisions about what levels of remote access should be permitted from which types of client devices.
Why do organizations use enterprise remote access?
Many organizations let their employees, contractors, business partners, and vendors use enterprise remote access technologies to perform work remotely using organization-owned and bring your own device (BYOD) client devices that must be secured against data breaches and theft. Security concerns include the lack of physical security controls, the use of unsecured networks, connection of infected devices to internal networks, and the availability of internal resources to external hosts.
What is checkpoint VPN?
Check Point Remote Access VPN provides users with secure, seamless access to corporate networks and resources when traveling or working remotely. Privacy and integrity of sensitive information is ensured through multi-factor authentication, endpoint system compliance scanning and encryption of all transmitted data.
What is Remote Access VPN?
Remote Access VPN ensures that the connections between corporate networks and remote and mobile devices are secure and can be accessed virtually anywhere users are located.
What are the requirements for VPN?
Each host typically has VPN client software loaded or uses a web-based client. Privacy and integrity of sensitive information is ensured through: 1 Multi-factor authentication 2 Endpoint system compliance scanning 3 Encryption of all transmitted data
What is a compliance check?
Compliance checks verify that the client complies with the organization's security policy. Non-compliant client connections to the encryption domain will be blocked.
What is endpoint compliance?
Endpoint compliance verifies the security level of the endpoint, and reports back to the Security Gateway. The gateway can allow connectivity to specific network resources, based on compliance level.
What are the options for multiple authentication?
Multiple authentication options including username and passwords, challenge and response, User Certificate and CAPI, software or hardware smartcards and one time tokens
Is it safe to work remotely?
Accessing corporate resources while away from the office are essential to the productivity of employees. However, remote locations are often not secure. Simple acts such as checking e-mail via a wireless internet connection in a coffee shop are enough to compromise user systems and corporate data. These leave corporations vulnerable to lawsuits, breach of data, and failure to comply with regulatory requirements.
