How to setup a remote access VPN?
Use a VPN Router with the built-in VPN server capability
- Launch a browser window from your PC connected to the routers’ network
- Enter the router IP address in the search to login into your router
- Enter the username and password of your router and login into it.
- Go to the Settings page and select VPN Service or setup page.
- Enable the VPN service by selecting the checkbox and apply
How to speed up VPN remote access?
How to speed up a VPN
- Choose another server. Connecting to your nearest server will usually offer the best performance, but there are occasional exceptions.
- Refresh your system. If speeds are notably worse than unusual with several servers, the problem could be closer to home. ...
- Switch protocol. ...
- Tweak protocol settings. ...
- Use a wired connection. ...
- Try split tunneling. ...
How do access remote network with OpenVPN?
Using OpenVPN to Securely Access Your Network Remotely
- Visit http://tplinkwifi.net, and log in with your TP-Link ID or the password you set for the router.
- Go to Advanced > VPN Server > OpenVPN, select the checkbox to enable VPN Server.
- Select the Service Type (communication protocol) for OpenVPN Server: UDP, TCP.
How to activate open VPN?
- Right-click the Start button.
- Click Settings. Source: Windows Central
- Click Network & Internet.
- Click VPN. Source: Windows Central
- Click Add a VPN connection.
- Click the dropdown menu below VPN provider. Source: Windows Central
- Click Windows (built-in).
- Click the Connection name field. ...
- Type a name for the VPN connection. ...
- Click the Server name or address field. ...

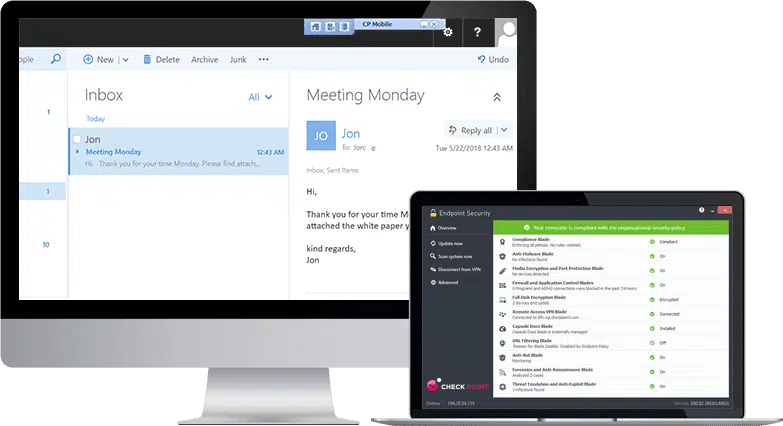
What is remote access VPN Check Point?
Provide users with secure, seamless remote access to corporate networks and resources when traveling or working remotely. Privacy and integrity of sensitive information is ensured through multi-factor authentication, endpoint system compliance scanning and encryption of all transmitted data.
How do I connect to Check Point VPN?
Configuration - Check Point security gatewayOpen SmartConsole > Security Policies > Access Tools > VPN Communities.Click Star Community. ... Enter an Object Name for the VPN Community.In the Center Gateways area, click the plus sign to add a Check Point Security Gateway object for the center of the community.More items...•
What type of VPN is Check Point?
The Check Point secured VPN implementation is based on IPSec (IP Security). IPSec is a commonly used set of protocols that was developed to support the secure exchange of packets at the IP layer between gateways that are connected over a public network (such as the Internet), and to create VPNs.
How do I update my Check Point VPN?
Below is a quick process to patch your computer and restore VPN/Endpoint connectivity.Validate if your Check Point VPN/EndPoint Client version is one of the following: ... If your client version is: Check Point Endpoint VPN E80. ... Reboot your machine.Click on EPPatcher_for_users.exe to install the patch.More items...
How do I configure checkpoint firewall?
Navigate to DEVICE–>INTERNET and click on Add an Internet Connection. Note- Below Image has already configured WAN Interface. 5. After Configuring WAN Interface, Navigate to ROUTING and Click on New and enter Gateway IP of WAN.
What is a VPN endpoint?
VPN goes between a computer and a network (client-to-server), or a LAN and a network using two routers (server-to-server). Each end of the connection is an VPN "endpoint", the connection between them is a "VPN tunnel".
What is the difference between site-to-site VPN and remote access VPN?
A remote access VPN connects remote users from any location to a corporate network. A site-to-site VPN, meanwhile, connects individual networks to each other.
What are the 3 types of VPN?
VPNs can be divided into three main categories – remote access, intranet-based site-to-site, and extranet-based site-to-site. Individual users are most likely to encounter remote access VPNs, whereas big businesses often implement site-to-site VPNs for corporate purposes.
How do you create a route based VPN in checkpoint?
Enabling Route Based VPNIn SmartConsole Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on., ... Open the Security Gateway / Cluster object.From the left tree, click Network Management > VPN Domain.More items...
What is mobile checkpoint VPN?
Check Point Mobile VPN for Android devices is an L3 VPN client. It supplies secure connectivity and access to corporate resources using the L3 IPSec/SSL VPN Tunnel. The application is available in the Google Play Store: https://play.google.com/store/apps/details? id=com.checkpoint.VPN&hl=en.
How do I install Checkpoint VPN client on Mac?
Installing the ClientDownload the Endpoint Security VPN for Mac E82. 50 - Disc Image file to the client computer.Double-click the file. After the disk image mounts to the file system, a Finder window opens with the contents of the package.Double-click the Endpoint_Security_VPN. ... Follow the on-screen instructions.
How does Checkpoint endpoint security work?
Endpoint protection works via a combination of network and device-level defenses. At the network level, the organization may restrict access to the enterprise network based on a device's compliance with corporate security policies and least privilege.
What is Check Point Mobile?
Check Point Mobile for Windows is an IPsec VPN client. It is best for medium to large enterprises that do not require an Endpoint Security policy.
What is endpoint security suite?
The Endpoint Security Suite simplifies endpoint security management by unifying all endpoint security capabilities in a single console and a single client. Endpoint Security Software Blades include: Desktop Firewall and Security Verification, Full Disk Encryption, Media Encryption and Port Protection, SandBlast Agent, Anti-Malware and Program Control, WebCheck browser virtualization and Remote Access VPN.
Does Check Point Mobile support two factor authentication?
Check Point Mobile for Windows, Check Point VPN Plugin for Windows 8.1 and Check Point Capsule VPN for Windows 10 do not support "two factor user authentication". (The limitation applies only to E80.64 and earlier in the context of Check Point Mobile for Windows.)
Is remote access a weak point?
Organizations must also make sure that their corporate network remains safe and that remote access does not become a weak point in their IT security.
Does Endpoint Security VPN include firewall?
Note: Endpoint Security VPN for Mac OS X includes a Desktop Firewall, but not Security Verification.
What is checkpoint remote access?
Check Point remote access solutions use IPsec and SSL encryption protocols to create secure connections. All Check Point clients can work through NAT devices, hotspots, and proxies in situations with complex topologies, such as airports or hotels. These are the types of installations for remote access solutions:
What is security verification?
Security Verification for Endpoint computers - Makes sure that devices connecting to the Security Gateway meet security requirements. Endpoint machines that are not compliant with the security policy have limited or no connectivity to corporate resources. Some Check Point solutions supply this.
What is secure connectivity?
Secure Connectivity - Traffic is encrypted between the client and VPN Security Gateway. After users authenticate, they can access the corporate resources that are permitted to them in the access policy. All Check Point solutions supply this.
What is a firewall desktop?
Desktop Firewall - Protects endpoint computers at all times with a centrally managed security policy. This is important because remote clients are not in the protected network and traffic to clients is only inspected if you have a Desktop Firewall. Some Check Point solutions supply this
What is client based application?
Client-based - Client application installed on endpoint computers and devices. The client supplies access to most types of corporate resources according to the access privileges of the user.
What is an on demand client?
On demand client - Users connect through a web browser and a client is installed when necessary. The client supplies access to most types of corporate resources according to the access privileges of the user.
Is remote access a weak point?
Organizations must also make sure that their corporate network remains safe and that remote access does not become a weak point in their IT security.