Maximum Concurrent VPN Sessions By Device Model
| Device Model | Maximum Concurrent Remote Access VPN Se ... |
| ASA 5555-X | 5000 |
| Firepower 1010 | 75 |
| Firepower 1120 | 150 |
| Firepower 1140 | 400 |
Full Answer
How do I set up a VPN on firepower Management Center?
On your Firepower Management Center web interface, choose Devices > VPN > Remote Access. Existing remote access policies are listed. Select a remote access VPN policy and click Edit . Click Add and specify the following in the Add Connection Profile window: Connection Profile —Provide a name that the remote users will use for VPN connections.
How do I configure Cisco AnyConnect for firepower threat defense?
Select the AnyConnect Client Image that the VPN users will use to connect to the remote access VPN. The Cisco AnyConnect Secure Mobility client provides secure SSL or IPSec (IKEv2) connections to the Firepower Threat Defense device for remote users with full VPN profiling to corporate resources.
How does firepower Threat Defense Support remote access VPNs?
Firepower Threat Defense devices can be configured to support Remote Access VPNs over SSL or IPsec IKEv2 by the Firepower Management Center. Functioning as secure gateways in this capacity, they authenticate remote users, authorize access, and encrypt data to provide secure connections to your network.
What types of VPN connections does the firepower Management Center support?
The Firepower Management Center supports the following types of VPN connections: Remote Access VPNs on Firepower Threat Defense devices. Remote access VPNs are secure, encrypted connections, or tunnels, between remote users and your company’s private network.
How does Cisco remote access VPN Work?
Remote and mobile users use the Cisco AnyConnect Secure VPN client to establish VPN sessions with the adaptive security appliance. The adaptive security appliance sends web traffic to the Web Security appliance along with information identifying the user by IP address and user name.
Does Cisco FTD support VPN?
VPN Topology The Firepower Management Center configures site-to-site VPNs on FTD devices only. You can select from three types of topologies, containing one or more VPN tunnels: • Point-to-point (PTP) deployments establish a VPN tunnel between two endpoints.
Does Cisco firepower support route based VPN?
In November 2020 Cisco released the Firepower Threat Defence (FTD) and Firepower Management Centre (FMC) version 6.7. Supported from this version is the long-awaited Virtual Tunnel Interface (VTI) for route-based site-to-site VPNs.
How do I create a FTD site to VPN?
2:2112:24Configuring IPSec Site to Site VPN in FTD using FMC - YouTubeYouTubeStart of suggested clipEnd of suggested clipIn the stop VPN topology view let's click Add VPN. And you have two options fire power device andMoreIn the stop VPN topology view let's click Add VPN. And you have two options fire power device and fire threat defense click on fire power threat defense to configure site-to-site VPN foresight to FTD.
How can I check Cisco firepower VPN status?
The simplest place to check the status of your VPN is in FMC. Browse to System -> Health -> Events. Then click on VPN Status. The remaining verification takes place on the FTD CLI.
How do I change my AnyConnect client profile?
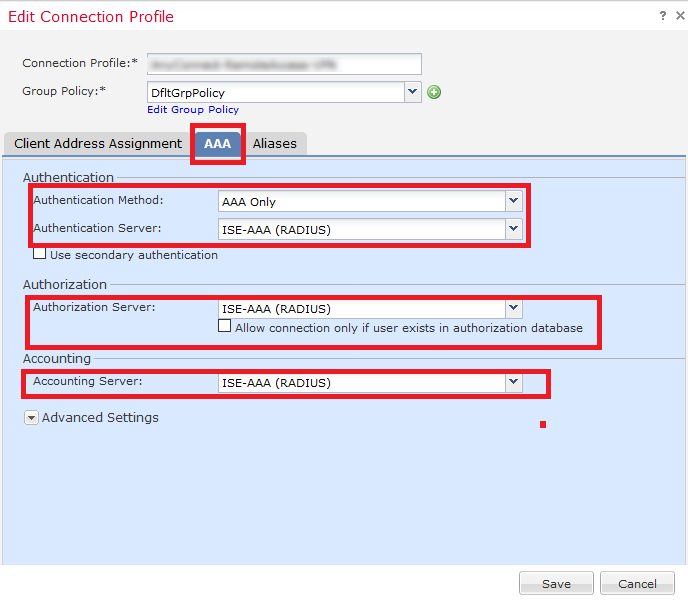
Navigate to Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles. Select the AnyConnect VPN profile in Connection Profiles and click Edit. The Edit AnyConnect Connection Profile window is displayed. Set the Method as AAA in the Authentication.
What is the difference between policy based VPN and route based VPN?
In a policy-based VPN configuration, the action must be permit and must include a tunnel. Route-based VPNs support the exchange of dynamic routing information through VPN tunnels. You can enable an instance of a dynamic routing protocol, such as OSPF, on an st0 interface that is bound to a VPN tunnel.
What VPN types are supported by ASA?
For VPN Services, the ASA 5500 Series provides a complete remote-access VPN solution that supports numerous connectivity options, including Cisco VPN Client for IP Security (IPSec), Cisco Clientless SSL VPN, network-aware site-to-site VPN connectivity, and Cisco AnyConnect VPN client.
How do I check my IPSec tunnel status in FTD?
In order to monitor the tunnel status, navigate to the CLI of the FTD or ASA. From the FTD CLI, verify phase-1 and phase-2 with the command show crypto ikev2 sa. This section provides information you can use in order to troubleshoot your configuration.
What is IKEv2?
IKEv2 (Internet Key Exchange version 2) is a VPN encryption protocol responsible for request and response actions. It handles the SA (security association) attribute within an authentication suite called IPSec.
What is PRF Sha?
The configuration is similar to the IKEv1 policy, the only new command is prf sha. PRF is the Pseudo Random Function algorithm which is the same as the integrity algorithm.
What is site to site VPN?
A site-to-site virtual private network (VPN) refers to a connection set up between multiple networks. This could be a corporate network where multiple offices work in conjunction with each other or a branch office network with a central office and multiple branch locations.
What is Sysopt connection permit VPN?
The sysopt connection permit-vpn command allows all the traffic that enters the security appliance through a VPN tunnel to bypass interface access lists, while a vpn-filter is applied to postdecrypted traffic after it exits a tunnel and to preencrypted traffic before it enters a tunnel.
What is IKEv2?
IKEv2 (Internet Key Exchange version 2) is a VPN encryption protocol responsible for request and response actions. It handles the SA (security association) attribute within an authentication suite called IPSec.
What is site to site VPN?
A site-to-site virtual private network (VPN) refers to a connection set up between multiple networks. This could be a corporate network where multiple offices work in conjunction with each other or a branch office network with a central office and multiple branch locations.
What is PRF Sha?
The configuration is similar to the IKEv1 policy, the only new command is prf sha. PRF is the Pseudo Random Function algorithm which is the same as the integrity algorithm.
What IPv6 policy does Firepower use?
If you configure more than one address assignment method, the Firepower Threat Defense device tries each of the options until it finds an IP address.
What is remote access VPN?
Remote Access VPN policy contains the connection profiles targeted for specific devices. These policies pertain to creating the tunnel itself, such as, how AAA is accomplished, and how addresses are assigned (DHCP or Address Pools) to VPN clients. They also include user attributes, which are identified in group policies configured on the Firepower Threat Defense device or obtained from a AAA server. A device also provides a default connection profile named DefaultWEBVPNGroup. The connection profile that is configured using the wizard appears in the list.
What is Firepower Threat Defense?
The Firepower Threat Defense device supports applying user authorization attributes (also called user entitlements or permissions) to VPN connections from the external RADIUS server that are configured for authentication and/or authorization in the remote access VPN policy.
What is AnyConnect profile?
An AnyConnect client profile is a group of configuration parameters stored in an XML file that the client uses to configure its operation and appearance. These parameters (XML tags) include the names and addresses of host computers and settings to enable more client features.
What is Cisco AnyConnect Secure Mobility?
The Cisco AnyConnect Secure Mobility client provides secure SSL or IPsec (IKEv2) connections to the Firepower Threat Defense device for remote users with full VPN profiling to corporate resources. Without a previously-installed client, remote users can enter the IP address of an interface configured to accept clientless VPN connections in their browser to download and install the AnyConnect client. The Firepower Threat Defense device downloads the client that matches the operating system of the remote computer. After downloading, the client installs and establishes a secure connection. In case of a previously installed client, when the user authenticates, the Firepower Threat Defense device, examines the version of the client, and upgrades the client if necessary.
What is the only VPN client?
The only supported VPN client is the Cisco AnyConnect Secure Mobility Client. No other clients or native VPNs are supported. Clientless VPN is not supported for VPN connectivity; it is only used to deploy the AnyConnect client using a web browser.
Can Firepower Threat Defense resolve IP addresses?
Without DNS, the devices cannot resolve AAA server names, named URLs, and CA Servers with FQDN or Hostnames. It can only resolve IP addresses.
Why create a VPN profile?
You can create a remote access VPN connection profile to allow your users to connect to your inside networks when they are on external networks, such as their home network . Create separate profiles to accommodate different authentication methods.
Where does remote access VPN problem originate?
Remote access VPN connection issues can originate in the client or in the Firepower Threat Defense device configuration. The following topics cover the main troubleshooting problems you might encounter.
How to use a VPN on a computer?
Step 1. Using a web browser, open https://ravpn-address , where ravpn-address is the IP address or hostname of the outside interface on which you are allowing VPN connections. You identify this interface when you configure the remote access VPN. The system prompts the user to log in. Step 2.
How to complete a VPN connection?
To complete a VPN connection, your users must install the AnyConnect client software. You can use your existing software distribution methods to install the software directly. Or, you can have users install the AnyConnect client directly from the Firepower Threat Defense device.
What is AnyConnect client profile?
AnyConnect client profiles are downloaded to clients along with the AnyConnect client software. These profiles define many client-related options, such as auto connect on startup and auto reconnect, and whether the end user is allowed to change the option from the AnyConnect client preferences and advanced settings.
Where is change of authorization policy configured?
Most of the Change of Authorization policy is configured in the ISE server. However, you must configure the FTD device to connect to ISE correctly. The following procedure explains how to configure the FTD side of the configuration.
What is Cisco ISE?
Cisco ISE has a client posture agent that assesses an endpoint's compliance for criteria such as processes, files, registry entries, antivirus protection, antispyware protection, and firewall software installed on the host. Administrators can then restrict network access until the endpoint is in compliance or can elevate local user privileges so they can establish remediation practices. ISE Posture performs a client-side evaluation. The client receives the posture requirement policy from ISE, performs the posture data collection, compares the results against the policy, and sends the assessment results back to ISE.
What certificates are needed for AnyConnect?
Certificates are essential when you configure AnyConnect. Only RSA based certificates are supported in SSL and IPSec. Elliptic Curve Digital Signature Algorithm certificates (ECDSA) are supported in IPSec, but it's not possible to deploy new AnyConnect package or XML profile when ECDSA based certificate is used. It means that you can use it for IPSec, but you will have to predeploy AnyConnect package and XML profile to every user and any change in XML profile will have to be manually reflected on each client (bug: CSCtx42595 ). Additionally the certificate should have Subject Alternative Name extension with DNS name and/or IP address to avoid errors in web browsers.
Can VPN traffic come from pool?
This means, that you need to allow traffic coming from pool of addresses on outside interface via Access Control Policy. Although the pre-filter or access-control rule is added intending to allow VPN traffic only, if clear-text traffic happens to match the rule criteria, it is erroneously permitted.
What is VPN in Firepower?
A virtual private network (VPN) connection establishes a secure tunnel between endpoints over a public network such as the Internet. This chapter applies to Remote Access and Site-to-site VPNs on Firepower Threat Defense devices.
What is remote access VPN?
Remote access VPNs are secure, encrypted connections, or tunnels, between remote users and your company’s private network. The connection consists of a VPN endpoint device, which is a workstation or mobile device with VPN client capabilities, and a VPN headend device, or secure gateway, at the edge of the corporate private network.
How does a VPN work point to point?
In a point-to-point VPN topology, two endpoints communicate directly with each other. You configure the two endpoints as peer devices, and either device can start the secured connection.
Why use PKI in VPN?
Using a PKI improves the manageability and scalability of your VPN since you do not have to configure pre-shared keys between all the encrypting devices. Instead, you individually enroll each participating device with a CA server, which is explicitly trusted to validate identities and create an identity certificate for the device. When this has been accomplished, each participating peer sends their identity certificate to the other peer to validate their identities and establish encrypted sessions with the public keys contained in the certificates. See Certificate Enrollment Objects for details on enrolling FTD devices.
How to validate a peer's certificate?
In order to validate a peer’s certificate, each participating device must retrieve the CA's certificate from the server. A CA certificate is used to sign other certificates. It is self-signed and called a root certificate. This certificate contains the public key of the CA, used to decrypt and validate the CA's digital signature and the contents of the received peer's certificate. The CA certificate may be obtained by:
What is the only VPN client?
The only supported VPN client is the Cisco AnyConnect Secure Mobility Client. No other clients or native VPNs are supported. Clientless VPN is not supported for VPN connectivity; it is only used to deploy the AnyConnect client using a web browser.
What is Cisco AnyConnect Secure Mobility?
The Cisco AnyConnect Secure Mobility client provides secure SSL or IPsec (IKEv2) connections to the Firepower Threat Defense device for remote users with full VPN profiling to corporate resources. Without a previously-installed client, remote users can enter the IP address of an interface configured to accept clientless VPN connections in their browser to download and install the AnyConnect client. The Firepower Threat Defense device downloads the client that matches the operating system of the remote computer. After downloading, the client installs and establishes a secure connection. In case of a previously installed client, when the user authenticates, the Firepower Threat Defense device, examines the version of the client, and upgrades the client if necessary.
What is AnyConnect profile?
An AnyConnect client profile is a group of configuration parameters stored in an XML file that the client uses to configure its operation and appearance. These parameters (XML tags) include the names and addresses of host computers and settings to enable more client features.
How to check VPN banner?
You can check the banner settings under Group Policy > General Settings> Banner. Edit the connect profile you have created for management VPN tunnel. Click Edit Group Policy> AnyConnect> Management Profile. Click the Management VPN Profiledrop-down and select the management profile file object you have created.
Can you disable VPN connection profile?
When you want to enforce a single connection profile on a user or user group, you can choose to disable the connection profile so that the group alias or URLs are not available for the users to select when they connect using the AnyConnect VPN client.
Is VPN load balancing disabled?
VPN load balancing is disabled by default. You must explicitly enable VPN load balancing. Only the FTD devices that are co-located can be added to a load-balancing group. A load-balancing group must have a minimum of two FTD devices.
Can Firepower Threat Defense resolve IP addresses?
Without DNS, the devices cannot resolve AAA server names, named URLs, and CA Servers with FQDN or Hostnames. It can only resolve IP addresses.
The Remote Access VPN Identity Source
Firepower Threat Defense provides secure gateway capabilities that support remote access SSL and IPsec-IKEv2 VPNs. The full tunnel client, AnyConnect Secure Mobility Client, provides secure SSL and IPsec-IKEv2 connections to the security gateway for remote users.
Troubleshoot the Remote Access VPN Identity Source
For other related troubleshooting information, see Troubleshoot Realms and User Downloads, Troubleshoot User Control, and VPN Troubleshooting for Firepower Threat Defense.
Introduction
Requirements
- Cisco recommends that you have knowledge of these topics: 1. Basic VPN, TLS and IKEv2 knowledge 2. Basic Authentication, Authorization, and Accounting (AAA) and RADIUS knowledge 3. Experience with Firepower Management Center
Components Used
- The information in this document is based on these software and hardware versions: 1. Cisco FTD 6.2.2 2. AnyConnect 4.5
Configuration
- 2. Remote access wizard
1. Go to Devices > VPN > Remote Access > Add a new configuration. 2. Name the profile according to your needs, select FTD device: 1. In step Connection Profile, type Connection Profile Name, select Authentication Server and Address Poolswhich you have created earlier: 1. Click o…
Connection
- To connect to FTD you need to open a browser, type DNS name or IP address pointing to the outside interface, in this example https://vpn.cisco.com. Youwill then have to login using credentials stored in RADIUS server and follow instructions on the screen. Once AnyConnect installs, you then need to put the same address in AnyConnect window and click Connect.
Limitations
- Currently unsupported on FTD, but available on ASA: 1. Double AAA Authentication 2. Dynamic Access Policy 3. Host Scan 4. ISE posture 5. RADIUS CoA 6. VPN load-balancer 7. Local authentication (Enhancement: CSCvf92680 ) 8. LDAP attribute map 9. AnyConnect customization 10. AnyConnect scripts 11. AnyConnect localization 12. Per-app VPN 13. SCEP proxy 14. WSA in…
Security Considerations
- You need to remember that by default, sysopt connection permit-vpn option is disabled. This means, that you need to allow traffic coming from pool of addresses on outside interface via Access Control Policy. Although the pre-filter or access-control rule is added intending to allow VPN traffic only, if clear-text traffic happens to match the rule criteria, it is erroneously permitted…