Here’s how to setup a Remote Access IPsec VPN on the Cisco Router IOS platform Step1. Define the authentication and authorization methods used. In this case, we’re defining a new group called VPN which will use the local database for authenticating and authorizing the user.
Full Answer
How is a VPN connection created with an IPsec server?
After the IPSec server has been configured, a VPN connection can be created with minimal configuration on an IPSec client, such as a supported Cisco 870 series access router. When the IPSec client initiates the VPN tunnel connection, the IPSec server pushes the IPSec policies to the IPSec client and creates the corresponding VPN tunnel connection.
How do I configure IPsec remote access?
†Set the connection type to IPSec remote access. †Configure the address assignment method, in the following example, address pool. †Configure an authentication method, in the following example, preshared key.
How do I configure the Cisco VPN client?
Complete these steps in order to configure the VPN Client 4.8: Choose Start > Programs > Cisco Systems VPN Client > VPN Client. Click New to launch the Create New VPN Connection Entry window. Enter the name of the Connection Entry along with a description. Enter the outside IP address of the router in the Host box.
How to configure a VPN using Easy VPN and an IPSEC tunnel?
Configuring a VPN Using Easy VPN and an IPSec Tunnel 1 Remote, networked users 2 VPN client—Cisco 870 series access route ... 3 Router—Providing the corporate office ne ... 4 VPN server—Easy VPN server; for example, ... 5 Corporate office with a network address ... 1 more rows ...

How do I enable IPSec on a Cisco router?
To configure the IPSec VPN tunnel on Cisco 881 ISR:Configure the ISAKMP Policy. ... Enable NAT Keepalive. ... Configure the IPSec Peer. ... Define the IPSec Transform Set. ... Enable IPSec Fragmentation. ... Configure the IPSec Profile. ... Create the Tunnel Interfaces. ... Create the Access Control List (ACL)More items...
How can we configure IPSec VPN?
Configuring authentication methodIn the administration interface, go to Interfaces.Click Add > VPN Tunnel.Type a name of the new tunnel.Set the tunnel as active and type the hostname of the remote endpoint. ... Select Type: IPsec.Select Preshared key and type the key.More items...
Does Cisco VPN use IPSec?
Remote access VPNs are used by remote clients to log in to a corporate network. The example in this chapter illustrates the configuration of a remote access VPN that uses the Cisco Easy VPN and an IPSec tunnel to configure and secure the connection between the remote client and the corporate network.
What is IPSec remote access VPN?
IPSec remote access is used to connect remote-access clients, such as a PC or small office, home office (SOHO) device (a small-end router or firewall appliance) to a corporate network.
What is the difference between VPN and IPsec?
The major difference between an IPsec VPN and an SSL VPN comes down to the network layers at which encryption and authentication are performed. IPsec operates at the network layer and can be used to encrypt data being sent between any systems that can be identified by IP addresses.
What is Cisco IPsec?
IPsec is a framework of open standards developed by the IETF. It provides security for the transmission of sensitive information over unprotected networks such as the Internet. IPsec acts at the network layer, protecting and authenticating IP packets between participating IPsec devices (“peers”), such as Cisco routers.
Is Cisco AnyConnect IPsec or SSL?
Anyconnect is the replacement for the old Cisco VPN client and supports SSL and IKEv2 IPsec. When it comes to SSL, the ASA offers two SSL VPN modes: Clientless WebVPN.
How does Cisco remote access VPN Work?
Remote and mobile users use the Cisco AnyConnect Secure VPN client to establish VPN sessions with the adaptive security appliance. The adaptive security appliance sends web traffic to the Web Security appliance along with information identifying the user by IP address and user name.
How does remote access VPN Work?
The remote access VPN does this by creating a tunnel between an organization's network and a remote user that is “virtually private,” even though the user may be in a public location. This is because the traffic is encrypted, which makes it unintelligible to any eavesdropper.
Can IPSec be used for remote access?
This guide describes step by step the configuration of a remote access to the Astaro Security Gateway by using IPSec. IPSec allows you to give individual hosts access to your network through an encrypted IPSec tunnel.
What ports need to be open for IPSec VPN?
Mobile VPN with IPSec requires the client to access the Firebox on UDP ports 500 and 4500, and ESP IP Protocol 50. This often requires a specific configuration on the client's internet gateway, so clients might not be able to connect from hotspots or with mobile Internet connections.
Is IPSec VPN better than SSL VPN?
When it comes to corporate VPNs that provide access to a company network rather than the internet, the general consensus is that IPSec is preferable for site-to-site VPNs, and SSL is better for remote access.
How IPSec works step by step?
Interesting traffic initiates the IPSec process—Traffic is deemed interesting when the IPSec security policy configured in the IPSec peers starts the IKE process....Step 1: Defining Interesting Traffic. ... Step 2: IKE Phase One. ... Step 3: IKE Phase Two. ... Step 4: IPSec Encrypted Tunnel. ... Step 5: Tunnel Termination.
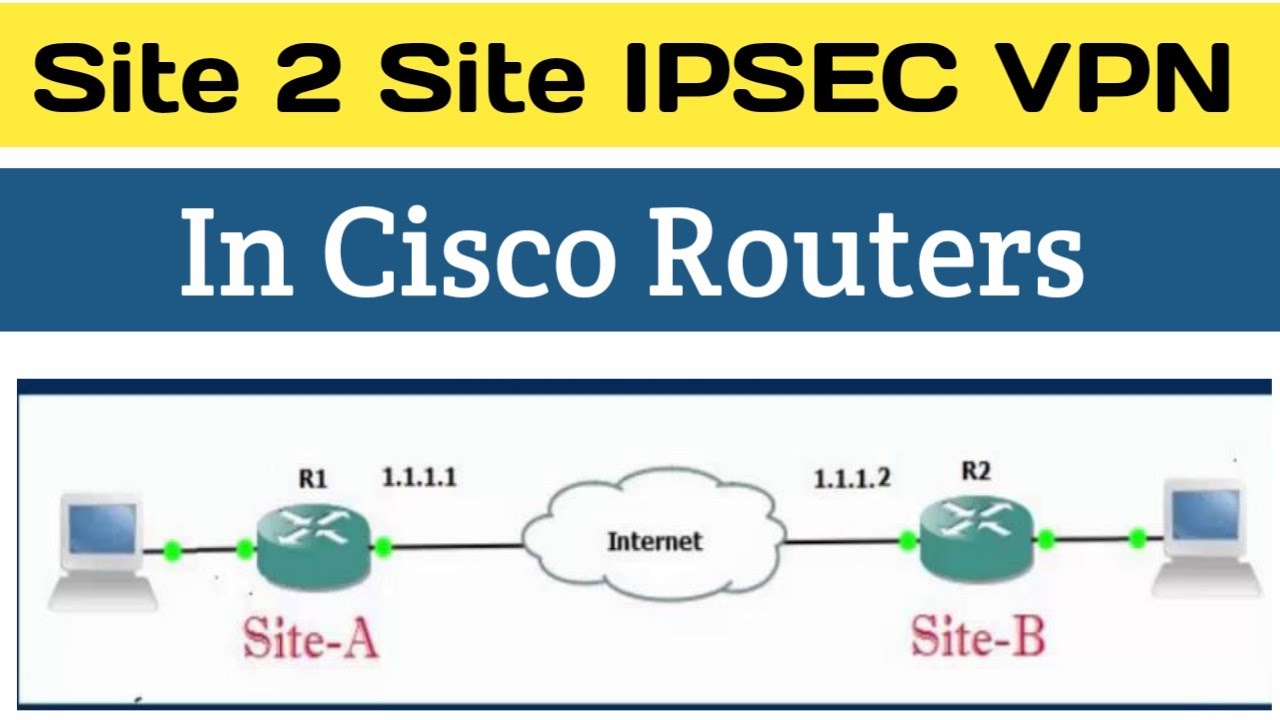
How many steps are there to configuring site to site IPSec VPNs?
Configure IPSec - 4 Simple Steps To configure IPSec we need to setup the following in order: Create extended ACL. Create IPSec Transform. Create Crypto Map.
How do I setup a VPN tunnel?
To establish a site-to-site VPN tunnel, complete the following configuration tasks:Add the subnet IP address objects for your local network and remote network. ... (Optional) Import the certificates for authentication between two peers. ... Enable the site-to-site VPN feature on the security appliance. ... Configure IKE policies.More items...
What is required when creating an IPSec VPN policy?
Creating an IPsec VPN connection Go to VPN > IPsec Connections > Select Wizard > Enter a name > Click Start. Select Site To Site as the connection type, select Head office, and the policy created earlier. Set the Authentication type to Preshared key. In Local subnet field, select the local LAN created earlier.
What is Cisco Easy VPN?
The Cisco Easy VPN client feature eliminates much of the tedious configuration work by implementing the Cisco Unity Client protocol. This protocol allows most VPN parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, WINS server addresses, and split-tunneling flags, to be defined at a VPN server, such as a Cisco VPN 3000 series concentrator that is acting as an IPSec server.
What are the two types of VPNs?
Two types of VPNs are supported—site-to-site and remote access. Site-to-site VPNs are used to connect branch offices to corporate offices, for example. Remote access VPNs are used by remote clients to log in to a corporate network. The example in this chapter illustrates the configuration of a remote access VPN that uses ...
What is a Cisco 870 router?
The Cisco 870 series routers support the creation of Virtual Private Networks (VPNs). Cisco routers and other broadband devices provide high-performance connections to the Internet, but many applications also require the security of VPN connections which perform a high level of authentication and which encrypt the data between two particular ...
Does Cisco 850 support VPN?
Note The material in this chapter does not apply to Cisco 850 series routers. Cisco 850 series routers do not support Cisco Easy VPN.
Can you negotiate with a peer in a security association?
Note With manually established security associations, there is no negotiation with the peer , and both sides must specify the same transform set.
Does Cisco Easy VPN support multiple destinations?
Note The Cisco Easy VPN client feature supports configuration of only one destination peer. If your application requires creation of multiple VPN tunnels, you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on both the client and the server.
What is VPN on Cisco router?
This chapter explains the basic tasks for configuring an IP-based, remote access Virtual Private Network (VPN) on a Cisco 7200 series router. In the remote access VPN business scenario, a remote user running VPN client software on a PC establishes a connection to the headquarters Cisco 7200 series router.
How to verify that authentication proxy is successfully configured on the router?
To verify that the authentication proxy is successfully configured on the router, ask a user to initiate an HTTP connection through the router. The user must have authentication and authorization configured at the AAA server. If the user authentication is successful, the firewall completes the HTTP connection for the user. If the authentication is unsuccessful, check the access list and the AAA server configurations.
What command to use to verify PPTP?
After you complete a connection, enter the show vpdn tunnel command or the show vpdn session command to verify your PPTP and MPPE configuration.The following example contains typical output:
What is Cisco IOS firewall proxy?
Using the Cisco IOS firewall authentication proxy feature , network administrators can apply specific security policies on a per-user basis. Users can be identified and authorized on the basis of their per-user policy, and access privileges tailored on an individual basis are possible, in contrast with general policy applied across multiple users.
What is the radiusserverkey command?
Sets the authentication and encryption key for communications between the router and the AAA server. For RADIUS servers use the radiusserverkey command.
What is authentication proxy?
With the authentication proxy feature, users can log into the network or access the Internet via HTTP, and their specific access profiles are automatically retrieved and applied from an authentication server. The user profiles are active only when there is active traffic from the authenticated users.
How to display user authentication entries?
Display the user authentication entries using the show ip auth-proxy cache command in privileged EXEC mode. The authentication proxy cache lists the host IP address, the source port number, the timeout value for the authentication proxy, and the state of the connection. If the authentication proxy state is HTTP_ESTAB, the user authentication was successful.
Where does the VPN client connect to?
The VPN Client gets connected with the router at the central site.
How to view VPN logs?
Launch the LogViewer on the VPN Client in order to view the logs. Make sure that the filter is set to High for all the configured classes. This is a sample log output:
What is crypto isakmp?
debug crypto isakmp —Displays debug information about IPSec connections, and shows the first set of attributes that is denied due to incompatibilities on both ends.
What happens when a router is unavailable?
When the primary RADIUS server becomes unavailable, the router will failover to the next active backup RADIUS server. The router will continue to use the secondary RADIUS server forever, even if the primary server is available. Usually the primary server is high performance and the preferred server.
Does Cisco use encryption?
Delivery of Cisco cryptographic products does not imply third-party authority to import , export, distribute or use encryption. Importers, exporters, distributors and users are responsible for compliance with U.S. and local country laws. By using this product you agree to comply with applicable laws and regulations.
Is IPSec VPN accounting available?
Note: IPSec VPN Accounting is now available. Refer to IPSec VPN Accounting for more information and sample configurations.
What is the command ezvpn-author group radius?
In this configuration the command ‘aaa authorization network ezvpn-author group radius’ tells us that the configuration for Easy VPN group (policies) must be downloaded from a RADIUS server.
What is the advantage of Easy VPN?
The main advantage of Easy VPN is that IPSec policies are centrally managed on the server (Head end router providing IPSec feature) and are pushed to client devices. This policy push is known as Mode Configuration. This requires minimum configuration on the end-user side. The IPSec policies can be configured on a RADIUS server and then downloaded to an Easy VPN server, further reducing configuration required on the Easy VPN server.
How many group policies do you need to configure a Radius server?
Let us be more specific about the requirement so that we can configure our RADIUS server. In our requirement we need to create two group policies:
What is a remote control policy?
Controlling policy for remote access through a RADIUS server is only a single example among multiple available. There is lot that can be achieved with a RADIUS server and AAA protocol. This not only helps in centralizing everything but helps you strengthen your security posture. If a policy needs to be updated, the time it takes to propagate the updated policies is greatly reduced. This could result in lowering operational costs in the long run.
Can two groups of remote users connect to the corporate network?
Now we are required to allow two sets or groups of remote users to connect to the corporate network. Each set must be assigned a different IP address. Most important, the remote users of one group should not be allowed to connect using the profile of the other group, because each group has a unique set of policies for accessing the corporate network.
Can you add a static route dynamically?
You can also instruct the device to add a static route dynamically for the connecting remote clients. In this example we have achieved it with the command ‘reverse-route’.
Is Cisco router a VPN?
Since this is client server architecture in which we have a Cisco router as an Easy VPN Server, performing the responsibility of a server, the client end responsibility is fulfilled by: