Is DarkComet a virus?
DarkComet is a widely known piece of malware. If a user installs an antivirus, or a darkcomet remover, they can un-infect their computer quickly. Its target machines are typically anything from Windows XP, all the way up to Windows 10.
Can remote access Trojans be detected?
AIDE—short for Advanced Intrusion Detection Environment—is a HIDS designed specifically to focus on rootkit detection and file signature comparisons, both of which are incredibly useful for detecting APTs like Remote Access Trojans.
What type of malware is DarkComet?
Remote Access Trojan (RAT)DarkComet is a Remote Access Trojan (RAT) application that may run in the background and silently collect information about the system, connected users, and network activity. Backdoor. DarkComet may attempt to steal stored credentials, usernames and passwords, and other personal and confidential information.
Is remote access Trojan a malware?
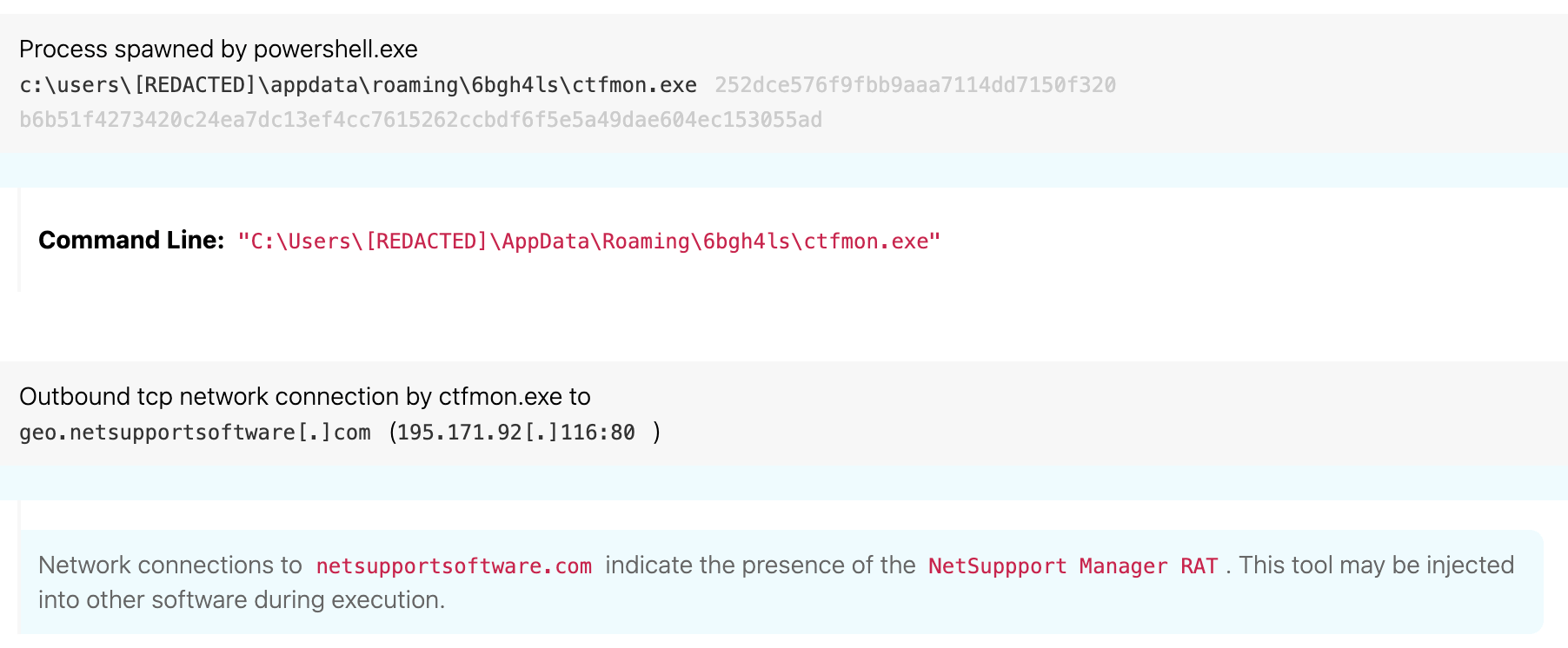
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
How are remote access Trojans delivered?
A remote access Trojan (RAT) is a malware program that includes a back door for administrative control over the target computer. RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment.
What is the best remote access Trojan?
10 Best Remote Access Software (Remote Control Software) In 2022Comparison of Top Remote Access Tools.#1) NinjaOne (Formerly NinjaRMM)#2) SolarWinds Dameware Remote Support.#3) Atera.#4) Supremo.#5) ManageEngine Remote Access Plus.#6) RemotePC.#7) TeamViewer.More items...•
When was DarkComet created?
2008DarkComet is one of the most famous RATs, developed by Jean-Pierre Lesueur in 2008.
What can NanoCore do?
NanoCore can provide the threat actor with information such as computer name and OS of the affected system. It also opens a backdoor that allows the threat actors to access the webcam and microphone, view the desktop, create internet message windows and offers other options.
What encryption does the DarkComet protocol used in the network traffic eg AES?
Encryption Details All command and control traffic is encrypted with a form of the RC4-256 algorithm.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
Can an Iphone get a remote access Trojan?
The iOS Trojan is smart and spies discretely, i.e. does not drain a battery. The RCS mobile Trojans are capable of performing all kinds of spying you can expect from such a tool, including location reporting, taking photos, spying on SMS, WhatsApp and other messengers, stealing contacts and so on.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
Can an Iphone get a remote access Trojan?
The iOS Trojan is smart and spies discretely, i.e. does not drain a battery. The RCS mobile Trojans are capable of performing all kinds of spying you can expect from such a tool, including location reporting, taking photos, spying on SMS, WhatsApp and other messengers, stealing contacts and so on.
Which virus that Cannot be detected by antivirus software is?
A stealth virus has an intelligent architecture, making it difficult to eliminate it completely from a computer system. The virus is smart enough to rename itself and send copies to a different drive or location, evading detection by the system's antivirus software.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
Can Norton detect RATs?
Antivirus software like Bitdefender, Kaspersky, Webroot, or Norton, can detect RATs and other types of malware if they infect your devices.
What are the fun functions of trojan?
Additionally, the trojan has a number of “fun functions” including, the Fun Manager – different types of fun functions, including: hiding the desktop, lock, task icons, sys tray icons, taskbar, start button, task manager, and open/close the CD tray.
What is a darkcomet?
DarkComet is a freely available remote access trojan (RAT) developed by independent programmer, “DarkCoderSC,” first observed in 2011, and is still considered to be one of the most common RATs used. It is marketed as a “tool” as opposed to a “trojan” as it is claimed to be for network administrator use; however, its functionality attracts hackers.
Is a trojan a tool?
It is marketed as a “tool” as opposed to a “trojan” as it is claimed to be for network administrator use; however, its functionality attracts hackers. The trojan uses Crypters to evade antivirus tools and can disable Task Manager, Registry Editor, Folder Options, Windows Firewall, and Windows User Account Control (UAC).
What is DarkComet?
DarkComet is the name of a remote access/administration tool (RAT). Programs of this type are designed to control systems through a remote network connection. I.e., to control computers and perform various tasks remotely using another computer.
How did DarkComet infiltrate my computer?
To trick people into downloading and installing programs such as DarkComet or malware, cyber criminals use spam campaigns, trojans, dubious file or software download channels, fake software update and/or unofficial activation tools.
How to avoid installation of malware?
Do not open files (attachments) or click links that are included in irrelevant emails, especially if they are received from unknown, suspicious addresses. Download software and files from official websites and use direct download links. Various third party downloaders, installers and other such tools should not be trusted or used.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically.
How to use Malwarebytes Anti Malware Nebula?
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints. Nebula endpoint tasks menu. Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found. On the Quarantine page you can see which threats were quarantined and restore them if necessary.
Does Backdoor DarkComet run in the background?
Backdoor.DarkComet may run silently in the background and may not provide any indication of infection to the user. Backdoor.DarkComet may also disable antivirus programs and other Microsoft Windows security features.
Is Backdoor.DarkComet a software?
Backdoor.DarkComet may be distributed using various methods. This software may be packaged with free online software, or could be disguised as a harmless program and distributed by email. Alternatively, this software may be installed by websites using software vulnerabilities. Infections that occur in this manner are usually silent and happen without user knowledge or consent.
What is a RAT trojan?
RAT trojan is typically installed on a computer without its owner’s knowledge and often as a trojan horse or payload. For example, it is usually downloaded invisibly with an email attachment, torrent files, weblinks, or a user-desired program like a game. While targeted attacks by a motivated attacker may deceive desired targets into installing RAT ...
What is a RAT?
A remote access trojan (RAT), also called cree pware, is a kind of malware that controls a system via a remote network connection. It infects the target computer through specially configured communication protocols and enables the attacker to gain unauthorized remote access to the victim. RAT trojan is typically installed on a computer without its ...
What is poison ivy rat keylogger?
PoisonIvy RAT keylogger, also called “Backdoor.Darkmoon”, enables keylogging, screen/ video capturing, system administrating, file transferring, password stealing, and traffic relaying. It was designed by a Chinese hacker around 2005 and has been applied in several prominent attacks including the Nitro attacks on chemical companies and the breach of the RSA SecurID authentication tool, both in 2011.
What does RAT stand for?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can access your system just like he has physical access to your device. So, the user can access your files, use your camera, and even turn off or turn on your machine.
What is the back orifice?
Back Orifice has 2 sequel variants, Back Orifice 2000 released in 1999 and Deep Back Orifice by French Canadian hacking organization QHA. 2. Sakula. Sakula, also known as Sakurel and VIPER, is another remote access trojan that first surfaced in November 2012. It was used in targeted intrusions throughout 2015.
Why do RATs use a randomized filename?
It is kind of difficult. RATs are covert by nature and may make use of a randomized filename or file path structure to try to prevent identification of itself. Commonly, a RAT worm virus does not show up in the lists of running programs or tasks and its actions are similar to those of legal programs.
Can you recover data after a RAT attack?
Luckily, you can still regain your data after malware RAT attacks if you have a backup copy of it. Yet, you have to make the copy before you lost the original files with a reliable and RAT-free tool such as MiniTool ShadowMaker, which is a professional and powerful backup program for Windows computers.
