Create a Remote Access Control Policy Definition In a two- to three-page essay, design and describe a remote access control policy that details the requirements for establishing secure access between remote offices located in Atlanta, San Francisco, Chicago, and Dallas.
Full Answer
What is a remote access policy?
Remote access is any connection made to an organization's internal network and systems from an external source by a device or host. Remote locations can be almost anywhere in the world, from the employee’s home to an off-site office, hotels, transportation hubs, and cafes. What Is a Remote Access (Control) Policy?
What is an access control policy?
An access control policy provides rules and guidelines structuring who can access data and resources at an organization. It takes the form of a document offering a high-level overview, and is then implemented via more specific rules and procedures. In this article, we’ll go over everything you need to include in an access control policy.
What is a remote access policy (rap)?
What Is a Network Security Policy? A remote access policy is commonly found as a subsection of a more broad network security policy (NSP). The network security policy provides the rules and policies for access to a business’s network.
What are the security guidelines for remote access?
Remote policies have guidelines for access that can include the following: Hardware and software configuration standards for remote access, including anti-malware, firewalls, and antivirus. Encryption policies. Information security, confidentiality, and email policies. Physical and virtual device security.
What should be in a remote access policy?
What Should You Address in a Remote Access Policy?Standardized hardware and software, including firewalls and antivirus/antimalware programs.Data and network encryption standards.Information security and confidentiality.Email usage.Physical and virtual device security.Network connectivity, e.g., VPN access.More items...•
How do I make a remote access control?
Allow Access to Use Remote Desktop ConnectionClick the Start menu from your desktop, and then click Control Panel.Click System and Security once the Control Panel opens.Click Allow remote access, located under the System tab.Click Select Users, located in the Remote Desktop section of the Remote tab.More items...•
What are the examples of remote user security policy best practices?
Best Practices For Remote Access SecurityEnable encryption. ... Install antivirus and anti-malware. ... Ensure all operating systems and applications are up to date. ... Enforce a strong password policy. ... Use Mobile Device Management (MDM) ... Use Virtual Private Network (VPN) ... Use two-factor authentication.More items...•
Which policy defines the security controls while working remotely?
ISO 27001 controls for remote working: A 6.2. 1 – Mobile device policy.
What is remote access control?
Remote access control refers to the ability to monitor and control access to a computer or network (such as a home computer or office network computer) anywhere and anytime. Employees can leverage this ability to work remotely away from the office while retaining access to a distant computer or network.
What is a remote system control?
In electronics, a remote control (also known as a remote or clicker) is an electronic device used to operate another device from a distance, usually wirelessly. In consumer electronics, a remote control can be used to operate devices such as a television set, DVD player or other home appliance.
What is an example of remote control operations for providing security to an organization?
Popular examples include Remote Desktop Protocol (RDP) and Virtual Network Computing (VNC). While remote desktop access can have convenience advantages, this method is not typically recommended as it introduces significant security risks to the corporate network.
What is a best practice for compliance in the remote access domain?
Instead, a best practice is to adopt the principle of least privilege, which means that access for all users should be blocked by default and enabled only for the specific accounts that require it. This will require more configuration, but it is well worth the added security benefits.
Why is a remote access policy definition a best practice for handling remote employees and authorized users who require remote access from home or on business trips?
A remote access policy aims to keep corporate data safe from exposure to hackers, malware, and other cybersecurity risks while allowing employees the flexibility to work from remote locations.
What policies are required for ISO 27001?
The following policies are required for ISO 27001 with links to the policy templates:Data Protection Policy.Data Retention Policy.Information Security Policy.Access Control Policy.Asset Management Policy.Risk Management Policy.Information Classification and Handling Policy.More items...
What are some best practices for securing your home workplace?
Security Tips for Employees Working From HomeSecure Your Home Office. ... Secure Your Home Router. ... Separate Work and Personal Devices. ... Encrypt Your Devices. ... Use Supported Operating Systems. ... Keep Your Operating System Up-To-Date. ... Keep Your Software Up-To-Date. ... Enable Automatic Locking.More items...•
How do I setup a remote access to an IP address?
Once you've set up the target PC to allow access and have the IP address, you can move to the remote computer. On it, open the Start Menu, start typing “Remote Desktop” and select Remote Desktop Connection when it appears in the search results. Then in the box that appears type the IP address and click Connect.
How do I set up Remote Desktop to control my computer from anywhere?
Just follow these steps:On the computer you want to access remotely, click the Start menu and search for "allow remote access". ... On your remote computer, go to the Start button and search for "Remote Desktop". ... Click "Connect." Log in with the username and password you use on your home computer to gain access.
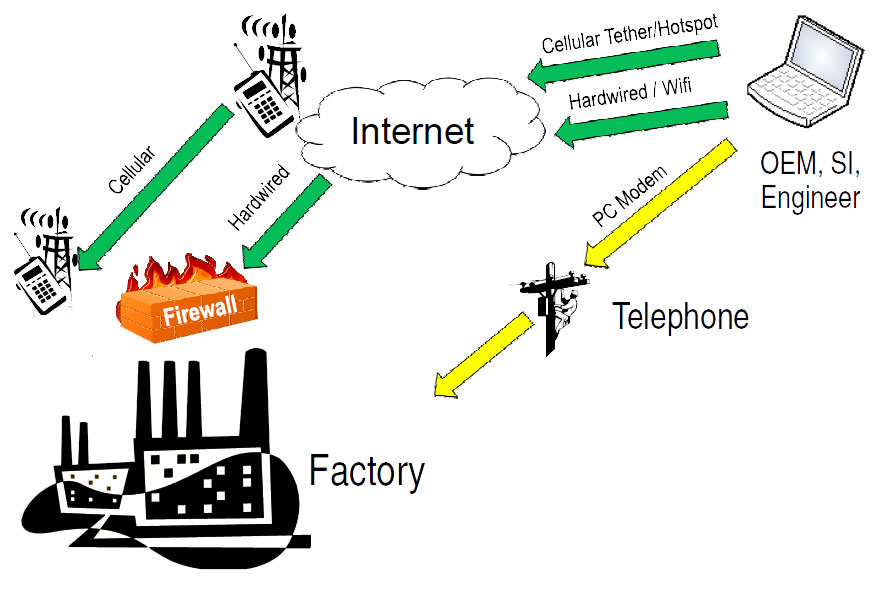
What methods can be used to connect remotely?
The primary remote access protocols in use today are the Serial Line Internet Protocol (SLIP), Point-to-Point Protocol (PPP), Point-to-Point Protocol over Ethernet (PPPoE), Point-to-Point Tunneling Protocol (PPTP), Remote Access Services (RAS), and Remote Desktop Protocol (RDP).
Do you need static IP for remote access?
In order to access your computer or device remotely, you will need to point your device(s) to a static IP address. Static IP addresses are often very expensive, and many Internet Service Providers (ISPs) don't even offer them to residential customers. The easy and (free) answer is to setup dynamic DNS.
What Is Remote Access?
Remote access is any connection made to an organization's internal network and systems from an external source by a device or host. Remote locations can be almost anywhere in the world, from the employee’s home to an off-site office, hotels, transportation hubs, and cafes.
Why Is a Remote Access Policy Necessary?
The numerous types of mobile devices and the different ways to connect pose challenges for the IT department. Devices can include cell phones, tablets, laptops, and any other device a remote worker relies on to conduct business. They can be company owned and secured, personally owned and authorized by a Bring Your Own Device (BYOD) policy, or a combination. Each class of device has its own set of security challenges. According to the National Institute for Standards and Technology’s Guidelines for Managing the Security of Mobile Devices in the Enterprise, “…Security controls available for laptops today are quite different than those available for smartphones, tablets, and other mobile device types.” Since different devices demand different controls, the policy has to detail what is allowed, compliant, and secure. The policy should answer the following questions:
What Problems Arise Without a Remote Access Policy?
Therefore, consequences for misuse can also be clearly outlined to compel compliance and appropriate precautions for data use and access. Elements such as firewalls, connectivity guidelines, personal use restrictions, and antivirus updates can help IT prevent both malicious and accidental loss and disruption of corporate information assets. The remote access control policies also provide protections for confidentiality, intellectual property, and information compliance.
What is smartsheet in healthcare?
Smartsheet is a work execution platform that enables healthcare companies to improve data safety, manage security processes, and keep privacy in check. Securely track and share confidential information with authorized users, mange control of user access, and increase visibility into who has access to what business-critical information, while meeting or exceeding all of HIPAA’s regulatory requirements. Rest assured that your assets are encrypted and stored under strict security requirements, eliminating the threat of cyberattacks and data loss, while still enabling medical professionals to access the information they need, anytime, anywhere.
What is VPN policy?
Policies for VPN remote access can be standardized. These policies “shore up” and prevent the use of rogue devices and access by non-authorized users , including the worker's family members or housemates. The policy also enforces proper email protocols to protect information from being sent through unsecured or untrusted sources, and also provides rules that limit or prohibit split tunnel configurations that allow mobile users to access both secure and unsecure networks simultaneously.
What is telecommuting?
“Telecommuting,” a term coined in the 1970s, has experienced explosive growth in today’s era of mobile connectivity. Now called distributed offices, remote work, telework, mobile work, smart work, and work shifting, many people are finding flexibility and increased productivity conducting business away from a centralized office environment. Researchers have long studied the benefits of remote work - from the successes that remote work had on traffic reduction during the 1984 Los Angeles Olympics to the 2016 findings by a Gallup survey on the increased hours for remote work.
What percentage of people work remotely?
According to research conducted by Gallup, 43 percent of workers in the U.S. worked remotely at least some of the time in 2016. Remote workers report higher job satisfaction and flexibility, experience fewer distractions and interruptions, and are more productive. Companies experience less absenteeism, less stress on office accommodations, and realize greater employee retention. A recent New York Times article found that finance, insurance, real estate, and transportation were most likely to have and support remote work (retail and education were least likely candidates). The trend is only increasing: the 2016 Gallup poll also found that those who work remotely log more hours away from the office than was reported in their 2012 findings. Not only are people logging more hours, but remote workers are saving money when it comes to commuting costs and businesses are saving on office space expenses.
Why you need a remote access policy
Access to IT and business resources -- data, databases, systems and networks -- must be protected from unauthorized and potentially damaging attacks. Securing access to company resources from employees working remotely ensures IT assets and employees are shielded from potential disruptions.
How to create a remote access security policy
Remote access security policies should be developed by a cross-functional team to address operational, legal, competitive and other issues associated with remote access to information resources. The team should coordinate with internal departments for input on their remote access requirements and with HR to ensure uniform compliance by employees.
Remote access security policy sample
A remote access security policy can be simple. In fact, a few paragraphs added to an existing cybersecurity policy may be sufficient. The policy language should define remote access security activities and how they build on existing security policies and procedures, noting the metrics discussed previously.
What to Include in an Access Control Policy Document
Our example from Loyola University Chicago makes clear who the policy applies to (“faculty, staff, students, contractors and vendors”) and how it applies – specifically, when they connect to systems that deal with Loyola Protected Data.
Implementation
An access control policy on its own doesn’t do much. For it to be effective, it must be supported by methods, procedures, and some form of access control model.
Conclusion
The contents of your access control policy depend largely on the needs of your organization. Hopefully this article gives you an idea of what you should include when writing an access control policy document.
What Is a Remote Access Policy?
For example, sales personnel can now use tablets and other mobile devices to connect remotely to their office networks while on client calls and bring up data that may be important for closing deals . Recent events have further boosted the number of remote workers to an estimated 42% of the US workforce.
What are the considerations when formulating a remote access policy?
Other considerations when formulating a remote access policy include but are not limited to the following: Standardized hardware and software, including firewalls and antivirus/antimalware programs. Data and network encryption standards. Information security and confidentiality. Email usage.
Why Is a Remote Access Policy Important?
If a remote access policy is not in place, such risky behavior could go on unmitigated, without the organization finding out about it until after the occurrence of a breach.
What is remote work?
Remote work has brought with it a few challenges, including potential computer and network security risks. There is a real need for guidelines surrounding remote access, along with other policies. A remote access policy serves as a guide for remote users connecting to the network. It extends the policies governing network and computer use in ...
Why is password policy important?
It helps ensure that only those users who need it are given network access, as long as their devices are also compliant with the guidelines. When implemented properly, it helps safeguard the network from potential security threats.
What is RAS in IT?
Parallels® Remote Application Server (RAS) provides secure remote access for your networks out of the box. It features granular permission policies that enable administrators to enforce access restrictions and settings based on the end-users device or Active Directory group, helping ease the workloads of IT administrators by not requiring any further configuration.
How to ensure that you do not miss anything when updating your remote access policy?
To ensure that you do not miss anything when updating your remote access policy, consider your organizational, legal, contractual and regulatory obligations when you compile the list of policy requirements. After that, identify the procedural and technical controls required to fulfill the policy, making sure to reinforce or replace existing controls that have not been effective.
What is remote access in a company name?
Remote access is defined as any connection to [COMPANY NAME]’s internal network from a location outside of any affiliated company offices.
Why is remote access important?
Today, every organization should have a robust remote access policy that provides employees with clear direction on how to connect securely when at home or on the road. As remote work opportunities increase and travel remains a big part of corporate life, it’s more important than ever for organizations to ensure their employees have a secure means of accessing critical corporate data from any location.
How should VPN usage be monitored?
Monitoring. Remote access and VPN usage should be logged and monitored in a central database and reviewed regularly to detect anomalies and make changes to remote access privileges.
How long do remote users have to log in?
Remote access must be logged in a central database and kept for a period of at least 30 days. Access logs must be reviewed regularly.
What is the purpose of the Company Name policy?
The intent of this policy is to establish guidelines specifically pertaining to remote access to [COMPANY NAME]’s internal network. Preventing unauthorized access to company data from insecure networks is of utmost importance to [COMPANY NAME]. This policy is designed to ensure remote and/or traveling employees have the ability to securely connect to the corporate network without fear of threat and to provide the Company with an additional means of monitoring and controlling access to the internal network.
What to do if your connection is compromised?
If you believe your connection may have been compromised, please immediately report the incident to [RELEVANT CONTACT].
Is multifactor authentication required for VPN?
And to make it even stronger, we recommend multi-factor authentication as a requirement for VPN access. Restricted use. Remote access privileges shouldn’t be given out in the office like candy, but rather on an as-needed basis.
What is the purpose of remote access policy?
Hence, the purpose of this policy is to define standards for connecting to the group’s network from any host. These standards are designed to minimize the potential exposure to the group from damages, which may result from unauthorized use of the group resources. Damages include the loss of sensitive or company confidential data, intellectual property, damage to public image, damage to critical group internal systems, etc.
What is the Organization Group policy?
This policy applies to all Organization Group employees, contractors and vendors with corporate owned computers or workstations used to connect to the Group’s network. This policy applies to remote access connections used to do work on behalf of the Group, including reading or sending email, viewing intranet web resources and network/system/application support.
What is the purpose of e-Citrix?
The main objective of this policy is to allow Organization IT Support staff, selected vendors and approved business users to access Organization resources through remote access. The current infrastructure through e-Citrix technology allows remote access to Organization’s enterprise application system.
Can IT support staff access applications?
a) IT Support staff are allowed remote access for applications for support purposes. IT Managers are advised to allow remote access only on a “need to have” basis based on Classification of Business Functions in Appendix A.
Can IT Security provide remote support?
c) IT Remote Support Services should not be provided for application with business function that has been classified as “Required” or “Non -Critical”. IT Security does not recommend remote support services for such applications to reduce the Groups’ exposure to unnecessary outside threats. However, such application may be allowed remote support services on an ad-hoc basis for a limited time period and approved by the Organization IT Management.