Can a Trojan give remote access?
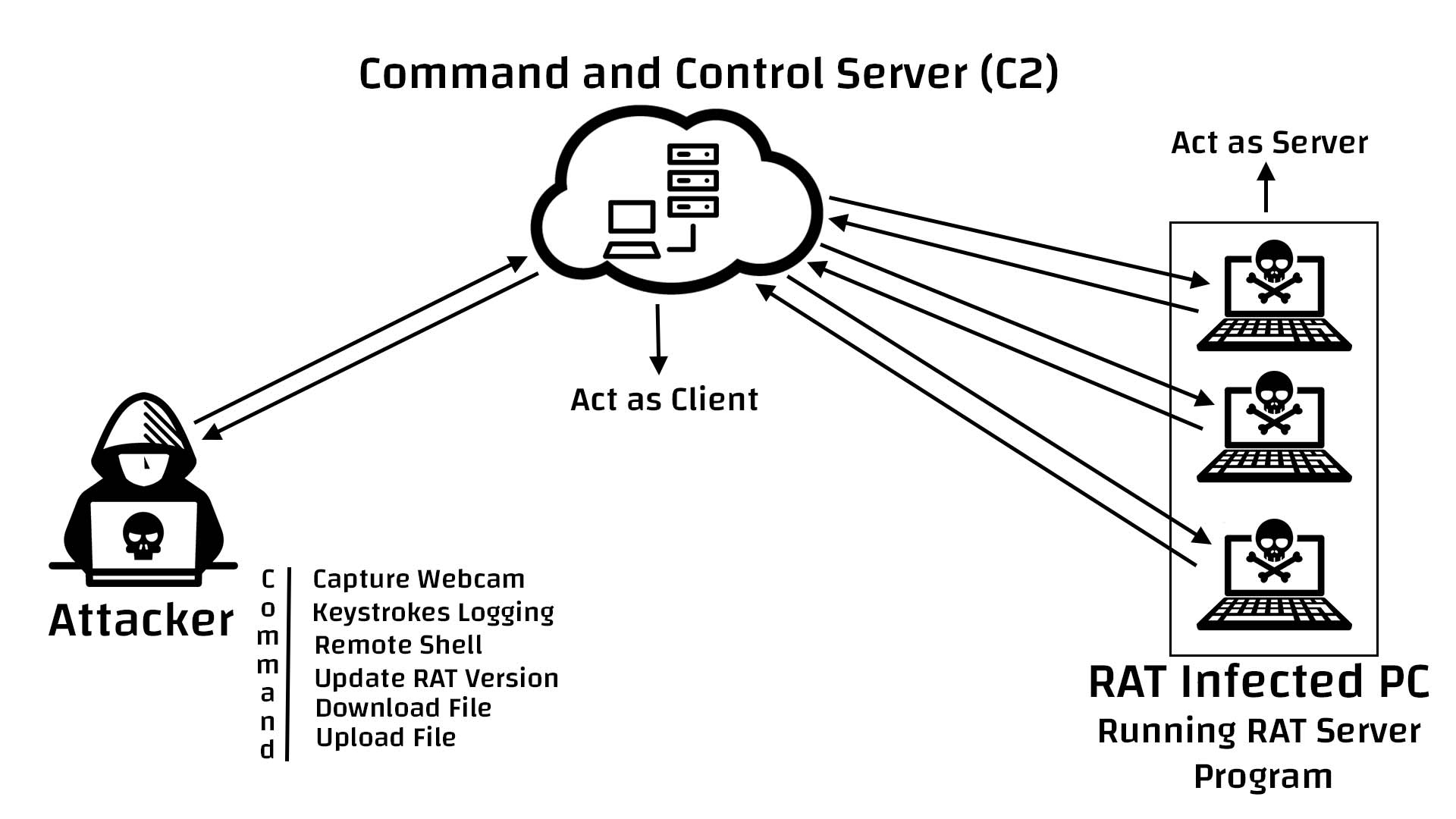
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Can you get a virus from remote access?
Many remote access software solutions don't scan the remote computer for viruses or malware. If your home or work PC has been infected, and you're using it to access your office network remotely, then a hacker could easily install malware onto your business's servers and spread to every machine in your office.
Can Kaspersky detect remote access Trojan?
Put a good antivirus on your smartphone. For example, Kaspersky Internet Security for Android not only finds and removes Trojans, but also blocks websites with malware and mobile subscriptions.
What are the variant of remote access Trojan?
There are a large number of Remote Access Trojans. Some are more well-known than others. SubSeven, Back Orifice, ProRat, Turkojan, and Poison-Ivy are established programs. Others, such as CyberGate, DarkComet, Optix, Shark, and VorteX Rat have a smaller distribution and utilization.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
What happens if you give someone remote access to your computer?
This can be even worse than just conning you out of money, as undetected malware can allow hackers to steal your identity, including your passwords and financial information, over and over again, even if you get new passwords and account numbers.
Does factory reset remove Trojans?
In short, yes, a factory reset will usually remove viruses … but (there's always a 'but' isn't there?) not always. Due to the wide variety and ever evolving nature of computer viruses, it's impossible to say for sure that a factory reset will be the answer to curing your device from a malware infection.
Can Windows Defender remove Trojan?
Windows Defender comes packed with the Windows 10 update and offers top-notch antimalware protection to keep your device and data safe. Although, Windows Defender is not capable of handling all kinds of viruses, malware, trojan, and other security threats.
Can Trojan virus be removed?
Trojan viruses can be removed in various ways. If you know which software contains the malware, you can simply uninstall it. However, the most effective way to remove all traces of a Trojan virus is to install antivirus software capable of detecting and removing Trojans.
What are the main features of a remote access Trojan?
RAT (remote access Trojan)Monitoring user behavior through keyloggers or other spyware.Accessing confidential information, such as credit card and social security numbers.Activating a system's webcam and recording video.Taking screenshots.Distributing viruses and other malware.Formatting drives.More items...
Which is the best remote access Trojan?
Blackshades is a Trojan which is widely used by hackers to gain access to any system remotely. This tool frequently attacks the Windows-based operating system for access.
What was the first remote access Trojan?
The oldest RAT was first developed in 1996 [10], however legitimate remote access tools were first created in 1989 [11]. Since then, the number of RATs has grown rapidly. The first phase was marked by home-made RATs. In these years, everyone made their own RAT, however these did not prosper and were not heavily used.
Can a virus pass through TeamViewer?
The infected computer is controlled via TeamViewer. Cybercriminals can connect to the remote computer (they know the ID and password for TeamViewer) or they can send commands via the TeamViewer chat, to basically do whatever they please on the infected machine.
Can someone hack into your computer using TeamViewer?
If you are using TeamViewer, then beware and make sure you're running the latest version of the popular remote desktop connection software for Windows.
Can you get a virus from connecting to VPN?
As long as you are using a reliable VPN service with some powerful encryption and well-secured servers, there is nothing to worry about. It is highly unlikely that hackers will try to infect a VPN connection with malware and viruses in the first place since that is too much hassle for them.
Can you get a virus from AnyDesk?
Therefore, the presence of AnyDesk's modified version can lead to high-risk computer infections and serious privacy issues. The desktop shortcut of the malicious version is called "AnyDask" and its entry in the list of installed programs is "AnyDeskApp".
What is RAT software?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can ac...
What’s the difference between the RAT computer virus and RAT software?
As for functions, there is no difference between the two. Yet, while remote administration tool is for legit usage, RAT connotes malicious and crim...
What are the popular remote access applications?
The common remote desktop tools include but are not limited to TeamViewer, AnyDesk, Chrome Remote Desktop, ConnectWise Control, Splashtop Business...
How are Remote Access Trojans Useful to Hackers?
Attackers using remote control malware cut power to 80,000 people by remotely accessing a computer authenticated into SCADA (supervisor y control and data acquisition) machines that controlled the country’s utility infrastructure. RAT software made it possible for the attacker to access sensitive resources through bypassing the authenticated user's elevated privileges on the network. Having access to critical machines that control city resources and infrastructure is one of the biggest dangers of RAT malware.
Why do attackers use remote devices?
Instead of storing the content on their own servers and cloud devices, attackers use targeted stolen devices so that they can avoid having accounts and servers shut down for illegal content.
What happens if you remove the internet from your computer?
Removing the Internet connection from the device disables remote access to your system by an attacker. After the device can no longer connect to the Internet, use your installed anti-malware program to remove it from local storage and memory. Unless you have monitoring configured on your computer, you won't know which data and files transferred to an attacker. You should always change passwords across all accounts, especially financial accounts, after removing malware from your system.
What is remote control software?
Legitimate remote-control software exists to enable an administrator to control a device remotely. For example, administrators use Remote Desktop Protocol (RDP) configured on a Windows server to remotely manage a system physically located at another site such as a data center. Physical access to the data center isn’t available to administrators, so RDP gives them access to configure the server and manage it for corporate productivity.
What Is The Best Trojan Remote Access?
Hackers commonly use Blackshades to gain remote access to computers. Windows-based operating systems are frequently targeted by this tool. The Trojan has infected 500,000 systems worldwide until now.
Where Are Remote Access Trojans Used?
Malware developers use Remote Access Trojan (RAT) tools to gain full access and control over a user’s computer, including mouse and keyboard control, file access, and network resources.
What Can You Do With A Remote Access Tool?
The remote access programs and tools (sometimes called RATs) allow remote access and manipulation of systems from another location. All types of users can use remote access programs to access files and data on remote computers, and many of them are legitimate tools.
What Is Trojan Ddos?
An infected computer is used to launch a DoS attack from a pre-defined address using this type of malicious program. The malicious user infects a number of computers with this type of Trojan in advance (for example, as part of a mass spam mailing) in order to conduct a successful DoS attack.
What Is The Purpose Of A Trojan Horse?
In general, a Trojan is designed to damage, disrupt, steal, or in general cause some other harm to your data or network.
How do remote access Trojans work?
The Remote Access Trojans get themselves downloaded on a device if the victims click on any attachment in an email or from a game. It enables the attacker to get control over the device and monitor the activities or gaining remote access. This RAT makes itself undetected on the device, and they remain in the device for a longer period of time for getting data that may be confidential.
What is the most powerful Trojan?
One of the most powerful Trojans that are popularly used by the attacker or hacker is Remote Access Trojan. This is mostly used for malicious purposes. This Trojan ensures the stealthy way of accumulating data by making itself undetected. Now, these Trojans have the capacity to perform various functions that damages the victim.
What is the advantage of remote access?
Advantage of Remote Access Trojans : It can be used to capture screenshots. The attacker can activate the webcam, or they can record video. The RAT can be used to delete the files or alter files in the system. It can also be used to capture screenshots.
How Is A Remote Access Trojan Executed?
An attacker uses a Trojan to execute a program file on a system. Once the user attempts to open the file, the Trojan is executed, and some dangerous actions are taken. A remote access Trojan program uses a backdoor to control the target machine with administrative privileges.
What Is A Remote Trojan?
A Remote Access Trojan (RAT) is a program that allows malware developers to gain full control over a user’s computer, including mouse and keyboard control, file access, and network resources.
What Is The Best Remote Access Tool?
It is a tool for viewing videos with TeamViewer. With TeamViewer, remote access and shared meeting features are combined in a single secure app, and its elegant interface hides most of its complexity. For enterprise and corporate use, it is our top pick for remote access software.
What Is An Example Of A Trojan Virus?
A number of trojans are known to be malicious in government, including the Swiss MiniPanzer and MegaPanzer, as well as the German “state trojan” nicknamed R2D2. Governmentware in Germany exploits security gaps that are unknown to the general public and accesses smartphone data before it is encrypted.
What is a Git Repository?
A Git repository refers to an online container where your source-code can be stored, contributed to, and managed over time. It is analogous to a smart folder on your workstation which keeps track of all the changes that has been made to it ever since its initiation.
How to set-up a Git Repository on GitHub
After clicking on New, you are given the following fields to fill and initialize your new repository. The repository could either be Private (restricted to contributors only) or Public (freely available to all).
Cloning (downloading) your repository
You could either simply download your repository using the Download ZIP option or introduce yourself to a world of limitless possibilities by using the Command Line Interface (CLI) for Git. If you don’t already have Git installed on your system, you may refer to this amazing guide here.
Cloning a GitHub repository using CLI
The following example illustrates a simple cloning of the repository using just the URL. But in case you want to put the entire structure into a folder name of your choice, you could add the destination directory parameter as well.
What are Remotes?
In contrast to a local repository (offline), a remote is a reference to a repository which is hosted on a cloud platform used by GitHub. https://github.com/ss-is-master-chief/MyGitHubRepository.git is an example of such a repository we have created previously and can be referenced using the URL.
What are Git States?
Git States refer to which state your modified files are currently in. For example, once you have made some changes to the `README.md` file, the file is now `modified`. But this doesn’t mean, we can upload the changes to the repository right away.
Merging
Let us create a new branch called new_branch and make some changes to it by creating a new file called new_branch_file.txt. We have added the line “This is a new branch file” to the new_branch_file.txt.
