
A remote-access scam starts with you getting an email, phone call, or text saying that you’re being charged a certain amount for a software product — typically, an antivirus like McAfee, Trend Micro, or Norton.
What is a remote access scam?
Remote access scams are a unique scenario where victims are socially engineered to provide remote access to their computer via a legitimate remote access tool such as TeamViewer, LogMeIn, Go-To-Meeting, or a similar remote desktop software.
What happens when you get a call from a computer scammer?
The caller will request remote access to your computer to ‘find out what the problem is’. The scammer may try to talk you into buying unnecessary software or a service to ‘fix’ the computer, or they may ask you for your personal details and your bank or credit card details.
How do you spot a tech support scam?
It's simple. If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam. Tech companies just don't operate that way. But tech support scammers do.
What are the signs of unwanted remote access to computer?
They ask you to buy software or sign up to a service to fix the computer. They ask for your personal details and your bank or credit card details. The caller is very persistent and may become abusive. Never give an unsolicited caller remote access to your computer.
Can you be scammed through your email address?
They can also send you emails impersonating someone else or a company to try to sell you goods or services that don't exist, which is known as phishing. Scammers can use phishing emails to access your email account too. “When a hacker knows your email address, they have half of your confidential information.
What can a scammer get from your email?
Scammers use email or text messages to trick you into giving them your personal information. They may try to steal your passwords, account numbers, or Social Security numbers. If they get that information, they could gain access to your email, bank, or other accounts.
What can a scammer do with AnyDesk?
AnyDesk is used legitimately by millions of IT professionals worldwide, to remotely connect to their clients' devices to help with technical issues. However, scammers can try to misuse AnyDesk (or any other remote access software) to connect to your computer and steal data, access codes, and even money.
Can someone hack my bank account with my email address?
It's also possible hackers could use your email account to gain access to your bank account or credit card information, draining funds from an account, or racking up charges. They might even use your email and password to sign up for online sites and services, sticking you with monthly fees in the process.
Should I delete my email if it was hacked?
If you have been hacked several times and your email provider isn't mitigating the amount of spam you are receiving, then consider starting afresh but don't delete your email address! Many experts do warn against deleting email accounts as most email providers will recycle your old email address.
What happens when a scammer gets access to your computer?
If you gave permission to the caller to access your computer, you should no longer consider it to be safe or clean. They might have installed programs, changed settings, or even installed a virus. In short, you can no longer trust it.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
How do I completely remove AnyDesk?
Uninstallation via the “Control Panel”Go to Start and open Control Panel.Select the Programs tab.Click on “Programs and Features”.Find AnyDesk among the programs.In the window that appears, click “Delete”.
Should I worry about a sextortion email?
First, if a “sextortion” email appears in your inbox, stay calm. Do not answer it and do not pay money to the attacker. Nobody will actually blackmail you; it's just spam. Even if you get an email that looks like it was sent from your own account, ignore it.
What can someone do with an email without password?
If a hacker wanted to try breaking into one of your online accounts, knowing your email address is a solid first step. Obviously, they can't log in without your password, but by knowing your email address, they could target you with phishing emails – malicious attachments that install malware on your machine.
Should I be worried about sextortion?
Sextortion is a serious crime that involves a perpetrator threatening to publish private and explicit information or material about you (or share it with your friends and family) if you do not give in to their demands. These demands usually involve sexual images, money, or sexual favors.
Can someone use my email address without me knowing it?
For convenience, your browser or email program can remember your password. If you allow this, your email is only as secure as your PC. Anyone who can access your PC can access your email. Nowadays, of course, the simplest way to hack someone's email is to use a phishing attack.
What is remote access scam?
Remote access scams try to convince you that you have a computer or internet problem and that you need to buy new software to fix the problem.
What to do if you think you have provided your account details to a scammer?
If you think you have provided your account details to a scammer, contact your bank or financial institution immediately.
What is malware scam?
Malware tricks you into installing software that allows scammers to access your files and track what you are doing, while ransomware demands payment to ‘unlock’ your computer or files.
How to protect your computer from spyware?
Make sure your computer is protected with regularly updated anti-virus and anti-spyware software, and a good firewall. Research first and only purchase software from a source that you know and trust.
Can a scammer be abusive?
The scammer may initially sound professional and knowledgeable—however they will be very persistent and may become abusive if you don't do what they ask.
How to stop remote access?
1. Shut down and disconnect your device from the Internet. That puts an absolute stop on any external meddling. It also often automatically revokes remote access for when you restart.
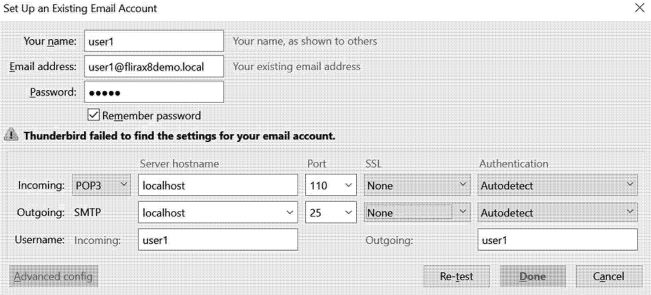
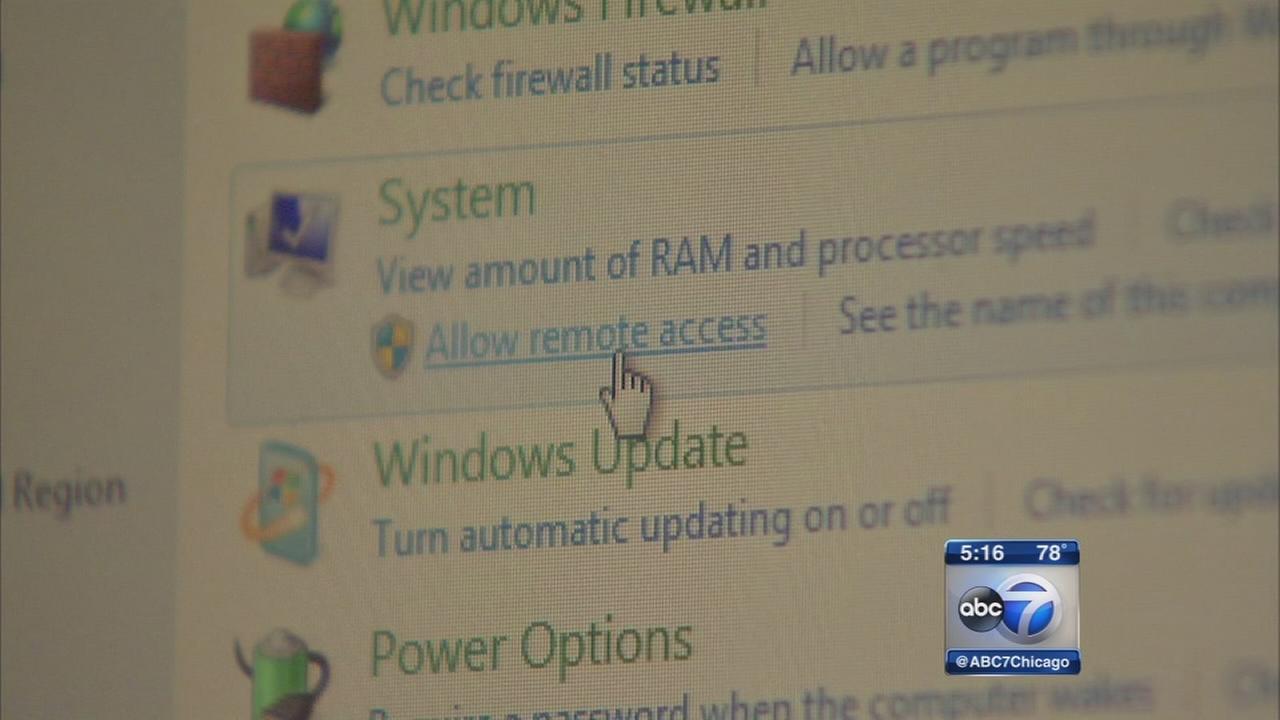
What is remote access on a PC?
You probably know what "remote access" is, but for those who don't, it's a feature of Windows that enables someone in another location to access your PC via the Internet.
How do I know whether a number I see is a fake Microsoft tech support number?
One of the favorite scam techniques is for tech support scammers to give you fake phone numbers they claim are a correct Microsoft tech support number. Don't fall for that scam. See above for the best way to find the correct Microsoft tech support number.
How many people fall victim to Microsoft scams?
According to Microsoft's Digital Crime Unit, some 3.3 million people fall victim to the tech support scam every year, costing victims around $1.5 billion.
How do you know if you're a victim of a scam?
How will you know you're one of those victims? It's simple. If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam.
What credit monitoring agencies freeze credit applications?
9. Put a freeze on credit applications via the three credit monitoring agencies -- Equifax, Experian and TransUnion . This will cost a few dollars but is worth it. Each of the bureaus has its own "credit lock" service but you might find the following article useful: Credit Freeze and Thaw Guide.
Is ATT Tech Support 360 reliable?
They're inexpensive, reliable, and offer other plans like remote computer backups.
How Big Is The Problem?
- In Australia, remote access scams are now the sixth largest scam type. As of September, the total reported losses via the ACCC are $4.7 million, yet this only represents reported losses. We can safely assume that total losses run well into the tens of millions per annum. The losses are on t…
What Is The Impact on Victims?
- From a trust and emotional perspective, all victims are materially impacted by scams. From a loss perspective, the amounts can vary from a few thousand dollars to someone's entire life savings. Different banks have different approaches in terms of reimbursing customers — that is, at what stage is the bank liable for protecting the customer vs. the victim being responsible. However, th…
How Can We Protect Victims?
- Dubbed the “call that could wipe out your life savings,” four in ten consumers have not heard of remote access scams. Protection begins on the front lines, and raising awareness about these scams with consumers and businesses is a starting point. There is a lot of great work being done in this space by entities such as Scamwatch and UK Financeas well as by the banking industry it…
What Can Banks Do to Detect Remote Access Scams?
- Most authentication and fraud prevention solutions rely on known device and IP location parameters to measure fraud risk. While these controls can be effective, RATs, by design, circumvent traditional fraud detection tools that look for the presence of malware, bots, and blacklisted devices, or IP addresses. Instead of relying on static controls, BioCatchuses machin…