Here’s a comparison of these four main VPN types:
| Remote Access VPN | Personal VPN | Mobile VPN | Site-to-Site VPN | |
| Who Connects Where? | User connects to a private network. | User connects to the internet via a thir ... | User connects to a private network. | Network connects to another network. |
| Software Required? | Users usually need to install software o ... | Users install a VPN service’s software o ... | Users usually need to install software o ... | Users do not need to run additional soft ... |
| Best Used For | Connecting to your company’s network – o ... | Protecting your privacy and bypassing ge ... | Achieving a consistent connection to a p ... | Joining up two or more networks, to crea ... |
How to install remote access?
Install Remote Access service on Windows Server 2019: 1. Open Server Manager Console. 2. At the top of the Server Manager, click on Manage and select Add Roles and Features. 3. On the Before you begin page, click Next. 4. Select Role-based or feature-based installation and then click Next.
How to set up routing and remote access?
- In Routing and Remote Access, expand the server → IPV4 → NAT.
- Right click on External Network, go to properties → Services and ports.
- Click on Add, enter the description for this service, enter the RDP port and IP address of the VPS and click on Ok.
How do I enable remote access in Windows 10?
Windows 10 Fall Creator Update (1709) or later
- On the device you want to connect to, select Start and then click the Settings icon on the left.
- Select the System group followed by the Remote Desktop item.
- Use the slider to enable Remote Desktop.
- It is also recommended to keep the PC awake and discoverable to facilitate connections. ...
How do I connect to a VPN?
To make a VPN connection from the Taskbar, use these steps:
- Click the network icon in the Taskbar
- Click the VPN button. Source: Windows Central
- Select the VPN connection.
- Click the Connect button. Source: Windows Central
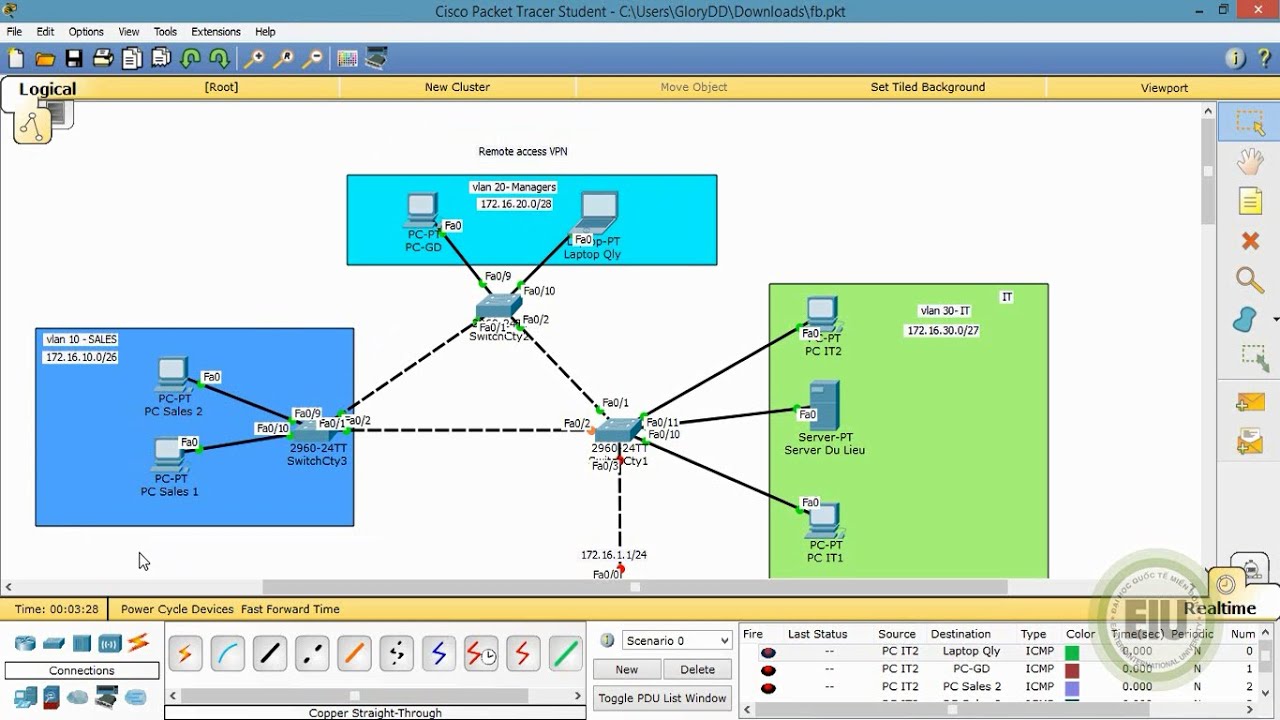
What is remote access VPN?
A remote access virtual private network (VPN) enables users who are working remotely to securely access and use applications and data that reside in the corporate data center and headquarters, encrypting all traffic the users send and receive.
What is VPN example?
VPNs are primarily used for remote access to a private network. For example, employees at a branch office could use a VPN to connect to the main office's internal network. Alternatively, a remote worker, who may be working from home, could need to connect to their company's internet or restricted applications.
Which of the following is an example of a remote access VPN client?
Which of the following is an example of a remote-access VPN client? B. The Cisco AnyConnect Secure Mobility Client is an example of a remote-access VPN client.
What are the 3 types of VPN?
The Three Main Types of VPNs VPNs can be divided into three main categories – remote access, intranet-based site-to-site, and extranet-based site-to-site. Individual users are most likely to encounter remote access VPNs, whereas big businesses often implement site-to-site VPNs for corporate purposes.
What are four types of VPN?
Here are five common VPN protocols and their primary benefits. PPTP. Point-to-Point Tunneling Protocol is one of the oldest VPN protocols in existence. ... L2TP/IPSec. Layer 2 Tunnel Protocol is a replacement of the PPTP VPN protocol. ... OpenVPN. ... SSTP. ... IKEv2.
What are the two types of VPN?
Types of VPNsSite-to-Site VPN: A site-to-site VPN is designed to securely connect two geographically-distributed sites. ... Remote Access VPN: A remote access VPN is designed to link remote users securely to a corporate network.More items...
Which VPN is best for remote access?
Best Remote Access VPNs for business.Perimeter 81 – Best all-round business VPN.GoodAccess – Security Strategy Options.ExpressVPN – Lightning Fast VPN.Windscribe – VPN with Enterprise-Friendly Features.VyprVPN – Secure VPN with Business Packages.NordVPN – Security-first VPN.More items...•
What is the difference between remote access and a VPN?
A VPN is a smaller private network that runs on top of a larger public network, while Remote Desktop is a type of software that allows users to remotely control a computer. 2. Remote Desktop allows access and control to a specific computer, while VPN only allows access to shared network resources.
Which of the following is type of VPN?
Explanation: VPNs are of two types. These are remote access VPNs & Site-to-site VPNs. Remote Access VPNs are used for business & home users. Site-to-site VPNs are mainly used in companies and firms with different geographical locations.
Which type of VPN is best?
The Best VPN Service for 2022NordVPN - Best VPN for Privacy.Surfshark - Best VPN for Security.Private Internet Access VPN - Best VPN for Windows.IPVanish - Best VPN for Android.Ivacy - Most Affordable.Atlas VPN - Best Data Breach Monitoring.ExpressVPN - Best Encryption.PureVPN - Best Server Base.More items...
How do I know my VPN type?
When you first set up a VPN connection by opening the Network preference, clicking the plus (+) button near the bottom-left corner of the window, choosing VPN from the Interface pop-up menu, and selecting the kind of protocol you'll use from the VPN Type menu, the Service Name field will display the protocol in ...
Which is best VPN?
ExpressVPN received a CNET Editors' Choice Award for best overall VPN. We evaluate VPNs based on their overall performance in three main categories: speed, security and price. Express isn't the cheapest, but it's among the fastest and, so far, is the most secure.
How do I know if I have a VPN?
You can also navigate to your settings application, click network, and then see if you're running a VPN/proxy. Harder to check on Android/iPhone and doesn't really happen on the device. Check with your company's IT people to see if the WiFi is set up with a VPN/proxy.
What is VPN and its types?
Virtual Private Network (VPN) services fall into four main types: personal VPNs, remote access VPNs, mobile VPNs, and site-to-site VPNs. In this guide, we explain how each of these VPN types work and when to use them. A VPN is a service that creates a private tunnel within a public connection (e.g. the internet).
What is a VPN for Netflix?
Using a Netflix VPN means that you can make your laptop, phone, tablet and even your games console or TV streaming device (think Chromecast, Roku, Amazon Fire) appear to be in a completely different country to the one you're really in.
What is remote access VPN?
What is a remote access VPN? Businesses use remote access VPNs to establish a secure connection between their network and the devices used by remote workers. Once connected, employees are able to access the resources on the network just as if their devices were physically plugged in at the office.
What are the advantages of remote access VPN?
Another advantage of remote access VPNs is that they provide companies with an affordable way to secure data sent by offsite employees. The initial investment needed to set up a remote access VPN is minimal and they can easily be scaled as a company grows and this is especially true if a VPN service provider is used.
Why is VPN important for business?
The most important benefit though is data security. When an offsite employee sends data through a VPN, it is encrypted, so even if a hacker is able to intercept that data, they won’t be able to use it. This is particularly important if an employee accesses their companies’ network using public Wi-Fi while traveling because traffic sent over these networks is usually not encrypted.
What is a network access server?
A network access server could be a dedicated server or it might be a software application running on a shared server. Users connect to the NAS over the internet in order to use a remote access VPN. In order to sign in to the VPN, the NAS requires that users provide valid credentials. To authenticate these credentials, the NAS uses either its own authentication process or a separate authentication server running on the network.
Why do businesses use VPNs?
Businesses use remote access VPNs to establish a secure connection between their network and the devices used by remote workers. Once connected, employees are able to access the resources on the network just as if their devices were physically plugged in at the office.
What is site to site VPN?
A site-to-site VPN uses a secure gateway to connect a network at one location to one or more networks at another location. This type of VPN doesn’t require each device at the end location to have a VPN client installed because the gateway handles the traffic.
Is it good to work remotely?
The ability to work remotely is one of the perks that many businesses offer employees to help sweeten the deal. The recent coronavirus outbreak has only exacerbated that, leading many more organizations to allow their employees to work remotely. While this is good news for employees, it could end up causing a great deal of disruption to organizations that aren’t prepared and one way to do so is to look into remote access VPN solutions.
What is remote access VPN?
In remote access VPN, you might want users on the remote networks to access the Internet through your device. However, because the remote users are entering your device on the same interface that faces the Internet (the outside interface), you need to bounce Internet traffic right back out of the outside interface. This technique is sometimes called hair pinning.
Where does remote access VPN problem originate?
Remote access VPN connection issues can originate in the client or in the Firepower Threat Defense device configuration. The following topics cover the main troubleshooting problems you might encounter.
How to view VPN configuration?
Click Device, then click View Configuration in the Site-to-Site VPN group.
How to use a VPN on a computer?
Step 1. Using a web browser, open https://ravpn-address , where ravpn-address is the IP address or hostname of the outside interface on which you are allowing VPN connections. You identify this interface when you configure the remote access VPN. The system prompts the user to log in. Step 2.
How to complete a VPN connection?
To complete a VPN connection, your users must install the AnyConnect client software. You can use your existing software distribution methods to install the software directly. Or, you can have users install the AnyConnect client directly from the Firepower Threat Defense device.
What is AnyConnect client profile?
AnyConnect client profiles are downloaded to clients along with the AnyConnect client software. These profiles define many client-related options, such as auto connect on startup and auto reconnect, and whether the end user is allowed to change the option from the AnyConnect client preferences and advanced settings.
How long is a VPN idle?
Idle Timeout —The length of time, in minutes, that the VPN connection can be idle before it is automatically closed, from 1-35791394. The default is 30 minutes. Browser Proxy During VPN Sessions —Whether proxies are used during a VPN session for Internet Explorer web browsers on Windows client devices.
What is remote access VPN?
What Is a Remote Access VPN? A remote access virtual private network (VPN) enables users who are working remotely to securely access and use applications and data that reside in the corporate data center and headquarters, encrypting all traffic the users send and receive. The remote access VPN does this by creating a tunnel between an ...
Why is VPN remote access?
The remote access VPN does this by creating a tunnel between an organization’s network and a remote user that is “virtually private,” even though the user may be in a public location. This is because the traffic is encrypted, which makes it unintelligible to any eavesdropper.
Does SASE require a VPN?
Using SASE, an organization does not have to maintain a separate stand-alone proxy or VPN. Rather, users connect to a SASE solution (which provides access to the cloud and data center) with consistent security. Some advantages of using a SASE are that it allows companies to:
How to use remote access VPN?
To use a remote access VPN on your device you typically need to install client software or configure your device’s operating system to connect to the VPN. There also needs to be a VPN server on the network end of the connection.
What are the different types of VPNs?
Virtual Private Network (VPN) services fall into four main types: personal VPNs, remote access VPNs, mobile VPNs, and site-to-site VPNs. In this guide, we explain how each of these VPN types work and when to use them.
What is a VPN service?
A personal VPN service connects you to a VPN server, which then acts as a middleman between your device and the online services you want to access.
Why use mobile VPN?
Mobile VPNs tend to be used to ensure consistent availability for mobile workers, or for the convenience of having a VPN that tolerates connection changes. For example:
What is intranet VPN?
Intranet-Based VPN: When the networks being connected belong to a single company, the combined VPN is known as an intranet-based VPN. This enables a company to establish a single wide area network (WAN) that spans two or more of its offices. Users in the company can access resources from other sites as easily as if they were on their own site.
How many types of VPN are there?
The four types of VPN outlined here have different applications, making it easy to choose between them.
How many ways can a VPN be implemented?
There are three main ways a site-to-site VPN can be implemented:
What is a VPN client?
An employee who is working from home uses VPN client software on a laptop in order to connect to the company network. Remote access VPNs connect individual users to another network via a VPN client that is installed on the user device. Site-to-site VPNs are “always on” connections that use VPN gateways to connect two sites together.
What is site to site VPN?
Site-to-site VPNs are “always on” connections that use VPN gateways to connect two sites together. Users at each site can access the network on the other site without having to use any special clients or configurations on their individual devices. Recommend. Network Security 1.0. Final Exam Answers.
Does a toy manufacturer have a VPN?
A toy manufacturer has a permanent VPN connection to one of its parts suppliers. All users at a large branch office can access company resources through a single VPN connection. A mobile sales agent is connecting to the company network via the Internet connection at a hotel.
What is remote access VPN?
Explanation: Remote access VPNs connect individual users to another network via a VPN client that is installed on the user device. Site-to-site VPNs are “always on” connections that use VPN gateways to connect two sites together. Users at each site can access the network on the other site without having to use any special clients ...
What is a VPN for a toy manufacturer?
A toy manufacturer has a permanent VPN connection to one of its parts suppliers. A mobile sales agent is connecting to the company network via the Internet connection at a hotel. An employee who is working from home uses VPN client software on a laptop in order to connect to the company network. Explanation: Remote access VPNs connect individual ...
What is remote access VPN?
Simply put, remote access VPNs connect the user to a secure remote server in order to access a private network. The added encryption ensures that security isn’t compromised. This is the foundation upon which the so-called commercial VPN services are built.
What are the different types of VPNs?
VPNs can be divided into three main categories – remote access, intranet-based site-to-site, and extranet-based site-to-site. Individual users are most likely to encounter remote access VPNs, whereas big businesses often implement site-to-site VPNs for corporate purposes.
Why is it important to have a variety of VPN protocols?
Having variety in protocols is important for bypassing censorship, eliminating VPN blocks, or streaming videos effectively . Other providers, such as ProtonVPN and AirVPN, choose to focus on a single protocol – usually OpenVPN, as it’s open-source and currently considered the most secure option.
Why do VPNs have multiple protocols?
Others prefer to support several variations of one protocol, due to design philosophy or limited resources. The main advantage of multi-protocol VPNs is the number of options they give you.
What is business oriented VPN?
Business-oriented VPNs are marked by several specific features that facilitate the process of setting up, deploying, and managing VPN connections for companies.
What is VPN for business?
1. VPNs for Business or Pleasure. When looking at a VPN’s two major purposes – business or personal use – you can either get a service tailored to meet the needs of large enterprises, or a service that focuses on individual users .
What is a VPN network?
Simply put, a virtual private network by itself is the secure, private connection between your device and the endpoint – or your destination. It utilizes a certain VPN protocol to encrypt and mask your traffic. This is the VPN technology working to keep your data safe.
What is VPN in the internet?
A Virtual Private Network (VPN) is a network that allows the private networks at a remote location securely connect to the public Internet and provide access only to the intended recipients for transmitting data. VPN is built by creating the virtual point-to-point connection using the dedicated connections, traffic encryption or virtual tunneling protocols.
How does network security work?
The enforcement of network security, whether it be local network security, or wireless network security is the core for creating the secure environment of the daily working processes. Network security is accomplished through hardware and software . Network security system must be sophisticated and modern inside, but simple and understandable for the user. The visual scheme of the security system can be presented in the form of a Network Security diagram. ConceptDraw DIAGRAM provides the toolkit for network security system visualization with its Network Security Diagram solution.
What is a campus network?
A campus network provides wireless access to the Internet or LAN to users located in two or more buildings or in the open space surrounding those buildings. A campus network is usually set in the campus of a university, but the same kind of planning and design can be applied for other purposes. For example, the campus network can used for an office or industrial park, in a public place like a supermarket with an entertainment center, even on a farm. Another form of temporary campus network can exist during special events such as music festivals or rallies.
What is wireless network solution?
The Wireless Networks Solution extends ConceptDraw DIAGRAM software with professional diagramming tools, set of wireless network diagram templates and samples, comprehensive library of wireless communications and WLAN objects to help network engineers and designers efficiently design and create Wireless network diagrams that illustrate wireless networks of any speed and complexity , and help to identify all required equipment for construction and updating wireless networks, and calculating their costs.
What is VPN security?
f) All computers connected to Organization internal networks via VPN or any other technology must use the most up-to-date anti-virus software that is the corporate standard (refer to IT Security); this includes personal computers.
Who is covered by the VPN policy?
This policy applies to all Organization employees, contractors, consultants, temporaries, and other workers including all personnel affiliated with third parties utilizing VPNs to access the Organization network. This policy applies to implementations of VPN that are directed through a VPN Gateway.