
What is FIPS 140-3 development?
See FIPS 140-3 Development for more details. This Federal Information Processing Standard (140-2) specifies the security requirements that will be satisfied by a cryptographic module, providing four increasing, qualitative levels intended to cover a wide range of potential applications and environments.
What is FIPS 140-2 validation?
Here’s Why it Matters The Federal Information Processing Standard (FIPS) 140-2 is an important IT security benchmark and U.S. government standard issued by the National Institute of Standards and Technology (NIST). FIPS 140-2 validation is required for the sale of products with cryptography modules to the federal government.
What are the Federal Information Processing Standard (140-2) requirements for cryptographic modules?
This Federal Information Processing Standard (140-2) specifies the security requirements that will be satisfied by a cryptographic module, providing four increasing, qualitative levels intended to cover a wide range of potential applications and environments. The areas covered, related to the secure... See full abstract
What is FIPS compliance and why is it important?
FIPS Compliance is mandatory for US government endpoints, which means that all computers used for government work must be FIPS compliant. Government/federal organizations, subsidiaries, and their contractors must ensure FIPS compliance as they handle information protected by federal government rules.
What are FIPS 140-2 requirements?
FIPS 140-2 cryptography requirements and validation process FIPS 140-2 requires that any hardware or software cryptographic module implements algorithms from an approved list. The FIPS validated algorithms cover symmetric and asymmetric encryption techniques as well as use of hash standards and message authentication.
What does FIPS 140-2 cover?
FIPS 140-2 is the standard used by the United States government to validate the fact that cryptographic modules and solutions (hardware and software) produced by private sector companies meet the NIST standards and adhere to the Federal Information Security Management Act of 2002 (FISMA).
Is bomgar FIPS compliant?
Bomgar has received the National Institute of Standards and Technology's (NIST) FIPS 140-2 Level 2 validation for its B200 and B300 appliances and version 13.1.
Is BeyondTrust FIPS compliant?
BeyondTrust is the only Secure Remote Access provider that meets the rigorous requirements of Federal Information Processing Standard Publication (FIPS) 140-2 Level 1 validation.
What are the 4 levels of FIPS?
FIPS 140-2 has 4 levels of security, with level 1 being the least secure, and level 4 being the most secure: FIPS 140-2 Level 1- Level 1 has the simplest requirements. It requires production-grade equipment, and atleast one tested encryption algorithm.
How do I verify FIPS 140-2 compliance?
The easiest way to determine if your vendor is FIPS 140-2 certified is to check the NIST website. If a company's name appears in NIST's Cryptographic Module Validation Program (CMVP), they have been vetted by NIST and you should feel comfortable using the vendor's technology.
Is Splashtop FIPS compliant?
Splashtop uses the FIPS validated/certified OpenSSL module, which is the unmodified certified source code, for this configuration to be FIPS compliant.
Who owns Dameware?
SolarWinds IncThe Austin software maker reported a second-quarter profit of $19.4 million on $64 million in revenue compared to a profit of $13 million on $45.8 million revenue during the same three months last year. A division of software maker SolarWinds Inc.
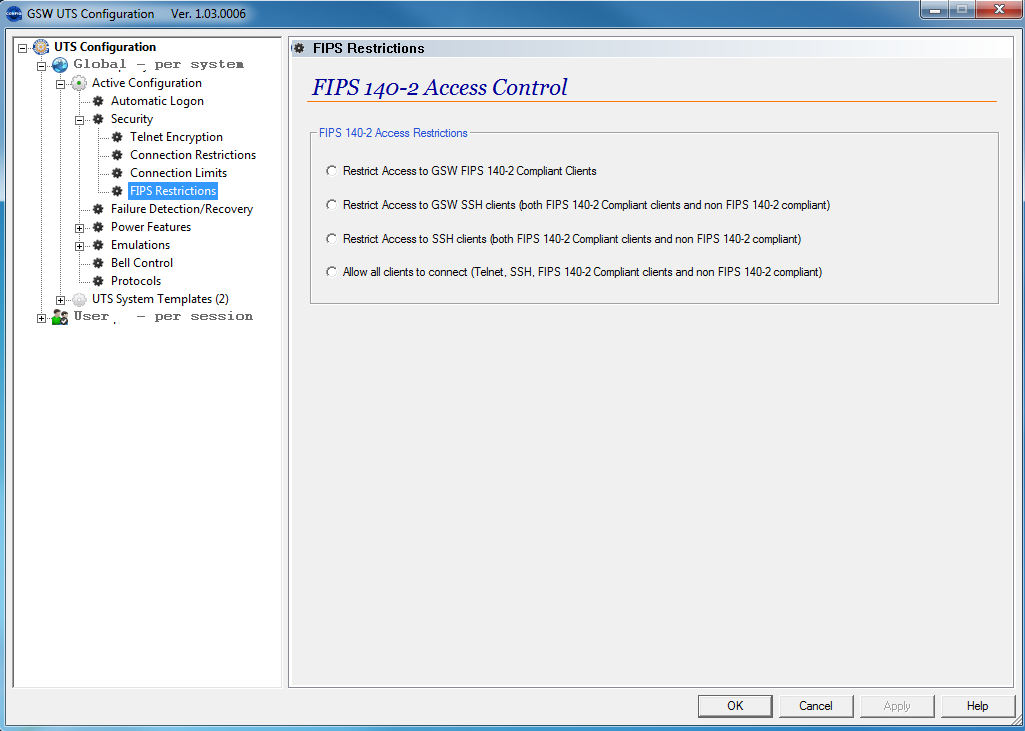
What is FIPS modules Dameware?
FIPS (Federal Information Processing Standards) are a set of standards that describe document processing, encryption algorithms and other information technology standards for use within non-military government agencies and by government contractors and vendors who work with the agencies.
How secure is bomgar?
Bomgar is still the most secure remote support software in the world. Now called BeyondTrust Remote Support, it's trusted by more customers than ever before. Sign-up for a free trial.
Does Bomgar use RDP?
This competitive document details the key advantages Bomgar provides over Windows' built-in remote access tools, including the ability to run RDP sessions securely through the Bomgar Box.
Open source tools for controls, risk exception libraries and policy reviews, approvals and version management of all of the above
Looking for advice on alternatives to RSA archer or RSAM for any of you familiar with these compliance tools that help store controls and other daily metadata around policy reviews, annual policy scheduled reviews, exceptions, architecture reviews, etc. Hope I made sense here.
Am I wasting my time?
Most techy guy in a <10 employee manufacturer. Put in charge of becoming NIST 800-171 compliant. I've been doing my homework, identifying tools we would need, thinking about alternatives of how to become complaint, hardware research, software research, reading through documentation, etc etc. I'm not a cyber security expert, not even close.
Sub using Prime Contractor Assets for Self Assessment
If you are a sub contractor using a prime contractors laptop for contract support, how does the sub report their self assessment? Technically all contract work is being done on a complaint prime contract system and network.
800-53 Guidance
I'm just being introduced to the wonderful world that is security frameworks and compliance and feel quite overwhelmed and would like if someone could "point" me into the right direction. What i'm attempting to accomplish is something "minor" but slowly give me more experience.
SSP Nist 800-171
Hi guys I am writing an SSP for a windows domain environment to meet the NIST 800-171 110 controls
How many login attempts can be made in 1 minute?
No more than 10,000 login attempts may be made over SSH in 1 minute. With password based authentication, that changes the probability to 1:803k which is less than 1:100k. With public key authentication, the 10k login attempts changes the probability to approximately 1:2^2034.
What is the keypad control in LEDs?
Keypad Control In LEDs Status Out Proprietary Temperature/ Humidity Adapter Data In Console Data In and Out, Control In, Status Out Removable Power Supply Power Port
How many attempts to break a key in a minute?
bits of encryption strength, the likeliness of breaking the key in a minute with this strategy is 4000 in 2^112 attempts or 1 in 2^100.
What is the firmware version of Uplogix 430?
This document applies to LMS firmware version 4.3.5.19979 which runs on the product.
How many characters does Uplogix LM require?
Uplogix LM requires a minimum 7‐character password and a minimum 7‐character shared secret for remote authentication . Thus, for password authentication over the console, SSH and TLS web GUI, the probability of successfully guessing the password is at least 1 in 26^7.
What is a guest role in Uplogix?
The Guest Role, provided by default in the module, has access to a limited number of Uplogix commands. The Guest Role can login to the local manager and run various show commands. The complete list of Guest Role commands is available in Appendix A.
VShell Server
VShell server, a secure alternative to Telnet and FTP with additional data tunneling services, is a secure portal to a server's resources and the network. VShell provides secure authentication, strong encryption, and data integrity using the open Secure Shell protocol (SSH2).
SecureCRT
SecureCRT is an extremely customizable terminal emulator with support for Secure Shell (SSH1 and SSH2) as well as Telnet, Telnet/TLS, Rlogin, serial, and TAPI protocols. SecureCRT is ideal for connecting to remote systems running Windows, UNIX, and VMS.
SecureFX
SecureFX is a high-security file transfer client with great flexibility in configuration and transfer protocols. SecureFX includes a command-line utility for scripting batch jobs to perform secure unattended file transfers and also supports "relentless" file transfers that automatically reconnect and resume when connections are broken.
Our domain controller went tits up at 4PM on a Friday
Oh and did I mention that as of 5PM I'm on PTO for 6.5 days to go to my brother's wedding?
Lying to the IT guy about rebooting
This has to be one of the most common lies users tell. "I totally rebooted before I called you".
Is hiring a skilled Microsoft on-premises infrastructure admin these days like finding a unicorn?
I could be rather selective 10 or so years ago when searching for mid-career Microsoft admins/engineers. Today, just finding someone competent seems to be an exercise in futility.
