
Once the scammer convinces you to give them remote access, they’ll ask you to install a program such as LogMeIn, TeamViewer or GoToAssist, which allows someone from another computer to operate your computer as if they were sitting right in front of it. Normally, these programs are used for legitimate tech support and worker collaboration purposes, but they can also be used by fraudsters for criminal purposes. While the scammer is connected to your computer, they will basically try to pull a high-tech confidence trick on you. As part of this trick, the scammer will make it seem like your computer has a problem and that they’re fixing it, but really they’re just running harmless programs that look strange to most people. Some examples include using the Command Prompt tool to generate ominous messages, or opening Temp files in Notepad and claiming that the random characters that show up are a sign of corruption. They will then offer to fix the problem for a fee of a few hundred dollars, pretend to repair your computer and take your money, possibly using any credit card or bank details you give them to make additional fraudulent charges in the future.
Full Answer
How do remote access scams work?
Remote access scams. Remote access scams try to convince you that you have a computer or internet problem and that you need to buy new software to fix the problem. The scammer will phone you and pretend to be a staff member from a large telecommunications or computer company, such as Telstra, the NBN or Microsoft.
What happens if you give a tech support scammer access to computer?
Once you've given a tech support scammer access to your computer, they can access your computer over and over again, scanning it for passwords, bank accounts and lots of other sensitive data. Click here to access a step-by-step plan to remove scammers ability to access your computer remotely.
What are the signs of unwanted remote access to computer?
They ask you to buy software or sign up to a service to fix the computer. They ask for your personal details and your bank or credit card details. The caller is very persistent and may become abusive. Never give an unsolicited caller remote access to your computer.
How can I protect my computer from being scammed?
Ideally, you would have a full system backup that would enable you to restore your computer to its previous state, ensuring the scammers no longer have access to your machine. If you don't know how to back up your system, you might visit the site of our friend Leo Notenboom and search on "backup."

What happens if you give a scammer access to your computer?
If you gave permission to the caller to access your computer, you should no longer consider it to be safe or clean. They might have installed programs, changed settings, or even installed a virus. In short, you can no longer trust it.
How can I expose an online scammer?
If you believe you're a victim of internet fraud or cybercrime, report it to the Internet Crime Complaint Center (IC3). Or, you can use the FBI's online tips form. Your complaint will be forwarded to federal, state, local, or international law enforcement.
What can a scammer do with AnyDesk?
AnyDesk is used legitimately by millions of IT professionals worldwide, to remotely connect to their clients' devices to help with technical issues. However, scammers can try to misuse AnyDesk (or any other remote access software) to connect to your computer and steal data, access codes, and even money.
Is IT safe to give someone remote access to your computer?
Remote access solutions could leave you vulnerable. If you don't have proper security solutions in place, remote connections could act as a gateway for cybercriminals to access your devices and data. Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular.
How do you trick a scammer?
0:262:22A Simple Scam Trick (Don't get fooled!) - YouTubeYouTubeStart of suggested clipEnd of suggested clipPeople something that scammers can quickly throw. Together. You then divide your list into threeMorePeople something that scammers can quickly throw. Together. You then divide your list into three groups and you make three predictions.
Can I expose a scammer?
You can report scams to the federal government. Your report may keep others from experiencing a scam. Government agencies use reports of scams to track scam patterns. They may even take legal action against a company or industry based on the reports.
Can you be hacked through AnyDesk?
AnyDesk was abused by individuals to steal from users who did not understand the need to keep their access codes as safe as they do their personal data. AnyDesk is an exceptionally secure software for remote connections, using banking-level security and encryption protocols.
Is IT safe to give AnyDesk access?
AnyDesk Remote Desktop Software comes with the highest security standards. From military-grade encryption to customizable security features, AnyDesk offers outstanding security that perfectly fits your needs.
What happens when a hacker gets remote access to my computer?
Hackers use RDP to gain access to the host computer or network and then install ransomware on the system. Once installed, regular users lose access to their devices, data, and the larger network until payment is made.
Can you get a virus from remote access?
Many remote access software solutions don't scan the remote computer for viruses or malware. If your home or work PC has been infected, and you're using it to access your office network remotely, then a hacker could easily install malware onto your business's servers and spread to every machine in your office.
Can someone see me through my computer screen?
But, just like any other tech devices, webcams are prone to hacking, which can lead to a serious, unprecedented privacy breach. Think of a case where an authorized person accesses and illegally takes control of your webcam, without your knowledge. Such a person will effortlessly spy on you and the people around you.
What do hackers want off your computer?
Computer hackers are unauthorized users who break into computer systems in order to steal, change or destroy information, often by installing dangerous malware without your knowledge or consent. Their clever tactics and detailed technical knowledge help them access the information you really don't want them to have.
What happens if I get scammed?
If you've been scammed, consider reporting the fraud to the police to see if they can take any action, as well as to your state consumer protection office. You can also report scams to the FTC. File a report online with the FTC, or by phone at (877) 382-4357.
How do I get my money back from a scammer in South Africa?
Call the South African Fraud Prevention Service You can contact SAFPS on 011 867 2234 or via email at for help with fraud prevention, combating financial fraud and crime, and help if you are a victim of impersonation or fraud.
What is a remote access scam?
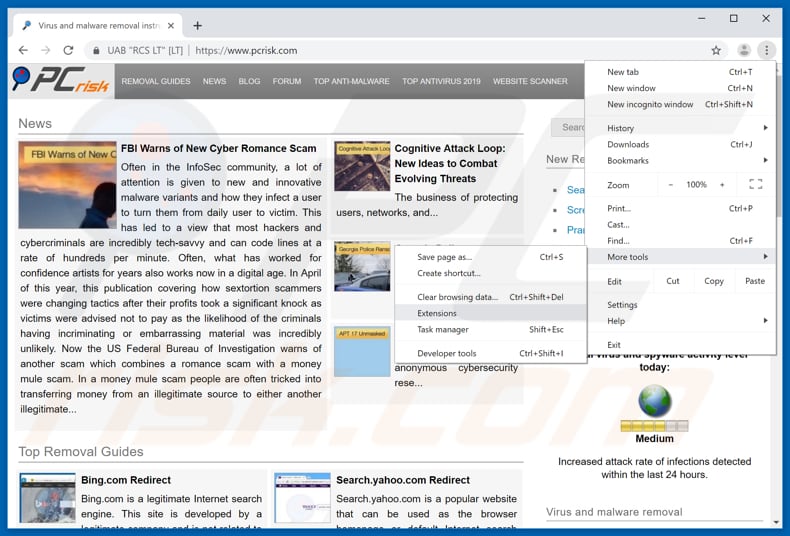
Remote access scams are a unique scenario where victims are socially engineered to provide remote access to their computer via a legitimate remote access tool such as TeamViewer , LogMeIn, Go-To-Meeting, or a similar remote desktop software . Once given permission to take over the computer, the scammer is able to steal personal and financial information which can later be used to defraud the victim.
What can banks do to detect remote access scams?
Most authentication and fraud prevention solutions rely on known device and IP location parameters to measure fraud risk. While these controls can be effective, RATs, by design, circumvent traditional fraud detection tools that look for the presence of malware, bots, and blacklisted devices, or IP addresses.
How can we protect victims?
Protection begins on the front lines, and raising awareness about these scams with consumers and businesses is a starting point. There is a lot of great work being done in this space by entities such as Scamwatch and UK Finance as well as by the banking industry itself. However, this is not an issue that can be addressed in isolation, as the sophistication of scams continues to improve.
Is cybercrime opportunistic?
Cybercrime is opportunistic, and there is no time like the present for criminals to adapt their tactics, old and new, to defraud online customers. Remote access scams are one of those tactics, and the number of attacks has grown during the COVID-19 pandemic. Cybercriminals are using the unstable environment to their advantage to take ...
What is remote access scam?
Remote access scams try to convince you that you have a computer or internet problem and that you need to buy new software to fix the problem.
What to do if you think you have provided your account details to a scammer?
If you think you have provided your account details to a scammer, contact your bank or financial institution immediately.
What is malware scam?
Malware tricks you into installing software that allows scammers to access your files and track what you are doing, while ransomware demands payment to ‘unlock’ your computer or files.
How to protect your computer from spyware?
Make sure your computer is protected with regularly updated anti-virus and anti-spyware software, and a good firewall. Research first and only purchase software from a source that you know and trust.
Can a scammer be abusive?
The scammer may initially sound professional and knowledgeable—however they will be very persistent and may become abusive if you don't do what they ask.
What to do if you give a scammer your information?
If You Gave a Scammer Your Personal Information. If a Scammer Has Access to Your Computer or Phone. Report a Scam to the FTC. Scammers can be very convincing. They call, email, and send us text messages trying to get our money or our sensitive personal information — like our Social Security number or account numbers.
Where to report a scam?
If you were scammed, report it to the FTC at ReportFraud.ftc.gov.
What to do if you send money through a money transfer app?
Did you send money through a money transfer app? Report the fraudulent transaction to the company behind the money transfer app and ask if they can reverse the payment. If you linked the app to a credit card or debit card, report the fraud to your credit card company or bank. Ask if they can reverse the charge.
How to get money back from a fraudulent credit card?
Contact the company or bank that issued the credit card or debit card. Tell them it was a fraudulent charge. Ask them to reverse the transaction and give you your money back.
What to do if you are scammed?
What To Do if You Were Scammed. Find out what to do if you paid someone you think is a scammer, gave them some personal information , or if they have access to your phone or computer. If You Paid a Scammer. If You Gave a Scammer Your Personal Information. If a Scammer Has Access to Your Computer or Phone. Report a Scam to the FTC.
How to intercept a package sent by USPS?
If you sent it by U.S. mail, contact the U.S. Postal Inspection Service at 877-876-2455 and ask them to intercept the package. To learn more about this process, visit USPS Package Intercept: The Basics.
How to take back control of your phone number?
Contact your service provider to take back control of your phone number. Once you do, change your account password. Also check your credit card, bank, and other financial accounts for unauthorized charges or changes. If you see any, report them to the company or institution.
How to stop remote access?
1. Shut down and disconnect your device from the Internet. That puts an absolute stop on any external meddling. It also often automatically revokes remote access for when you restart.
How do you know if you're a victim of a scam?
How will you know you're one of those victims? It's simple. If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam.
How do I know whether a number I see is a fake Microsoft tech support number?
One of the favorite scam techniques is for tech support scammers to give you fake phone numbers they claim are a correct Microsoft tech support number. Don't fall for that scam. See above for the best way to find the correct Microsoft tech support number.
How many people fall victim to Microsoft scams?
According to Microsoft's Digital Crime Unit, some 3.3 million people fall victim to the tech support scam every year, costing victims around $1.5 billion.
What can hackers look for in a computer?
Once they get access, they can digitally crawl all over your PC, looking for confidential information like passwords and account numbers.
What credit monitoring agencies freeze credit applications?
9. Put a freeze on credit applications via the three credit monitoring agencies -- Equifax, Experian and TransUnion . This will cost a few dollars but is worth it. Each of the bureaus has its own "credit lock" service but you might find the following article useful: Credit Freeze and Thaw Guide.
What happens if a virus is detected?
Once you realize what's happened, you need to take immediate action to minimize the potential damage.
What Is A Remote Access Scam?
How Big Is The Problem?
- In Australia, remote access scams are now the sixth largest scam type. As of September, the total reported losses via the ACCC are $4.7 million, yet this only represents reported losses. We can safely assume that total losses run well into the tens of millions per annum. The losses are on the rise as well, with September 2020 representing a new record, with over $1.1 million lost and in e…
What Is The Impact on Victims?
- From a trust and emotional perspective, all victims are materially impacted by scams. From a loss perspective, the amounts can vary from a few thousand dollars to someone's entire life savings. Different banks have different approaches in terms of reimbursing customers — that is, at what stage is the bank liable for protecting the customer vs. the victim being responsible. However, th…
How Can We Protect Victims?
- Dubbed the “call that could wipe out your life savings,” four in ten consumers have not heard of remote access scams. Protection begins on the front lines, and raising awareness about these scams with consumers and businesses is a starting point. There is a lot of great work being done in this space by entities such as Scamwatch and UK Financeas well as by the banking industry it…
What Can Banks Do to Detect Remote Access Scams?
- Most authentication and fraud prevention solutions rely on known device and IP location parameters to measure fraud risk. While these controls can be effective, RATs, by design, circumvent traditional fraud detection tools that look for the presence of malware, bots, and blacklisted devices, or IP addresses. Instead of relying on static controls, BioCatchuses machin…