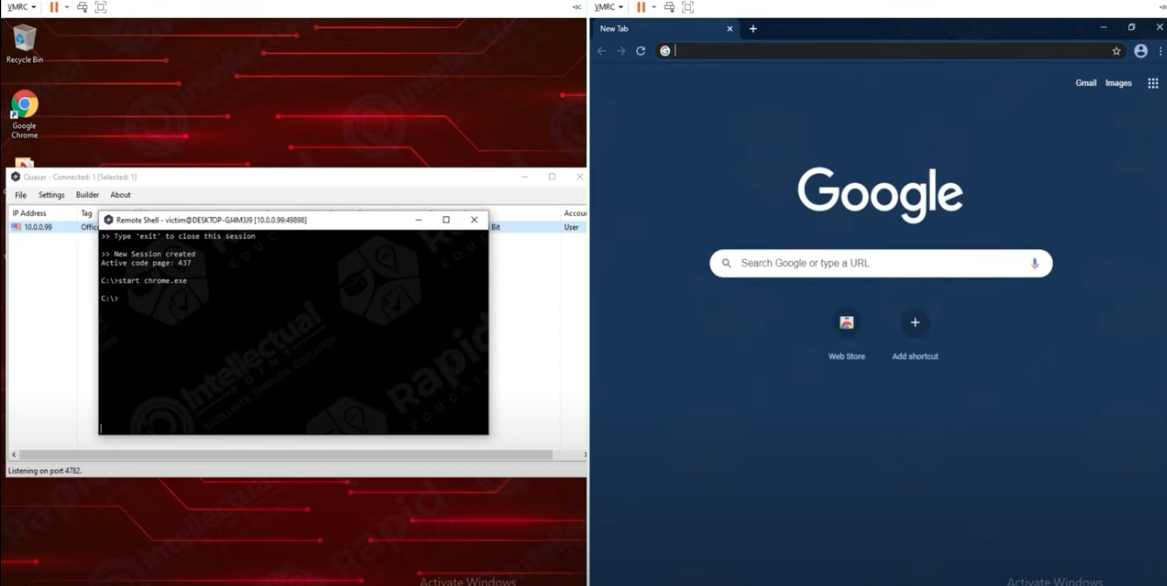
Examples of a Remote Access Trojan Attack :
- Remote Access Trojan can be sent as an attachment or link. It will be sent in the form of an email and the email will appear to come from a place that is trustworthy. If the attachment gets clicked by the user, the RAT gets downloaded. ...
- This can also be used in the form of the Man in the Middle attack.
Full Answer
What is a remote access trojan (RAT)?
What Is a RAT Virus? A remote access trojan (RAT), also called creepware, is a kind of malware that controls a system via a remote network connection. It infects the target computer through specially configured communication protocols and enables the attacker to gain unauthorized remote access to the victim.
What is a Trojan virus and how does it work?
Furthermore, the Trojan virus may bring more and more other cyber infections to the same machine, which making the situation worse. Furthermore, this Trojan virus can watch what you are doing on the computer and send the sensitive information collected to the remote hackers.
How to remove Trojan Horse virus from Windows 10?
1、Keep pressing "Windows+R" keys on your keyboard. 2、Type "Regedit" into the Run box and click OK to open Registry Editor. Note: Of course, it's highly recommended that you should remove trojan horse in a professional way if there are still some similar probelms with your computer.

How are remote access Trojans delivered?
A remote access Trojan (RAT) is a malware program that includes a back door for administrative control over the target computer. RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment.
Can a Trojan give remote access?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
What are the variant of remote access Trojan?
There are a large number of Remote Access Trojans. Some are more well-known than others. SubSeven, Back Orifice, ProRat, Turkojan, and Poison-Ivy are established programs. Others, such as CyberGate, DarkComet, Optix, Shark, and VorteX Rat have a smaller distribution and utilization.
Can an Iphone get a remote access Trojan?
The iOS Trojan is smart and spies discretely, i.e. does not drain a battery. The RCS mobile Trojans are capable of performing all kinds of spying you can expect from such a tool, including location reporting, taking photos, spying on SMS, WhatsApp and other messengers, stealing contacts and so on.
How do I know if someone is accessing my computer remotely?
You can try any of these for confirmation.Way 1: Disconnect Your Computer From the Internet.Way 2. ... Way 3: Check Your Browser History on The Computer.Way 4: Check Recently Modified Files.Way 5: Check Your computer's Login Events.Way 6: Use the Task Manager to Detect Remote Access.Way 7: Check Your Firewall Settings.More items...•
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
Which is the best remote access Trojan?
Blackshades is a Trojan which is widely used by hackers to gain access to any system remotely. This tool frequently attacks the Windows-based operating system for access.
How would users recognize if ones computer is infected?
Signs of an infection include your computer acting strangely, glitching and running abnormally slow. Installing and routinely updating antivirus software can prevent virus and malware infections, as can following cautious best practices.
How can I remotely access another computer over the Internet?
You can set up remote access to your Mac, Windows, or Linux computer.On your computer, open Chrome.In the address bar, enter remotedesktop.google.com/access .Under “Set up Remote Access,” click Download .Follow the onscreen directions to download and install Chrome Remote Desktop.
Can someone install spyware on my iPhone remotely?
Spyware can be loaded onto your iPhone remotely via a malicious app, or physically if someone gains access to your phone. Use long and unique passwords for all your accounts and two-factor authentication to secure your personal data.
Can someone see my iPhone screen remotely?
If your iPhone backs everything up to your iCloud account, then someone can spy on your activity by accessing your iCloud account from any web browser. They would need your Apple ID username and password in order to do this, so if you know that a third party has that information, there are a few steps you should take.
Can you RAT an iPhone?
So someone would need direct physical access to your iOS device and a computer to install a RAT exploit into it. Even if you accessed a web site or email with a RAT package hidden in it, it cannot execute or do anything on a normal iOS installation.
How do I remove remote malware?
1:283:06How to remove a computer virus remotely - YouTubeYouTubeStart of suggested clipEnd of suggested clipYou can launch the anti-malware. Program first let's accept all the licensing terms and clickMoreYou can launch the anti-malware. Program first let's accept all the licensing terms and click continue. And then start scanning.
How can I remotely access another computer over the Internet?
You can set up remote access to your Mac, Windows, or Linux computer.On your computer, open Chrome.In the address bar, enter remotedesktop.google.com/access .Under “Set up Remote Access,” click Download .Follow the onscreen directions to download and install Chrome Remote Desktop.
Is a backdoor malware?
A backdoor is a malware type that negates normal authentication procedures to access a system. As a result, remote access is granted to resources within an application, such as databases and file servers, giving perpetrators the ability to remotely issue system commands and update malware.
What is data sending Trojan?
A data-sending Trojan is a kind of Trojan virus that relays sensitive information back to its owner. This type of Trojan can be used to retrieve sensitive data, including credit card information, email addresses, passwords, instant messaging contact lists, log files and so on.
What is RAT software?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can ac...
What’s the difference between the RAT computer virus and RAT software?
As for functions, there is no difference between the two. Yet, while remote administration tool is for legit usage, RAT connotes malicious and crim...
What are the popular remote access applications?
The common remote desktop tools include but are not limited to TeamViewer, AnyDesk, Chrome Remote Desktop, ConnectWise Control, Splashtop Business...
How are Remote Access Trojans Useful to Hackers?
Attackers using remote control malware cut power to 80,000 people by remotely accessing a computer authenticated into SCADA (supervisor y control and data acquisition) machines that controlled the country’s utility infrastructure. RAT software made it possible for the attacker to access sensitive resources through bypassing the authenticated user's elevated privileges on the network. Having access to critical machines that control city resources and infrastructure is one of the biggest dangers of RAT malware.
Why do attackers use remote devices?
Instead of storing the content on their own servers and cloud devices, attackers use targeted stolen devices so that they can avoid having accounts and servers shut down for illegal content.
How to install a RAT?
An attacker must convince the user to install a RAT either by downloading malicious software from the web or running an executable from a malicious email attachment or message. RATs can also be installed using macros in Microsoft Word or Excel documents. When a user allows the macro to run on a device, the macro silently downloads RAT malware and installs it. With the RAT installed, an attacker can now remotely control the desktop, including mouse movement, mouse clicks, camera controls, keyboard actions, and any configured peripherals.
What is remote control software?
Legitimate remote-control software exists to enable an administrator to control a device remotely. For example, administrators use Remote Desktop Protocol (RDP) configured on a Windows server to remotely manage a system physically located at another site such as a data center. Physical access to the data center isn’t available to administrators, so RDP gives them access to configure the server and manage it for corporate productivity.
What happens if you remove the internet from your computer?
Removing the Internet connection from the device disables remote access to your system by an attacker. After the device can no longer connect to the Internet, use your installed anti-malware program to remove it from local storage and memory. Unless you have monitoring configured on your computer, you won't know which data and files transferred to an attacker. You should always change passwords across all accounts, especially financial accounts, after removing malware from your system.
Can malware writers name processes?
For most applications and processes, you can identify any suspicious content in this window, but malware writers name processes to make them look official. If you find any suspicious executables and processes, search online to determine if the process could be a RAT or other type of malware.
How do remote access Trojans work?
The Remote Access Trojans get themselves downloaded on a device if the victims click on any attachment in an email or from a game. It enables the attacker to get control over the device and monitor the activities or gaining remote access. This RAT makes itself undetected on the device, and they remain in the device for a longer period of time for getting data that may be confidential.
What is the most powerful Trojan?
One of the most powerful Trojans that are popularly used by the attacker or hacker is Remote Access Trojan. This is mostly used for malicious purposes. This Trojan ensures the stealthy way of accumulating data by making itself undetected. Now, these Trojans have the capacity to perform various functions that damages the victim.
What is the advantage of remote access?
Advantage of Remote Access Trojans : It can be used to capture screenshots. The attacker can activate the webcam, or they can record video. The RAT can be used to delete the files or alter files in the system. It can also be used to capture screenshots.
What Can Remote Access Trojans Do?
Malware developers use Remote Access Trojan (RAT) tools to gain full access and control over a user’s computer, including mouse and keyboard control, file access, and network resources.
What Is The Best Trojan Remote Access?
Hackers commonly use Blackshades to gain remote access to computers. Windows-based operating systems are frequently targeted by this tool. The Trojan has infected 500,000 systems worldwide until now.
Are Remote Access Trojans Illegal?
According to law enforcement officials, it is not illegal to possess a remote-access tool. IT support is often provided by remote-access tools in corporate environments. The use of such tools for illegal purposes is a different ballgame, never mind the purpose-built remote access Trojan that can be used.
Is Remote Access Detectable?
Could the website detect that Desktop 2 is being remotely operated? Desktop 1 cannot be detected, but remote operations can be. There is no way they can do it. In theory, if they have access to your home ISP, they could see the inbound/outbound connections between your home PC and the server.
What Damage Can A Trojan Do?
In general, a Trojan is designed to damage, disrupt, steal, or in general cause some other harm to your data or network. You are fooled by a Trojan by pretending to be a legitimate application or file.
What Happens If You Give Someone Remote Access To Your Computer?
The caller has access to your PC security if you give them access. scammers may try to reach you in a more clever way by tricking you into downloading malware onto your computer, which then flashes a message warning that you have a virus and need to contact “tech support” to have it removed from your computer.
Can Vpn Transmit Viruses?
The likelihood of being hacked or infected is lower when using a virtual private network. As a result, this is not because a VPN will remove malicious software from your device, but rather because you are not exposed to it. This means that you won’t be able to hack your device in the first place because you are not exposed.
What are Remote Access Trojans?
Remote Access Trojans (RATs) are programs that allow hackers to control or monitor your computer remotely, usually through the internet. RATs can be either purchased or programmed by a hacker him-or-herself, but generally they fall under three categories:
How to prevent a RAT from taking over your computer again?
Plugging the Ethernet cable into your router and disabling WiFi should prevent a RAT from taking over your computer again. If you do not plug in an Ethernet cord, ensure that your wireless is turned off and that all security programs are up to date as this will stop any future attacks.
How Do Remote Access Trojans Spread?
As with most malware infections, RATs typically come through malspam, phishing and spearphishing campaigns. For example, a user may receive a phishing email carrying a malicious pdf or Word document, or the mail may contain a URL that takes the victim to a webpage for a fake software plugin and a message that a required tool is missing or needs updating. Adobe Flash, Adobe Reader and similar popular products are often spoofed for just this kind of trick due to their wide adoption across platforms.
What is a Remote Access Trojan?
Sometimes referred to as a “remote administration tool” due to their similarity to legitimate IT admin tools like TeamViewer and LogMeIn, a remote access trojan is essentially a hidden backdoor into another user’s computer. This backdoor gives the person operating the RAT a whole range of different functions that can be used for malicious purposes, depending on which particular RAT platform they’re utilizing.
How Do Threat Actors Use RATs Against The Enterprise?
While there’s certainly been cases of “lone wolf” actors targeting individuals and organizations and remaining undetected for over a decade, until recently the main threat to enterprise from RATs came from APT campaigns, including those targeting the most sensitive of installations such as a nuclear power plant in India (targeted by the DTrack RAT), oil and gas companies in the Middle East, telecoms across Africa and Asia ( DanBot RAT ), government agencies around the globe ( Calypso RAT ), and most recently an energy-sector organization in Europe ( PupyRAT ).
How Can CISOs Protect Against Remote Access Trojans?
In the past, RATs were difficult to develop and required a high degree of proficiency to operate. They were anything but “fire-and-forget” tools. They required threat actors to invest time and effort in inserting the malware into victims’ systems, manually operate the connection and then carry out whatever nefarious activities they had planned. As we have seen, things have changed more recently, and like other crimeware such as ransomware as a service, malware developers have seen and grasped the opportunity to make profit by selling easy access to tools that others do not have the skill to make for themselves.
How did RATs help hackers?
Using these RATs, hackers were able to take complete control over victims’ machines, gain access to entire networks, exfiltrate troves of sensitive corporate data and avoid detection until after they had realized all their goals.
How Do RATs Evade Detection?
RATS piggyback on the same remote access services that legitimate tools like TeamViewer use, exploiting Windows Remote Desktop (RDP) and TCP networking protocols to install a backdoor to the attacker’s own machine.
Why does a RAT stay on my computer?
The reason why remote access trojan (RAT) can stay in your computer for a long time is its capacity to trespass the system security utility, such as system firewall and authentic security software, through the way of pretending to be a system component. You should remove remote access trojan (RAT) manually as soon as possible.
Can a Trojan be silently modified?
It can silently make modification on the Windows registry as well as crucial system settings and options, which will offer it the access to the deep of the system and perform undesirable task as soon as you turn on the system. It is wise to get rid of the Trojan from your computer in time. The infected computer will perform very slowly and weirdly.
Can a Trojan attack a computer?
Most of time, this Trojan virus can still attack your computer even you have an antivirus program safeguard your computer. For this reason, we all shall be more careful when we are viewing anything online. remote access trojan (RAT) is capable of installing itself on the target machine within a short time without your knowledge.