
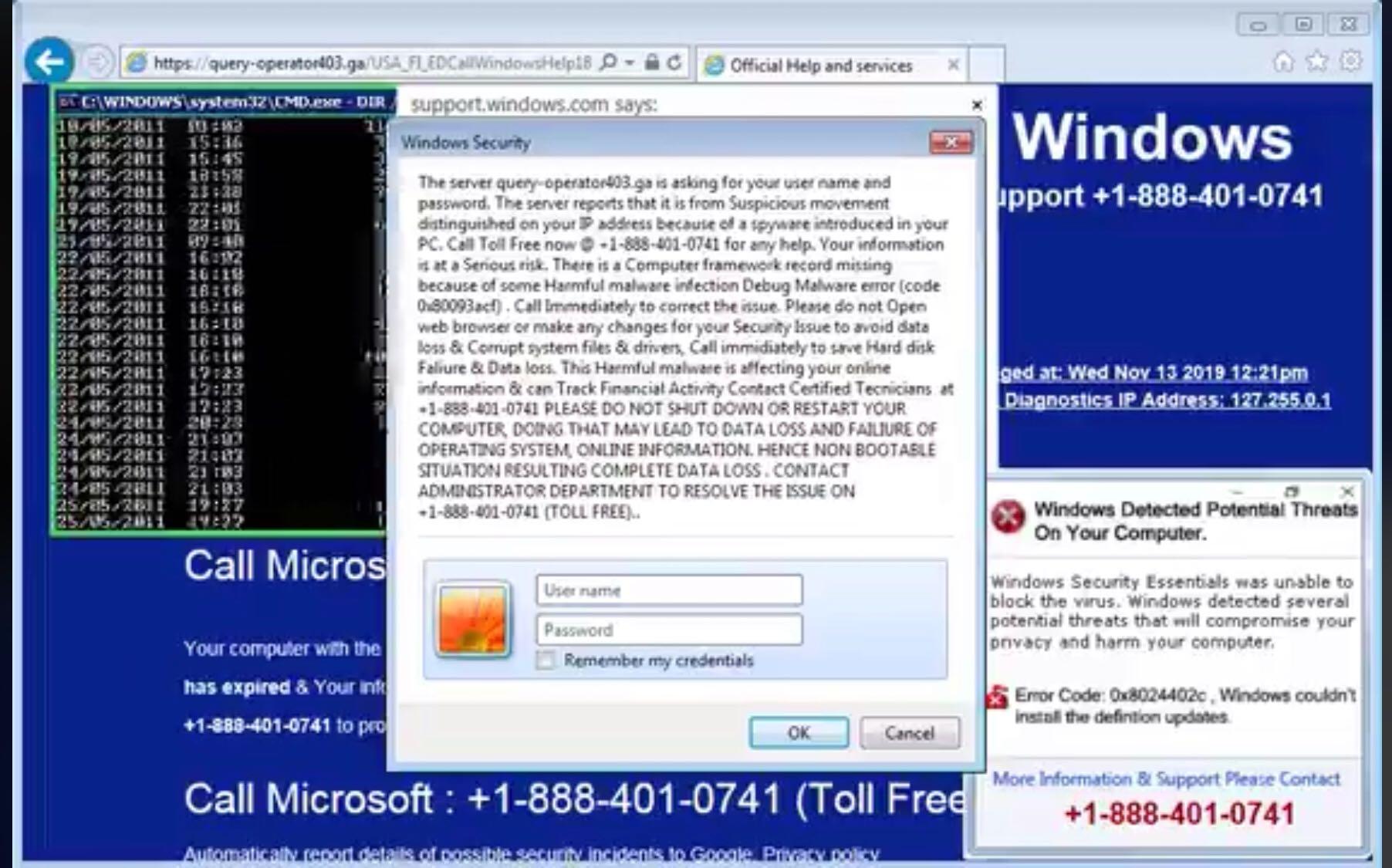
In a remote access scam, a scammer attempts to persuade you into giving them remote control over your personal computer, which allows the scammer to con money out of you and steal your private information. Remote access scams are often related to tech support scams, (example: Dell Computer tech support) and typically starts on the phone with either a cold call from a fake tech support specialist telling you your computer is infected with malware, or a scary-looking pop-up ad that says there’s a problem with your computer and gives you a phone number to call for help. Scammers may also try to convince you to give them remote access by telling you they have money to give you that they can only deliver by connecting to your computer, as seen in the recent FTC refund scam that’s been making the rounds. Another very recent refund scam includes asking you to display your online bank account, and putting a fake deposit on your account statement. The scammers then lead you to believe that they made a typo on the fake refund issued and ask for a gift card as a refund to them.
Full Answer
How do remote access scams work?
Remote access scams. Remote access scams try to convince you that you have a computer or internet problem and that you need to buy new software to fix the problem. The scammer will phone you and pretend to be a staff member from a large telecommunications or computer company, such as Telstra, the NBN or Microsoft.
What happens when you get a call from a computer scammer?
The caller will request remote access to your computer to ‘find out what the problem is’. The scammer may try to talk you into buying unnecessary software or a service to ‘fix’ the computer, or they may ask you for your personal details and your bank or credit card details.
How can I protect my computer from being scammed?
Ideally, you would have a full system backup that would enable you to restore your computer to its previous state, ensuring the scammers no longer have access to your machine. If you don't know how to back up your system, you might visit the site of our friend Leo Notenboom and search on "backup."
How do you spot a tech support scam?
It's simple. If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam. Tech companies just don't operate that way. But tech support scammers do.

How do you remotely access another computer?
Use Remote Desktop to connect to the PC you set up: On your local Windows PC: In the search box on the taskbar, type Remote Desktop Connection, and then select Remote Desktop Connection. In Remote Desktop Connection, type the name of the PC you want to connect to (from Step 1), and then select Connect.
What is remote access takeover?
As technology advances, fraudsters and scammers are also becoming more advanced. In some cases, they may try to convince you to give them remote access to your computer and your online banking. This is known as remote access takeover, or computer access takeover.
How does a remote access work?
Remote access simply works by linking the remote user to the host computer over the internet. It does not require any additional hardware to do so. Instead, it requires remote access software to be downloaded and installed on both the local and remote computers.
Can a scammer access my bank account?
Yes, this is possible. Identity theft was the number one reported type of fraud in 2020 [*], according to the FTC. When scammers gain access to your personal information by phishing, for example, they can do one or more of the following: Gain access to your bank account and spend or transfer all your money.
Can someone remotely access my computer without my knowledge?
"Can someone access my computer remotely without me knowing?" The answer is "Yes!". This could happen when you are connected to the internet on your device.
What happens when a hacker gets remote access to my computer?
Increased network activity. For any attacker to take control of a computer, they must remotely connect to it. When someone is remotely connected to your computer, your Internet connection will be slower. Also, many times after the computer is hacked, it becomes a zombie to attack other computers.
How do I trace remote access?
1:132:22How to trace remote access logs VPN access - YouTubeYouTubeStart of suggested clipEnd of suggested clipAnd I'm just gonna type in C colon backslash Windows backslash tracing and that's gonna open up myMoreAnd I'm just gonna type in C colon backslash Windows backslash tracing and that's gonna open up my tracing directory.
What dangers can remote desktop Services give to computers?
Remote Desktop Service – The RisksRDS Exposed on the Internet. ... Man-in-the Middle Attacks (MiTM) ... Encryption Attacks. ... Denial of Service (Network Level Authentication) ... Transport Layer Security Authentication. ... High Level Encryption. ... Network Level Authentication. ... RDS Exposed on the Internet.
Can remote desktop be monitored?
A: YES, your employer can and has the right to monitor your Citrix, Terminal, and Remote Desktop sessions.
How much information does a scammer need?
Much like a Social Security number, a thief only needs your name and credit card number to go on a spending spree. Many merchants, particularly online, also ask for your credit card expiration date and security code. But not all do, which opens an opportunity for the thief.
What if a scammer has my personal information?
Report Identity Theft. Report identity (ID) theft to the Federal Trade Commission (FTC) online at IdentityTheft.gov or by phone at 1-877-438-4338. The FTC will collect the details of your situation.
What can a scammer do with my picture?
Information fraudsters could get from your photos A photo posted on your birthday, for example, would provide them with your date of birth, whereas a photo of a new house could potentially give them details of where you live.
What is the risk of RDP?
In many cases, servers with RDP publicly accessible to the internet have failed to enable multi-factor authentication (MFA). This means that an attacker who compromises a user account by exposing a weak or reused password through a brute force attack can easily gain access to a user's workstation via RDP.
What is the difference between remote access and remote support?
While remote access is the ability to connect to a remote device, remote support is the action of providing technical support once a remote access connection is established for the specific purpose of troubleshooting and solving technical issues.
How do I get rid of remote support customer client on Mac?
Locate the com. apple. RemoteDesktop folder, and drag it to the Trash. Locate the Client, Shared Settings, and Task Server folders and drag them to the Trash.
What is remote access support?
Remote Support is the ability to remotely access and control a computer or mobile device anytime, anywhere using a reliable and secure remote support software like Zoho Assist.
What do scammers ask for?
The scammer may try to talk you into buying unnecessary software or a service to ‘fix’ the computer, or they may ask you for your personal details and your bank or credit card details.
Can a scammer get your number?
Scammers can obtain your number fraudulently. Make sure your computer is protected with regularly updated anti-virus and anti-spyware software, and a good firewall. Research first and only purchase software from a source that you know and trust.
Can I give my credit card info over the phone?
Never give your personal, credit card or online account details over the phone unless you made the call and the phone number came from a trusted source. If you receive a phone call out of the blue about your computer and remote access is requested – hang up – even if they mention a well-known company such as Telstra.
What is a remote access scam?
Remote access scams are a unique scenario where victims are socially engineered to provide remote access to their computer via a legitimate remote access tool such as TeamViewer, LogMeIn, Go-To-Meeting, or a similar remote desktop software.
How big is the problem?
In Australia, remote access scams are now the sixth largest scam type. As of September, the total reported losses via the ACCC are $4.7 million, yet this only represents reported losses. We can safely assume that total losses run well into the tens of millions per annum.
What is the impact on victims?
From a trust and emotional perspective, all victims are materially impacted by scams. From a loss perspective, the amounts can vary from a few thousand dollars to someone's entire life savings. Different banks have different approaches in terms of reimbursing customers — that is, at what stage is the bank liable for protecting the customer vs.
How can we protect victims?
Dubbed the “call that could wipe out your life savings,” four in ten consumers have not heard of remote access scams. Protection begins on the front lines, and raising awareness about these scams with consumers and businesses is a starting point.
What can banks do to detect remote access scams?
Most authentication and fraud prevention solutions rely on known device and IP location parameters to measure fraud risk. While these controls can be effective, RATs, by design, circumvent traditional fraud detection tools that look for the presence of malware, bots, and blacklisted devices, or IP addresses.
How does scammer revolt work?
Scammer Revolt uses a couple of methods. The first and easiest is when the scammer uses TeamViewer and you connect to their machine. TeamViewer allows the controlling PC to view/copy/move/etc. files without the other PC knowing, especially if you black out their screen.
Why does Revolt use a virtual computer?
Scammer Revolt also uses a virtual computer to prevent the scammer from harming him while connecting. Sometimes a scammer seems to pick up on this and ask him if he's using a virtual computer or disconnect. Keep on watching the vids. Ive been binging them, you will pick up quickly how they do it.
How to scan for rootkits?
Click the Settings tab at the top, and then in the left column, select Detections and Protections, and if not already checked place a checkmark in the selection box for Scan for rootkits. Click the Scan tab at the top of the program window, select Threat Scan and click the Scan Now button.
How to run JRT as administrator?
Run the tool by double-clicking it. If you are using Windows Vista, 7, or 8; instead of double-clicking, right-mouse click JRT.exe and select "Run as Administrator". The tool will open and start scanning your system. Please be patient as this can take a while to complete depending on your system's specifications.
What is a BleepingComputer?
Welcome to BleepingComputer, a free community where people like yourself come together to discuss and learn how to use their computers. Using the site is easy and fun. As a guest, you can browse and view the various discussions in the forums, but can not create a new topic or reply to an existing one unless you are logged in. Other benefits of registering an account are subscribing to topics and forums, creating a blog, and having no ads shown anywhere on the site.
How many people fall victim to Microsoft scams?
According to Microsoft's Digital Crime Unit, some 3.3 million people fall victim to the tech support scam every year, costing victims around $1.5 billion.
What happens if you call the IRS and hang up?
If you receive what is obviously a scam call (the IRS doesn't actually phone people to tell them they owe taxes) and hang up, the phone may ring again. This time, the caller claims to be from the police (complete with spoofed caller ID that seems to confirm it) and demands to know why you hung up.
How to deal with identity theft scam?
Here's our 10-point plan to deal with it: 1. Shut down and disconnect your device from the Internet.
What happens if a virus is detected?
Once you realize what's happened, you need to take immediate action to minimize the potential damage.
Is Tech Support a scam?
If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam. Tech companies just don't operate that way.
What Is A Remote Access Scam?
How Big Is The Problem?
- In Australia, remote access scams are now the sixth largest scam type. As of September, the total reported losses via the ACCC are $4.7 million, yet this only represents reported losses. We can safely assume that total losses run well into the tens of millions per annum. The losses are on the rise as well, with September 2020 representing a new record, with over $1.1 million lost and in e…
What Is The Impact on Victims?
- From a trust and emotional perspective, all victims are materially impacted by scams. From a loss perspective, the amounts can vary from a few thousand dollars to someone's entire life savings. Different banks have different approaches in terms of reimbursing customers — that is, at what stage is the bank liable for protecting the customer vs. the victim being responsible. However, th…
How Can We Protect Victims?
- Dubbed the “call that could wipe out your life savings,” four in ten consumers have not heard of remote access scams. Protection begins on the front lines, and raising awareness about these scams with consumers and businesses is a starting point. There is a lot of great work being done in this space by entities such as Scamwatch and UK Financeas well as by the banking industry it…
What Can Banks Do to Detect Remote Access Scams?
- Most authentication and fraud prevention solutions rely on known device and IP location parameters to measure fraud risk. While these controls can be effective, RATs, by design, circumvent traditional fraud detection tools that look for the presence of malware, bots, and blacklisted devices, or IP addresses. Instead of relying on static controls, BioCatchuses machin…