19 Ways You Can Make Remote Work Even More Secure.
- Use a secure remote access platform. A remote-access platform provides a secure way for employees to connect to their work computers from anywhere in ...
- Use an encrypted messaging app.
- Use a VPN.
- Use a password manager.
- Use a secure browser.
Full Answer
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...
How do I find my Remote Desktop Connection?
You'll need this later.
- Make sure you have Windows 10 Pro. To check, go to Start > Settings > System > About and look for Edition . ...
- When you're ready, select Start > Settings > System > Remote Desktop, and turn on Enable Remote Desktop.
- Make note of the name of this PC under How to connect to this PC. You'll need this later.
How to set up windows for remote file access?
- Select Start.
- In your programs list, Expand Windows Accessories, then select Remote Desktop Connection. ...
- Enter your home computer's IP address, then select Connect.
- Enter your Home computer's username and password, then select OK.
- Your computer is not certified by a third party verification service. ...
Is rdweb secure?
Using Remote Web Access is fine but is less secure than a good VPN, especially if you don't take extra precautions to secure it, i.e. using an alternate server only for RWA, placing it in a DMZ, getting a valid 3rd party SSL cert, etc. Thanks for your feedback! This person is a verified professional.
How do I make remote access secure?
Basic Security Tips for Remote DesktopUse strong passwords.Use Two-factor authentication.Update your software.Restrict access using firewalls.Enable Network Level Authentication.Limit users who can log in using Remote Desktop.
Which method of remote access is the most secure?
Implement a Secure Connection for Remote Network AccessWired Connection: A wired connection is the most secure method for remote network access.Home Wi-Fi: The second most secure network connection is using a secured home Wi-Fi connection.More items...•
Why is remote access not secure?
In many cases, servers with RDP publicly accessible to the internet have failed to enable multi-factor authentication (MFA). This means that an attacker who compromises a user account by exposing a weak or reused password through a brute force attack can easily gain access to a user's workstation via RDP.
Is remote access security secure?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
Which protocol for remote access is more secure and why?
POINT-TO-POINT TUNNELING PROTOCOL (PPTP) It's used to establish virtual connections across the internet via PPP and TCP/IP, enabling two networks to use the internet as their WAN link while retaining the security benefits of a private network. PPTP is a great option because it's simple and secure.
Which option creates a secure connection for remote workers?
The only way to secure your remote workforce is a secure VPN. Employees must connect from their laptops, desktops and mobile devices over a VPN connection. It's the secure, private method for virtually entering the corporate office, so to speak.
What are security considerations for remote users examples?
Five Remote Access Security Risks And How To Protect Against ThemWeak remote access policies. ... A deluge of new devices to protect. ... Lack of visibility into remote user activity. ... Users mixing home and business passwords. ... Opportunistic phishing attempts.
Is RDP secure without VPN?
Remote Desktop Protocol (RDP) Integrated in BeyondTrust Establishing remote desktop connections to computers on remote networks usually requires VPN tunneling, port-forwarding, and firewall configurations that compromise security - such as opening the default listening port, TCP 3389.
Why is secure remote access important?
A secure remote access system protects your employees from web-based threats such as phishing attacks, ransomware and malware while they're logged in to your company's network. These cyber incidents can lead to unauthorized access and use of both the company's business data and the employee's personal data.
What is secure remote access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
What are the methods for remote access?
Remote Access Control MethodsDirect (Physical) Line. The first direct remote access control that can be implemented is a direct line from a computer to the company's LAN. ... Virtual Private Network. Another method which is more common is establishing a VPN. ... Deploying Microsoft RDS.
What is secure remote access software?
SASE and secure remote access Secure Access Service Edge is an emerging concept that combines network and security functions into a single cloud service, not only to alleviate traffic from being routed through the data center, but also to embrace a remote workforce, IoT adoption and cloud-based application use.
What are the two types of remote access server?
Remote Access Methods1- Remote Access Server: It's one server in organization network that it is the destination of all remote access connections.2- Remote Access Client: All computers that remote connect to network, called remote access client or remote computer.More items...•
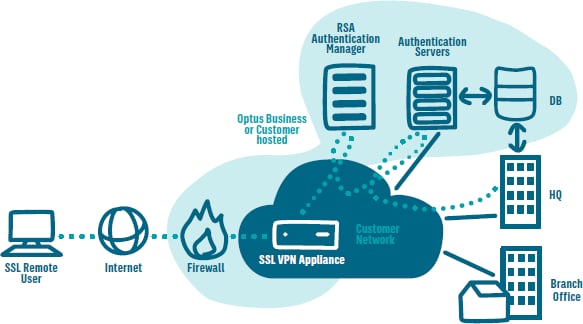
What is the first thing that’s required to ensure smooth remote access via a VPN?
The first thing that’s required to ensure smooth remote access via a VPN is to plan out a comprehensive network security policy.
What is the line of defense for remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly.
Why is IPSEC used?
This allows IPSec to protect data transmission in a variety of ways. IPSec is used to connect a remote user to an entire network. This gives the user access to all IP based applications. The VPN gateway is located at the perimeter of the network, and the firewall too is setup right at the gateway.
What are the implications of IPSec connections for corporations?
What are the implications of IPSec connections for corporations, considering the very nature of this connection? Well, your employee will only be able to access the network from a single, authorized device. Security is further boosted by the enforcement of antivirus and firewall policies.
What is IPSEC encryption?
IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect data flows between hosts and security gateways.
Why use two factor authentication for VPN?
Adopting two-factor authentication for remote access through VPN further boosts your network security. Now let’s take a look at why you should choose a particular VPN type as a secure connection methodology instead of the alternatives.
What is remote access VPN?
The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network (VPDN) due to its early adoption on dial-up internet.
What is secure remote access?
Secure remote access refers to any security policy, solution, strategy or process that exists to prevent unauthorized access to your network, its resources, or any confidential or sensitive data. Essentially, secure remote access is a mix of security strategies and not necessarily one specific technology like a VPN.
What technologies are used for secure remote access?
Secure remote access is comprised of a multitude of security solutions and technologies. Some of the most prominent include the following:
Secure remote access solution
Enables employees with precise access to the applications and data required to do their job from anywhere.
Why is secure remote access important?
With the work from home shift in the workforce, endpoints are accessing corporate networks from multiple locations. Today, employees’ home networks are often the originating point for network connections, multiplying the risk on both home and corporate networks.
What are the benefits of secure remote access?
While the benefits of secure remote access are numerous, there are four key advantages in which to focus on:
Can secure remote access be achieved without VPN?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
How can AT&T help organizations with secure remote access?
AT&T Cybersecurity is uniquely positioned to help organizations address these immediate challenges with an eye toward the future by helping them balance connectivity, collaboration, and cybersecurity affordably.
How Do I Set Up Secure Remote Access?
Determine a security policy for your organization that includes which level of access certain groups/levels of employees will have and which level of account verification you want to enable or enforce. Here are the security features you can enable in Splashtop:
Why is remote access important?
Since remote access enables accessing a company device from anywhere in the world over the public Internet, security is an important consideration. Plus, if you’re using to remote access to provide support to your customers’ computers and devices, then you can potentially put your customers’ data at risk too whenever a security issue arises.
What is splashtop remote support?
Splashtop Remote Support: for MSPs and IT teams who want unattended remote access to their users’ computers to provide remote support. LEARN MORE | FREE TRIAL
Can you lock your remote computer's keyboard and mouse?
Lock the remote computer’s keyboard and mouse while in session. Lock the streamer settings using Splashtop admin credentials. In your Splashtop Account Settings, you can enable Two-step verification. In your Splashtop Account Team Settings, you can enable or disable the following features: In-session file transfer.
Is Splashtop Secure?
Yes, Splashtop’s remote access and remote support solutions are highly secure. All connections are protected with TLS and 256-bit AES encryption. Splashtop also comes with top security features including device authentication and two-factor authentication. Plus, Splashtop’s cutting-edge infrastructure provides a secure computing environment with advanced intrusion prevention and firewalls at multiple layers.
Use a secure remote access platform
A remote-access platform provides a secure way for employees to connect to their work computers from anywhere in the world. With strong security features like two-factor authentication, password policies, and session monitoring, you can be sure that your data is safe when accessed remotely.
Use an encrypted messaging app
Messaging apps are a great way to keep in touch with employees when you're not in the office. However, not all messaging apps are created equal when it comes to security.
Use a VPN
A VPN (virtual private network) is a great way to keep your data safe when you're working remotely. It creates a secure connection between your device and the internet, which makes it difficult for anyone to track what you're doing online.
Use a password manager
A password manager is a great way to keep your passwords safe and secure. It stores all of your passwords in a secure encrypted database, so you don't have to remember them all yourself. You should also consider using a password randomizer. This tool generates unique, hard-to-crack passwords for all of your online accounts.
Use a secure browser
A secure browser like Tor Browser is a great way to keep your data safe when you're working remotely. It encrypts all of your traffic and prevents anyone from tracking what you're doing online. Secure browsing is especially important for employees who might be working abroad using public Wi-Fi networks.
Restrict access to certain applications
If you don't want employees to have access to certain applications or files when they're working remotely, you can restrict access to them using a remote access platform. This means that employees can only access the applications and files that you approve of, which helps to keep your data safe and secure and is part of good data governance.
Restrict internet usage
If you don't want employees to use the internet for personal reasons when they're working remotely, you can restrict their internet usage. This means that employees can only use the internet for work-related purposes, which helps to keep your data safe and secure.
How can information security managers mitigate external security threats?
Information security managers can mitigate external security threats by encrypting data to protect the confidentiality and integrity of communications and authenticating endpoints to verify identities.
What is telework security policy?
A telework security policy should define the form of remote access, types of telework devices allowed to use each form of remote access and the type of access each type of employee or contractor is granted. NIST also suggests the policy should cover how the organization's remote access servers are administered and how policies in those servers are ...
Do teleworkers have to have the same security?
Teleworkers' PCs, laptops and handhelds should have the same local security controls as client devices for non-telework employees. For instance, remote devices should receive the same application and security devices as those found in government facilities. They should employ antivirus software and personal firewalls.
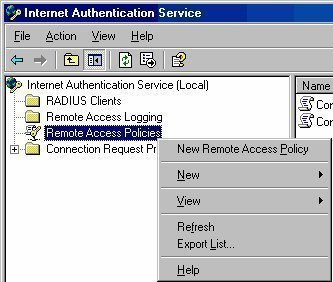
How to secure RDP?
Ananth: There are some built-in, no-cost defenses that can secure RDP. These include: 1 Patching: Keep servers especially up to date. 2 Complex passwords: Also use two-factor authentication, and implement lockout policies. 3 Default port: Change the default port used by RDP from 3389 to something else via the Registry. 4 Windows firewall: Use the built-in Windows firewall to restrict RDP sessions by IP address. 5 Network Level Authentication (NLA): Enable NLA, which is non-default on older versions. 6 Limit RDP access: Limit RDP access to a specific user group. Don't allow any domain admin to access RDP. 7 Tunnel RDP access: Tunnel access via IPSec or Secure Shell (SSH).
What are some built-in, no-cost defenses that can secure RDP?
Ananth: There are some built-in, no-cost defenses that can secure RDP. These include: Patching: Keep servers especially up to date. Complex passwords: Also use two-factor authentication, and implement lockout policies. Default port: Change the default port used by RDP from 3389 to something else via the Registry.
What is the RDP vulnerability?
Most notably, 2019 gave rise to a vulnerability known as BlueKeep that could allow cybercriminals to remotely take over a connected PC that's not properly patched.
What is RDP brute forcing?
Ananth: One common tactic is RDP brute-forcing, where attackers automate many login attempts using common credentials, hoping one hits. The second involves exploiting a software vulnerability to gain control of an RDP server. For instance, attackers could exploit BlueKeep ( CVE-2019-0708) to gain complete control of a managed service provider's (MSP) unpatched RDP servers.
What firewall is used to restrict RDP sessions?
Windows firewall: Use the built-in Windows firewall to restrict RDP sessions by IP address.
What is the first step in an attack chain that would likely be used to attack internal data stores and directory services?
Gamblin: Finding and exploiting an RDP vulnerability will be the first step in an attack chain that would likely be used to attack internal data stores and directory services to pivot to either a financial motive, or the ability to disrupt operations.
How many systems are exposed to the internet via RDP?
Web crawlers like shodan.io make it easy for attackers to quickly identify vulnerable public-facing machines. Worldwide, more than two million systems are exposed to the internet via RDP, of which more than 500,000 are in the US.
How to open local security policy?
Go to the Start menu or open a Run prompt (Windows Key + R) and type “secpol.msc” to open the Local Security Policy menu.
How to change rules on firewall?
When Windows Firewall opens, click “Advanced Settings” on the left side of the window . Then right-click on “Inbound Rules” and choose “New Rule.”
How to see who is logging into my PC?
If you’re wondering how you can keep track of who is logging into your PC (and from where), you can open up Event Viewer to see.
Is network level authentication necessary?
It’s not a necessity to require Network Level Authentication, but doing so makes your computer more secure by protecting you from Man in the Middle attacks . Systems even as old as Windows XP can connect to hosts with Network Level Authentication, so there’s no reason not to use it.
Is remote desktop secure?
How to Enable and Secure Remote Desktop on Windows. While there are many alternatives, Microsoft’s Remote Desktop is a perfectly viable option for accessing other computers, but it has to be properly secured. After recommended security measures are in place, Remote Desktop is a powerful tool for geeks to use and lets you avoid installing third ...
How secure is remote desktop?
How secure is Windows Remote Desktop? Remote Desktop sessions operate over an encrypted channel, preventing anyone from viewing your session by listening on the network. However, there is a vulnerability in the method used to encrypt sessions in earlier versions of RDP.
How to restrict access to remote desktop?
Use firewalls (both software and hardware where available) to restrict access to remote desktop listening ports (default is TCP 3389). Using an RDP Gateway is highly recommended for restricting RDP access to desktops and servers (see discussion below). As an alternative to support off-campus connectivity, you can use the campus VPN software to get a campus IP address and add the campus VPN network address pool to your RDP firewall exception rule. Visit our page for more information on the campus VPN service.
What is RDP gateway?
It provides a way to tightly restrict access to Remote Desktop ports while supporting remote connections through a single "Gateway" server. When using an RD Gateway server, all Remote Desktop services on your desktop and workstations should be restricted to only allow access only from the RD Gateway. The RD Gateway server listens for Remote Desktop requests over HTTPS (port 443) and connects the client to the Remote Desktop service on the target machine.
Why is RDP gateway important?
By enforcing the use of an RDP gateway, you also get a third level of auditing that is easier to read than combing through the domain controller logins and is separate from the target machine so it is not subject to tampering. This type of log can make it much easier to monitor how and when RDP is being used across all the devices in your environment.
What to do if remote desktop is not used?
If Remote Desktop is not used for system administration, remove all administrative access via RDP, and only allow user accounts requiring RDP service. For Departments that manage many machines remotely remove the local Administrator account from RDP access at and add a technical group instead.
How to check if you need authentication for remote connection?
To check you may look at Group Policy setting Require user authentication for remote connections by using Network Level Authentication found at ComputerPoliciesWindows ComponentsRemote Desktop ServicesRemote Desktop Session HostSecurity. This Group Policy setting must be enabled on the server running the Remote Desktop Session Host role.
Why is Remote Desktop better than 3rd party?
One advantage of using Remote Desktop rather than 3rd party remote admin tools is that components are updated automatically with the latest security fixes in the standard Microsoft patch cycle. Make sure you are running the latest versions of both the client and server software by enabling and auditing automatic Microsoft Updates. If you are using Remote Desktop clients on other platforms, make sure they are still supported and that you have the latest versions. Older versions may not support high encryption and may have other security flaws.