
What’s a Remote Access Trojan and How to Remove It Remotely
- Connect to the infected computer and reboot it into Windows Safe Mode to perform an in-depth virus cleanup. ...
- If the attacker has removed any antivirus from the infected computer, take advantage of the file transfer feature available in FixMe.IT remote desktop application and install the anti-malware software remotely.
- If the infection is already too serious, or your antivirus software cannot detect the RAT on the machine, go to Recovery settings and reset the user’s system completely.
Full Answer
How to get rid of remote access trojan (RAT)?
If you have difficulty in removing remote access trojan (RAT), it is suggested to download an advanced removal tool on your computer to get rid of the Trojan automatically and safely. remote access trojan (RAT) is a dangerous computer infection that gets into the target computers secretly without consent.
What are some examples of remote access trojan?
Remote Access Trojan Examples 1 Back Orifice. Back Orifice (BO) rootkit is one of the best-known examples of a RAT. ... 2 Sakula. Sakula, also known as Sakurel and VIPER, is another remote access trojan that first surfaced in November 2012. 3 Sub7. Sub7, also known as SubSeven or Sub7Server, is a RAT botnet. ... 4 PoisonIvy. ... 5 DarkComet. ...
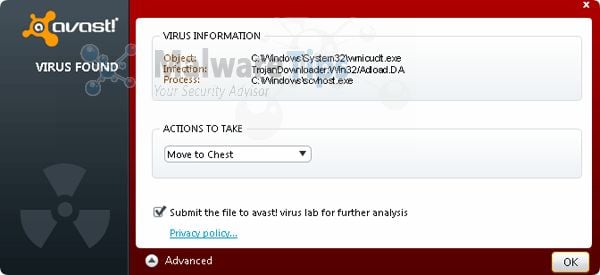
Which is the Best Antivirus for remote access trojan detection?
Remote Access Trojan Detection 1 Avast 2 AVG 3 Avira 4 Bitdefender 5 Kaspersky 6 Malwarebytes 7 McAfee 8 Microsoft Windows Defender 9 Norton 10 PC Matic 11 Sophos 12 Trend Micro More ...
Can you remove a trojan virus?
Trojan viruses can be removed in various ways. If you know which software contains the malware, you can simply uninstall it. However, the most effective way to remove all traces of a Trojan virus is to install antivirus software capable of detecting and removing Trojans.
Can remote access Trojans be detected?
AIDE—short for Advanced Intrusion Detection Environment—is a HIDS designed specifically to focus on rootkit detection and file signature comparisons, both of which are incredibly useful for detecting APTs like Remote Access Trojans.
How do I remove remote malware?
1:283:06How to remove a computer virus remotely - YouTubeYouTubeStart of suggested clipEnd of suggested clipYou can launch the anti-malware. Program first let's accept all the licensing terms and clickMoreYou can launch the anti-malware. Program first let's accept all the licensing terms and click continue. And then start scanning.
Is remote access Trojan a malware?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
How are remote access Trojans delivered?
A remote access Trojan (RAT) is a malware program that includes a back door for administrative control over the target computer. RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment.
Can an Iphone get a remote access Trojan?
The iOS Trojan is smart and spies discretely, i.e. does not drain a battery. The RCS mobile Trojans are capable of performing all kinds of spying you can expect from such a tool, including location reporting, taking photos, spying on SMS, WhatsApp and other messengers, stealing contacts and so on.
How do I remove a Trojan virus from Windows 10?
Remove malware from your Windows PCOpen your Windows Security settings.Select Virus & threat protection > Scan options.Select Windows Defender Offline scan, and then select Scan now.
Can you get a virus from remote access?
Many remote access software solutions don't scan the remote computer for viruses or malware. If your home or work PC has been infected, and you're using it to access your office network remotely, then a hacker could easily install malware onto your business's servers and spread to every machine in your office.
What are the 7 steps of malware removal?
Malware Removal (scenario)Identify and research malware symptoms. ... Quarantine the infected systems. ... Disable System Restore (in Windows). ... Remediate the infected systems. ... Schedule scans and run updates. ... Enable System Restore and create a restore point (in Windows). ... Educate the end user.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
Can Kaspersky detect remote access Trojan?
Put a good antivirus on your smartphone. For example, Kaspersky Internet Security for Android not only finds and removes Trojans, but also blocks websites with malware and mobile subscriptions.
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
Which virus that Cannot be detected by antivirus software is?
A stealth virus has an intelligent architecture, making it difficult to eliminate it completely from a computer system. The virus is smart enough to rename itself and send copies to a different drive or location, evading detection by the system's antivirus software.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
What is the best remote access Trojan?
10 Best Remote Access Software (Remote Control Software) In 2022Comparison of Top Remote Access Tools.#1) NinjaOne (Formerly NinjaRMM)#2) SolarWinds Dameware Remote Support.#3) Atera.#4) Supremo.#5) ManageEngine Remote Access Plus.#6) RemotePC.#7) TeamViewer.More items...•
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
What is RAT software?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can ac...
What’s the difference between the RAT computer virus and RAT software?
As for functions, there is no difference between the two. Yet, while remote administration tool is for legit usage, RAT connotes malicious and crim...
What are the popular remote access applications?
The common remote desktop tools include but are not limited to TeamViewer, AnyDesk, Chrome Remote Desktop, ConnectWise Control, Splashtop Business...
What are Remote Access Trojans?
Remote Access Trojans (RATs) are programs that allow hackers to control or monitor your computer remotely, usually through the internet. RATs can be either purchased or programmed by a hacker him-or-herself, but generally they fall under three categories:
How to prevent a RAT from taking over your computer again?
Plugging the Ethernet cable into your router and disabling WiFi should prevent a RAT from taking over your computer again. If you do not plug in an Ethernet cord, ensure that your wireless is turned off and that all security programs are up to date as this will stop any future attacks.
Why are some files missing on my computer?
Some files on your computer may be missing. Those data are still in the computer, but they are hidden by the virus and you have no way to make them show up. Furthermore, the Trojan virus may bring more and more other cyber infections to the same machine, which making the situation worse.
Why does a RAT stay on my computer?
The reason why remote access trojan (RAT) can stay in your computer for a long time is its capacity to trespass the system security utility, such as system firewall and authentic security software, through the way of pretending to be a system component. You should remove remote access trojan (RAT) manually as soon as possible.
What is locksmith angels?
Although Locksmith Angels’ main aim is on emergency business and home locksmith servicing, we also provide a wide variety of automotive services for your safety.
What is a RAT?
remote access trojan (RAT) is a dangerous computer infection that gets into the target computers secretly without consent. It causes your computer to function abnormally and drops additional threats to further destroy your computer. Furthermore, it has conflicts with many system programs.
Can a Trojan attack a computer?
Most of time, this Trojan virus can still attack your computer even you have an antivirus program safeguard your computer. For this reason, we all shall be more careful when we are viewing anything online. remote access trojan (RAT) is capable of installing itself on the target machine within a short time without your knowledge.
Can a Trojan be silently modified?
It can silently make modification on the Windows registry as well as crucial system settings and options, which will offer it the access to the deep of the system and perform undesirable task as soon as you turn on the system. It is wise to get rid of the Trojan from your computer in time. The infected computer will perform very slowly and weirdly.
Is manual removal effective?
The Manual removal is effective but not for everyone, especially for a regular PC user. If you have difficulty in removing remote access trojan (RAT), it is suggested to download an advanced removal tool on your computer to get rid of the Trojan automatically and safely.
A Reader Writes
For the past month my computer has been acting strangely. From what I've read, I'm pretty sure it's been infected with a Remote Access Trojan. Obviously, I'm really concerned.Can you tell me how to remove them, and how I can avoid getting infected in the future?
Matthew's Reply
Ouch. Remote Access Trojans are nasty, simply because they allow an attacker to do just that – remotely access your machine from anywhere in the world.
Knowing When You're Infected
So, how do you know when you've been infected? Well, a good clue is when your computer is acting strangely.
Turn Off the Internet
The first step is, obviously, to disconnect your computer from the Internet.
Fire Up Your Anti-Malware Software
If you're sensible, you've likely already got some anti-malware already installed and updated. Now it's just a matter of running it, and hoping that it catches whatever's installed.
Wipe Your System
One of the biggest problems with RAT malware is that it gives the attacker complete control of your system. If they want, they can easily install additional malware. There's also the risk that your chosen anti-malware won't recognize the RAT on your system. With that in mind, you might be tempted to just wipe your machine and start afresh.
Prevention is Better Than the Cure
The most effective way to deal with RATs is to not get infected in the first place. I know, it's easier said than done, but by adopting a few strategies, you drastically improve your odds.
Can a Remote Access Trojan be installed to BIOS?
Access to the BIOS has been known to the world’s hackers since 2015. Many believe that the NSA was planting RATs and trackers on BIOS even earlier.
What is intrusion detection?
Intrusion detection systems are important tools for blocking software intrusion that can evade detection by antivirus software and firewall utilities. The SolarWinds Security Event Manager is a Host-based Intrusion Detection System. However, there is a section of the tool that works as a Network-based Intrusion Detection System. This is the Snort Log Analyzer. You can read more about Snort below, however, you should know here that it is a widely used packet sniffer. By employing Snort as a data collector to feed into the Snort Log Analyzer, you get both real-time and historic data analysis out of the Security Event Manager.
How does a RAT toolkit work?
Other elements propagate the RAT by sending out links to infected web pages. These are sent to the social media contacts of an infected user.
What is SIEM in security?
This dual capability gives you a full Security Information and Event Management (SIEM) service. This means that you can watch Snort-captured events live and also examine cross-packet intrusion signatures identified through log file records.
How does Beast RAT work?
The Beast RAT attacks Windows systems from Windows 95 up to Windows 10. This uses the same client-server architecture that Back Orifice pioneered with the server part of the system being the malware that gets installed surreptitiously on the target computer. Once the server element is operational, the hacker can access the victim computer at will through the client program. The client connects to the target computer at port number 6666. The server is also able to open connections back to the client and that uses port number 9999. Beast was written in 2002 and is still widely in use.
How to get rid of a RAT?
Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system. RAT prevention systems are rare because the RAT software can only be identified once it is operating on your system.
What can a hacker do with a RAT?
A hacker with a RAT can command power stations, telephone networks, nuclear facilities, or gas pipelines. RATs not only represent a corporate network security risk, but they can also enable belligerent nations to cripple an enemy country.
