
21 Server Security Tips to Secure Your Server
- Secure Server Connectivity. When connecting to a remote server, it is essential to establish a secure channel for communication.
- Server User Management. Using intrusion prevention software to monitor login attempts is a way to protect your server against brute force attacks.
- Server Password Security. The first thing is to set password requirements and rules that must be followed by all members on the server.
- Other Best Practices to Secure a Server. Regularly updating the software on a server is a crucial step in keeping it safe from hackers. ...
- Develop a Cybersecurity Policy For Remote Workers. ...
- Choose a Remote Access Software. ...
- Use Encryption. ...
- Implement a Password Management Software. ...
- Apply Two-factor Authentication. ...
- Employ the Principle of Least Privilege. ...
- Create Employee Cybersecurity Training.
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
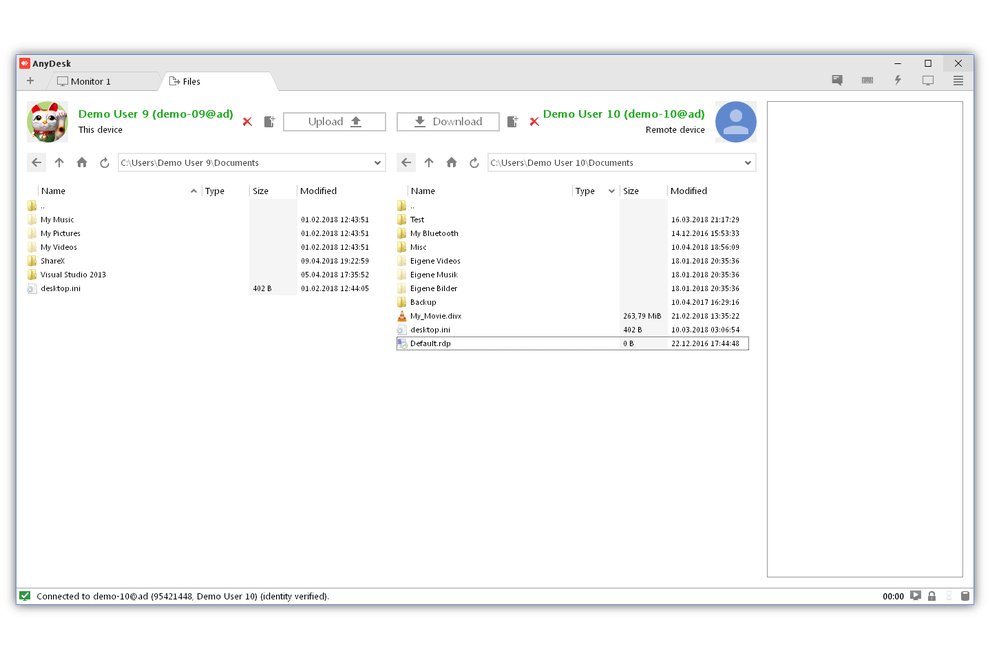
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...
How do I find my Remote Desktop Connection?
You'll need this later.
- Make sure you have Windows 10 Pro. To check, go to Start > Settings > System > About and look for Edition . ...
- When you're ready, select Start > Settings > System > Remote Desktop, and turn on Enable Remote Desktop.
- Make note of the name of this PC under How to connect to this PC. You'll need this later.
How to set up windows for remote file access?
- Select Start.
- In your programs list, Expand Windows Accessories, then select Remote Desktop Connection. ...
- Enter your home computer's IP address, then select Connect.
- Enter your Home computer's username and password, then select OK.
- Your computer is not certified by a third party verification service. ...
Is rdweb secure?
Using Remote Web Access is fine but is less secure than a good VPN, especially if you don't take extra precautions to secure it, i.e. using an alternate server only for RWA, placing it in a DMZ, getting a valid 3rd party SSL cert, etc. Thanks for your feedback! This person is a verified professional.
Which method of remote access is the most secure?
Implement a Secure Connection for Remote Network AccessWired Connection: A wired connection is the most secure method for remote network access.Home Wi-Fi: The second most secure network connection is using a secured home Wi-Fi connection.More items...•
How do I keep my remote workers secure?
Here are a few security best practices your remote employees should follow.Run software updates regularly. ... Secure video meetings. ... Watch out for email phishing. ... Create strong passwords. ... Never leave your bag, briefcase or laptop unattended. ... Use caution with wireless networks. ... Keep your work separate.
What is secure remote access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
What are the most common remote work security risks?
Top Security Risks of Remote WorkingGDPR and remote working. Remote work means an employer has less control and visibility over employees' data security. ... Phishing Emails. ... Weak Passwords. ... Unsecured Home Devices. ... Unencrypted File Sharing. ... Open Home WiFi Networks.
What are some ways to successfully and securely work from home?
Secure your home office and remote workUse antivirus software. ... Make sure your system and programs are up to date. ... Pay attention to Wi‑Fi and network security. ... Secure your privacy with a VPN. ... Avoid oversharing your screen. ... Beware phishing scams. ... Don't share personal information in messages or social media.More items...
Which will create a secure Internet connection while working remotely?
6) Set up a VPN Setting up a VPN and requiring all remote connections to pass through it is a basic best practice for keeping resources secure when employees work remotely.
What are some ways to successfully and securely work from home select all that apply?
Security Tips for Employees Working From HomeSecure Your Home Office. ... Secure Your Home Router. ... Separate Work and Personal Devices. ... Encrypt Your Devices. ... Use Supported Operating Systems. ... Keep Your Operating System Up-To-Date. ... Keep Your Software Up-To-Date. ... Enable Automatic Locking.More items...•
What are some ways a manager can do to secure their employees data?
9 Ways to Protect Sensitive Employee Information#1: Develop formal policies and procedures. ... #2: Maintain records securely. ... #3: Comply with recordkeeping laws. ... #4: Restrict access. ... #5: Keep an access log and monitor it. ... #6: Investigate incidents of unauthorized access. ... #7: Avoid using SSNs when possible.More items...•
What is remote access VPN?
The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network (VPDN) due to its early adoption on dial-up internet.
What is the first thing that’s required to ensure smooth remote access via a VPN?
The first thing that’s required to ensure smooth remote access via a VPN is to plan out a comprehensive network security policy.
Why is IPSEC used?
This allows IPSec to protect data transmission in a variety of ways. IPSec is used to connect a remote user to an entire network. This gives the user access to all IP based applications. The VPN gateway is located at the perimeter of the network, and the firewall too is setup right at the gateway.
What are the implications of IPSec connections for corporations?
What are the implications of IPSec connections for corporations, considering the very nature of this connection? Well, your employee will only be able to access the network from a single, authorized device. Security is further boosted by the enforcement of antivirus and firewall policies.
What is IPSEC encryption?
IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect data flows between hosts and security gateways.
Why use two factor authentication for VPN?
Adopting two-factor authentication for remote access through VPN further boosts your network security. Now let’s take a look at why you should choose a particular VPN type as a secure connection methodology instead of the alternatives.
What is the line of defense for remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly.
Why is remote access important?
It is essential for these individuals to have safe, anytime, anywhere access to corporate networks and services.
What are the risks of remote access?
Many potential risks accompany vendor remote access —from introducing malware into your systems to technical and business dangers.
What percentage of Verizon network intrusions exploited weak or stolen credentials?
According to Verizon’s Data Breach Investigation Report, “76 percent of network intrusions exploited weak or stolen credentials.” Since vendors don’t need constant access to your network, they often use one remote access tool license and share generic logins and passwords across technicians. This makes the credentials easy for hackers to guess. What’s more, the vendor’s ex-employees often retain remote access to your systems.
What happens if you give access to an outsider?
Recognize that granting system access to an outsider lowers your security level to that of the external provider. If they lack strong security controls, they become your weakest link. If a hacker compromises their system, that partner can become a backdoor into your environment .
Why is reducing network entry points important?
By reducing network entry points to the least amount that are necessary, you increase your ability to monitor and block unwanted activity on your network.
Where should a server be placed?
Because of this, NIST recommends; in most cases, that a server should be placed at an enterprise's network perimeter so it serves as a single point of entry to the network and enforces the remote work security policy before any remote access traffic is permitted into the enterprise's internal networks.
Can compromised servers be used to eavesdrop?
The National Institute of Standards and Technology (NIST) advises that compromised servers could be wielded to eavesdrop on and manipulate remote access communications. They can also provide a starting point for attacking other hosts within your organization.
What is RDP server?
RDP is a protocol originally developed by Microsoft, which enables remote connection to a compute system. RDP is also available for MacOs, Linux and other operating systems. The RDP server listens on TCP port 3389 and UDP port 3389, and accepts connections from RDP clients.
What is SASE security?
SASE is a new security model, leveraging software-defined networking (SDN), that helps users connect securely to remote data centers. It includes technologies like cloud access security broker (CASB), secure web gateway (SWG), firewall as a service (FWaaS), and ZTNA (ZTNA, described above, can be a component within a SASE solution).
What is zero trust security?
In the zero trust security model, users only have the rights they need to perform the role they have. All user accounts and devices on the network are not trusted by default. This is very different from traditional security solutions that allow users full access to the target network.
Can an attacker compromise a VPN?
When an attacker compromises a VPN (virtual private network), they can easily gain access to the rest of the network. Historically, many companies deployed VPNs primarily for technical roles, enabling them to access key IT systems. Today, all users, including non-technical roles, might access systems remotely using VPN. The problem is that many old firewall rules allow access for VPN clients to almost anything on the network.
Who needs privileged accounts?
Many organizations need to provide privileged accounts for two types of users: employees and external users, such as technicians and contractors. However, organizations using external vendors or contractors must protect themselves from potential threats from these sources.
Is remote access technology progressing?
Remote access technology made great progress. There are many new ways for users to access computing resources remotely, from a variety of endpoint devices. Here are some of the technologies enabling secure remote access at organizations today.
How secure is remote desktop?
How secure is Windows Remote Desktop? Remote Desktop sessions operate over an encrypted channel, preventing anyone from viewing your session by listening on the network. However, there is a vulnerability in the method used to encrypt sessions in earlier versions of RDP.
How to restrict access to remote desktop?
Use firewalls (both software and hardware where available) to restrict access to remote desktop listening ports (default is TCP 3389). Using an RDP Gateway is highly recommended for restricting RDP access to desktops and servers (see discussion below). As an alternative to support off-campus connectivity, you can use the campus VPN software to get a campus IP address and add the campus VPN network address pool to your RDP firewall exception rule. Visit our page for more information on the campus VPN service.
What is RDP gateway?
It provides a way to tightly restrict access to Remote Desktop ports while supporting remote connections through a single "Gateway" server. When using an RD Gateway server, all Remote Desktop services on your desktop and workstations should be restricted to only allow access only from the RD Gateway. The RD Gateway server listens for Remote Desktop requests over HTTPS (port 443) and connects the client to the Remote Desktop service on the target machine.
Why is RDP gateway important?
By enforcing the use of an RDP gateway, you also get a third level of auditing that is easier to read than combing through the domain controller logins and is separate from the target machine so it is not subject to tampering. This type of log can make it much easier to monitor how and when RDP is being used across all the devices in your environment.
What to do if remote desktop is not used?
If Remote Desktop is not used for system administration, remove all administrative access via RDP, and only allow user accounts requiring RDP service. For Departments that manage many machines remotely remove the local Administrator account from RDP access at and add a technical group instead.
How to check if you need authentication for remote connection?
To check you may look at Group Policy setting Require user authentication for remote connections by using Network Level Authentication found at ComputerPoliciesWindows ComponentsRemote Desktop ServicesRemote Desktop Session HostSecurity. This Group Policy setting must be enabled on the server running the Remote Desktop Session Host role.
Why is Remote Desktop better than 3rd party?
One advantage of using Remote Desktop rather than 3rd party remote admin tools is that components are updated automatically with the latest security fixes in the standard Microsoft patch cycle. Make sure you are running the latest versions of both the client and server software by enabling and auditing automatic Microsoft Updates. If you are using Remote Desktop clients on other platforms, make sure they are still supported and that you have the latest versions. Older versions may not support high encryption and may have other security flaws.
How to access remote access server?
On the Remote Access server, open the Remote Access Management console: On the Start screen, type, type Remote Access Management Console, and then press ENTER. If the User Account Control dialog box appears, confirm that the action it displays is what you want, and then click Yes.
How to install Remote Access on DirectAccess?
On the DirectAccess server, in the Server Manager console, in the Dashboard, click Add roles and features. Click Next three times to get to the server role selection screen. On the Select Server Roles dialog, select Remote Access, and then click Next.
How to deploy DirectAccess for remote management only?
In the DirectAccess Client Setup Wizard, on the Deployment Scenario page , click Deploy DirectAccess for remote management only, and then click Next.
How to add roles and features to DirectAccess?
On the DirectAccess server, in the Server Manager console, in the Dashboard, click Add roles and features.
What group does DirectAccess belong to?
For a client computer to be provisioned to use DirectAccess, it must belong to the selected security group . After DirectAccess is configured, client computers in the security group are provisioned to receive the DirectAccess Group Policy Objects (GPOs) for remote management.
How to add domain suffix in remote access?
On the DNS Suffix Search List page, the Remote Access server automatically detects domain suffixes in the deployment. Use the Add and Remove buttons to create the list of domain suffixes that you want to use. To add a new domain suffix, in New Suffix, enter the suffix, and then click Add. Click Next.
What is a remote access URL?
A public URL for the Remote Access server to which client computers can connect (the ConnectTo address)
What is remote desktop?
Remote Desktop is a Windows service that allows users to connect to a host computer from a different location. This allows users to access information stored on a separate computer from any place that allows them to log on to the Remote Desktop application. This has many practical applications in business, but also opens up some obvious security ...
How to change scope of remote desktop?
In the Firewall options, select the Exceptions tab and highlight Remote Desktop. Click the edit button followed by the Change Scope button.
How to limit users on a host computer?
Limit users who can log on to the host computer. Go to the host computer's system properties and select the Remote tab. If Remote Desktop is set up, the box that reads "Allow Users to Connect Remotely" should be checked. If not, check it now. Click the Select Remote Users button, and add which groups of users that can have access to the computer. ...
How to unlock a user who has been locked out?
In order to manually unlock a user who has been locked out, go to Administrative Tools in the Start Menu and select Computer Management. In the Local Users and Groups setting, you can click on an individual user and restore their access by un-checking the Account is Disable box.
Can you allow admin access to host computer?
In most versions of Windows, this will still allow users in the administrator group to access the host computer. If you want to change that, go to the Run box in your Windows Start Menu and enter
Can you use only certain IP addresses for remote desktop?
Allow only certain IP addresses to access the Remote Desktop. IP addresses are a unique series of numbers that identifies a computer, and through Windows it is possible to limit the Remote Desktop Connection to only known and trusted IP addresses. To do so, navigate to your Windows Firewall settings through the Windows Control Panel.
What is the best way to establish a secure connection?
When connecting to a remote server, it is essential to establish a secure channel for communication. Using the SSH (Secure Shell) Protocol is the best way to establish a protected connection. Unlike the previously used Telnet, SSH access encrypts all data transmitted in the exchange.
How to ensure secure communication?
Another way to ensure secure communication is to use private and virtual private networks (VPNs), and software such as OpenVPN (see our guide on installing and configuring OpenVPN on CentOS ). Unlike open networks which are accessible to the outside world and therefore susceptible to attacks from malicious users, private and virtual private networks restrict access to selected users.
What port does SSH use?
By default, SSH uses port 22. Everyone, including hackers, knows this. Most people do not configure this seemingly insignificant detail. However, changing the port number is an easy way to reduce the chances of hackers attacking your server.
What is FTPS file transfer protocol?
It encrypts data files and your authentication information. FTPS uses both a command channel and a data channel, and the user can encrypt both.
Why use a VPN?
When you want to connect to a remote server as if doing it locally through a private network, use a VPN. It enables an entirely secure and private connection and can encompass multiple remote servers. For the servers to communicate under the same VPN, they must share security and configuration data.
Why is a certificate important for a server?
Not only does the certificate encrypt data, but it is also used for user authentication. Therefore, by managing certificates for your servers, it helps establish user authority. Administrators can configure servers to communicate with centralized authority and any other certificate that the authority signs.
When to set up a firewall?
Set up a firewall during the initial server setup or when you make changes to the services the server offers. By default, a typical server runs different services including public, private and internal services.
Can you share PrivX credentials?
So even when using shared accounts, the user cannot share any credentials to anyone else.
Can you restrict access to specific networks?
You can also restrict access to only to specific networks/target hosts when connecting from the PrivX GUI to websites. Login as self to web target is possible if the user provides own credentials for the web service. Again, optional session recording is possible. If needed, additional PrivX Extender component can be used to access Web targets (as well as SSH and RDP targets) in a private network or virtual private clouds (VPC).
How to secure RDP?
Ananth: There are some built-in, no-cost defenses that can secure RDP. These include: 1 Patching: Keep servers especially up to date. 2 Complex passwords: Also use two-factor authentication, and implement lockout policies. 3 Default port: Change the default port used by RDP from 3389 to something else via the Registry. 4 Windows firewall: Use the built-in Windows firewall to restrict RDP sessions by IP address. 5 Network Level Authentication (NLA): Enable NLA, which is non-default on older versions. 6 Limit RDP access: Limit RDP access to a specific user group. Don't allow any domain admin to access RDP. 7 Tunnel RDP access: Tunnel access via IPSec or Secure Shell (SSH).
What firewall is used to restrict RDP sessions?
Windows firewall: Use the built-in Windows firewall to restrict RDP sessions by IP address.
What is the RDP vulnerability?
Most notably, 2019 gave rise to a vulnerability known as BlueKeep that could allow cybercriminals to remotely take over a connected PC that's not properly patched.
What is RDP brute forcing?
Ananth: One common tactic is RDP brute-forcing, where attackers automate many login attempts using common credentials, hoping one hits. The second involves exploiting a software vulnerability to gain control of an RDP server. For instance, attackers could exploit BlueKeep ( CVE-2019-0708) to gain complete control of a managed service provider's (MSP) unpatched RDP servers.
What are some built-in, no-cost defenses that can secure RDP?
Ananth: There are some built-in, no-cost defenses that can secure RDP. These include: Patching: Keep servers especially up to date. Complex passwords: Also use two-factor authentication, and implement lockout policies. Default port: Change the default port used by RDP from 3389 to something else via the Registry.
How many systems are exposed to the internet via RDP?
Web crawlers like shodan.io make it easy for attackers to quickly identify vulnerable public-facing machines. Worldwide, more than two million systems are exposed to the internet via RDP, of which more than 500,000 are in the US.
Can RDP be placed on the internet?
Some major organizations place RDP directly on the internet, but most (hopefully) are doing this unknowingly. Checking on this is pretty simple; just fire up your favorite internet-wide scanner and look at all the RDP instances directly exposed. Ananth: There are some built-in, no-cost defenses that can secure RDP.
