If you’ve already been victimized by a remote access scam, there are still ways you can recover from it. Contact the financial institution associated with any payment method you gave the scammer, such as your credit card issuer or bank, and tell them about the scam. While it may be difficult to recover funds taken directly from your bank account, it’s often quite easy to dispute credit card charges related to fraud, and credit cards generally have better security features for customers. You should also file a complaint with the FTC, as your report will help them track down and build a case against the scammers.
Full Answer
What is a remote access scam?
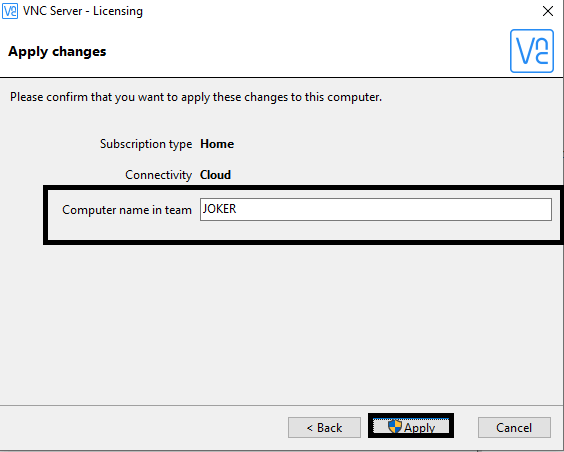
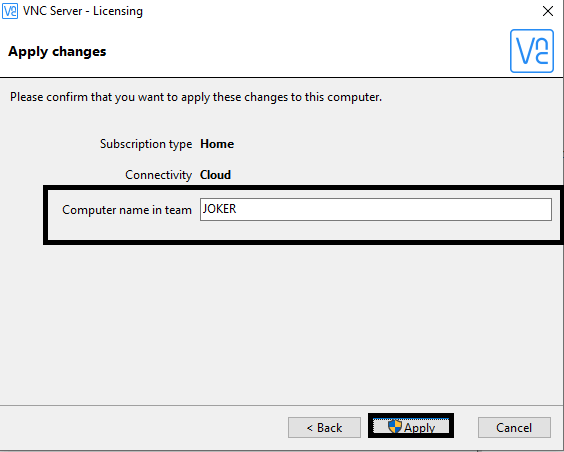
Remote access scams are a unique scenario where victims are socially engineered to provide remote access to their computer via a legitimate remote access tool such as TeamViewer, LogMeIn, Go-To-Meeting, or a similar remote desktop software.
What happens if you give a tech support scammer access to computer?
Once you've given a tech support scammer access to your computer, they can access your computer over and over again, scanning it for passwords, bank accounts and lots of other sensitive data. Click here to access a step-by-step plan to remove scammers ability to access your computer remotely.
How do you spot a tech support scam?
It's simple. If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam. Tech companies just don't operate that way. But tech support scammers do.
How do computer scams affect the elderly?
Once given permission to take over the computer, the scammer is able to steal personal and financial information which can later be used to defraud the victim. Over 70% of these computer scams originate via a phone call, and 82% of losses are against victims aged 65 and over.

What happens if you give a scammer access to your phone?
By having your cell number, a scammer could trick caller ID systems and get into your financial accounts or call financial institutions that use your phone number to identify you. Once the scammer convinces your carrier to port out your number, you may never get it back. Scam porting is a big problem for phone owners.
What can I do if a scammer controls my computer?
If you gave a scammer remote access to your computer, update your computer's security software. Then run a scan and delete anything it identifies as a problem. If you gave your user name and password to a tech support scammer, change your password right away.
Can a scammer gain access to my phone?
Scammers use auto-dialers and spoofed area codes to trick people into picking up the phone. From there, it's a numbers game. The scammers want to get as much personal information from the call recipient as possible. That can include anything from names and birth dates to credit card numbers.
What can a scammer do with AnyDesk?
AnyDesk is used legitimately by millions of IT professionals worldwide, to remotely connect to their clients' devices to help with technical issues. However, scammers can try to misuse AnyDesk (or any other remote access software) to connect to your computer and steal data, access codes, and even money.
How do I stop remote access to my computer?
Open System and Security. Choose System in the right panel. Select Remote Settings from the left pane to open the System Properties dialog box for the Remote tab. Click Don't Allow Connections to This Computer and then click OK.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
Can someone hack my bank account with my phone number?
With your phone number, a hacker can start hijacking your accounts one by one by having a password reset sent to your phone. They can trick automated systems — like your bank — into thinking they're you when you call customer service.
What can a scammer do with my name and phone number?
With your personal information, scammers can:access and drain your bank account.open new bank accounts in your name and take out loans or lines of credit.take out phone plans and other contracts.purchase expensive goods in your name.steal your superannuation.gain access to your government online services.More items...
Can someone access my phone remotely?
Yes. Unfortunately, they can even hack a phone's camera. But you can also learn how to block hackers from your Android or iOS phone.
Does deleting AnyDesk stop access?
With regards to Anydesk specifically, uninstalling the application, is enough to prevent remote access to your system.
How do I completely remove AnyDesk?
Uninstallation via the “Control Panel”Go to Start and open Control Panel.Select the Programs tab.Click on “Programs and Features”.Find AnyDesk among the programs.In the window that appears, click “Delete”.
Can a scammer access my bank account?
Yes, this is possible. Identity theft was the number one reported type of fraud in 2020 [*], according to the FTC. When scammers gain access to your personal information by phishing, for example, they can do one or more of the following: Gain access to your bank account and spend or transfer all your money.
How do I report a computer scammer?
The Federal Trade Commission (FTC) is the main agency that collects scam reports. Report the scam to the FTC online, or by phone at 1-877-382-4357 (9:00 AM - 8:00 PM, ET).
Can someone lock your computer?
Locking your computer keeps your files safe while you are away from your computer. A locked computer hides and protects programs and documents, and will allow only the person who locked the computer to unlock it again. You unlock your computer by logging in again (with your NetID and password).
How do I get rid of fake Microsoft security warning?
How to Remove the “Virus Alert from Microsoft” Scam in 2022Preliminary Step: Close the “Virus Alert from Microsoft” Notification.Run a Full System Scan With Your Antivirus.Delete Any Infected Files.Keep Your Device Protected Against Dangerous Websites.
Can Microsoft freeze your computer?
To prevent further issues, users should immediately contact 'Microsoft Technicians' via a telephone number ("1-800-745-9386") provided. They will then supposedly receive help in resolving these issues. In fact, "Microsoft Has Blocked The Computer" error is fake - a scam that has nothing to do with Microsoft.
How to stop a scammer from stealing my computer?
First you need to do damage control. That means you should do an erase and install of your system from the ground up. You have possibly compromised your whole system to the scammer. Change all of your passwords and if you store any credit card or other financial information on the computer notify you banks and change that information too.
What to do if you don't have a pre-breach backup?
If you don't have a pre-breach backup, then make a backup of the system disk to external storage, then wipe the disk and reinstall from known-good distributions, and migrate over only documents and not applications from the backup copy. Anything on this disk is now questionable at best.
What is a remote access scam?
Remote access scams are a unique scenario where victims are socially engineered to provide remote access to their computer via a legitimate remote access tool such as TeamViewer , LogMeIn, Go-To-Meeting, or a similar remote desktop software . Once given permission to take over the computer, the scammer is able to steal personal and financial information which can later be used to defraud the victim.
What can banks do to detect remote access scams?
Most authentication and fraud prevention solutions rely on known device and IP location parameters to measure fraud risk. While these controls can be effective, RATs, by design, circumvent traditional fraud detection tools that look for the presence of malware, bots, and blacklisted devices, or IP addresses.
How can we protect victims?
Protection begins on the front lines, and raising awareness about these scams with consumers and businesses is a starting point. There is a lot of great work being done in this space by entities such as Scamwatch and UK Finance as well as by the banking industry itself. However, this is not an issue that can be addressed in isolation, as the sophistication of scams continues to improve.
Is cybercrime opportunistic?
Cybercrime is opportunistic, and there is no time like the present for criminals to adapt their tactics, old and new, to defraud online customers. Remote access scams are one of those tactics, and the number of attacks has grown during the COVID-19 pandemic. Cybercriminals are using the unstable environment to their advantage to take ...
How to stop remote access?
1. Shut down and disconnect your device from the Internet. That puts an absolute stop on any external meddling. It also often automatically revokes remote access for when you restart.
What is remote access on a PC?
You probably know what "remote access" is, but for those who don't, it's a feature of Windows that enables someone in another location to access your PC via the Internet.
How do I know whether a number I see is a fake Microsoft tech support number?
One of the favorite scam techniques is for tech support scammers to give you fake phone numbers they claim are a correct Microsoft tech support number. Don't fall for that scam. See above for the best way to find the correct Microsoft tech support number.
How many people fall victim to Microsoft scams?
According to Microsoft's Digital Crime Unit, some 3.3 million people fall victim to the tech support scam every year, costing victims around $1.5 billion.
What can hackers look for in a computer?
Once they get access, they can digitally crawl all over your PC, looking for confidential information like passwords and account numbers.
How do you know if you're a victim of a scam?
How will you know you're one of those victims? It's simple. If someone phoned you claiming to be from Tech Support or claiming they've detected a virus on your PC and they need access, it was a scam.
What credit monitoring agencies freeze credit applications?
9. Put a freeze on credit applications via the three credit monitoring agencies -- Equifax, Experian and TransUnion . This will cost a few dollars but is worth it. Each of the bureaus has its own "credit lock" service but you might find the following article useful: Credit Freeze and Thaw Guide.