The real fact is that the person that you allowed to remotely connect to your computer is a criminal. When you gave permission for the criminals to access your computer, they are not removing any virus, or fixing the computer, they are actually stealing all of the personal information on your hard drive.
Full Answer
Should I allow remote access to my computer?
Allowing someone to remotely access your computer is not a bad thing, it can be very helpful. Unfortunately, there are a lot of criminals out there that take advantage of this tool to take over your computer. When this happens, it could cost you dearly.
How do I connect to a remote PC?
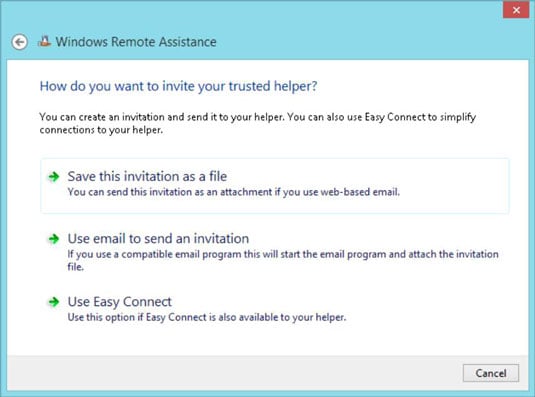
To connect to a remote PC, that computer must be turned on, it must have a network connection, Remote Desktop must be enabled, you must have network access to the remote computer (this could be through the Internet), and you must have permission to connect.
How do I get permission to connect to a remote desktop?
For permission to connect, you must be on the list of users. Before you start a connection, it's a good idea to look up the name of the computer you're connecting to and to make sure Remote Desktop connections are allowed through its firewall.
How did my husband fall for the Microsoft Remote Access scam?
My trusting husband fell for the scam where a pop up window told him that there was a problem with his computer and to call a number pretending to be Microsoft. He called them and gave them remote access to our computer.

What happens if you give someone remote access to your computer?
This can be even worse than just conning you out of money, as undetected malware can allow hackers to steal your identity, including your passwords and financial information, over and over again, even if you get new passwords and account numbers.
How do I stop remote access to my computer?
Open System and Security. Choose System in the right panel. Select Remote Settings from the left pane to open the System Properties dialog box for the Remote tab. Click Don't Allow Connections to This Computer and then click OK.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
What can a scammer do with AnyDesk?
AnyDesk is used legitimately by millions of IT professionals worldwide, to remotely connect to their clients' devices to help with technical issues. However, scammers can try to misuse AnyDesk (or any other remote access software) to connect to your computer and steal data, access codes, and even money.
What happens when someone hacks your computer?
If your computer is hacked, you might notice some of the following symptoms: Frequent pop-up windows, especially the ones that encourage you to visit unusual sites, or download antivirus or other software. Changes to your home page. Mass emails being sent from your email account.
How do I block remote access to administrator?
How to disable Remote Desktop Access for Administrators PrintPress Win+R.Type secpol.msc and hit Enter:Navigate to: Security Settings\Local Policies\User Rights Assignment. ... Click Add User or Group:Click Advanced:Click Find Now:Select the user you want to deny access via Remote Desktop and click OK:Click OK here:More items...•
How can I tell who is remoted into my computer?
RemotelyHold down the Windows Key, and press “R” to bring up the Run window.Type “CMD“, then press “Enter” to open a command prompt.At the command prompt, type the following then press “Enter“: query user /server:computername. ... The computer name or domain followed by the username is displayed.
Can someone see me through my computer screen?
But, just like any other tech devices, webcams are prone to hacking, which can lead to a serious, unprecedented privacy breach. Think of a case where an authorized person accesses and illegally takes control of your webcam, without your knowledge. Such a person will effortlessly spy on you and the people around you.
Is someone monitoring my computer?
Look for Suspicious Processes You can find suspicious processes by opening the Windows Task Manager. After booting up your computer and loading Windows, press Ctrl+Alt+Del and select “Task Manager.” From the “Processes” tab, scroll through the list of active running while looking for any that are out of the ordinary.
How do I completely remove AnyDesk?
Uninstallation via the “Control Panel”Go to Start and open Control Panel.Select the Programs tab.Click on “Programs and Features”.Find AnyDesk among the programs.In the window that appears, click “Delete”.
Does deleting AnyDesk stop access?
With regards to Anydesk specifically, uninstalling the application, is enough to prevent remote access to your system.
How do I remove access from AnyDesk?
To revoke permissions for connecting to your PC, there are two options:Press the “Clear All Tokens” Button. You can disable this feature entirely by checking the option in the “Security” tab. ... Change the Password. Even changing the password to the same password again invalidates all tokens.
Do hackers use AnyDesk?
Sophos discovered that the AvosLocker attackers installed AnyDesk so it works in Safe Mode, tried to disable the components of security solutions that run in Safe Mode, and then ran the ransomware in Safe Mode.
Is IT safe to give AnyDesk access?
AnyDesk Remote Desktop Software comes with the highest security standards. From military-grade encryption to customizable security features, AnyDesk offers outstanding security that perfectly fits your needs.
Is IT safe to share AnyDesk ID?
It's completely secure and a tool for when IT experts want to work on remote devices without being on-site. In addition, AnyDesk uses banking-standard TLS 1.2 technology to protect users' computers, as well as RSA 2048 asymmetric key exchange encryption to verify every connection.
What are the disadvantages of AnyDesk app?
The Cons. It can be slightly intimidating for first-time users. It cannot work without an active internet connection. The free version doesn't have the address book feature.
How to Enable Remote Desktop
The simplest way to allow access to your PC from a remote device is using the Remote Desktop options under Settings. Since this functionality was a...
Should I Enable Remote Desktop?
If you only want to access your PC when you are physically sitting in front of it, you don't need to enable Remote Desktop. Enabling Remote Desktop...
Why Allow Connections only With Network Level Authentication?
If you want to restrict who can access your PC, choose to allow access only with Network Level Authentication (NLA). When you enable this option, u...
What happens when you give permission for a criminal to access your computer?
When you gave permission for the criminals to access your computer, they are not removing any virus, or fixing the computer, they are actually stealing all of the personal information on your hard drive. Any personal information on that computer now belongs to them. See the following links.
Can I change my passwords and notify all financial institutions?
Generally - you're probably fine - but I would change all your passwords and notify all financial institutions you deal with and watch your credit rating.
How to stop someone from accessing my computer?
This includes removing any Ethernet cables and turning off your Wi-Fi connections.
How to install antivirus on another computer?
If you don't have an antivirus, download an installer on another computer and transfer it to your computer via USB. Install the antivirus and then run a scan with it.
How to know if malware has been removed?
Monitor your computer after removing any malware. If your antivirus and/or Anti-Malware found malicious programs, you may have successfully removed the infection, but you'll need to keep a close eye on your computer to ensure that the infection hasn't remained hidden.
What to do if your computer is compromised?
Change all of your passwords . If your computer was compromised, then there’s a possibility that all of your passwords have been recorded with a keylogger. If you’re sure the infection is gone, change the passwords for all of your various accounts. You should avoid using the same password for multiple services.
Why is public Wi-Fi so dangerous?
Try to avoid public Wi-Fi spots. Public Wi-Fi spots are risky because you have zero control over the network. You can't know if someone else using the spot is monitoring traffic to and from your computer. By doing this, they could gain access to your open browser session or worse. You can mitigate this risk by using a VPN whenever you are connected to a public Wi-Fi spot, which will encrypt your transfers.
What to do if you can't get rid of intrusion?
If you're still experiencing intrusions, or are concerned that you may still be infected, the only way to be sure is to completely wipe your system and reinstall your operating system.
Why does my computer turn on without my input?
If your computer appears to turn on without your input when you're not using it, it is likely waking from Sleep mode to install updates .
How to run JRT as administrator?
Run the tool by double-clicking it. If you are using Windows Vista, 7, or 8; instead of double-clicking, right-mouse click JRT.exe and select "Run as Administrator". The tool will open and start scanning your system. Please be patient as this can take a while to complete depending on your system's specifications.
Can I use the programs below to clean, remove adware and remove malware?
You can use the programs below to clean, remove adware and remove malware. Though I doubt the criminals installed any, it would be a good idea
Can you rerun MBAM?
Rerun MBAM and be sure to allow it to remove that one threat that it found .
How to stop a scammer from stealing my computer?
First you need to do damage control. That means you should do an erase and install of your system from the ground up. You have possibly compromised your whole system to the scammer. Change all of your passwords and if you store any credit card or other financial information on the computer notify you banks and change that information too.
What to do if you don't have a pre-breach backup?
If you don't have a pre-breach backup, then make a backup of the system disk to external storage, then wipe the disk and reinstall from known-good distributions, and migrate over only documents and not applications from the backup copy. Anything on this disk is now questionable at best.
What does it mean when a computer technician is remotely accessing your computer?
When a technician is remotely accessing your computer, you may be able to see what they are doing. Often, remote access software will show the other person’s actions to you on the screen. In addition to being able to see, there may be some kind of communication between you and the technician. This could be in the form of a voice or a chatbox.
Why Would You Want to Provide Remote Access?
There are several legitimate reasons to provide access to your computer. For instance, a remote desktop for Mac or PC can allow you to access files and folders stored on your computer when you are not near it.
What Are the Risks Involved in Giving Remote Access?
Before you let anyone else have remote access to your computer, you should, first of all, consider the risks .
What to Do If Someone Wants to Access Your Computer?
If someone does want to access your computer and they have phoned you, there is a strong chance that this is a hoax .
How to protect your computer from cybercriminals?
You should ensure that you have both antivirus and firewall protection installed and that you keep this updated. Make sure that you download and install all updates to your operating system.
What are the benefits of remote access?
The other benefit of being able to provide remote access is that a technician can get into your machine and fix any software problems that you may have.
What to do if you receive an unsolicited call?
If the call is unsolicited, ask for some credentials or proof of identity before you proceed in downloading, installing, or setting up any remote access software.
