This allows remote users to connect to the ASA and access the remote network through an IPsec encrypted tunnel. The remote user requires the Cisco VPN client
Cisco Systems VPN Client
Cisco Systems VPN Client is a software application for connecting to virtual private networks based on Internet Key Exchange version 1. On July 29, 2011, Cisco announced the end of life of the product. No further product updates were released after July 30, 2012, and support ce…
How to set up a VPN with Cisco?
Steps Download Article
- Make sure the Cisco VPN Client is installed on your remote computer. ...
- Collect the information needed to configure your Cisco VPN Client. ...
- Launch the Cisco VPN Client and access the VPN Dialer from where you have it stored on your computer.
- Configure and create a new connection entry. ...
How to install ASDM on Cisco ASA?
That said, here goes:
- Make sure ASDM image has been uploaded to the ASA you're needing to connect to.
- Enable HTTP on the ASA you are wanting to connect to
- Browse to the ASA's IP address
- Download ASDM installer from the Firewall (after authenticating)
Can you explain stateful inspection in Cisco ASA?
There is no such table on the ASA device specifically for stateful functionality. The only thing that would give you the details will be :- show conn Also, if you want to see which service is being inspected on the ASA device, you can check show service-policy and remember TCP, UDP etc protocols are always inspected on the ASA device.
Is IKEv2 support on Cisco ASA firewall?
It is on the roadmap, however to have support for IKEv2 across the board, including ASA. 02-26-2011 04:43 AM 02-26-2011 04:43 AM Please note that IKEv2 is supported on the Cisco ASA Firewalls starting from software v8.4, please see the following link:
Does remote access VPN use IPsec?
While Remote access VPN supports SSL and IPsec technology.
What is IPsec remote access VPN?
Internet Protocol Security (IPsec) is a suite of protocols that support cryptographically secure communication at the IP layer. With IPsec connections, you can provide secure access between two hosts, two sites, or remote users and a LAN. The firewall supports IPsec as defined in RFC 4301.
How do I access my Cisco ASA remotely?
There are eight basic steps in setting up remote access for users with the Cisco ASA.Configure an Identity Certificate.Upload the SSL VPN Client Image to the ASA.Enable AnyConnect VPN Access.Create a Group Policy.Configure Access List Bypass.Create a Connection Profile and Tunnel Group.Configure NAT Exemption.More items...•
What VPN types are supported by ASA?
For VPN Services, the ASA 5500 Series provides a complete remote-access VPN solution that supports numerous connectivity options, including Cisco VPN Client for IP Security (IPSec), Cisco Clientless SSL VPN, network-aware site-to-site VPN connectivity, and Cisco AnyConnect VPN client.
What is the difference between VPN and IPSec?
SSL VPNs. The major difference between an IPsec VPN and an SSL VPN comes down to the network layers at which encryption and authentication are performed. IPsec operates at the network layer and can be used to encrypt data being sent between any systems that can be identified by IP addresses.
What are the 3 protocols used in IPSec?
IPsec is a suite of protocols widely used to secure connections over the internet. The three main protocols comprising IPsec are: Authentication Header (AH), Encapsulating Security Payload (ESP), and Internet Key Exchange (IKE).
How does remote access VPN Work?
A remote access VPN works by creating a virtual tunnel between an employee's device and the company's network. This tunnel goes through the public internet but the data sent back and forth through it is protected by encryption and security protocols to help keep it private and secure.
What is remote access VPN Cisco?
This allows remote users to connect to the ASA and access the remote network through an IPsec encrypted tunnel. The remote user requires the Cisco VPN client software on his/her computer, once the connection is established the user will receive a private IP address from the ASA and has access to the network.
How do I run a Cisco VPN server?
Connect to VPNConnect to the internet.Open Cisco AnyConnect Secure Mobility Client.Enter vpn.cmu.edu and click Connect.Click the Group drop-down and choose the VPN option that best suits your needs.Enter your Andrew userID and password.Authenticate with 2fa (DUO).Click OK.
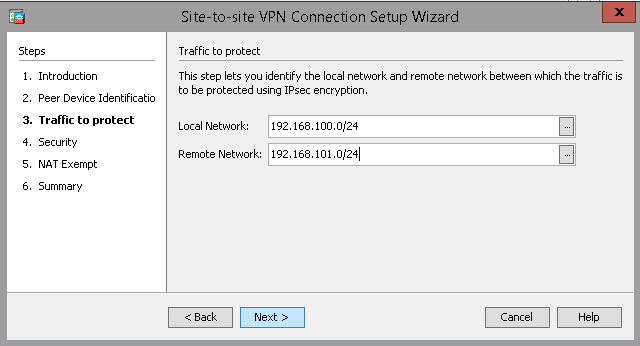
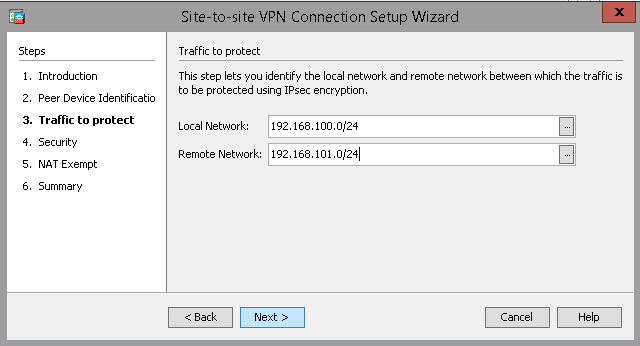
How do I configure IPsec on ASA firewall?
To configure the IPSec VPN tunnel on Cisco ASA 55xx:Configure IKE. Establish a policy for the supported ISAKMP encryption, authentication Diffie-Hellman, lifetime, and key parameters. ... Create the Access Control List (ACL) ... Configure IPSec. ... Configure the Port Filter. ... Configure Network Address Translation (NAT)
What are 3 types of VPN tunnels?
We'll look at three of the most common: IPsec tunnels, Dynamic multi point VPNs, and MPLS-based L3VPNs.IPsec Tunnels. In principle, a network-based VPN tunnel is no different from a client-based IPsec tunnel. ... Dynamic Multi point VPN (DMVPN) ... MPLS-based L3VPN.
Is Cisco AnyConnect IPsec or SSL?
Anyconnect is the replacement for the old Cisco VPN client and supports SSL and IKEv2 IPsec. When it comes to SSL, the ASA offers two SSL VPN modes: Clientless WebVPN.
What is the difference between IPSec and SSL VPN?
While an IPsec VPN allows users to connect remotely to an entire network and all its applications, SSL VPNs give users remote tunneling access to a specific system or application on the network. Choosing the right application comes down to a balance of convenience for the end-user and security for the organization.
Which is better IPSec or OpenVPN?
IPSec is generally regarded as faster than OpenVPN. The main reason for this is actually a pro for OpenVPN in another area, and that is how it is implemented. IPSec is implemented in the IP stack of the kernel, whereas OpenVPN is implemented in the userspace.
What is OpenVPN vs IPSec?
OpenVPN uses a chosen UDP or TCP port, allowing for flexible configuration choices. On the other hand, IPSec uses predefined communication channels, UDP 500 and UDP 4500, to establish the encrypted tunnel and ESP for the transmission of encrypted data.
How IPSec works step by step?
Interesting traffic initiates the IPSec process—Traffic is deemed interesting when the IPSec security policy configured in the IPSec peers starts the IKE process....Step 1: Defining Interesting Traffic. ... Step 2: IKE Phase One. ... Step 3: IKE Phase Two. ... Step 4: IPSec Encrypted Tunnel. ... Step 5: Tunnel Termination.
How many interfaces does an ASA have?
The ASA has two interfaces: inside and outside. Imagine the outside interface is connected to the Internet where a remote user wants to connect to the ASA. On the inside we find R1, I will only use this router so the remote user has something to connect to on the inside network. Let’s look at the configuration!
What is VPN_POLICY?
The group policy is called VPN_POLICY and it’s an internal group policy which means it is created locally on the ASA. You can also specify an external group policy on a RADIUS server. I added some attributes, for example a DNS server and an idle timeout (15 minutes). Split tunneling is optional but I added it to show you how to use it, it refers to the access-list we created earlier.
Does Cisco VPN require ASA?
The remote user requires the Cisco VP N client software on his/her computer, once the connection is established the user will receive a private IP address from the ASA and has access to the network .
Can remote VPN users access certain networks?
If you want to configure an access-list so the remote VPN users can only reach certain networks , IP addresses or ports then you can apply this under the group policy.
Can you use VPN on remote network?
If you don’t want this then you can enable split tunneling. With split tunneling enabled, we will use the VPN only for access to the remote network. Here’s how to enable it:
What is Cisco AnyConnect Secure Mobility Solution?
The Cisco AnyConnect Secure Mobility Solution provides a comprehensive, highly secure enterprise mobility solution. the Cisco AnyConnect Secure Mobility Solution continues to lead with next-generation security and encryption, including support for the Suite B set of cryptographic algorithms, and support for IPv6 networks. More importantly, it adapts its tunneling protocol to the most efficient method. AnyConnect client can be used to connect both SSL VPN as well as IKEv2 IPSec VPN. In this document we will see how to configure only IKEv2 IPSec VPN.
What is active/active failover?
Active/Active failover is only available to security appliances in multiple context mode. In an Active/Active failover configuration, both security appliances can pass network traffic. In Active/Active failover, you divide the security contexts on the security appliance into failover groups. A failover group is simply a logical group of one or more security contexts. You can create a maximum of two failover groups on the security appliance. The admin context is always a member of failover group 1. Any unassigned security contexts are also members of failover group 1 by default. We have already seen the configuration for Active/Standby failover in the previous article. This article focuses on how to configure an Active/Active Failover configuration on ASA Security Appliance. Network Diagram (Physical Topology)
What happens when a VPN user terminates a session?
Normally when the remote VPN user terminates the session, the anyconnect installer will be uninstalled. The anyconnect keep-installer installed command leaves it installed on the user’s computer.
When remote users connect to our WebVPN, do they have to use HTTPS?
The following option is not required but useful, whenever someone accesses the ASA through HTTP then they will be redirected to HTTPS:
What is AnyConnect VPN?
Anyconnect is the replacement for the old Cisco VPN client and supports SSL and IKEv2 IPsec. When it comes to SSL, the ASA offers two SSL VPN modes: Clientless WebVPN. AnyConnect VPN. The clientless WebVPN method does not require a VPN client to be installed on the user’s computer. You just open your web browser, ...
Why does my client tries to download AnyConnect?
The client tries to download the Anyconnect automatically, this is because of the anyconnect ask none default anyconnect command that we used. Since we are using a self-signed certificate you will get the following error message:
What is the IP address of AnyConnect?
You can see that we received IP address 192.168.10.100 (the first IP address from the VPN pool). Anyconnect creates an additional interface, just like the legacy Cisco VPN client does.
What is an ayconnECT_policy?
The group policy is called “ANYCONNECT_POLICY” and it’s an internal group policy which means that we configure it locally on the ASA. An external group policy could be on a RADIUS server.
Does Outlook have full network access?
Microsoft Outlook Web Access. There is no full network access when you use clientless WebVPN. Anyconnect VPN offers full network access. The remote user will use the anyconnect client to connect to the ASA and will receive an IP address from a VPN pool, allowing full access to the network. In this lesson we will use clientless WebVPN only for ...
What is VPN debug?
Run a VPN debug that is filtered for the peer IP on the VPN tunnel you're troubleshooting. The VPN debug will show each VPN phase as they establish and will give verbose errors about what goes wrong when the VPN tunnel fails to connect.
Can you run a packet tracer from ASA?
You can run a packet-tracer from the ASA CLI to simulate VPN traffic and see where traffic may be failing. In the following command, "inside" is our local interface, 192.168.1.100 is the local IP we're testing traffic from, 12345 is the source port (it can be anything you choose), and 192.168.2.100 is the remote IP we're trying to reach. This packet-tracer will simulate ICMP traffic.
