These are the primary remote access protocols that are in use today:
- Serial Line Internet Protocol (SLIP)
- Point-to-Point Protocol (PPP) and Point-to-Point Protocol over Ethernet (PPPoE)
- Point-to-Point Tunneling Protocol (PPTP)
- Remote Access Services (RAS)
- Remote Desktop Protocol (RDP)
How to setup RDP for remote access?
- Get the IP address for that PC using the procedure we outlined previously.
- Use Registry Editor to change the Remote Desktop listening port number on that PC.
- Make notes on which port number goes with which IP address.
How to properly secure remote access?
- Windows or Mac login when connecting remotely
- Request permission to connect to the user’s computer
- Automatically blank the remote screen when connected
- Automatically lock remote computer when disconnected
- Lock the remote computer’s keyboard and mouse while in session
- Lock the streamer settings using Splashtop admin credentials
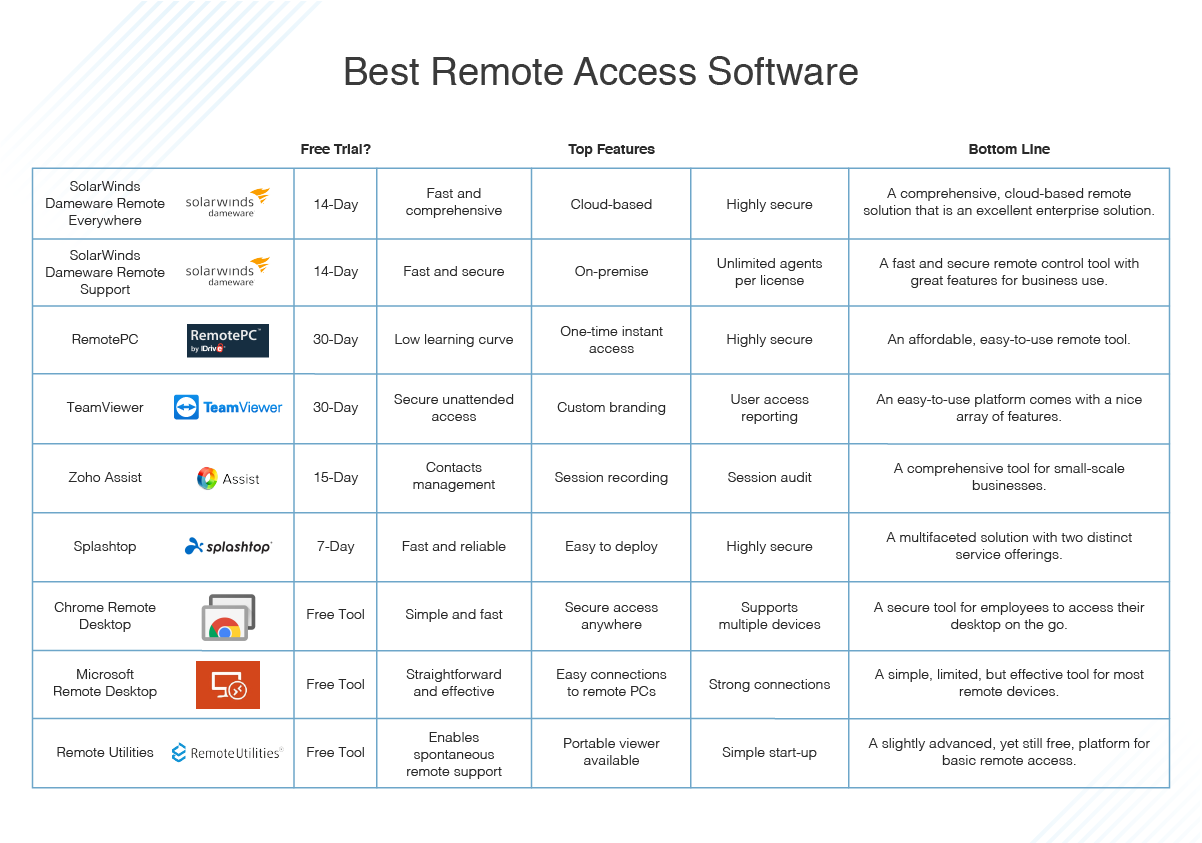
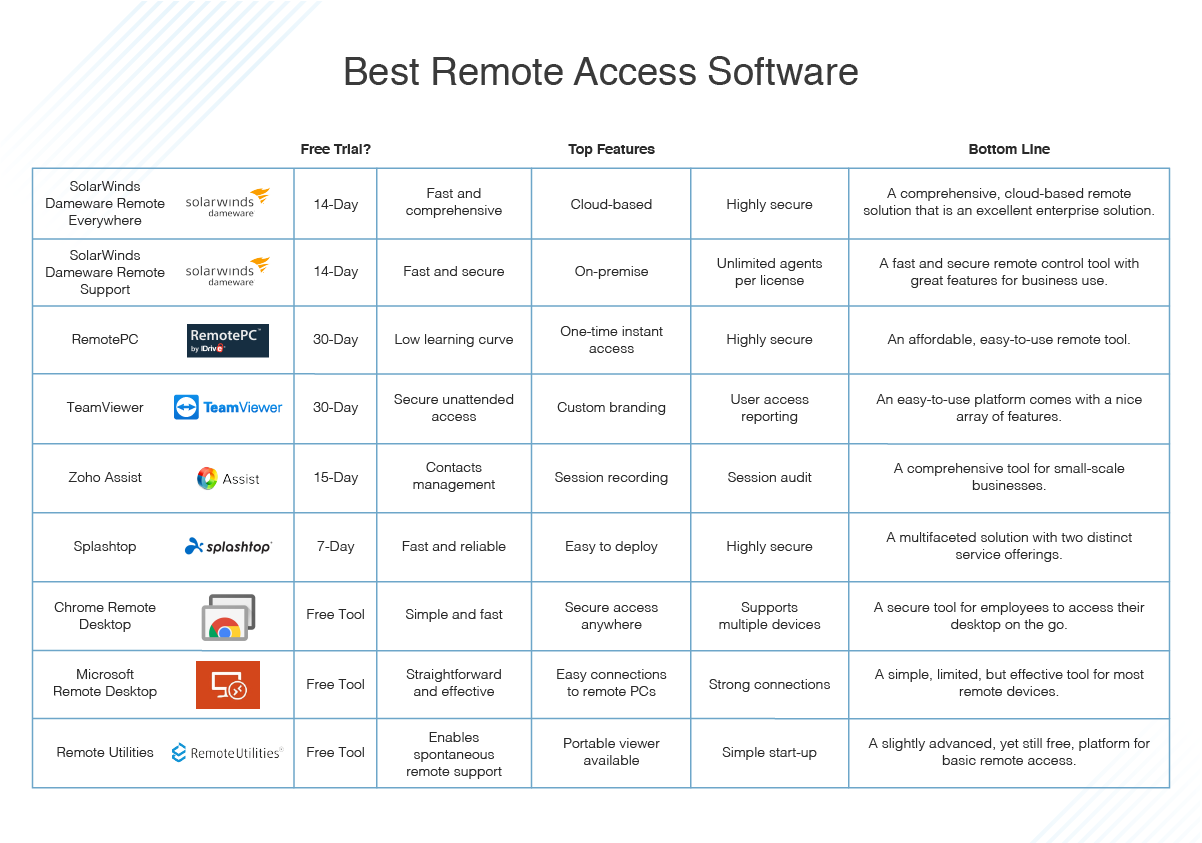
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...
How secure is enabling remote access?
- iOS/Android: Swap album and artist titles in CarPlay/Android Auto.
- iOS/Android: Rare crash if your library had ~200,000 items.
- Desktop: Reduce hover play background size to allow clicking on poster.
- iOS: Crash for high CPU in some cases if server disks were offline.
- CarPlay/Android Auto: Show all albums when album types are enabled.
What is a remote login protocol?
The rlogin user command and the rlogind daemon provide the remote login protocol, allowing users to log in to a remote host and use their terminals as if they were directly connected to the remote host.
How many types of remote access are there?
Types of remote access: virtual private network. SaaS remote desktop tools. common remote service ports.
What are the five popular protocols?
Popular Network ProtocolsOverview. ... Introduction to the Network Protocol. ... Ethernet. ... Internet Protocol (IP) ... Internet Control Message Protocol (ICMP) ... Address Resolution Protocol (ARP) ... Transmission Control Protocol (TCP) ... User Datagram Protocol (UDP)More items...•
What is the protocol for secure network connection remote site?
SSL VPN stands for Secure Sockets Layer Virtual Private Network. It's a safe and secure way for remote users to easily connect to your network. Think about SSL VPN like a secure tunnel that connects you from wherever you are, to your company's internal network safely.
Which technology is used in remote access?
virtual private network (VPN) technologyRemote access software is usually accomplished using a virtual private network (VPN) technology. This type of method is more available compared to others since it is a more secure remote access software that connects the user and the enterprise's networks through an internet connection.
Who is more secure protocol for remote login?
While Remote Desktop is more secure than remote administration tools such as VNC that do not encrypt the entire session, any time Administrator access to a system is granted remotely there are risks. The following tips will help to secure Remote Desktop access to both desktops and servers that you support.
What are the 3 major protocol?
There are three main types of network protocols, including network management protocols, network communication protocols and network security protocols.
What are the four types of protocols?
Common Internet protocols include TCP/IP (Transmission Control Protocol/Internet Protocol), UDP/IP (User Datagram Protocol/Internet Protocol), HTTP (HyperText Transfer Protocol) and FTP (File Transfer Protocol).
What is the most widely used protocol?
TCP IP is the most widely used communications protocol.
Is SSH A protocol?
SSH or Secure Shell is a network communication protocol that enables two computers to communicate (c.f http or hypertext transfer protocol, which is the protocol used to transfer hypertext such as web pages) and share data.
What are two types of remote management?
Remote Access Control MethodsDirect (Physical) Line. The first direct remote access control that can be implemented is a direct line from a computer to the company's LAN. ... Virtual Private Network. Another method which is more common is establishing a VPN. ... Deploying Microsoft RDS.
What is remote accessing?
Remote access is the act of connecting to IT services, applications, or data from a location other than headquarters. This connection allows users to access a network or computer remotely via the internet.
What is remote control access?
Remote Access and Control Software is the ability for an authorized person to access a computer or network from a geographical distance through a network connection.
What is remote server access?
A remote access server (RAS) is a type of server that provides a suite of services to remotely connected users over a network or the Internet. It operates as a remote gateway or central server that connects remote users with an organization's internal local area network (LAN).
What is remote access protocol?
A remote access protocol manages the connection between a remote computer and a remote access server. These are the primary remote access protocols that are in use today:
What is PPP protocol?
Point-to-Point Protocol (PPP) PPP is used to implement TCP/IP over point-to-point connections (for example, serial and parallel connections). It is most commonly used for remote connections to ISPs and LANs. PPP uses the Link Control Protocol (LCP) to communicate between PPP client and host. LCP tests the link between client and PPP host ...
How to use PPTP?
To use PPTP, you set up a PPP session between the client and server, typically over the Internet. Once the session is established, you create a second dial-up session that dials through the existing PPP session, using PPTP. The PPTP session tunnels through the existing PPP connection , creating a secure session.
How does PPTP work?
PPTP is both simple and secure. To use PPTP, you set up a PPP session between the client and server, typically over the Internet.
How to dial into a modem?
Type the name of the system you will be dialing into in the Type a Name for the Computer You Are Dialing field. This field defaults to My Connection. Select the modem installed in your computer that you want to use for this connection from the Select a Device dropdown list.
What is LCP in PPP?
LCP tests the link between client and PPP host and specifies PPP client configuration. PPP can support several network protocols, and because it features error checking and can run over many types of physical media, PPP has almost completely replaced SLIP.
What is DHCP used for?
DHCP is the protocol within the TCP/IP protocol stack that is used to assign TCP/IP addressing information, including host IP address, subnet mask, and DNS configuration. This information can be assigned over a LAN connection or a dial-up connection.
What is a RAS modem?
Both Windows NT and Windows 2000 include technology to allow users to dial up a server and connect to not only that server, but also to that server’s host network. This technology is known as RAS. RAS is used in smaller networks where a dedicated dial-up router is not practical or possible. In a RAS setup, you can basically connect a modem to a Windows NT or Windows 2000 server and, by way of the RAS, configure that modem as dial-out only, dial-up only, or a combination.
How to use PPTP?
To use PPTP, you set up a PPP session between the client and server, typically over the Internet. Once the session is established, you create a second dial-up session that dials through the existing PPP session using PPTP. The PPTP session tunnels through the existing PPP connection, creating a secure session.
What is LCP in PPP?
LCP tests the link between client and PPP host and specifies PPP client configuration. Through LCP, PPP also supports authentication negotiation, as well as negotiation of encryption and compression between client and server, using compression control protocols (CCPs) and encryption control protocols (ECPs).
What is PPTP in a network?
PPTP is the Microsoft-created protocol based on PPP. It is used to create virtual connections across the Internet using TCP/IP and PPP so that two networks can use the Internet as their WAN link and yet retain private network security. PPTP is both simple and secure.
How to display destination address on PPP?
Select the connection to establish the PPP connection or choose not to dial an initial connection. Then click Next to display the Destination Address window.
What is PPP over Ethernet?
There is a version of PPP called PPP over Ethernet (PPPoE) that allows the authentication methods of PPP to be used over Ethernet and high-speed Internet connections so individual users can be authenticated for Internet access over a shared medium like Ethernet or DSL.
What is PPP used for?
PPP is used to implement TCP/IP; it is the protocol that establishes a connection over point-to point links (for example, dial-up and dedicated leased lines). It is most commonly used for remote connections to ISPs and LANs.
What are the two methods of remote access?
First, you need to consider two distinct methods of remote access, each of which uses different protocols: Dial-up. Virtual private networking (VPN) Within each method, there are three basic categories for protocols: Connectivity. Authentication.
How to make sense of all the protocol configuration options involved in setting up remote access servers?
To help make sense of all the protocol configuration options involved in setting up remote access servers, take a look at the categories of protocols and the advantages and disadvantages of the various protocols within each one.
What protocol is used for dial up encryption?
For data encryption in a dial-up session in a Windows network. In order to use MPPE, the authentication protocol for the dial-up session must be either EAP-TLS or MS-CHAP version 1 or 2. VPN protocols.
What is virtual private network?
Virtual private networking protocols encapsulate PPP frames (the data units at the data link layer of the OSI model) into IP datagrams at the network layer. These datagrams are then sent across an internetwork, which can be either a private network or, more commonly, the Internet. This encapsulation creates a “tunnel” that acts like a dedicated WAN link, even though it usually uses the Internet—thus, a “virtual” private network.
Why do you want to be encrypted in a remote session?
First, you want the best security you can provide for the remote session. You want authentication to be encrypted so that someone who is snooping cannot see it , and you want the data that is passed in the remote session to be encrypted for the same reason. Second, older systems and their associated protocols are less capable in terms ...
What is dial up modem?
Dial-up involves one modem connecting with another over the Public Switched Telephone Network (PSTN), creating a temporary, dedicated WAN link. There are three possible protocols for making the initial connection: Point-to-Point Protocol (PPP), Serial Line Internet Protocol (SLIP), and Asynchronous NetBEUI (AsyBEUI). Table A explains their differences.
How does dial up authentication work?
Authenticating the user. Part of the dial-up process involves authentication, usually by providing a password. Since that password can be intercepted and used to gain unauthorized access, it should be encrypted using the strongest possible method that is supported by both the server and the client.
Serial Line Internet Protocol (Slip)`
Point-To-Point Tunneling Protocol
- PPTP is a remote access protocol, based on PPP, created by Microsoft. It’s used to establish virtual connections across the internet via PPP and TCP/IP, enabling two networks to use the internet as their WAN link while retaining the security benefits of a private network. PPTP is a great option because it’s simple and secure. To use PPTP, you’ll have to set up a PPP session be…
Windows Remote Access Services
- Windows 2000 and Windows NT let users dial up a server and connect to both the server and the server’s host network. This is referred to as RAS, which is used in smaller networks where a dedicated dial-up router would not be possible or practical. With a RAS setup, you can connect a modem to a Windows 2000 or Windows NT server and configure the modem as dial-out only, di…
Remote Desktop Protocol
- Finally, there is the RDP, which is very similar to the Independent Computing Architecture (ICA) protocol used by Citrix products. RDP is utilized to access Windows Terminal Services, which is a close relative of the product line provided by Citrix WinFrame. RDP offers the same core functions as ICA, although there are some limitations. RDP provides remote access for Windows clients o…
Serial Line Internet Protocol
Point-To-Point Protocol
Point-To-Point Tunneling Protocol
Windows Remote Access Services
Independent Computing Architecture (ICA) Protocol
- A relatively new technology for remote access is the Citrix WinFrame (or MetaFrame) products (including Windows Terminal Server), which use the ICA protocol. Put simply, Citrix WinFrame allows multiple computers to take control of a virtual computer and use it as if it were their desktop. The advantage is that a company can put all of its time and ...