Full Answer
What is remote access trojan (RAT)?
What is Remote Access Trojan (RAT)? A remote access Trojan (RAT) is a malware program that opens a backdoor, enabling administrative control over the victim’s computer. RATs are typically downloaded together with a seemingly legitimate program, like a game, or are sent to the target as an email attachment.
How do I protect against a remote access trojan?
While there are several measures that can be helpful depending on the size of the environment you’re looking to protect—including security awareness training and antivirus software— intrusion detection systems are your best bet for preventing a Remote Access Trojan from slipping past your security setup.
How to remove Trojan virus from Mac?
How to Remove Trojan Virus from Mac 1 Once you’ve downloaded the app, install it and then launch it from your Applications folder. 2 Click on the Malware Removal tab. 3 Click Scan and CleanMyMac X will start examining your Mac for malware, including worms, spyware, viruses, etc. 4 When the scan is done click Remove. See More....
What is a Mac Trojan and how does it work?
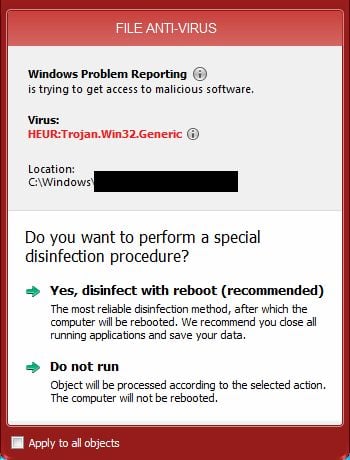
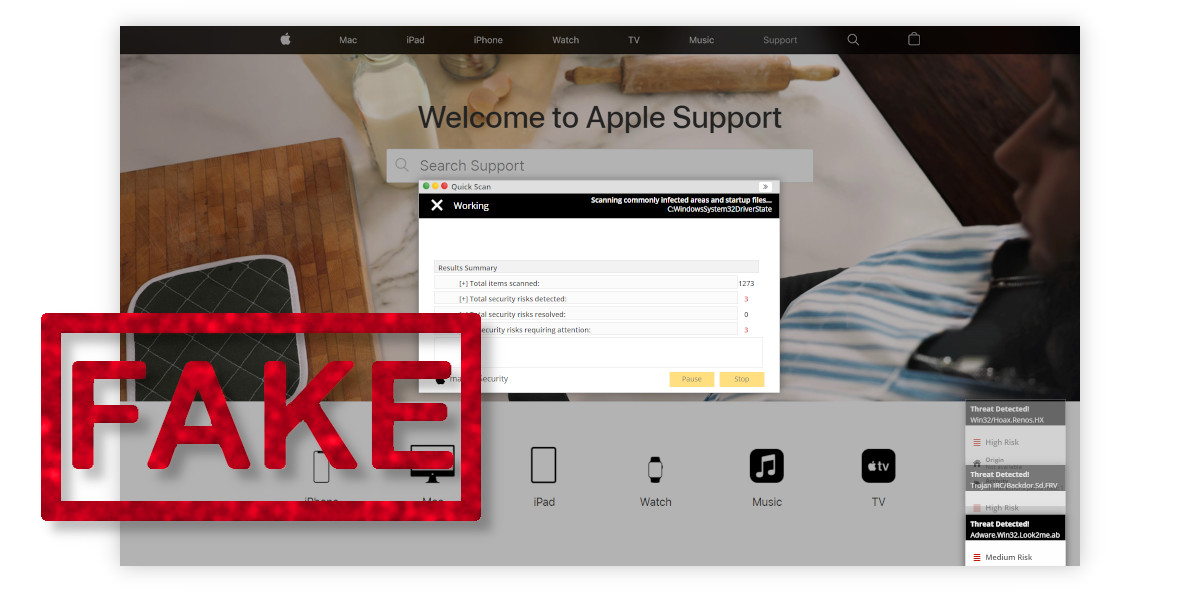
One of the most pernicious types of trojan is linked to adware that displays a pop-up claiming your Mac has been infected and then takes you to a download for what is claimed to be an anti-virus tool, but which in itself is a virus.
Can a Trojan give remote access?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Can Mac be infected with Trojan virus?
Are Trojans viruses a threat to Macs? Although Macs are still fairly secure machines, the days of them being considered immune to malware are well behind us. As Macs grow more popular, they become an increasingly popular target for hackers, who'll use all kinds of attacks, including Trojans.
Can Macs get RAT?
RATs don't self-replicate, nor exploit vulnerabilities in networks like worms do. They get onto your Mac when you open a RAT malware email attachment, click on a link, visit a website, or download software.
How are remote access Trojans delivered?
A remote access Trojan (RAT) is a malware program that includes a back door for administrative control over the target computer. RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment.
How do you tell if your Mac is infected?
Seeing programs you did not download: If you see new icons on your desktop for applications that you did not download, you have a potential unwanted program (PUP) infection on your hands. You may also see a pop-up telling you “Your Mac is infected.
How do I know if my Mac has got a virus?
How to know if your Mac has a virus?You're seeing recurrent popups and scan reports that appear at random. ... Your browser is being redirected to unwanted sites. ... You're seeing redundant ads while surfing the web. ... Your personal files have been encrypted and cannot be accessed. ... Your Mac is slower than usual.
Can BitDefender detect rats?
BitDefender Antivirus for Mac automatically detects Proton RAT, and other pieces of malware it may have subsequently dumped on your system. Infected users are also advised to change all the passwords sitting in their OS X KeyChain, “or any browser password stores,” according to the HandBrake team.
Can BitDefender find rats?
Security researchers at Bitdefender have discovered a new Golang-written RAT that targets devices by using the CVE-2019-2725 (Oracle WebLogic RCE) vulnerability identified last year.
How do I know if someone is accessing my computer remotely?
You can try any of these for confirmation.Way 1: Disconnect Your Computer From the Internet.Way 2. ... Way 3: Check Your Browser History on The Computer.Way 4: Check Recently Modified Files.Way 5: Check Your computer's Login Events.Way 6: Use the Task Manager to Detect Remote Access.Way 7: Check Your Firewall Settings.More items...•
How would users recognize if ones computer is infected?
Signs of an infection include your computer acting strangely, glitching and running abnormally slow. Installing and routinely updating antivirus software can prevent virus and malware infections, as can following cautious best practices.
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
How do I know if I have Trojan virus?
Here are the most common signs of a Trojan malware attack:Your computer feels slow. ... Crashes and freezes. ... Unfamiliar apps on your device. ... Internet redirects. ... Changes to your desktop, taskbar, or browser. ... More pop-ups. ... Your antivirus software is deactivated.
Does Apple detect viruses on Mac?
macOS includes built-in antivirus technology called XProtect for the signature-based detection and removal of malware. The system uses YARA signatures, a tool used to conduct signature-based detection of malware, which Apple updates regularly.
What is a trojan virus?
A trojan virus, or to give it it’s full name, a Trojan Horse, is so-called because it’s a cyber equivalent of the Wooden Horse of Troy. In that case, the wooden horse was used to trick the defenders of Troy into allowing enemy soldiers behind the city walls. In the case of a trojan virus on your Mac, it tricks users into downloading the virus by hiding it in something that looks legitimate.
How to fix a Mac that behaves strangely?
If you’ve spotted that your Mac behaves strangely, you need to perform a thorough malware scan. The best way to do it is to use a dedicated tool like CleanMyMac X. It's much better than ordinary trojan removers, as it can detect and neutralize thousands of threats, including adware, spyware, ransomware, worms, and more. You can download it for free here.
Why does my Mac run so slowly?
Your Mac starts running very slowly as if something is hogging the processor.
Does malware get removed from Mac?
Every trace of the malware will be removed from your Mac.
Does CleanMyMac X protect against malware?
If you want to protect your Mac from trojan viruses and malware in real-time, CleanMyMac X can also prove useful. With its newest Malware Monitor feature, you can stay updated on anything that wants to creep into your Mac. Here’s how to enable real-time protection in CleanMyMac X:
What is remote access trojan?
Like most other forms of malware, Remote Access Trojans are often attached to files appearing to be legitimate, like emails or software bundles. However, what makes Remote Access Trojans particularly insidious is they can often mimic above-board remote access programs.
What happens if you install remote access Trojans?
If hackers manage to install Remote Access Trojans in important infrastructural areas—such as power stations, traffic control systems, or telephone networks—they can wreak havoc across neighborhoods, cities, and even entire nations.
How does Snort intrusion detection work?
The intrusion detection mode operates by applying threat intelligence policies to the data it collects, and Snort has predefined rules available on their website, where you can also download policies generated by the Snort user community. You can also create your own policies or tweak the ones Snort provides. These include both anomaly- and signature-based policies, making the application’s scope fairly broad and inclusive. Snort’s base policies can flag several potential security threats, including OS fingerprinting, SMB probes, and stealth port scanning.
What is the best way to detect malware?
The best option, especially for larger organizations, is to employ an intrusion detection system, which can be host-based or network-based. Host-based intrusion detection systems (HIDSs), which are installed on a specific device, monitor log files and application data for signs of malicious activity; network-based intrusion detection systems (NIDSs), on the other hand, track network traffic in real time, on the lookout for suspicious behavior. When used together, HIDSs and NIDSs create a security information and event management (SIEM) system. SIEM is an incredibly beneficial part of a strong security regimen and can help to block software intrusions which have slipped past firewalls, antivirus software, and other security countermeasures.
How do remote access Trojans evade live data analysis?
One way in which Remote Access Trojans can evade the live data analysis NIDSs provide is by dividing the command messaging sent through the malware across multiple data packets. NIDSs like Zeek, which focus more on application layers, are better able to detect split command messaging by running analyses across multiple data packets. This is one advantage Zeek has over Snort.
What is APT in computer security?
The practice of stealthy, ongoing hacking seeking to accumulate data over time, as opposed to causing damage to information or systems, is known as an advanced persistent threat (APT ). Remote Access Trojans are a powerful tool in this type of attack, because they do not slow down a computer’s performance or automatically begin deleting files once installed—and because they’re so adaptable.
Is remote access Trojans good?
That said, antivirus software will not do much good if users are actively downloading and running things they shouldn’t.
What is intrusion detection?
Intrusion detection systems are important tools for blocking software intrusion that can evade detection by antivirus software and firewall utilities. The SolarWinds Security Event Manager is a Host-based Intrusion Detection System. However, there is a section of the tool that works as a Network-based Intrusion Detection System. This is the Snort Log Analyzer. You can read more about Snort below, however, you should know here that it is a widely used packet sniffer. By employing Snort as a data collector to feed into the Snort Log Analyzer, you get both real-time and historic data analysis out of the Security Event Manager.
Can antivirus be used to get rid of a RAT?
Antivirus systems don’t do very well against RATs. Often the infection of a computer or network goes undetected for years. The obfuscation methods used by parallel programs to cloak the RAT procedures make them very difficult to spot. Persistence modules that use rootkit techniques mean that RATs are very difficult to get rid of. Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system.
Can a Remote Access Trojan be installed to BIOS?
Access to the BIOS has been known to the world’s hackers since 2015. Many believe that the NSA was planting RATs and trackers on BIOS even earlier.
How to protect yourself from remote access trojans?
Just like protecting yourself from other network malware threats, for remote access trojan protection, in general, you need to avoid downloading unknown items; keep antimalware and firewall up to date, change your usernames and passwords regularly; (for administrative perspective) block unused ports, turn off unused services, and monitor outgoing traffic.
What is a RAT trojan?
RAT trojan is typically installed on a computer without its owner’s knowledge and often as a trojan horse or payload. For example, it is usually downloaded invisibly with an email attachment, torrent files, weblinks, or a user-desired program like a game. While targeted attacks by a motivated attacker may deceive desired targets into installing RAT ...
How does RAT malware work?
Once get into the victim’s machine, RAT malware will hide its harmful operations from either the victim or the antivirus or firewall and use the infected host to spread itself to other vulnerable computers to build a botnet.
Why do RATs use a randomized filename?
It is kind of difficult. RATs are covert by nature and may make use of a randomized filename or file path structure to try to prevent identification of itself. Commonly, a RAT worm virus does not show up in the lists of running programs or tasks and its actions are similar to those of legal programs.
Is Sub 7 a trojan horse?
Typically, Sub 7 allows undetected and unauthorized access. So, it is usually regarded as a trojan horse by the security industry. Sub7 worked on the Windows 9x and Windows NT family of OSes, up to and including Windows 8.1. Sub7 has not been maintained since 2014. 4.
Can a RAT remote access trojan be used on a computer?
Since RAT remote access trojan will probably utilize the legitimate apps on your computer, you’d better upgrade those apps to their latest versions. Those programs include your browsers, chat apps, games, email servers, video/audio/photo/screenshot tools, work applications…
