Top Methods for Secure Remote Access
- Virtual Private Network. To access your business network, your employees are using Wi-Fi. To do so securely, provide...
- Shared Platforms. Another method for providing employees with secure remote access to business information is through...
- Privileged Access Management. To securely manage credentials for privileged accounts on a...
- VPNs. ...
- Desktop Sharing. ...
- The Verdict: VPNs and Desktop Sharing Are Not Secure Enough for Remote Vendor Access. ...
- The Best Alternative: Vendor Privileged Access Management. ...
- The Bottom Line.
Is your remote access solution secure?
While a Virtual Private Network or VPN is one of the most sought-after remote access solutions at the moment, it can still pose a few security risks for your organization. A VPN Access can still be exposed to a bunch of security threats outside of a company’s network.
What are the best practices for securing remote access?
Best Practices for Securing Remote Access. RAS: The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network ... IPSec: IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect ...
What are the different types of remote access services?
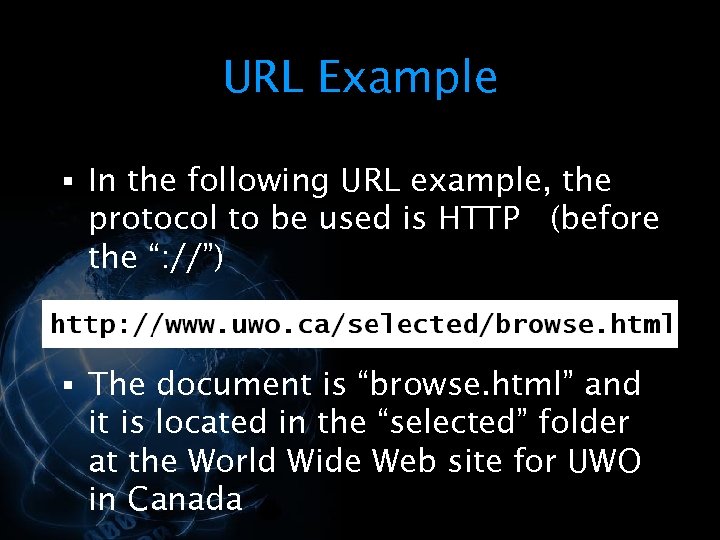
Some of the most prominent include the following: Virtual private network (VPN) – The most common and well-known form of secure remote access, VPNs typically use the public Internet to connect to a private network resource through an encrypted tunnel.
How to protect your network from remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly. Adopting two-factor authentication for remote access through VPN further boosts your network security.

How do I make remote access reliable and safe?
7 Best Practices For Securing Remote Access for EmployeesDevelop a Cybersecurity Policy For Remote Workers. ... Choose a Remote Access Software. ... Use Encryption. ... Implement a Password Management Software. ... Apply Two-factor Authentication. ... Employ the Principle of Least Privilege. ... Create Employee Cybersecurity Training.
What is more secure than RDP?
Security. Although both VPN and RDP are encrypted through internet connection, a VPN connection is less accessible to threats than a remote desktop connection. For this reason, VPN is often considered more secure than RDP.
Who is more secure protocol for remote login?
Virtual private networks (VPNs) are a commonly used remote-access solution. They are designed to provide an encrypted tunnel for network traffic between a remote user and the enterprise network. VPNs also support security solutions like MFA that help to mitigate the threat of compromised accounts.
Is RDP more secure than VPN?
RDP vs VPN Security Even though the same device is being used, an RDP changes its IP address to provide additional security. VPNs lack access controls and session monitoring, which are both effective means of security when it comes to network access.
Is SSH or RDP more secure?
Though they are quite similar, there are fundamental differences between them. SSH is considered more secure because it does not require additional tools such as a Virtual Private Network (VPN) or Multi-factor authentication (MFA) as RDP does.
Is VNC more secure than RDP?
While Remote Desktop is more secure than remote administration tools such as VNC that do not encrypt the entire session, any time Administrator access to a system is granted remotely there are risks. The following tips will help to secure Remote Desktop access to both desktops and servers that you support.
Why RDP is not secure?
The risks of such exposure are far too high. RDP is meant to be used only across a local area network (LAN). Since RDP hosts support a listening port awaiting inbound connections, even the most secure installations can be profiled as a Windows Operating System and its version.
Is Microsoft RDP encrypted?
Microsoft RDP includes the following features and capabilities: Encryption. RDP uses RSA Security's RC4 cipher, a stream cipher designed to efficiently encrypt small amounts of data. RC4 is designed for secure communications over networks.
Is FTP secure?
FTP was not built to be secure. It is generally considered to be an insecure protocol because it relies on clear-text usernames and passwords for authentication and does not use encryption. Data sent via FTP is vulnerable to sniffing, spoofing, and brute force attacks, among other basic attack methods.
Why would you use RDS instead of VPN?
The data is decrypted only at the intended destination. RDS – In RDS, the data is stored on the remote server and not on the end-point device. Hence, any threat to the end-point device does not cause data loss.
Can RDP be detected?
Detection. Detecting the use of RDP is something that is captured in several logs within a Microsoft Windows environment. Unfortunately, most organizations do not have a log management or SIEM solution to collect the logs that could alert to misuse, furthering the challenge to organizations to secure RDP.
How do I encrypt an RDP connection?
This post will walk through the steps required to force TLS encryption on all RDP connections.Step 1: Open the Root Console. ... Step 2: Open the Group Policy Editor Snap-in. ... Step 3: Navigate to the RDP Session Security Policies. ... Step 4: Require the Highest native Encryption possible.More items...
Is there an alternative to RDP?
With additional features built to go beyond those in RDP, DRS makes for a comprehensive and easy-to-use remote desktop connection manager alternative. Like RDP, DRS offers multi-platform remote access, with support for Mac, Windows, and Linux computers.
Why RDP is not secure?
The risks of such exposure are far too high. RDP is meant to be used only across a local area network (LAN). Since RDP hosts support a listening port awaiting inbound connections, even the most secure installations can be profiled as a Windows Operating System and its version.
Is RDP over Internet secure?
RDP's standard security employs RSA's RC4 encryption algorithm to protect data transmission. Random values are shared between client and server when a connection is initialized while the machines are in the Basic Settings Exchange phase. Remote Desktop encryption protects transmitted data from unauthorized use.
What is the difference between RDP and VPS?
In brief, RDP provides remote display and input capabilities over network connections for Windows-based applications running on a server, while VPS is a virtual machine that you can use to host your data and since VPS runs its own OS, you can get a Windows or Linux VPS server.
What are some good remote access platforms?
Some platforms that work well include Box.com, Dropbox, Microsoft OneDrive, and SharePoint, another Microsoft product .
What is PAM software?
To securely manage credentials for privileged accounts on a network, you can use privileged access management (PAM) software. This is ideal for privileged access or administrative accounts on any network. PAM tools can be used to secure, control, and monitor access to an organization’s resources.
Do vendors need VPN access?
While VPNs, shared platforms, and PAMs offer secure remote access for your employees, your vendors, contractors, and partners (external users) may also require access to your network. That’s where vendor privileged access management (VPAM) comes in.
What is the line of defense for remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly.
What is remote access VPN?
The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network (VPDN) due to its early adoption on dial-up internet.
Why is IPSec VPN important?
IPSec VPN connections are also important for an employee who needs widespread access to the company’s network. A word of warning: If you are using IPSec VPN for remote access, but you are not deploying Internet Key Exchange (IKE, certificates) as an authentication method, the connection will be vulnerable.
Why is IPSEC used?
This allows IPSec to protect data transmission in a variety of ways. IPSec is used to connect a remote user to an entire network. This gives the user access to all IP based applications. The VPN gateway is located at the perimeter of the network, and the firewall too is setup right at the gateway.
What is IPSEC protocol?
IPSec: IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect data flows between hosts and security gateways. The unique feature of IPSec is that it operates at the Network Layer of the Open Systems Interconnection (OSI) protocol model.
Should a company use IPSEC VPN?
A company should go for IPSec VPN remote access if it has a strong networking department with the ability to configure each employee’s hardware device individually (installing client software, enforcing security policies etc.).
What is secure remote access?
Secure remote access refers to any security policy, solution, strategy or process that exists to prevent unauthorized access to your network, its resources, or any confidential or sensitive data. Essentially, secure remote access is a mix of security strategies and not necessarily one specific technology like a VPN.
What technologies are used for secure remote access?
Secure remote access is comprised of a multitude of security solutions and technologies. Some of the most prominent include the following:
Secure remote access solution
Enables employees with precise access to the applications and data required to do their job from anywhere.
Why is secure remote access important?
With the work from home shift in the workforce, endpoints are accessing corporate networks from multiple locations. Today, employees’ home networks are often the originating point for network connections, multiplying the risk on both home and corporate networks.
What are the benefits of secure remote access?
While the benefits of secure remote access are numerous, there are four key advantages in which to focus on:
Can secure remote access be achieved without VPN?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
How can AT&T help organizations with secure remote access?
AT&T Cybersecurity is uniquely positioned to help organizations address these immediate challenges with an eye toward the future by helping them balance connectivity, collaboration, and cybersecurity affordably.
How does ZTNA improve security?
ZTNA improves your security posture by drastically reducing your attack surface. Application access is decoupled from network access. ZTNA moves away from network-centric security and instead focuses on securing the connection between user and application.
Why are IPs never exposed to the internet?
IPs are never exposed to the internet, creating a “darknet” and making the network impossible to find. Apps segmentation ensures that once users are authorized, application access is granted on a one-to-one basis so that authorized users have access only to specific applications rather than full access to the network.
What is ZTNA security?
ZTNA takes a user-to-application approach rather than a network-centric approach to security . The network becomes deemphasized, and the internet becomes the new corporate network, leveraging end-to-end encrypted TLS micro-tunnels instead of MPLS.
Can IoT services be hosted on premises?
IoT services that are hosted on-premises can benefit from optimized speeds. Performance speeds can increase if local users do not have to connect out to the internet to access apps that are hosted on-premises. The other option is ZTNA as a service, such as Zscaler Private Access.
Can a VPN be found by adversaries?
Opening the network in this way enables it to be “found” by your remote users, but it also means it can be found by adversaries. They can (and do) exploit the VPN attack surface to infiltrate the network, deliver malware such as ransomware, launch denial-of-service attacks, and exfiltrate critical business data.
What is secure remote access?
What it means to provide secure remote access has changed considerably in the past few years as a result of new technologies and the pandemic. At its most basic, secure remote access is having location-agnostic connectivity among enterprise users and centralized applications, resources and systems, whether cloud-based or on premises.
Who is responsible for secure remote access?
Although remote access tools, such as VPNs and firewalls, are typically under the purview of network teams, in this new era, cybersecurity teams tend to lead and manage the policies, processes and technologies associated with ensuring secure remote access.
The diminishing power of VPNs
One tactic organizations use to combat the vulnerabilities associated with working remotely -- especially if employees are using consumer-grade systems -- is to reestablish VPN standards. This entails enforcing basic protections, such as strong passwords, multifactor authentication, role-based access and encryption.
Setting secure remote access policies
A hallmark of secure remote access is the underlying policy that safeguards access to and the use of enterprise resources, such as data, databases, systems and networks.
Components of the secure remote access ecosystem
Secure remote access touches just about every aspect of enterprise security. TechTarget has curated a series of guides to help IT and security professionals get up to speed on important technologies and concepts.
Zero trust and secure remote access
Cybersecurity and IT teams realize words like perimeter and trust are quickly becoming outdated as borders dissolve and the base of users that need access to resources expands. No longer are organizations protected by four castle walls, with a firewall moat keeping miscreants out.
SASE and secure remote access
Secure Access Service Edge is an emerging concept that combines network and security functions into a single cloud service, not only to alleviate traffic from being routed through the data center, but also to embrace a remote workforce, IoT adoption and cloud-based application use.
What is the best remote desktop software?
RemotePC is the best remote desktop software right now. RemotePC is another stellar product from the team at iDrive (we also recommend its excellent cloud storage solution). RemotePC uses top-notch cloud tech to deliver class-leading remote access. Web, desktop, and mobile apps provide the access.
How long does it take to set up a remote access?
Using remote access software is simple. They generally take no more than a few minutes to set up, and you will usually have to install the software on the computer or other device you want to access the remote computer with.
What is remote desktop manager?
Remote Desktop Manager is a powerful remote computer access program offering scalable solutions for large businesses. It’s compatible with both Android and iOS devices and comes with a selection of impressive security features.
What is Zoho Assist?
Cloud-based Zoho Assist is one of our favorite remote access tools because it enables you to access almost any device. It provides specialized remote support and unattended access plans designed to streamline workflow processes.
How much does Connectwise Control cost?
ConnectWise Control provides highly specialized remote access solutions targeted at specific users. Its three Support plans start at $19 per month, come with some remote access features, and include powerful tools to help IT staff and support technicians solve problems remotely. The Access plan starts at $30 per month for 25 devices and is aimed at those who want to connect with numerous remote devices.
How much does Parallels Access cost?
It does support computer–computer connections, but the majority of its features are mobile-centered. Prices start from just $19.99 per year, making it one of the more affordable options on this list.
Is Chrome Remote Desktop free?
Chrome Remote Desktop is a free remote access program that’s available on Windows, Mac, Linux, iOS, and Android devices . It's extremely limited when compared to some of the paid options on this list, but it’s the best free software we’ve come across and is a great option for personal use.
What is remote access technology?
A common remote access technology in use today is the IPsec VPN. A piece of software called a VPN client is installed on the end user’s computer and is configured with details about the target network, such as the gateway IP address and a pre-shared security key. Each time the user wants to connect to the corporate network, they start the VPN client, which creates a secure connection to the corporate firewall.
How does SSL VPN work?
When setting up an SSL VPN, the network administrator publishes the VPN client to the firewall, providing it for download via the firewall's public connection. To access the corporate network, end users visit a public web page, from which they can install the SSL VPN client and download the configuration details.
What is SSL VPN?
SSL, which stands for Secure Sockets Layer, is a common encryption technology that is widely used to provide secure communication on the Internet. When setting up an SSL VPN, the network administrator publishes the VPN client to the firewall, providing it for download via the firewall's public connection. To access the corporate network, end users visit a public web page, from which they can install the SSL VPN client and download the configuration details.
Is SSL VPN better than IPsec?
Many organizations will find that SSL VPN provides advantages over IPsec VPN. Firewall manufacturers could speed up the adoption of SSL VPN by bundling more licenses with the firewall instead of selling them as add-ons.
Is SSL VPN more expensive than IPsec?
SSL VPN requires more processing overhead for the firewall compared to IPsec VPN. Some firewalls may not be able to handle as many SSL VPN client connections as IPsec VPN connections. Licensing is more expensive. While firewall manufacturers typically include many IPsec VPN licenses, SSL VPN licenses are usually sold as an add-on to the hardware.
Is VPN required for telecommuting?
Being able to connect securely to your corporate network from a remote location using a Virtual Private Network (VPN) is important, and it may be required by your job if you are a telecommuter. There are some remote access technologies that are widely used, but some new methods have recently emerged that have the ability to change how we work.
Is DirectAccess a LAN?
DirectAccess is not going to gain widespread adoption until the OS licensing requirements are revised and the networking is reworked to be more straightforward. While IPv6 is the future of networking, we currently live and work in an IPv4 world, especially on the LAN (as of May 2014, IPv4 still carried more than 96% of Internet traffic worldwide, according to Google ). Setting up a new remote access technology should not require one or more potentially expensive projects before it can be deployed.
Author: Haris Khan
Remote work is the new normal for IT teams around the globe, and there is no surprise as to why remote work is becoming so increasingly popular for organizations. The modern employee workforce is no longer restricted to one physical location.
What is secure remote access?
Secure remote access refers to the technology used for securely accessing a system or application remotely. Cybercriminals and malicious actors are consistently looking out for vulnerabilities and loopholes in remote work infrastructures to exploit and plan cyber attacks.
Which technologies are used for remote work access?
Secure remote access can be effectively implemented by utilizing a collection of highly innovative, secure, and flexible technologies while accessing a system or application from a remote location A few prominent examples of such technologies are listed below:
10 Best Practices for Secure Remote Work Access
Some of the best practices that you can adopt to improvise remote access security in your organization are described below:
Why cloud desktops are an optimal choice for secure remote access?
Cloud desktop solutions offer greater flexibility and ease of access as all of your files, applications and desktop reside on the cloud. Cloud desktops are one of the most resilient and secure forms of remote access.
All-In-One Secure Remote Access with V2 Cloud
As the organizational trend keeps transitioning to remote work, it’s crucial to comprehend the numerous cybersecurity risks and threats that are associated with remote access security. Remote work has become an increasingly viable option with tons of advantages.
