What are the security requirements for remote access?
7 Best Practices For Securing Remote Access for EmployeesDevelop a Cybersecurity Policy For Remote Workers. ... Choose a Remote Access Software. ... Use Encryption. ... Implement a Password Management Software. ... Apply Two-factor Authentication. ... Employ the Principle of Least Privilege. ... Create Employee Cybersecurity Training.
What is considered remote access?
Remote access is the ability for an authorized person to access a computer or network from a geographical distance through a network connection. Remote access enables users to connect to the systems they need when they are physically far away.
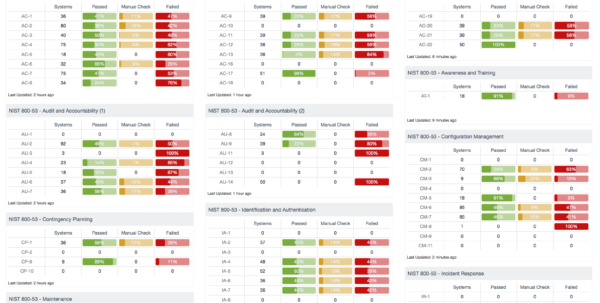
What are the NIST 800-53 technical controls?
What are the NIST 800-53 control families?Access Control. ... Awareness and Training. ... Audit and Accountability. ... Assessment, Authorization and Monitoring. ... Configuration Management. ... Contingency Planning. ... Identification and Authentication. ... Incident Response.More items...
What does NIST 800-53 assess?
Assessing Security and Privacy Controls in Information Systems and Organizations. Planning Note (3/30/2022): As stakeholders use NIST SP 800-53A and its derivative data formats, updates are identified to improve the quality of the publication.
How many types of remote access are there?
The primary remote access protocols in use today are the Serial Line Internet Protocol (SLIP), Point-to-Point Protocol (PPP), Point-to-Point Protocol over Ethernet (PPPoE), Point-to-Point Tunneling Protocol (PPTP), Remote Access Services (RAS), and Remote Desktop Protocol (RDP).
What are the two types of remote access server?
Remote Access Methods1- Remote Access Server: It's one server in organization network that it is the destination of all remote access connections.2- Remote Access Client: All computers that remote connect to network, called remote access client or remote computer.More items...•
What are the 4 technical controls?
Firewalls, intrusion detection systems (IDS), encryption, and identification and authentication mechanisms are examples of technical controls.
What is NIST 800-53 And how can it be used?
The NIST 800-53 is a cybersecurity standard and compliance framework developed by the National Institute of Standards in Technology. It's a continuously updated framework that tries to flexibly define standards, controls, and assessments based on risk, cost-effectiveness, and capabilities.
What are the NIST 800 standards?
The NIST 800 Series is a set of documents that describe United States federal government computer security policies, procedures and guidelines. NIST (National Institute of Standards and Technology) is a unit of the Commerce Department.
What is the difference between NIST 800-53 and 800?
The key distinction between NIST 800-171 vs 800-53 is that 800-171 refers to non-federal networks and NIST 800-53 applies directly to any federal organization.
What are the three types of security controls?
There are three main types of IT security controls including technical, administrative, and physical. The primary goal for implementing a security control can be preventative, detective, corrective, compensatory, or act as a deterrent.
What are NIST security controls?
NIST controls are generally used to enhance the cybersecurity framework, risk posture, information protection, and security standards of organizations. While NIST 800-53 is mandatory for federal agencies, commercial entities have a choice in leveraging the risk management framework in their security program.
What does it mean when you call someone and it says please enter your remote access code?
What is a remote access code? It is a code or a password that a user enters to gain access to a private network or server. It is a form of authentication that either permits or blocks an access attempt from entering a corporate system.
How can I tell if someone has remote access to my computer?
How to Know If Someone is Accessing My Computer Remotely?Way 1: Disconnect Your Computer From the Internet.Way 2. ... Way 3: Check Your Browser History on The Computer.Way 4: Check Recently Modified Files.Way 5: Check Your computer's Login Events.Way 6: Use the Task Manager to Detect Remote Access.More items...•
Can someone remotely access my computer when it's off?
Without appropriate security software installed, such as anti-malware tools like Auslogics Anti-Malware, it is possible for hackers to access the computer remotely even if it is turned off.
Can someone remotely access my computer without my knowledge?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
What is remote access?
Remote access is access to organizational systems (or processes acting on behalf of users) that communicate through external networks such as the Internet. Types of remote access include dial-up, broadband, and wireless. Organizations use encrypted virtual private networks (VPNs) to enhance confidentiality and integrity for remote connections. The use of encrypted VPNs provides sufficient assurance to the organization that it can effectively treat such connections as internal networks if the cryptographic mechanisms used are implemented in accordance with applicable laws, executive orders, directives, regulations, policies, standards, and guidelines. Still, VPN connections traverse external networks, and the encrypted VPN does not enhance the availability of remote connections. VPNs with encrypted tunnels can also affect the ability to adequately monitor network communications traffic for malicious code. Remote access controls apply to systems other than public web servers or systems designed for public access. Authorization of each remote access type addresses authorization prior to allowing remote access without specifying the specific formats for such authorization. While organizations may use information exchange and system connection security agreements to manage remote access connections to other systems, such agreements are addressed as part of CA-3. Enforcing access restrictions for remote access is addressed via AC-3.
Does VPN allow remote access?
Still, VPN connections traverse external networks, and the encrypted VPN does not enhance the availability of remote connections. VPNs with encrypted tunnels can also affect the ability to adequately monitor network communications traffic for malicious code. Remote access controls apply to systems other than public web servers or systems designed ...
Archived Resource
With the release of NIST Special Publication 800-53, Revision 5, this resource has been archived. The latest version of this resource is the NIST Privacy Framework and Cybersecurity Framework to NIST Special Publication 800-53, Revision 5 Crosswalk.
Details
Resource Identifier: NIST SP 800-53 Guidance/Tool Name: NIST Special Publication 800-53, Revision 5, Initial Public Draft, Security and Privacy Controls for Information Systems and Organizations Associated Core Classification: Complete Core - see mapping document below Contributor: National Institute of Standards and Technology (NIST) Contributor GitHub Username: @kboeckl Date First Posted: January 16, 2020 Date Last Verified or Updated: n/a Related Documentation: Mapping Document (XLSX) (link is external) Contributor Notes: n/a.
Where to send comments on a NIST publication?
Comments about specific definitions should be sent to the authors of the linked Source publication. For NIST publications, an email is usually found within the document.
What is remote access?
Definition (s): Access to an organizational information system by a user (or an information system) communicating through an external, non-organization-controlled network (e.g., the Internet). Source (s):
What is an access system?
Access by users (or information systems) communicating external to an information system security perimeter. Access to an organizational system by a user (or a process acting on behalf of a user) communicating through an external network.
What is access to an organizational system?
Access to an organizational system by a user (or a process acting on behalf of a user) communicating through an external network (e.g., the Internet).
When does the information system terminate shared/group account credentials?
The information system terminates shared/group account credentials when members leave the group.
What are the types of information systems?
Supplemental Guidance: Information system account types include, for example, individual, shared, group, system, guest/anonymous, emergency, developer/manufacturer/vendor, temporar y, and service. Some of the account management requirements listed above can be implemented by organizational information systems. The identification of authorized users of the information system and the specification of access privileges reflects the requirements in other security controls in the security plan. Users requiring administrative privileges on information system accounts receive additional scrutiny by appropriate organizational personnel (e.g., system owner, mission/business owner, or chief information security officer) responsible for approving such accounts and privileged access. Organizations may choose to define access privileges or other attributes by account, by type of account, or a combination of both. Other attributes required for authorizing access include, for example, restrictions on time-of-day, day-of-week, and point-of-origin. In defining other account attributes, organizations consider system-related requirements (e.g., scheduled maintenance, system upgrades) and mission/business requirements, (e.g., time zone differences, customer requirements, remote access to support travel requirements). Failure to consider these factors could affect information system availability. Temporary and emergency accounts are accounts intended for short-term use. Organizations establish temporary accounts as a part of normal account activation procedures when there is a need for short-term accounts without the demand for immediacy in account activation. Organizations establish emergency accounts in response to crisis situations and with the need for rapid account activation. Therefore, emergency account activation may bypass normal account authorization processes. Emergency and temporary accounts are not to be confused with infrequently used accounts (e.g., local logon accounts used for special tasks defined by organizations or when network resources are unavailable). Such accounts remain available and are not subject to automatic disabling or removal dates. Conditions for disabling or deactivating accounts include, for example: (i) when shared/group, emergency, or temporary accounts are no longer required; or (ii) when individuals are transferred or terminated. Some types of information system accounts may require specialized training.
What is remote access?
Remote access is access to organizational information systems by users (or processes acting on behalf of users) communicating through external networks ( e.g., the Internet). Remote access methods include, for example, dial-up, broadband, and wireless. Organizations often employ encrypted virtual private networks (VPNs) to enhance confidentiality and integrity over remote connections. The use of encrypted VPNs does not make the access non-remote; however, the use of VPNs, when adequately provisioned with appropriate security controls (e.g., employing appropriate encryption techniques for confidentiality and integrity protection) may provide sufficient assurance to the organization that it can effectively treat such connections as internal networks. Still, VPN connections traverse external networks, and the encrypted VPN does not enhance the availability of remote connections. Also, VPNs with encrypted tunnels can affect the organizational capability to adequately monitor network communications traffic for malicious code. Remote access controls apply to information systems other than public web servers or systems designed for public access. This control addresses authorization prior to allowing remote access without specifying the formats for such authorization. While organizations may use interconnection security agreements to authorize remote access connections, such agreements are not required by this control. Enforcing access restrictions for remote connections is addressed in AC-3.
Do organizations need interconnection security agreements?
While organizations may use interconnection security agreements to authorize remote access connections, such agreements are not required by this control. Enforcing access restrictions for remote connections is addressed in AC-3.