What are the essential processes of access control?
Access control systems include: • File permissions, such as create, read, edit or delete on a file server • Program permissions, such as the right to execute a program on an application server • Data rights, such as the right to retrieve or update information in a database Access control procedures are the methods and mechanisms used by ...
What is the purpose of access control?
- Complete visibility of the network endpoints connecting to the network
- Give secured network access to BYOD users
- Integration with MDM (Mobile Device Management) Solution for controlled access to mobile devices in a network
- Comprehensive Guest Management with customized captive portal and OTP based authentication
What are the types of access control?
What Are the 3 Types of Access Control?
- Discretionary Access Control (DAC)
- Managed/Mandatory Access Control (MAC)
- Role-Based Access Control (RBAC)
- The Benefits of IP Access Control Systems
- Secure Your Business Today
What is the best access control system?
Top 10 Reviews – Best Building Access Control Systems
- Vanderbilt Industries. Vanderbilt Industries is a top-rated door access control solution that offers a variety of access control systems as well as equipment.
- ISONAS. Isonas is top access control solution and is known as the “Pure IP” system meaning it operates solely on a network.
- Protection1. ...
- Bosch. ...
- Kisi. ...
- ADT. ...
- Honeywell. ...
- OpenPath. ...
- Brivo. ...
- Tyco. ...

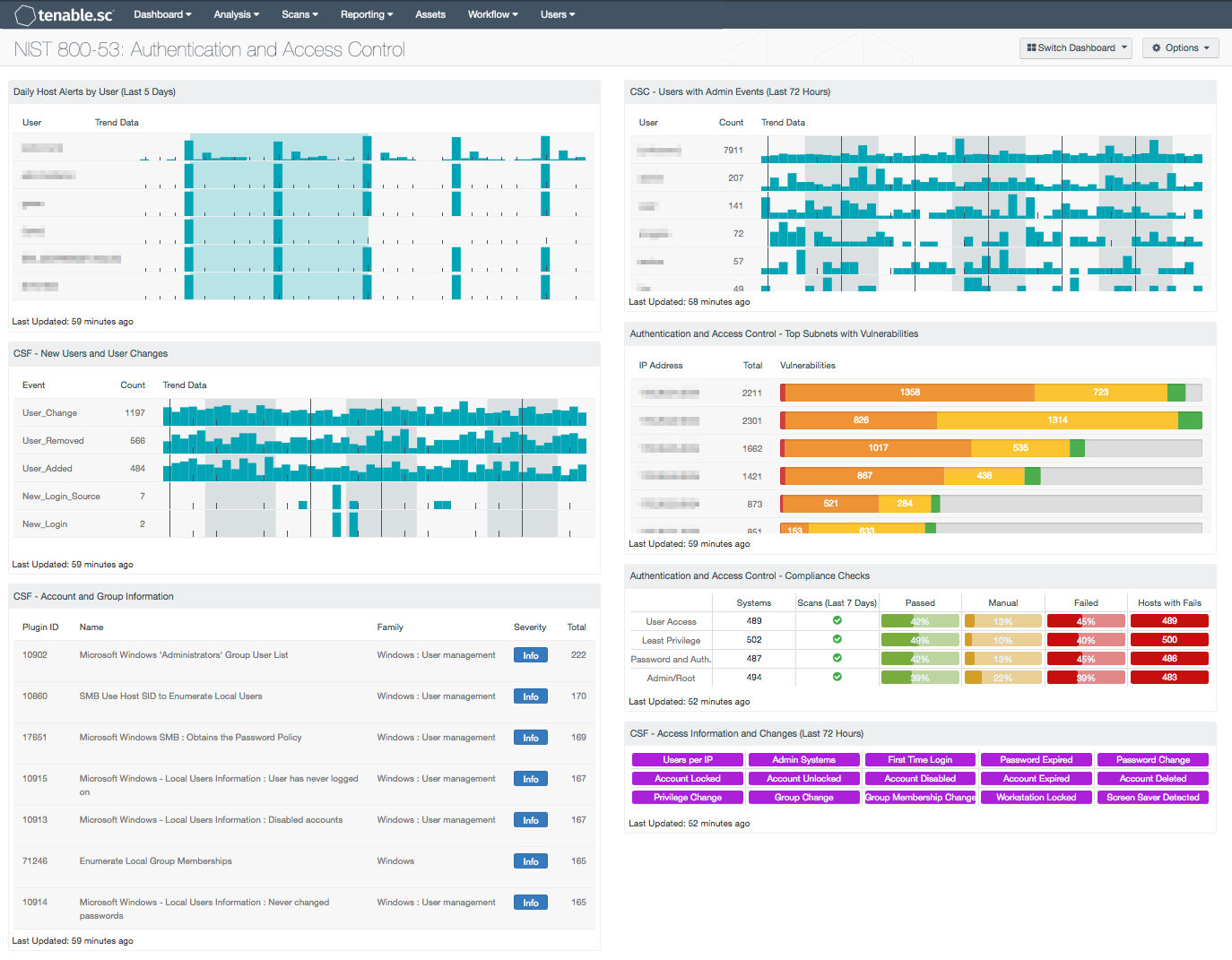
What are the NIST 800-53 technical controls?
What are the NIST 800-53 control families?Access Control. ... Awareness and Training. ... Audit and Accountability. ... Assessment, Authorization and Monitoring. ... Configuration Management. ... Contingency Planning. ... Identification and Authentication. ... Incident Response.More items...
What is the NIST 800 171?
NIST SP 800-171 is a NIST Special Publication that provides recommended requirements for protecting the confidentiality of controlled unclassified information (CUI).
What are NIST controls?
NIST controls are generally used to enhance the cybersecurity framework, risk posture, information protection, and security standards of organizations. While NIST 800-53 is mandatory for federal agencies, commercial entities have a choice in leveraging the risk management framework in their security program.
What are the NIST SP 800-53 security control attributes?
SP 800-53 Revision 4 has been updated to reflect the evolving technology and threat space. Example areas include issues particular to mobile and cloud computing; insider threats; applications security; supply chain risks; advanced persistent threat; and trustworthiness, assurance, and resilience of information systems.
What is the difference between NIST 800-53 and NIST 800-171?
The key distinction between NIST 800-171 vs 800-53 is that 800-171 refers to non-federal networks and NIST 800-53 applies directly to any federal organization.
What is the purpose of NIST 800-53?
What is the purpose of NIST 800-53? The NIST 800-53 framework is designed to provide a foundation of guiding elements, strategies, systems, and controls, that can agnostically support any organization's cybersecurity needs and priorities.
What are the NIST 800 standards?
The NIST 800 Series is a set of documents that describe United States federal government computer security policies, procedures and guidelines. NIST (National Institute of Standards and Technology) is a unit of the Commerce Department.
What is the NIST RMF?
The NIST Risk Management Framework (RMF) provides a comprehensive, flexible, repeatable, and measurable 7-step process that any organization can use to manage information security and privacy risk for organizations and systems and links to a suite of NIST standards and guidelines to support implementation of risk ...
What is NIST security standards?
NIST Compliance at a Glance NIST standards are based on best practices from several security documents, organizations, and publications, and are designed as a framework for federal agencies and programs requiring stringent security measures.
What is the difference between NIST 800-53 and NIST 800 53A?
NIST 800-53A is an extension of the NIST 800-53 that provides additional guidance on the conducting assessment of these controls and a detailed look at this will provide a better understanding of the requirements of 800-53. This additional guidance on these controls make it more easily understandable.
How many controls does NIST 800-53 have?
NIST SP 800-53 has had five revisions and is composed of over 1000 controls. This catalog of security controls allows federal government agencies the recommended security and privacy controls for federal information systems and organizations to protect against potential security issues and cyber attacks.
What is the difference between NIST CSF and NIST 800-53?
NIST CSF provides a flexible framework that any organization can use for creating and maintaining an information security program. NIST 800-53 and NIST 800-171 provide security controls for implementing NIST CSF. NIST 800-53 aids federal agencies and entities doing business with them to comply as required with FISMA.
What is the NIST SP 800-171 and who needs to follow it?
NIST 800-171 sets standards for safeguarding sensitive information on federal contractors' IT systems and networks. By requiring best-practice cybersecurity processes from government contractors, the resilience of the whole federal supply chain is strengthened.
Do I need to be NIST 800-171 compliant?
Computing Services. NIST SP 800-171 compliance is currently required by some Department of Defense contracts via DFARS clause 252.204-7012. The Office of Sponsored Programs is responsible for research contracts and will work with contracting officers to ensure that NIST 800-171 requirements are applicable.
How many controls does NIST 800-171 have?
110The 110 NIST 800-171 security controls are divided into 14 control families. Controls are mapped to appropriate university policies, standards or other documents where possible.
What does NIST stand for?
National Institute of Standards and TechnologyNational Institute of Standards and Technology (NIST)
What is remote access?
Definition (s): Access to an organizational information system by a user (or an information system) communicating through an external, non-organization-controlled network (e.g., the Internet). Source (s):
Where to send comments on a NIST publication?
Comments about specific definitions should be sent to the authors of the linked Source publication. For NIST publications, an email is usually found within the document.
What is an access system?
Access by users (or information systems) communicating external to an information system security perimeter. Access to an organizational system by a user (or a process acting on behalf of a user) communicating through an external network.
What is access to an organizational system?
Access to an organizational system by a user (or a process acting on behalf of a user) communicating through an external network (e.g., the Internet).
What is a portal in remote access?
A portal is a server that offers access to one or more applications through a single centralized interface. A teleworker uses a portal client on a telework client device to access the portal. Most portals are web-based—for them, the portal client is a regular web browser. Figure 2-2 shows the basic portal solution architecture. The application client software is installed on the portal server, and it communicates with application server software on servers within the organization. The portal server communicates securely with the portal client as needed; the exact nature of this depends on the type of portal solution in use, as discussed below.
Where should a remote access server be placed?
Intermediate remote access servers connect external hosts to internal resources, so they should usually be placed at the network perimeter. The server acts as a single point of entry to the network from the perimeter and enforces the telework security policy. If remote access is needed to a particular sub-network within the organization, there are generally two options: 1) place the remote access server at the edge of the sub-network, where the sub-network joins the full network; or 2) place it at the perimeter of the full network and use additional mechanisms to restrict the teleworkers to only be able to access the specified sub-network. The value of placing the remote access server at the network perimeter versus the sub-network perimeter differs for the four types of remote access methods:
What is the key component of controlling access to network communications and protecting their content?
major component of controlling access to network communications and protecting their content is the use of cryptography. At a minimum, any sensitive information passing over the Internet, wireless networks, and other untrusted networks should have its confidentiality and integrity preserved through use of cryptography. Federal agencies are required to use cryptographic algorithms that are NIST-approved and contained in FIPS-validated modules. The FIPS 140 specification, Security Requirements for Cryptographic Modules, defines how cryptographic modules are validated.24 It is important to note that for a remote access system to be considered compliant to FIPS 140, both sides of the interaction must have passed FIPS 140 validation. Many remote access systems, such as SSL VPNs, support the use of remote access client software from other vendors, so there may be two or more distinct validation certificates for a particular remote access system.
What is remote desktop access?
remote desktop access solution gives a teleworker the ability to remotely control a particular PC at the organization, most often the user’s own computer at the organization’s office, from a telework client device. The teleworker has keyboard and mouse control over the remote computer and sees that computer’s screen on the local telework client device’s screen. Remote desktop access allows the user to access all of the applications, data, and other resources that are normally available from their PC in the office. Figure 2-3 shows the basic remote desktop access architecture. A remote desktop access client program or web browser plug-in is installed on each telework client device, and it connects directly with the teleworker’s corresponding internal workstation on the organization’s internal network.
Why is remote access important?
The security of remote access servers, such as VPN gateways and portal servers, is particularly important because they provide a way for external hosts to gain access to internal resources, as well as a secured, isolated telework environment for organization-issued, third-party-controlled, and BYOD client devices. In addition to permitting unauthorized access to enterprise resources and telework client devices, a compromised server could be used to eavesdrop on communications and manipulate them, as well as a “jumping off” point for attacking other hosts within the organization. Recommendations for general server security are available from NIST SP 800-123, Guide to General Server Security. Remote access servers should be kept fully patched, operated using an organization-defined security configuration baseline, and managed only from trusted hosts by authorized administrators.
Which framework is most pertinent for securing enterprise telework, remote access, and BYOD technologies?
This appendix lists the Cybersecurity Framework48 subcategories that are most pertinent for securing enterprise telework, remote access, and BYOD technologies. Next to each subcategory is an explanation of its implications particular to enterprise telework, remote access, and BYOD security.
Can telework devices be stolen?
All telework devices, regardless of their size or location, can be stolen. Some thieves may want to read the contents of the data on the device, and quite possibly use that data for criminal purposes. To prevent this, an organization should have a policy of encrypting all sensitive data when it is at rest on the device and on removable media used by the device. The creation and use of cryptographic keys for encrypting remote data at rest should follow the same policies that an organization has for other keys that protect data at rest.33
What is remote access?
Remote access is access to organizational systems (or processes acting on behalf of users) that communicate through external networks such as the Internet. Types of remote access include dial-up, broadband, and wireless. Organizations use encrypted virtual private networks (VPNs) to enhance confidentiality and integrity for remote connections. The use of encrypted VPNs provides sufficient assurance to the organization that it can effectively treat such connections as internal networks if the cryptographic mechanisms used are implemented in accordance with applicable laws, executive orders, directives, regulations, policies, standards, and guidelines. Still, VPN connections traverse external networks, and the encrypted VPN does not enhance the availability of remote connections. VPNs with encrypted tunnels can also affect the ability to adequately monitor network communications traffic for malicious code. Remote access controls apply to systems other than public web servers or systems designed for public access. Authorization of each remote access type addresses authorization prior to allowing remote access without specifying the specific formats for such authorization. While organizations may use information exchange and system connection security agreements to manage remote access connections to other systems, such agreements are addressed as part of CA-3. Enforcing access restrictions for remote access is addressed via AC-3.
Does VPN allow remote access?
Still, VPN connections traverse external networks, and the encrypted VPN does not enhance the availability of remote connections. VPNs with encrypted tunnels can also affect the ability to adequately monitor network communications traffic for malicious code. Remote access controls apply to systems other than public web servers or systems designed ...
What is dynamic access control?
Supplemental Guidance: In contrast to conventional access control approaches which employ static information system accounts and predefined sets of user privileges, dynamic access control approaches (e.g., service-oriented architectures) rely on run time access control decisions facilitated by dynamic privilege management. While user identities may remain relatively constant over time, user privileges may change more frequently based on ongoing mission/business requirements and operational needs of organizations. Dynamic privilege management can include, for example, the immediate revocation of privileges from users, as opposed to requiring that users terminate and restart their sessions to reflect any changes in privileges. Dynamic privilege management can also refer to mechanisms that change the privileges of users based on dynamic rules as opposed to editing specific user profiles. This type of privilege management includes, for example, automatic adjustments of privileges if users are operating out of their normal work times, or if information systems are under duress or in emergency maintenance situations. This control enhancement also includes the ancillary effects of privilege changes, for example, the potential changes to encryption keys used for communications. Dynamic privilege management can support requirements for information system resiliency. Related control: AC-16.
What is dynamic approach to creating information system accounts?
Supplemental Guidance: Dynamic approaches for creating information system accounts (e.g., as implemented within service-oriented architectures) rely on establishing accounts (identities) at run time for entities that were previously unknown. Organizations plan for dynamic creation of information system accounts by establishing trust relationships and mechanisms with the appropriate authorities to validate related authorizations and privileges. Related control: AC-16.
When does the information system terminate shared/group account credentials?
The information system terminates shared/group account credentials when members leave the group.
What are the types of information systems?
Supplemental Guidance: Information system account types include, for example, individual, shared, group, system, guest/anonymous, emergency, developer/manufacturer/vendor, temporar y, and service. Some of the account management requirements listed above can be implemented by organizational information systems. The identification of authorized users of the information system and the specification of access privileges reflects the requirements in other security controls in the security plan. Users requiring administrative privileges on information system accounts receive additional scrutiny by appropriate organizational personnel (e.g., system owner, mission/business owner, or chief information security officer) responsible for approving such accounts and privileged access. Organizations may choose to define access privileges or other attributes by account, by type of account, or a combination of both. Other attributes required for authorizing access include, for example, restrictions on time-of-day, day-of-week, and point-of-origin. In defining other account attributes, organizations consider system-related requirements (e.g., scheduled maintenance, system upgrades) and mission/business requirements, (e.g., time zone differences, customer requirements, remote access to support travel requirements). Failure to consider these factors could affect information system availability. Temporary and emergency accounts are accounts intended for short-term use. Organizations establish temporary accounts as a part of normal account activation procedures when there is a need for short-term accounts without the demand for immediacy in account activation. Organizations establish emergency accounts in response to crisis situations and with the need for rapid account activation. Therefore, emergency account activation may bypass normal account authorization processes. Emergency and temporary accounts are not to be confused with infrequently used accounts (e.g., local logon accounts used for special tasks defined by organizations or when network resources are unavailable). Such accounts remain available and are not subject to automatic disabling or removal dates. Conditions for disabling or deactivating accounts include, for example: (i) when shared/group, emergency, or temporary accounts are no longer required; or (ii) when individuals are transferred or terminated. Some types of information system accounts may require specialized training.
What is a control?
The controls are flexible and customizable and implemented as part of an organization-wide process to manage risk. The controls address diverse requirements derived from mission and business needs, laws, executive orders, directives, regulations, policies, standards, and guidelines.
What is security and privacy control?
This publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets, individuals, other organizations, and the Nation from a diverse set of threats and risks, including hostile attacks, human errors, natural disasters, structural failures, foreign intelligence entities, and privacy risks. The controls are flexible and customizable and implemented as part of an organization-wide process to manage risk. The controls address diverse requirements derived from mission and business needs, laws, executive orders, directives, regulations, policies, standards, and guidelines. Finally, the consolidated control catalog addresses security and privacy from a functionality perspective (i.e., the strength of functions and mechanisms provided by the controls) and from an assurance perspective (i.e., the measure of confidence in the security or privacy capability provided by the controls). Addressing functionality and assurance helps to ensure that information technology products and the systems that rely on those products are sufficiently trustworthy.