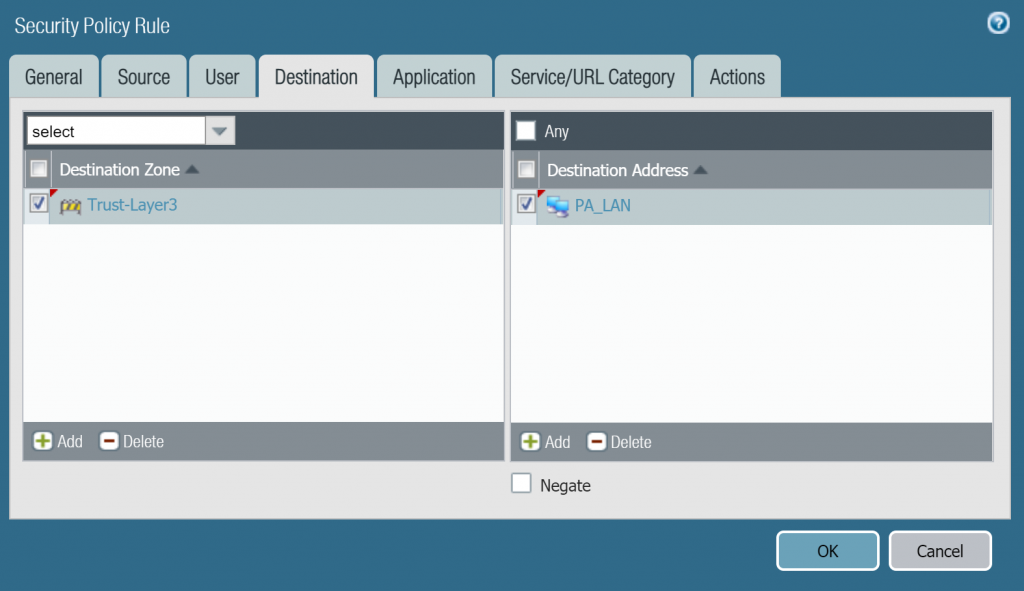
In the Palo Alto application, click Policies > Security > Add. Create firewalls rules to allow inbound traffic from the internet to the external IP address of the firewall. This rule should allow IPSec.
Full Answer
How to connect to Palo Alto VPN?
How To Connect To Palo Alto Vpn Inside? To configure IPSec VPN by setting up a tunnel interface, choose this question in the Network >Interface > Tunnel tab: and click OK. Adding and defining an IKE cryptocurrency profile (IKEv1 Phase-1) can be done through IKE network> profile and profile parameters > IKE Crypto network >.
How to configure GlobalProtect in Palo Alto?
- On the firewall that is hosting your GlobalProtect gateway (s) (or on Panorama if you plan to share the HIP profiles among multiple gateways), select Objects GlobalProtect HIP Profiles , ...
- Enter a Name and Description to identify the profile.
- Click Add Match Criteria to open the HIP Object/Profiles Builder.
Does Palo Alto support L2TP?
does palo alto support l2tp , pptp over ipsec vpn? Hello, Unfortunately, L2TP is currently not supported on PANOS. However, PPTP traffic through the PAN device is available. If you're utilizing a Microsoft VPN solution, you can implement a static nat to make PPTP functional.
How to configure IPsec?
To configure a route-based or policy-based IPsec VPN using autokey IKE:
- Configure interfaces, security zones, and address book information. (For route-based VPNs) Configure a secure tunnel st0.x interface. ...
- Configure Phase 1 of the IPsec VPN tunnel. ...
- Configure Phase 2 of the IPsec VPN tunnel. ...
- Configure a security policy to permit traffic from the source zone to the destination zone. ...
- Update your global VPN settings.
Does remote access VPN use IPsec?
While Remote access VPN supports SSL and IPsec technology.
How do I access my Palo Alto firewall remotely?
Go to Network > Interfaces > Ethernet, then click on the Interface name, for the external interface. I used ethernet1/3. Click the Advanced tab. Under the Other Info tab, next to Management Profile, use the dropdown to select Remote_management, then click OK.
What is IPsec remote access VPN?
Internet Protocol Security (IPsec) is a suite of protocols that support cryptographically secure communication at the IP layer. With IPsec connections, you can provide secure access between two hosts, two sites, or remote users and a LAN.
How do I configure IPsec VPN tunnel in Palo Alto?
Go to Network >Interface > Tunnel tab, click Add to create a new tunnel interface and assign the following parameters:Name: tunnel. ... Virtual router: (select the virtual router you would like your tunnel interface to reside)More items...•
How does remote access VPN Work?
A remote access VPN works by creating a virtual tunnel between an employee's device and the company's network. This tunnel goes through the public internet but the data sent back and forth through it is protected by encryption and security protocols to help keep it private and secure.
How do I connect to Palo Alto VPN?
1:2726:18Setup GlobalProtect VPN with Palo Alto - YouTubeYouTubeStart of suggested clipEnd of suggested clipThe next step is to set up what's called an authentication profile and to do that let's go ahead andMoreThe next step is to set up what's called an authentication profile and to do that let's go ahead and jump in to our Palo Alto and set that up.
What is the difference between site to site VPN and remote access VPN?
A remote access VPN connects remote users from any location to a corporate network. A site-to-site VPN, meanwhile, connects individual networks to each other.
Is IPsec VPN better than SSL VPN?
When it comes to corporate VPNs that provide access to a company network rather than the internet, the general consensus is that IPSec is preferable for site-to-site VPNs, and SSL is better for remote access.
What is the difference between VPN and IPsec?
SSL VPNs. The major difference between an IPsec VPN and an SSL VPN comes down to the network layers at which encryption and authentication are performed. IPsec operates at the network layer and can be used to encrypt data being sent between any systems that can be identified by IP addresses.
How do I configure IPsec VPN site to site?
To configure a route-based or policy-based IPsec VPN using autokey IKE:Configure interfaces, security zones, and address book information. ... Configure Phase 1 of the IPsec VPN tunnel. ... Configure Phase 2 of the IPsec VPN tunnel. ... Configure a security policy to permit traffic from the source zone to the destination zone.More items...
How IPsec VPN works step by step?
Authenticates and protects the identities of the IPSec peers. Negotiates a matching IKE SA policy between peers to protect the IKE exchange. Performs an authenticated Diffie-Hellman exchange with the end result of having matching shared secret keys. Sets up a secure tunnel to negotiate IKE phase two parameters.
How do I set up IPsec VPN?
Configuring the Server sideIn the administration interface, go to Interfaces.Double-click on VPN Server.In the VPN Server Properties dialog box, check Enable IPsec VPN Server. ... On tab IPsec VPN, select a valid SSL certificate in the Certificate pop-up list.Check Use preshared key and type the key.Save the settings.
What are the 3 protocols used in IPsec?
IPsec is a suite of protocols widely used to secure connections over the internet. The three main protocols comprising IPsec are: Authentication Header (AH), Encapsulating Security Payload (ESP), and Internet Key Exchange (IKE).
What is OpenVPN vs IPsec?
OpenVPN uses a chosen UDP or TCP port, allowing for flexible configuration choices. On the other hand, IPSec uses predefined communication channels, UDP 500 and UDP 4500, to establish the encrypted tunnel and ESP for the transmission of encrypted data.
How to add IPSec crypto to VPN?
Under Network > Network Profiles > IPSec Crypto , click Add to create a new Profile, define the IPSec Crypto profile to specify protocols and algorithms for identification, authentication, and encryption in VPN tunnels based on IPSec SA negotiation (IKEv1 Phase-2). These parameters should match on the remote firewall for the IKE Phase-2 negotiation to be successful.
How to create IPSec tunnel?
Under Network > IPSec Tunnels, click Add to create a new IPSec Tunnel. In the General window use the Tunnel Interface, the IKE Gateway and IPSec Crypto Profile from above to set up the parameters to establish IPSec VPN tunnels between firewalls.
How to add IKE crypto profile?
Go to Network > Network Profiles > IKE Crypto , click Add and define the IKE Crypto profile (IKEv1 Phase-1) parameters. Name does not matter, can be whatever you like. These parameters should match on the remote firewall for the IKE Phase-1 negotiation to be successful.
When configuring an IPSec tunnel, what is the proxy-ID configuration?
When configuring an IPSec Tunnel Proxy-ID configuration to identify local and remote IP networks for traffic that is NATed, the Proxy-ID configuration for the IPSec Tunnel must be configured with the Post-NAT IP network information, because the Proxy-ID information defines the networks that will be allowed through the tunnel on both sides for the IPSec configuration.
What is passive mode in firewall?
Enable Passive Mode - The firewall to be in responder only mode. The firewall will only respond to IKE connections and never initiate them.
Does Palo Alto Networks support IPSec?
NOTE: The Palo Alto Networks supports only tunnel mode for IPSec VPN. The transport mode is not supported for IPSec VPN.
Does topology require a license?
For such topology, does not require any special license.
Does the PA220 have a VPN?
In case this isn't clear.... the WAN interface of the PA220 would service both the remote access vpn and the ipsec site -to-site vpn.
How to add a VPN tunnel?
Add Primary and Secondary IPSec VPN Tunnels 1 Give the tunnel a descriptive#N#Name#N#. 2 Select the#N#Branch Device Type#N#for the IPSec device at the remote network site that you’re using to establish the tunnel with Prisma Access. 3 For the#N#Branch Device IP Address#N#, choose to use either a#N#Static IP#N#address that identifies the tunnel endpoint or a#N#Dynamic#N#IP address.#N#If you set the#N#Branch Device IP Address#N#to#N#Dynamic#N#, you must also add the IKE ID for the remote network site (#N#IKE Local Identification#N#) or for Prisma Access (#N#IKE Peer Identification#N#) to enable the IPSec peers to authenticate.#N#Because you do not have the values to use for the Prisma Access IKE ID (#N#IKE Peer Identification#N#) until the remote network is fully deployed, you would typically want to set the IKE ID for the remote network site (#N#IKE Local Identification#N#) rather than the Prisma Access IKE ID.
What is Prisma Access?
Based on the IPSec device type you selected, Prisma Access provides a recommended set of IPSec protocol and key lifetime settings to secure data within the IPSec tunnel between your branch device and Prisma Access in IKE Phase 2 for the Security Association (SA). You can use the recommended settings, or customize the settings as needed for your environment.
What is the authentication algorithm for Prisma Access?
Prisma Access supports the following authentication algorithms: sha1 (160 bits), sha256 (256 bits), sha384 (384 bits), sha512 (512 bits), and md5 (128 bits). You can also select null (no authentication).
Does Prisma Access initiate IKE connections?
so that Prisma Access only response to IKE connections and does not initiate them.
Does Prisma Access have IKE?
Based on the IPSec device you use to establish the tunnel at the remote network site, Prisma Access provides built-in, recommended IKE and IPSec security settings. You can use the recommended settings to get started quickly, or customize them as needed for your environment.
What is the difference between SSL VPN and IPsec?
Both are in popular use, but the main difference is the layer of network traffic it secures. An IPsec connection requires client software (provided by a third party or by the operating system), whereas an SSL VPN connection can be accessed through a web browser.
What is remote access?
Remote access allows end users to access resources on the corporate network from a distant location. The most common function of remote access is to enable employees who are traveling or telecommuting to connect to the company network and access resources such as internal applications, intranet, mail services, and file sharing.
How does a VPN work?
A VPN creates a “tunnel” that passes traffic privately between the remote network and the user. The tunnel protects the traffic and keeps it safe from being intercepted or tampered with. VPNs are commonly implemented using the protocols IPsec or SSL. Both are in popular use, but the main difference is the layer of network traffic it secures.
What is proxy based portal?
Proxy-based portals require remote users to connect to an intermediary server (the SSL Portal VPN) where they are granted access to applications and resources permitted from the network administrators.
What is emerging model of remote access?
An emerging model of remote access provides the benefit of a tunnel for broad application support while retaining strong control over access to applications through the next-generation firewall security policy. This approach allows administrators to safely enable remote user activity and access on the network. Combining the benefits from earlier implementations, this model is the most secure and practical remote access solution available today.
What is the primary method of remote access?
Virtual Private Networks. The predominant method of providing remote access is via a Virtual Private Network (VPN) connection. Normally, a user has no expectation of privacy on a public network, as their network traffic is viewable by other users and system administrators.
Does SSL VPN use client software?
However, due to the growing complexity of running code in a web browser and the diversity of browser platforms, many SSL VPN products now use client software as well. SSL VPNs may also provide remote access through a proxy. Proxy-based portals require remote users to connect to an intermediary server ...
How to add IKE crypto to network?
Go to Network >> Network Profile >> IKE Crypto and click Add. Now add below details-
What IP address is Sitea to Siteb?
We need to add routes to reach SITEA to SITEB and vise-versa. Below are the route from SITEA to SITEB, where gateway is IPSec peer IP , which is 10.10.10.2
Can we reach SiteB from SiteA?
We can successfully reach SiteB from SiteA. Let’s verify IPSec information from palo alto using below command-
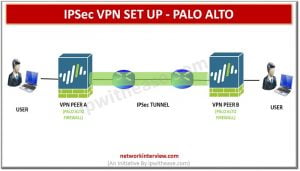
What is VPN in a VPN?
A VPN is a technology that creates a secured network connection over a traditional network by encrypting all communication between two hosts. We'll take a look at how to set up a site-to-site tunnel that uses strong IPSec encryption. When preparing for a site-to-site VPN configuration, many times you will need to have a conversation with ...
What is the authentication method on IKE?
The Authentication method can be set to a pre-shared key to be used on both peers to initiate negotiation, or a certificate can be imported to authenticate the handshake. On the IKE Gateway, under Advanced Options, several options can be set to accomodate certain situations: