
Some notable remote access methods that enable enterprises to secure access to their IT infrastructure include:
- Virtual private network (VPN): VPNs are the most common form of remote access. They use authentication and encryption...
- IPsec VPN: IPsec is a group of networking protocols used for establishing encrypted connections, such as VPNs, across...
- Develop a Cybersecurity Policy For Remote Workers. ...
- Choose a Remote Access Software. ...
- Use Encryption. ...
- Implement a Password Management Software. ...
- Apply Two-factor Authentication. ...
- Employ the Principle of Least Privilege. ...
- Create Employee Cybersecurity Training.
How to protect remote access?
To enable Remote Access in your UniFi Protect application:
- Access the UniFi OS Console hosting Protect via its IP address. ...
- Log in to your Ubiquiti SSO account.
- Go to the System Settings > Advanced menu, and enable the Remote Access toggle.
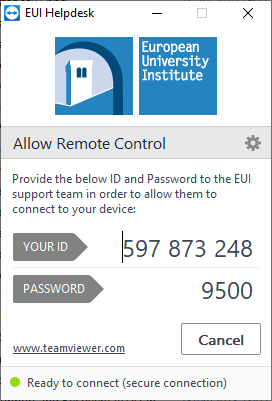
How to lock down TeamViewer for more secure remote access?
- access to your authenticator. Security: easy access, strong passwords and whitelists
- Our next stop is the security section. Select "Security" on the left panel. ...
- Some people prefer to manually set a very reliable password for their computer (and not rely on the randomly generated, which TeamViewer uses by default). ...
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...
Can someone help me with remote access?
Windows Remote Assistance lets someone you trust take over your PC and fix a problem from wherever they are. Before you can use it, you'll need to enable access. In the search box on the taskbar, type remote assistance, and then select Allow Remote Assistance invitations to be sent from this computer from the list of results.
What is a secure remote access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
Why is secure remote access important?
A secure remote access system protects your employees from web-based threats such as phishing attacks, ransomware and malware while they're logged in to your company's network. These cyber incidents can lead to unauthorized access and use of both the company's business data and the employee's personal data.
Which is a secure remote access protocol?
POINT-TO-POINT TUNNELING PROTOCOL (PPTP) It's used to establish virtual connections across the internet via PPP and TCP/IP, enabling two networks to use the internet as their WAN link while retaining the security benefits of a private network. PPTP is a great option because it's simple and secure.
Is remote access security Secure?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
What are the examples of remote user security policy best practices?
Best Practices For Remote Access SecurityEnable encryption. ... Install antivirus and anti-malware. ... Ensure all operating systems and applications are up to date. ... Enforce a strong password policy. ... Use Mobile Device Management (MDM) ... Use Virtual Private Network (VPN) ... Use two-factor authentication.More items...•
What is the most secure method for remote access?
The following technologies can contribute to secure remote access:VPNs;intrusion prevention systems and intrusion detection systems;Secure Access Service Edge (SASE) and software-defined perimeter;firewalls;cloud access security brokers;zero-trust network access;virtual desktop infrastructure; and.More items...•
What is the most secure remote access?
Best for Team Collaboration TeamViewer TeamViewer lets users access remote computers and devices running Windows, Mac OS, Linux, Android, and iOS. It also offers drag-and-drop file transfer, remote printing, and secure unattended access using two-factor authentication and 256-bit AES encryption.
What are the three types of remote connections?
Remote Access Control MethodsDirect (Physical) Line. The first direct remote access control that can be implemented is a direct line from a computer to the company's LAN. ... Virtual Private Network. Another method which is more common is establishing a VPN. ... Deploying Microsoft RDS.
Why is it important to mobile workers and users to know what the risks threats and vulnerabilities are when conducting remote access through the public Internet?
It is important to mobile workers and users to know what the risk, threats, and vulnerabilities so that they will know about how simply easy it is to access information through an open public network which could cause loss of vulnerable information.
What are potential risks associated with remote access?
Five Remote Access Security Risks And How To Protect Against ThemWeak remote access policies. ... A deluge of new devices to protect. ... Lack of visibility into remote user activity. ... Users mixing home and business passwords. ... Opportunistic phishing attempts.
What reasons would remote access be utilized in an enterprise?
Remote access, also known as remote login, is the ability to access the data stored on a computer from a remote location. It enables you to open, edit, and save files located on your device from anywhere in the world. This ability is handy for offsite workers, travelers, and those who work out of office.
What are the secure methods the remote users can use to connect to the internal network to perform file operations?
Most commonly, remote workers will use a remote access VPN client to connect to their organization's VPN gateway to gain access to its internal network, but not without authenticating first. Usually, there are two choices when using VPNs: IP Security (IPsec) or Secure Sockets Layer (SSL).
How does secure remote access work?
Every remote worker needs a way to connect with remote desktop services and applications that won't slow down their workflows. At the same time, IT administrators must manage those connections to ensure they don't leave the network open to threats.
Why is secure remote access important to remote work security?
Secure remote access approaches are so vital because it’s now impossible to control security at the endpoint. Each user in a remote or hybrid workforce is connecting to the network from a different type of computer or smartphone, and they’re using a variety of internet connections to log in.
Why Does Secure Remote Access Matter?
From reputational damage to regulatory fines to loss of customer trust, future business, and intellectual property – the costs can be widespread and high. In fact, the average cost of a data breach is $3.92M. If that weren’t enough, a data breach originating from a third party is both more likely and costly: 63% of data breaches come from a third party, and a data breach that originated via a third party costs an organization an additional $370,000. In short, you can’t afford not to secure the remote access of your third parties.
What is the final element of secure remote access?
The final element in secure remote access for third parties is visibility into exactly what they are doing in your network. Ideally, you can review audit logs that give you immediate visibility, in the event that something should break due to a third party, or you have to demonstrate compliance with regulatory requirements. Your method should provide:
What is remote access in business?
In today’s business environment, remote access to systems, data, and servers is a common and necessary occurrence. This remote access can be for employees, who are working from home or distributed remotely, and it can also be for third parties, such as contractors, technology vendors, business partners, and consultants.
How do current methods fail to properly secure third party remote access?
Current methods fail to properly secure third party remote access by identifying each individual, controlling their access, and auditing their activity.
What is the line of defense for remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly.
What is the first thing that’s required to ensure smooth remote access via a VPN?
The first thing that’s required to ensure smooth remote access via a VPN is to plan out a comprehensive network security policy.
Why is IPSEC used?
This allows IPSec to protect data transmission in a variety of ways. IPSec is used to connect a remote user to an entire network. This gives the user access to all IP based applications. The VPN gateway is located at the perimeter of the network, and the firewall too is setup right at the gateway.
What are the implications of IPSec connections for corporations?
What are the implications of IPSec connections for corporations, considering the very nature of this connection? Well, your employee will only be able to access the network from a single, authorized device. Security is further boosted by the enforcement of antivirus and firewall policies.
What is IPSEC encryption?
IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect data flows between hosts and security gateways.
Why use two factor authentication for VPN?
Adopting two-factor authentication for remote access through VPN further boosts your network security. Now let’s take a look at why you should choose a particular VPN type as a secure connection methodology instead of the alternatives.
What is remote access VPN?
The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network (VPDN) due to its early adoption on dial-up internet.
Direct Internet RDP access is not a solution
Don’t. Do. It. Period. RDP’s vulnerabilities go beyond exploiting weak passwords. The protocol itself is vulnerable. There has been something of a renaissance in RDP exploits since people tend to open it up in Azure and/or AWS. Instead of opening TCP port 3389 to the world, deploy a proper RDS environment with RD Gateway.
Use secure passwords
Good passwords are the first line of defense in protecting your systems. Passwords should be unique, of length, have a level of complexity, not be repeated. Diversity is our strength especially when it comes to passwords. Don’t use the same password on multiple systems. If a door has seven locks that use the same key, the door only has one lock.
Use Multifactor Authentication (MFA) where you can
MFA can be implemented with your VPN, Citrix and other systems. A system protected by MFA is prohibitively hard to exploit when passwords are compromised.
Use real certificates
RD Gateway, Citrix and SSL VPNs use certificates. Out of the box most systems come with self-signed certificates out of the box. These are the certificates that give you an error message and warning. Those are there for a reason. It is impossible to guarantee that certificate was legitimately issued.
Secure your VPN
I have a personal preference for IPsec VPNs. I hold this opinion due to the deluge of security vulnerabilities that are constantly discovered with SSL. Use modern protocols. Use Active Directory integrated authentication. Use MFA.
Paths to Home Connectivity
Current regulations do not allow schools to use federal E-rate funding to provide students with home internet. Even if districts want to simply extend their existing wireless networks beyond their school walls, they cannot do so if they purchased that broadband connectivity with E-rate funds.
Security Considerations
A number of schools have supported learning primarily by offering students access to third-party resources that are hosted in the public cloud. In these instances, students aren’t touching the district’s IT network. Still, even when students aren’t interacting with district resources, there may be security and compliance concerns to consider.
What is cloud based remote access?
Cloud-based remote access is a new type of remote access solution that enables flexible remote access to field machines. The network topology of a cloud-based remote access solution has three components: a remote gateway, a cloud server, and client software. Remote gateways are connected to field equipment in order to remotely access and control them. Client software is installed on the engineer’s PC. The cloud server can be installed on a cloud-based platform such as Amazon Web Service or Microsoft Azure. The remote gateway and client software will both initiate outbound secure connection requests to the cloud server. The cloud server will map the two connection requests and after successful authentication on both sides, a connection will be established.
What is remote gateway?
Remote gateways are connected to field equipment in order to remotely access and control them. Client software is installed on the engineer’s PC. The cloud server can be installed on a cloud-based platform such as Amazon Web Service or Microsoft Azure.
How to achieve a higher level of security?
One way to achieve a higher level of security is to have different pre-shared keys or X.509 certificates for each VPN tunnel. When the number of VPN connections required is few, it is easy to manage the keys or certificates for these connections. However, as the number of VPN tunnels grows, it would be very hard to manage these keys and certificates.
Why are RDC connections so troublesome?
RDC connections are equally troublesome in that they expose computing equipment on the plant network to the public network , creating security risks. Mitigating these security issues requires additional resources, both in terms of human resources and setup and maintenance costs. 4. VPN Security Is Hard to Manage.
What is VPN connection?
VPN connections between machine builders and machine operators are usually site-to-site connections, which typically provide a machine builder remote access to all local devices in a plant's network. The only way to mitigate this security risk is for IT departments to create separate end-to-end connections using VPN technology, which is complex and expensive, and drastically increases maintenance costs.
Author: Haris Khan
Remote work is the new normal for IT teams around the globe, and there is no surprise as to why remote work is becoming so increasingly popular for organizations. The modern employee workforce is no longer restricted to one physical location.
What is secure remote access?
Secure remote access refers to the technology used for securely accessing a system or application remotely. Cybercriminals and malicious actors are consistently looking out for vulnerabilities and loopholes in remote work infrastructures to exploit and plan cyber attacks.
Which technologies are used for remote work access?
Secure remote access can be effectively implemented by utilizing a collection of highly innovative, secure, and flexible technologies while accessing a system or application from a remote location A few prominent examples of such technologies are listed below:
10 Best Practices for Secure Remote Work Access
Some of the best practices that you can adopt to improvise remote access security in your organization are described below:
Why cloud desktops are an optimal choice for secure remote access?
Cloud desktop solutions offer greater flexibility and ease of access as all of your files, applications and desktop reside on the cloud. Cloud desktops are one of the most resilient and secure forms of remote access.
All-In-One Secure Remote Access with V2 Cloud
As the organizational trend keeps transitioning to remote work, it’s crucial to comprehend the numerous cybersecurity risks and threats that are associated with remote access security. Remote work has become an increasingly viable option with tons of advantages.
