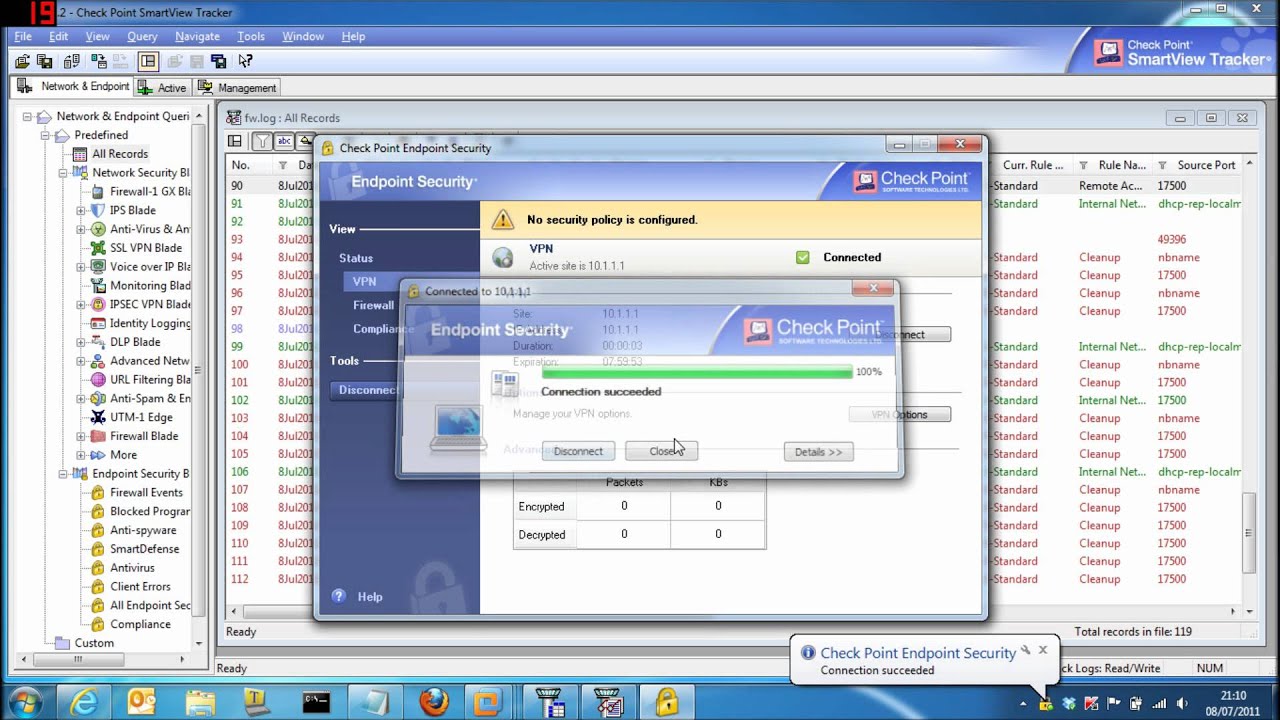
- Step 1. Go to Checkpoint Remote Access Vpn Download website using the links below
- Step 2. Enter your Username and Password and click on Log In
- Step 3. If there are any problems, here are some of our suggestions
Full Answer
What programs allow remote access?
The best remote desktop software right now
- RemotePC. RemotePC is a hugely-popular remote computer access application that’s suitable for both home and—in particular—for business users.
- Zoho Assist. Cloud-based Zoho Assist is one of our favorite remote access tools because it enables you to access almost any device.
- Splashtop. ...
- Parallels Access. ...
- LogMeIn Pro. ...
- Connectwise Control. ...
- TeamViewer. ...
How to properly secure remote access?
- Windows or Mac login when connecting remotely
- Request permission to connect to the user’s computer
- Automatically blank the remote screen when connected
- Automatically lock remote computer when disconnected
- Lock the remote computer’s keyboard and mouse while in session
- Lock the streamer settings using Splashtop admin credentials
How to unlock checkpoint admin account?
How to Unlock Checkpoint Admin Account? Use below command to see locked admin. Use -u to unlock specific admin or -ua for all. fwm lock_admin -v // View locked admins fwm lock_admin -u <admin> // Unlock a specific admin fwm lock_admin -ua // Unlock all admins.
How to lock down TeamViewer for more secure remote access?
How to make TeamViewer more secure
- Part One: Start TeamViewer only when you need it
- Part Two: Assign a secure password
- Part Three: Using Black and White lists
- Part Four: Using Two Factor Authentication (2FA
- Part Five: Using Unattended mode

What is remote access VPN checkpoint?
Provide users with secure, seamless remote access to corporate networks and resources when traveling or working remotely. Privacy and integrity of sensitive information is ensured through multi-factor authentication, endpoint system compliance scanning and encryption of all transmitted data.
How do I access Checkpoint VPN?
Go to VPN > Authentication Servers and click New to add an AD domain. See Configuring Remote Access Authentication Servers. Click permissions for Active Directory users to set access permissions....Use these options for remote access:Check Point VPN clients.Check Point Mobile clients.Check Point SSL VPN.L2TP VPN client.
Is checkpoint a VPN?
Remote Access with Encrypted VPN Technology.
What is mobile checkpoint VPN?
Check Point Mobile VPN for Android devices is an L3 VPN client. It supplies secure connectivity and access to corporate resources using the L3 IPSec/SSL VPN Tunnel. The application is available in the Google Play Store: https://play.google.com/store/apps/details? id=com.checkpoint.VPN&hl=en.
What is the difference between site to site VPN and remote access VPNS?
A remote access VPN connects remote users from any location to a corporate network. A site-to-site VPN, meanwhile, connects individual networks to each other.
What is remote secure access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
What is mobile access in Check Point?
Check Point Mobile Access is the safe and easy solution to securely connect to corporate applications over the Internet with your Smartphone, tablet or personal computer (PC). Mobile Access allows remote and mobile workers to simply and securely connect to email, calendar, contacts and corporate applications.
How does Check Point endpoint security work?
Endpoint protection works via a combination of network and device-level defenses. At the network level, the organization may restrict access to the enterprise network based on a device's compliance with corporate security policies and least privilege.
How do I use Check Point mobile VPN?
0:1010:30Check Point Remote Access VPN Setup and Config - YouTubeYouTubeStart of suggested clipEnd of suggested clipNow as i mentioned it's really easy and simple to set up the vpn. There's a little tab on the leftMoreNow as i mentioned it's really easy and simple to set up the vpn. There's a little tab on the left hand side which says vpn. And then you're left with three sections. Which is remote.
Who makes Checkpoint VPN?
Check Point Software Technologies Ltd. (www.checkpoint.com) is a leading provider of cyber security solutions to governments and corporate enterprises globally. Its solutions protect customers from 5th generation cyber-attacks with an industry leading catch rate of malware, ransomware and other types of attacks.
How do I download Checkpoint VPN?
Follow these instructions in order to install the latest version:Step 1: Download Checkpoint VPN E84.30. Download and save the VPN client installation file from this link. ... Step 2: Remove currently installed version. To uninstall the currently installed version of Check Point VPN Client: ... Step 3: Install new version.
How do I configure site to site VPN in Checkpoint r80?
0:0323:04Checkpoint R80.20 Training -IPSEC site to site Lab - YouTubeYouTubeStart of suggested clipEnd of suggested clipFor that you have to follow some steps so that we can configure our ip6 the first step should beMoreFor that you have to follow some steps so that we can configure our ip6 the first step should be enable ipsec on firewall 1 and firewall 2 which you want to perform. Second step is create a vpn.
How does Checkpoint endpoint security work?
Endpoint protection works via a combination of network and device-level defenses. At the network level, the organization may restrict access to the enterprise network based on a device's compliance with corporate security policies and least privilege.
What is site to site VPN?
A site-to-site virtual private network (VPN) refers to a connection set up between multiple networks. This could be a corporate network where multiple offices work in conjunction with each other or a branch office network with a central office and multiple branch locations.
What is check point security?
Check Point enables organizations to meet NIST remote access security standards and more while easily managing least privilege access to internal resources with real-time, intelligent trust decisions based on defined policies and contextual data. Check Point’s zero trust architecture also restricts user access to authorized resources so that the right people have access to the right resources at the right time, without the need for a VPN.
What is check point?
Check Point provides several secure remote access options for remote workers including VPN Replacement, Third-party Access, Developer Access and Privileged Access Management (PAM) as well as application. database and remote desktop access that meets or exceeds NIST security controls.
Why is remote access important?
The security of remote access servers is particularly important because they provide a way for external hosts to gain access to internal resources, as well as a secured, isolated telework environment for organization-issued, third-party-controlled, and BYOD client devices.
Why do organizations use enterprise remote access?
Many organizations let their employees, contractors, business partners, and vendors use enterprise remote access technologies to perform work remotely using organization-owned and bring your own device (BYOD) client devices that must be secured against data breaches and theft. Security concerns include the lack of physical security controls, the use of unsecured networks, connection of infected devices to internal networks, and the availability of internal resources to external hosts.
What decisions should organizations make about remote access?
Organizations should make risk-based decisions about what levels of remote access should be permitted from which types of client devices.
Which banks are responsible for isolating employees in Asian countries?
Goldman Sachs, JPMorgan Chase, Morgan Stanley and Barclays’ business continuity planning all called for isolating and protecting employees in Asian countries at the coronavirus outbreak epicenter.
What is a remote access VPN community?
By default, the Remote Access VPN Community includes a user group, All Users, that includes all defined users. You can use this group or add different user groups to the Remote Access VPN Community. The community can contain users defined in LDAP, which includes Active Directory, or users defined on the Security Management Server.
Which service defines the protocol and port of client connections to the gateway?
Optional - Select the Visitor Mode Service, which defines the protocol and port of client connections to the gateway.
What happens when no authentication methods are defined for the gateway?
If no authentication methods are defined for the gateway, users select an authentication method from the client.
How to enable IPsec VPN?
From SmartConsole, use the Gateways & Servers menu to configure the gateway and blades. Double-click the gateway. The Check Point Gateway window opens. In the Network Security tab at the bottom, select I Psec VPN to enable the blade.
What is endpoint security VPN?
Endpoint Security VPN combines Remote Access VPN with Endpoint Security in a client that is installed on endpoint computers. It is recommended for managed endpoints that require a simple and transparent remote access experience together with Desktop Firewall rules. It includes:
Is remote access a weak point?
Organizations must also make sure that their corporate network remains safe and that remote access does not become a weak point in their IT security.
Security that Promotes Productivity
Companies no longer have corporate data centers serving a contained network of systems but instead, today typically have some applications on-premises and some in the cloud with employees accessing these applications from a range of devices and multiple locations. This poses security challenges that were not an issue only a decade ago.
Easy Management
Streamline user onboarding/offboarding and effortlessly provision and de-provision access to internal applications in an intuitive process requiring just a few clicks.
Full Visibility
Get a full audit trail of user activity, including activity within an application. All audit logs are tied to users’ accounts and devices and can be exported to your SIEM for additional contextual data.
Improved User Experience
Give users a quick and secure connection to any application, hosted anywhere, from any device through their terminal. Eliminate VPNs, with heavy agents and unstable connectivity.
Ready to Experience Corporate Access?
We’re here to help. Contact us to learn more about clientless, cloud-delivered SASE technology.
