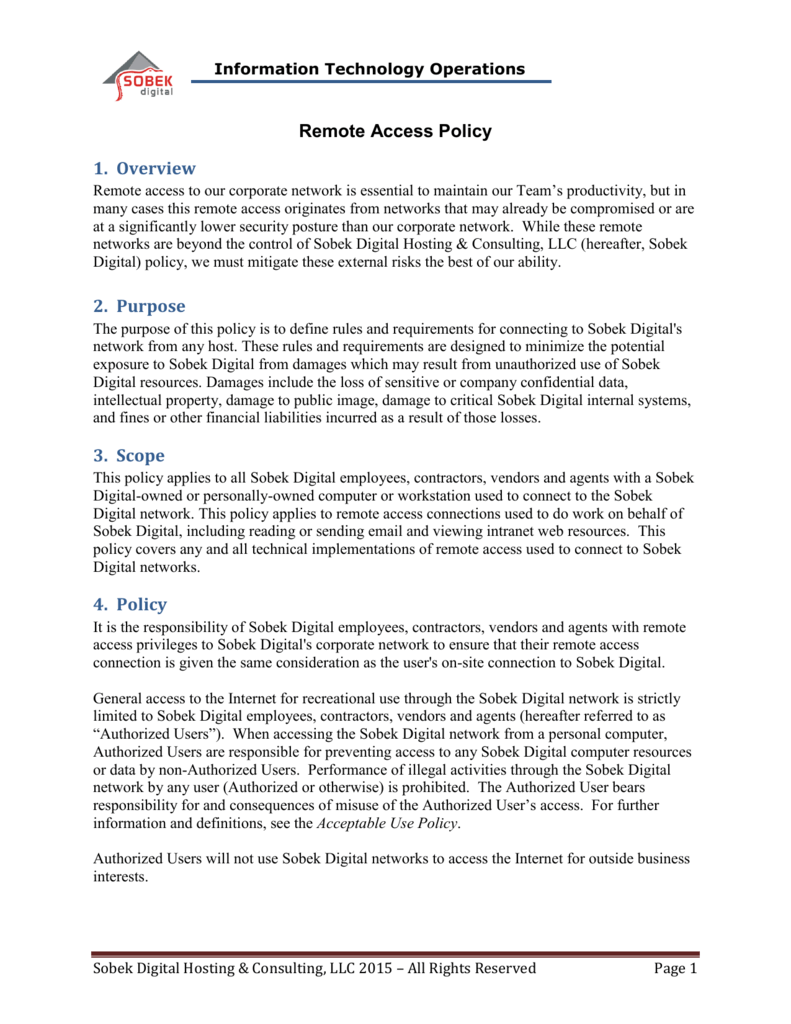
Policy It is the responsibility of <Company Name> employees, contractors, vendors and agents with remote access privileges to <Company Name>'s corporate network to ensure that their remote access connection is given the same consideration as the user's on-site connection to <Company Name>.
What is the company policy for remote network access?
This policy shall apply to all employees, contractors, and affiliates of [COMPANY NAME], and shall govern remote network access for all authorized users. Remote access is defined as any connection to [COMPANY NAME]’s internal network from a location outside of any affiliated company offices.
Do you have a template for implementing remote access policies?
Below, we’ve outlined some strong practices for implementing remote access policies and processes at your organization and included a remote access policy template that can serve as a solid foundation for your own.
What is a remote access policy (rap)?
What Is a Network Security Policy? A remote access policy is commonly found as a subsection of a more broad network security policy (NSP). The network security policy provides the rules and policies for access to a business’s network.
What are the security guidelines for remote access?
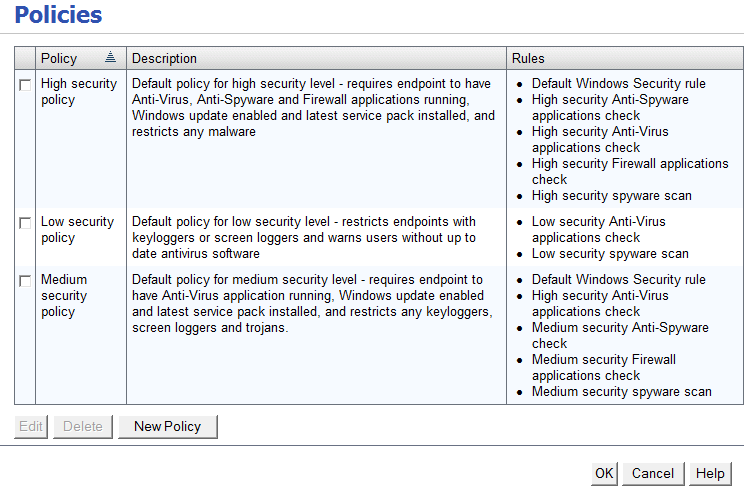
Remote policies have guidelines for access that can include the following: Hardware and software configuration standards for remote access, including anti-malware, firewalls, and antivirus. Encryption policies. Information security, confidentiality, and email policies. Physical and virtual device security.
What should be in a remote access policy?
A remote access policy should cover everything—from the types of users who can be given network access from outside the office to device types that can be used when connecting to the network. Once written, employees must sign a remote access policy acceptance form.
How is remote access critical for a company?
Remote access will allow your employees to safely work from any platform, device, or network whether at their home office, at an internet cafe, or abroad. They can access, edit, and share important files with colleagues, which makes collaboration easy and helps to streamline work for all employees concerned.
Which policy defines the security controls while working remotely?
ISO 27001 controls for remote working: A 6.2. 1 – Mobile device policy.
What constraints are available for use in a remote access policy?
Once a remote access policy has authorized a connection, it can also set connection restrictions (called constraints) based on the following: Encryption strength. Idle timeout. IP packet filters.
What is the purpose of a remote access policy?
A remote access policy aims to keep corporate data safe from exposure to hackers, malware, and other cybersecurity risks while allowing employees the flexibility to work from remote locations.
What should a company consider when looking at adding remote employees?
These expectations should include work hours, availability, deadlines, meeting scheduling and attendance, work submission and more. When setting these requirements consider the differences between remote and in-house workers.
What are examples of remote user security policy best practices?
Best Practices For Remote Access SecurityEnable encryption. ... Install antivirus and anti-malware. ... Ensure all operating systems and applications are up to date. ... Enforce a strong password policy. ... Use Mobile Device Management (MDM) ... Use Virtual Private Network (VPN) ... Use two-factor authentication.More items...•
What are the examples of security considerations for remote users?
Five Remote Access Security Risks And How To Protect Against ThemWeak remote access policies. ... A deluge of new devices to protect. ... Lack of visibility into remote user activity. ... Users mixing home and business passwords. ... Opportunistic phishing attempts.
What policies are required for ISO 27001?
The following policies are required for ISO 27001 with links to the policy templates:Data Protection Policy.Data Retention Policy.Information Security Policy.Access Control Policy.Asset Management Policy.Risk Management Policy.Information Classification and Handling Policy.More items...
What is remote access capabilities?
Remote access is the ability for an authorized person to access a computer or network from a geographical distance through a network connection. Remote access enables users to connect to the systems they need when they are physically far away.
Which of the below are correct protocol for remote access?
REMOTE DESKTOP PROTOCOL (RDP)
Should users be concerned about remote access?
Remote access solutions could leave you vulnerable. If you don't have proper security solutions in place, remote connections could act as a gateway for cybercriminals to access your devices and data. Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular.
What is the risk of RDP?
In many cases, servers with RDP publicly accessible to the internet have failed to enable multi-factor authentication (MFA). This means that an attacker who compromises a user account by exposing a weak or reused password through a brute force attack can easily gain access to a user's workstation via RDP.
What is remote network access?
Remote access is the act of connecting to IT services, applications, or data from a location other than headquarters. This connection allows users to access a network or computer remotely via the internet.
What is wrong with RDP?
RDP connectivity can sometimes fail due to issues with the Credential Security Support Provider (CredSSP) protocol. The CredSSP provides a means of sending user credentials from a client computer to a host computer when an RDP session is in use. In 2018, Microsoft updated the CredSSP to fix a security vulnerability.
What should a remote access policy cover?
To be effective, a remote access policy should cover everything related to network access for remote workers. Organizations must identify which users should be given access, since not everyone may benefit from having the privilege. For example, it might not be a good idea to give remote access to users with access to sensitive data ...
What are the considerations when formulating a remote access policy?
Other considerations when formulating a remote access policy include but are not limited to the following: Standardized hardware and software, including firewalls and antivirus/antimalware programs. Data and network encryption standards. Information security and confidentiality. Email usage.
What is remote work?
Remote work has brought with it a few challenges, including potential computer and network security risks. There is a real need for guidelines surrounding remote access, along with other policies. A remote access policy serves as a guide for remote users connecting to the network. It extends the policies governing network and computer use in ...
Why is password policy important?
It helps ensure that only those users who need it are given network access, as long as their devices are also compliant with the guidelines. When implemented properly, it helps safeguard the network from potential security threats.
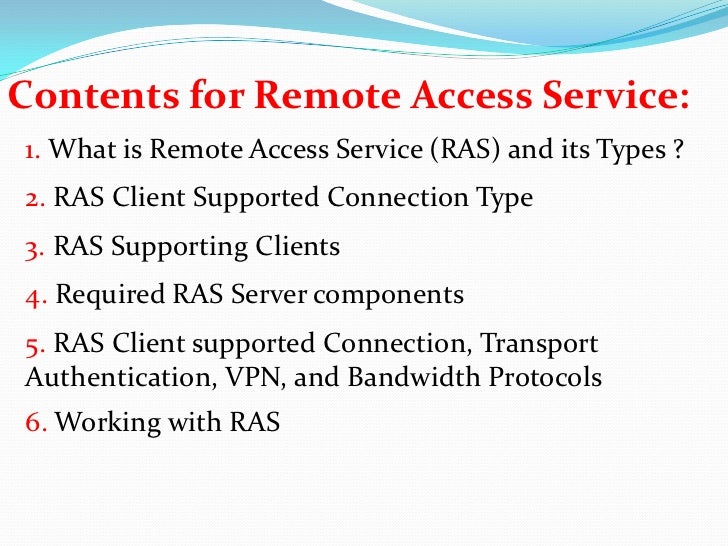
What is RAS in IT?
Parallels® Remote Application Server (RAS) provides secure remote access for your networks out of the box. It features granular permission policies that enable administrators to enforce access restrictions and settings based on the end-users device or Active Directory group, helping ease the workloads of IT administrators by not requiring any further configuration.
Can you customize remote access policy?
Always ensure that your remote access policy is not an exact copy of another organization’s template; rather, you should customize it depending on your requirements. Otherwise, it might not be that useful for your organization.
Working From the Couch
It's Friday and it's been a long week. You spent part of the week traveling for work and the other days in back-to-back meetings. Your alarm goes off at 6 a.m. and you just don't have the energy to jump out of bed, shower, dress up and make the commute to the office.
What's a Remote Access Policy?
A remote access policy is a document that details how an employee can safely connect to a company's computer network while working away from the office.
Inside a Remote Access Policy
Following on the example policy of the university, what should you include to devise this type of policy for your remote workers? First, start with an overview of what remote access is and why it's important to your company.
What is remote access in a company name?
Remote access is defined as any connection to [COMPANY NAME]’s internal network from a location outside of any affiliated company offices.
How long do remote users have to log in?
Remote access must be logged in a central database and kept for a period of at least 30 days. Access logs must be reviewed regularly.
What is the purpose of the Company Name policy?
The intent of this policy is to establish guidelines specifically pertaining to remote access to [COMPANY NAME]’s internal network. Preventing unauthorized access to company data from insecure networks is of utmost importance to [COMPANY NAME]. This policy is designed to ensure remote and/or traveling employees have the ability to securely connect to the corporate network without fear of threat and to provide the Company with an additional means of monitoring and controlling access to the internal network.
Is multifactor authentication required for VPN?
And to make it even stronger, we recommend multi-factor authentication as a requirement for VPN access. Restricted use. Remote access privileges shouldn’t be given out in the office like candy, but rather on an as-needed basis.
Do authorized users share login credentials?
Authorized users must protect their login credentials and must not share them with anyone for any reason. All inbound connections to [COMPANY NAME] internal networks must pass through an access control point before the user can reach a login banner.
Is VPN good for remote employees?
The home networks of most remote employees lack the security provided by a large corporate network, making them sitting ducks for hackers. A VPN puts a strong hedge of protection around their connection, keeping the interactions they have with your internal network – from emails to confidential data access – secure.
What is the purpose of remote access policy?
Hence, the purpose of this policy is to define standards for connecting to the group’s network from any host. These standards are designed to minimize the potential exposure to the group from damages, which may result from unauthorized use of the group resources. Damages include the loss of sensitive or company confidential data, intellectual property, damage to public image, damage to critical group internal systems, etc.
What is the Organization Group policy?
This policy applies to all Organization Group employees, contractors and vendors with corporate owned computers or workstations used to connect to the Group’s network. This policy applies to remote access connections used to do work on behalf of the Group, including reading or sending email, viewing intranet web resources and network/system/application support.
Does IT Security recommend remote support?
IT Security does not recommend remote support services for such applications to reduce the Groups’ exposure to unnecessary outside threats. However, such application may be allowed remote support services on an ad-hoc basis for a limited time period and approved by the Organization IT Management.
Why you need a remote access policy
Access to IT and business resources -- data, databases, systems and networks -- must be protected from unauthorized and potentially damaging attacks. Securing access to company resources from employees working remotely ensures IT assets and employees are shielded from potential disruptions.
How to create a remote access security policy
Remote access security policies should be developed by a cross-functional team to address operational, legal, competitive and other issues associated with remote access to information resources. The team should coordinate with internal departments for input on their remote access requirements and with HR to ensure uniform compliance by employees.
Remote access security policy sample
A remote access security policy can be simple. In fact, a few paragraphs added to an existing cybersecurity policy may be sufficient. The policy language should define remote access security activities and how they build on existing security policies and procedures, noting the metrics discussed previously.
What is remote work policy?
A remote work policy — also known as a work from home policy or telecommuting policy — is a set of guidelines that outlines how and when it’s appropriate for employees to work outside the office. These policies often cover who is eligible to work remotely, communication expectations, time-tracking processes, data security rules, ...
What is the option 1 for remote employees?
[Option 1: If your business provides equipment] We will provide remote employees with [ list of equipment, tools and supplies — e.g., laptops, headsets, cellphones, paper, printers] that are essential to their job duties. Equipment supplied by [ Company Name] is to be used for business purposes only.
What are the benefits of remote work?
Remote work can [ list of benefits remote work will bring to your business — e.g., improve productivity, reduce office and parking space, reduce traffic congestion, enhance work/life balance, protect the health and safety of employees during COVID-19 ]. [Optional] This remote work policy is in effect due to COVID-19 and public health guidelines ...
What happens if you fail to fulfill work requirements while working remotely?
Failure to fulfill work requirements or adhere to policies and procedures while working remotely may result in
How many hours can a remote worker work?
For instance, some companies allow their remote employees to work eight hours within a certain window, such as between 7am and 7pm, or be reachable during specified “core hours” based on your business’s headquarters (e.g., 9am-11am CST Monday to Friday).
What are the ground rules for remote work?
Here are 11 ground rules, guidelines and expectations to consider including in your remote work policy: 1. Purpose and scope. Start by explaining why you created the policy and who it applies to.
Why is it important to have a work from home policy?
That’s why it’s important to create a work from home policy that sets expectations for your employees, keeps them on track while working from home and helps mitigate any potential legal problems. Here are 11 ground rules, guidelines and ...