Remote Access Trojan (RAT)
- Botnets. Botnets are networks of computers infected by a botnet agent that are under hidden control of a third party.
- Browser hijacker. Browser hijackers, or simply hijackers, are a type of malware created for the purpose of modifying...
- Distributed Denial of Service (DDOS). DDOS, or Distributed Denial of Service tools, are malicious...
- Rootkits.
What is a remote access trojan (RAT)?
Malware spotlight: What is a Remote Access Trojan (RAT)? A Remote Access Trojan (RAT) is a type of malware that allows covert surveillance, a backdoor for administrative control and unfettered and unauthorized remote access to a victim’s machine.
What is a remote access toolkit (rat)?
A RAT is a type of malware that’s very similar to legitimate remote access programs. The main difference, of course, is that RATs are installed on a computer without a user’s knowledge.
What happens when you enable remote access to your computer?
When remote access is enabled, authorized computers and servers can control everything that happens on your PC. They can open documents, download software, and even move the cursor around your screen in real time. A RAT is a type of malware that’s very similar to legitimate remote access programs.
What should I do if I find a remote access trojan?
If Remote Access Trojan programs are found on a system, it should be assumed that any personal information (which has been accessed on the infected machine) has been compromised. Users should immediately update all usernames and passwords from a clean computer, and notify the appropriate administrator of the system of the potential compromise.

Is remote access Trojan illegal?
Law enforcement officials say that simply possessing a remote-access tool isn't illegal. In fact, remote-access tools are often used for IT support purposes in corporate environments.
What are the main features of a remote access Trojan?
RAT (remote access Trojan)Monitoring user behavior through keyloggers or other spyware.Accessing confidential information, such as credit card and social security numbers.Activating a system's webcam and recording video.Taking screenshots.Distributing viruses and other malware.Formatting drives.More items...
How is RAT malware installed?
An attacker must convince the user to install a RAT either by downloading malicious software from the web or running an executable from a malicious email attachment or message. RATs can also be installed using macros in Microsoft Word or Excel documents.
What is RAT network?
A Radio Access Technology or (RAT) is the underlying physical connection method for a radio based communication network. Many modern mobile phones support several RATs in one device such as Bluetooth, Wi-Fi, and GSM, UMTS, LTE or 5G NR.
Is someone using my computer remotely?
Open your Task Manager or Activity Monitor. These utilities can help you determine what is currently running on your computer. Windows – Press Ctrl + Shift + Esc. Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
Which connection is most commonly used in rats?
RAT infections are typically carried out via spear phishing and social engineering attacks. Most are hidden inside heavily packed binaries that are dropped in the later stages of the malware's payload execution.
What is a logic bomb virus?
A logic bomb is a string of malicious code inserted intentionally into a program to harm a network when certain conditions are met.
What does a RAT do to your computer?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Is a backdoor malware?
A backdoor is a malware type that negates normal authentication procedures to access a system. As a result, remote access is granted to resources within an application, such as databases and file servers, giving perpetrators the ability to remotely issue system commands and update malware.
How do you know if you have RATs?
Under decking is an area rats often use to nest. Sheds - look for rat holes (entrances to burrows) around the edges of sheds and out buildings. Rats like to burrow next to solid structures like walls. Garages - check for gaps around door frames or holes gnawed at the bottom of wooden doors.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
What are the variants of remote access Trojan?
Common Remote Access TrojansSakula. Sakula is a seemingly benign software with a legitimate digital signature, yet it allows attackers complete remote administration capabilities over a machine. ... KjW0rm. ... Havex. ... Agent. ... Dark Comet. ... AlienSpy. ... Heseber BOT. ... Sub7.More items...
What type of Trojan is specifically designed to provide remote access to the systems it is installed on?
Backdoors introduced through Trojan horses are known as remote access Trojans (RATs). Typically, a RAT makes entries in the registry or configuration files of the operating system, so that it is initialized every time the system is booted.
What are remote administration tools?
A remote administration tool (RAT) is a software program that gives you the ability to control another device remotely. You then have access to the device's system as if you had physical access to the device itself.
What is Remote Access Malware?
Remote access malware (or sometimes referred to as remote access trojan) is a type of malware that gives attackers and online perpetrators unauthorized access to a private system or network. This RAT malware aims to steal confidential information and cause a major security breach.
How Dangerous is Remote Access Malware?
Unlike most malware programs, remote access malware can still pose security dangers to your system even after being removed. This malware has the ability to alter files, modify hard disks, and download harmful data. Other than those things, remote access malware can gain user passwords and codes through screen and keystroke captures.
How to Prevent Remote Access Malware?
Fortunately, there are a couple of ways for you to combat remote access malware. Although it is one of the hardest malware to fight and remove, there are still several security practices that you can implement to at least keep yourself safe from this malware. Here are them:
How many people were affected by POS malware in 2014?
In the last two years, POS malware has compromised 100 million payment cards and potentially affected up to one in three people in the U.S.
What is PCI DSS?
The PCI DSS is a multi-layered security framework that can correctly reduce merchant risk of compromise. The following best practices, if implemented correctly, will reduce the risk of attacks.
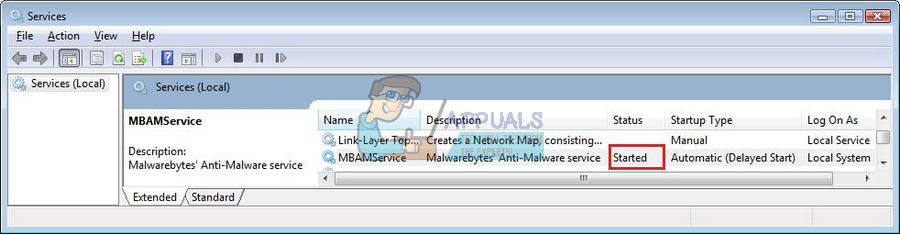
Why is anti-malware updated?
Antivirus or anti-malware programs are updated on a regular basis to detect against known malware. Maintaining an up-to-date anti-malware program that scans systems on a regular basis will prevent known POS malware or other malware from infecting systems.
What are the two types of authentication?
Two different forms of authentication should be implemented to access a remote access application. When configuring two-factor authentication, factors must contain two of three aspects: 1 Something only the user knows (e.g., a username and password) 2 Something only the user has (e.g., a cell phone or an RSA token) 3 Something the user is (e.g., a fingerprint)
What do merchants do with malware?
They can then configure systems to alert and report on suspicious activity, such as new files added to known directories where malware is installed or unauthorized access attempts.
What is a vulnerability scan?
Vulnerability scans are automated tests that passively test systems and networks to identify known weaknesses. These scans generate reports that provide specific information about weaknesses specific to the entities systems and networks. These reports allow entities to find and fix vulnerabilities in a timely manner.
How often do hackers scan the internet?
It is estimated that the average hacker could scan the entire internet for possible remote access vulnerabilities once every eight hours. This statistic is exactly why vulnerability scanning is crucial to merchant security.
What is remote access trojan?
Remote Access Trojans are programs that provide the capability to allow covert surveillance or the ability to gain unauthorized access to a victim PC. Remote Access Trojans often mimic similar behaviors of keylogger applications by allowing the automated collection of keystrokes, usernames, passwords, screenshots, browser history, emails, chat lots, etc. Remote Access Trojans differ from keyloggers in that they provide the capability for an attacker to gain unauthorized remote access to the victim machine via specially configured communication protocols which are set up upon initial infection of the victim computer. This backdoor into the victim machine can allow an attacker unfettered access, including the ability to monitor user behavior, change computer settings, browse and copy files, utilize the bandwidth (Internet connection) for possible criminal activity, access connected systems, and more.
Can you click on an unknown website?
As in all cases, never click email or website links from unknown locations or install software at the urging of unknown parties. Using a reputable antivirus and anti-malware solution will help to ensure Remote Access Trojans are unable to properly function, and will assist in mitigating any collection of data. Always lock public computers when not in use, and be wary of emails or telephone calls asking to install an application.
How to delete malware in Windows 10?
Open file location. Do no click on ‘End task’ before opening the file location. So, first click on the ‘open file location’ which will open the location of the suspected malware and then you can end that task. In the file location, you can delete the malware.
What is netstat command?
netstat: The netstat is a useful command for checking internet and network connections. -b attribute: displays the executable involved in creating each connection or listening port. -o attribute: displays the owning process id associated with each connection.
What is the protocol used to send a malware?
So, when a malware is running in the background, it must establish a connection to the outside internet world. They also use a protocol like TCP or UDP to establish the internet connection and send our private information outside. Another important factor is that every process is assigned a PID (Process ID) in Windows.
Can you delete malware from USB?
In the file location, you can delete the malware. If you are unable to delete the malware, you can follow our article — Remove Virus from USB Or Any Drive on Windows 10 Using CMD. Sometimes, it might also happen that the malware operates intermittently. In that case, we just cannot sit and wait for the malware to appear up.
What is botnet hacking?
Essentially, a botnet allows a hacker to utilize your computer resources for super nerdy (and often illegal) tasks, like DDOS attacks, Bitcoin mining, file hosting, and torrenting. Sometimes, this technique is utilized by hacker groups for the sake of cyber crime and cyber warfare.
What is a RAT in cyber security?
Maxim Apryatin/Shutterstock. In most cases, RATs are used like spyware. A money-hungry (or downright creepy) hacker can use a RAT to obtain keystrokes and files from an infected computer. These keystrokes and files could contain bank information, passwords, sensitive photos, or private conversations.
What is a RAT?
A RAT is a type of malware that’s very similar to legitimate remote access programs. The main difference, of course, is that RATs are installed on a computer without a user’s knowledge. Most legitimate remote access programs are made ...
What does remote access do on a PC?
When remote access is enabled, authorized computers and servers can control everything that happens on your PC. They can open documents, download software, and even move the cursor around your screen in real time.
Can a RAT be attached to a file?
Like most malware, RATs piggyback on legitimate-looking files. Hackers can attach a RAT to a document in an email, or within a large software package, like a video game. Advertisements and nefarious webpages can also contain RATs, but most browsers prevent automatic downloads from websites or notify you when a site is unsafe.
Can a hacker use a RAT?
Hackers can also control your computer remotely to perform embarrassing or illegal actions online in your name or use your home network as a proxy server to commit crimes anonymously. A hacker can also use a RAT to take control of a home network and create a botnet.
Is Kaspersky a RAT?
Kaspersky or Malwarebytes have an extensive, ever-expanding database of RATs, so you don’t have to worry about your anti-virus software being out of date or half baked. If you’ve run anti-virus, but you’re still paranoid that there’s a RAT on your PC, then you could always format your computer.
What is OSSEC in security?
OSSEC stands for Open Source HIDS Security . A HIDS is a Host Intrusion Detection System, which examines events on the computers in a network rather than trying to spot anomalies in the network traffic, which is what network intrusion detection systems do.
What is intrusion detection?
Intrusion detection systems are important tools for blocking software intrusion that can evade detection by antivirus software and firewall utilities. The SolarWinds Security Event Manager is a Host-based Intrusion Detection System. However, there is a section of the tool that works as a Network-based Intrusion Detection System. This is the Snort Log Analyzer. You can read more about Snort below, however, you should know here that it is a widely used packet sniffer. By employing Snort as a data collector to feed into the Snort Log Analyzer, you get both real-time and historic data analysis out of the Security Event Manager.
What is Solarwinds Event Manager?
SolarWinds Security Event Manager has hundreds of out-of-the-box correlation rules which can alert you to suspicious behaviors in real-time. You can also set up new rules thanks to the normalization of log data. The dashboard gives you a powerful command center for identifying potential network vulnerabilities.
How does Beast RAT work?
The Beast RAT attacks Windows systems from Windows 95 up to Windows 10. This uses the same client-server architecture that Back Orifice pioneered with the server part of the system being the malware that gets installed surreptitiously on the target computer. Once the server element is operational, the hacker can access the victim computer at will through the client program. The client connects to the target computer at port number 6666. The server is also able to open connections back to the client and that uses port number 9999. Beast was written in 2002 and is still widely in use.
What can a hacker do with a RAT?
A hacker with a RAT can command power stations, telephone networks, nuclear facilities, or gas pipelines. RATs not only represent a corporate network security risk, but they can also enable belligerent nations to cripple an enemy country.
How to get rid of a RAT?
Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system. RAT prevention systems are rare because the RAT software can only be identified once it is operating on your system.
What is a RAT?
RATs are tools that are usually used in a stealth type of hacker attack, which is called an Advanced Persistent Threat, or APT. This type of intrusion is not focused on damaging information or raiding computers quickly for data.
What is unauthorized software?
Unauthorized software is a common entrypoint for ransomware attacks. Monitoring software and integrations is very important, especially when workers are at home with others who may be installing software on their devices.
What is cybersecurity readiness?
Cybersecurity readiness is the ability to identify, prevent, and respond to cyber threats. Yet despite the daily headlines and warnings, organizations struggle to achieve cybersecurity readiness. Just look at the statistics: 78% of... READ MORE ».
What is the first step in mitigating risk throughout your attack surface?
Documenting policies, protocols, and authorized software is the first step in mitigating risk throughout your attack surface. From there, you can start to enforce changes that will improve security performance across your expanding digital ecosystem. 2. Unsecured networks.
Is social engineering easier than phishing?
Social engineering has a new dimension now that employees aren’t in the same physical space. It’s much easier to impersonate a colleague when they’re not sitting next to you, and in the current stressful environment some emotionally driven phishing emails are working better now than ever before.
