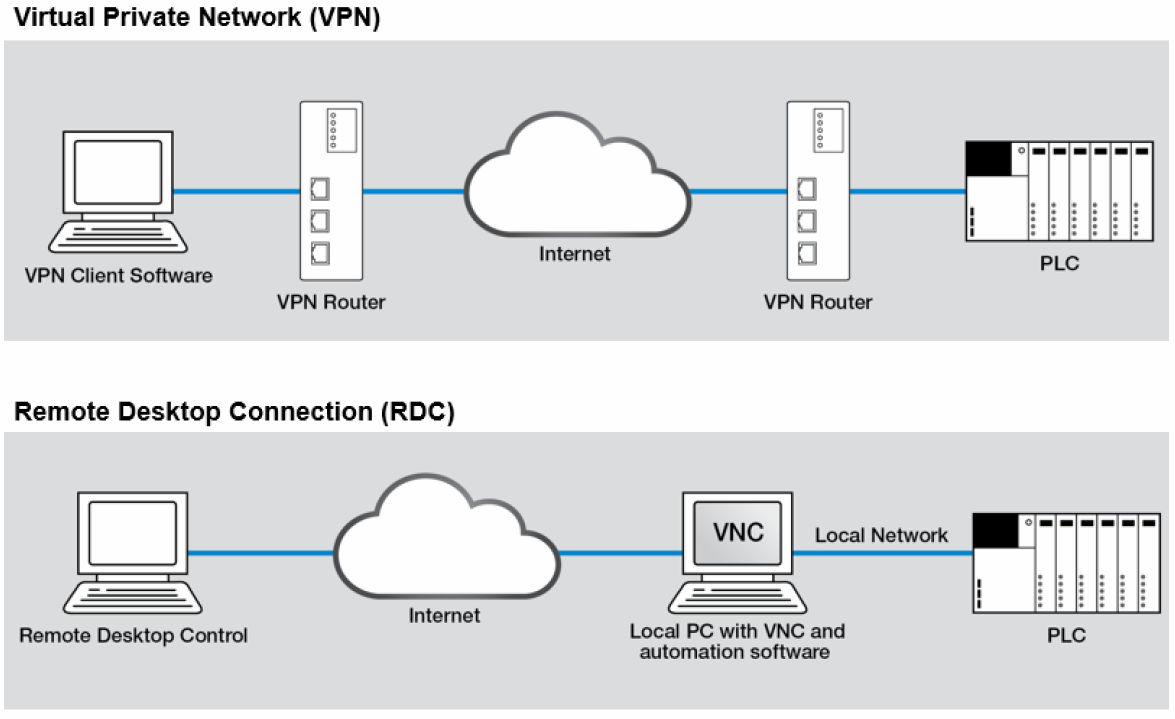
- A Virtual Private Network (VPN) enables secure remote access between distant network nodes. This secure data...
- Point-to-Point Tunneling Protocol (PPTP) is a Microsoft protocol used to encrypt data. Both client and the VPN...
- Layer 2 Tunneling Protocol (L2TP) is an encryption protocol that is vendor (Cisco, Juniper, etc.) independent. It is...
What are the best practices for securing remote access?
Best Practices for Securing Remote Access. RAS: The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network ... IPSec: IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect ...
What is remote access and how does it work?
Today, remote access is more commonly accomplished using: Software: Using a secure software solution like a VPN. Hardware: By connecting hosts through a hard-wired network interface or Wi-Fi network interface. Network: By connecting via the internet. Remote access VPNs connect individual users to private networks.
Is your remote access solution secure?
While a Virtual Private Network or VPN is one of the most sought-after remote access solutions at the moment, it can still pose a few security risks for your organization. A VPN Access can still be exposed to a bunch of security threats outside of a company’s network.
How does remote access VPN work?
With a remote access VPN, each user needs a VPN client capable of connecting to the private network's VPN server. When a user is connected to the network via a VPN client, the software encrypts the traffic before it delivers it over the internet.
What is remote assistant?
What is remote desktop connection?
What is remote access?
What are the different types of remote access methods?
Remote Access Control MethodsDirect (Physical) Line. The first direct remote access control that can be implemented is a direct line from a computer to the company's LAN. ... Virtual Private Network. Another method which is more common is establishing a VPN. ... Deploying Microsoft RDS.
Which method of remote access is the most secure?
Implement a Secure Connection for Remote Network AccessWired Connection: A wired connection is the most secure method for remote network access.Home Wi-Fi: The second most secure network connection is using a secured home Wi-Fi connection.More items...•
What are the two types of remote access servers?
Remote Access Methods1- Remote Access Server: It's one server in organization network that it is the destination of all remote access connections.2- Remote Access Client: All computers that remote connect to network, called remote access client or remote computer.More items...•
What is remote secure access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
What are the secure methods the remote users can use to connect to the internal network to perform file operations?
Most commonly, remote workers will use a remote access VPN client to connect to their organization's VPN gateway to gain access to its internal network, but not without authenticating first. Usually, there are two choices when using VPNs: IP Security (IPsec) or Secure Sockets Layer (SSL).
Which protocol for remote access is more secure and why?
POINT-TO-POINT TUNNELING PROTOCOL (PPTP) It's used to establish virtual connections across the internet via PPP and TCP/IP, enabling two networks to use the internet as their WAN link while retaining the security benefits of a private network. PPTP is a great option because it's simple and secure.
What two different types of encryption can be utilized with IPsec?
Each method is accompanied by a key, and these keys keep your data scrambled as it travels toward its destination. IPsec also uses two types of encryptions: symmetric and asymmetric. Symmetric encryption shares one key between users, whereas asymmetric encryption relies on both private and public keys.
What is the name of the Remote Access server?
Microsoft Remote Access Server (RAS) is the predecessor to Microsoft Routing and Remote Access Server (RRAS). RRAS is a Microsoft Windows Server feature that allows Microsoft Windows clients to remotely access a Microsoft Windows network.
What is the difference between RAS and VPN?
Information sent over a VPN is secure, it«s both authenticated and encrypted, while information sent via RAS lacks these security features. Although RAS served a purpose in providing LAN access to remote users, its time has clearly passed.
How do I make remote access secure?
Basic Security Tips for Remote DesktopUse strong passwords.Use Two-factor authentication.Update your software.Restrict access using firewalls.Enable Network Level Authentication.Limit users who can log in using Remote Desktop.
What are remote devices?
Remote Device means any device acceptable to us from time to time that provides for the capture of images from Items and for transmission through the clearing process.
What does SSH stand for?
Secure Socket ShellSSH, also known as Secure Shell or Secure Socket Shell, is a network protocol that gives users, particularly system administrators, a secure way to access a computer over an unsecured network.
What are the characteristics of various remote access security technologies?
Highly secure mobile computing - even in IPsec-hostile remote access environments. VPN tunnel without interrupting mobile computing sessions. Optimized network access control for remote access environments. Optimized network access control for remote access environments.
Why is remote authentication important?
MFA is important for remote workers for not only preventing unauthorized access, but in improving your organization's overall security posture. This is thanks to one of the great features of MFA: when an attempt is made to get into someone's account from an unauthorized device, the user will get a notification.
What is Microsoft protocol that allows a user to view and control the desktop of a remote computer?
Microsoft Remote Desktop Protocol (RDP)The Microsoft Remote Desktop Protocol (RDP) provides remote display and input capabilities over network connections for Windows-based applications running on a server. RDP is designed to support different types of network topologies and multiple LAN protocols.
How do I access network resources?
Press Windows Logo+R (or select Start, All Programs, Accessories, Run) to open the Run dialog box. Type the network address for a shared resource, and then click OK to open the resource in a folder window. In a program's Open or Save As dialog box, you can type a network address in the File Name text box.
What is remote access software?
A remote access software is a tool that allows you to access another computer from a remote location. From there, you can now access files, use apps, and even perform administrative tasks on the remote computer as if you’re in front of it.
Can a VPN be exposed to a security threat?
A VPN can still be exposed to a bunch of security threats outside of a company’s network. A report from Trustwave found that the majority of the data breaches it investigated in 2011 were associated with a VPN connection. One alternative option for a VPN is remote access software. A remote access software is a tool that allows you ...
Can remote desktop access restrict access to sensitive data?
Remote Desktop Access software also can restrict users to access sensitive and confidential data. You can also disable file transfer features on remote access software when there’s no reason for your employees to do so.
Is VPN a security risk?
While a Virtual Private Network or VPN is one of the most sought-after remote access solutions at the moment, it can still pose a few security risks for your organization. A VPN can still be exposed to a bunch of security threats outside of a company’s network.
What is remote access?
Remote access is the ability for an authorized person to access a computer or network from a geographical distance through a network connection.
How does remote access work?
Remote access is accomplished with a combination of software, hardware and network connectivity.
What are the types of remote access?
Traditionally, enterprises used modems and dial-up technologies to allow employees to connect to office networks via telephone networks connected to remote access servers. Devices connected to dial-up networks use analog modems to call assigned telephone numbers to make connections and send or receive messages.
What is remote access VPN?
The most basic form of VPN remote access is through a RAS. This type of VPN connection is also referred to as a Virtual Private Dial-up Network (VPDN) due to its early adoption on dial-up internet.
What is the line of defense for remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly.
Why is IPSec VPN important?
IPSec VPN connections are also important for an employee who needs widespread access to the company’s network. A word of warning: If you are using IPSec VPN for remote access, but you are not deploying Internet Key Exchange (IKE, certificates) as an authentication method, the connection will be vulnerable.
Why is IPSEC used?
This allows IPSec to protect data transmission in a variety of ways. IPSec is used to connect a remote user to an entire network. This gives the user access to all IP based applications. The VPN gateway is located at the perimeter of the network, and the firewall too is setup right at the gateway.
What is IPSEC protocol?
IPSec: IPSec is an IP packet authentication and encryption method. It uses cryptographic keys to protect data flows between hosts and security gateways. The unique feature of IPSec is that it operates at the Network Layer of the Open Systems Interconnection (OSI) protocol model.
Should a company use IPSEC VPN?
A company should go for IPSec VPN remote access if it has a strong networking department with the ability to configure each employee’s hardware device individually (installing client software, enforcing security policies etc.).
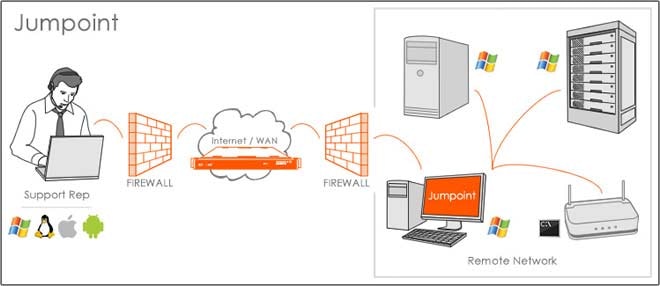
What is remote assistant?
The remote assistant can be considered a subset of the remote desktop. When you connect to another computer using the remote desktop, the current user of that computer is forced to sign-out. In other words, if an employee asks you for help with a problem and you use a remote desktop to connect to his computer, it is not possible for both of you to be able to view the desktop at the same time and do the necessary work. In terms of technical support, this is a huge problem. To solve this problem, remote assistant technology was introduced. In remote assistant, technical support person and an employee with a problem are able to connect to a computer at the same time.
What is remote desktop connection?
Remote Desktop Connection (RDC) is a Microsoft technology that allows a local computer to connect to and control a remote PC over a network or the Internet. The host computer can see and interact with the target computer through the target computer’s actual desktop interface—allowing the host user to see exactly what the target user sees. It is done through a Remote Desktop Service (RDS) or a terminal service. Microsoft Windows, Linux, and MacOS have the software available that allows for remote desktop access.
What is remote access?
In fact, Remote access is simply the ability to access a computer or network, at home or in an office, from a remote location. Remote access connection allows users to access a network or computer remotely via an internet connection or telecommunications. This post is dedicated to secure remote access.