Security
How to Implement an Effective Remote Access Policy | Smartsheet Now called distributed offices, remote work, telework, mobile work, smart work, and. A remote access policy statement, sometimes called a remote access control. have a standard policy in place - as work-life balance, productive and happy.
Eligibility
Small businesses are a prime target for hackers, particularly with many employees now working from home.
- Small business owners are still a target for hackers, largely because of their lack of cybersecurity.
- Phishing, brute-force attacks and ransomware are just some of the cybersecurity threats small business owners face.
- Remote work environments require small business owners to shift tactics in securing their networks.
Availability
What a successful remote work policy looks like
- Availability. Be clear in your remote work policy about your expectations surrounding your employees’ availability.
- Technology and equipment. Employees need the right tools to complete their work while telecommuting. ...
- Security. Companies must consider the security of their business data while permitting employees to work remotely.
- Legality and liability. ...
Responsiveness
Remote work challenges for teams
- Managing projects. Starting right at the top, the biggest challenge with remote working is managing projects when your team is spread out across multiple locations.
- Remote collaboration. The most common challenge remote teams report in studies is collaborating from different locations. ...
- Tracking tasks and productivity. ...
Productivity measurements
How to implement an effective remote access policy?
How to secure your remote access?
How to implement a successful remote work policy?
What are potential risks associated with remote access?

What should be in a remote access policy?
A remote access policy should cover everything—from the types of users who can be given network access from outside the office to device types that can be used when connecting to the network. Once written, employees must sign a remote access policy acceptance form.
What are the four basic elements of a remote access policy?
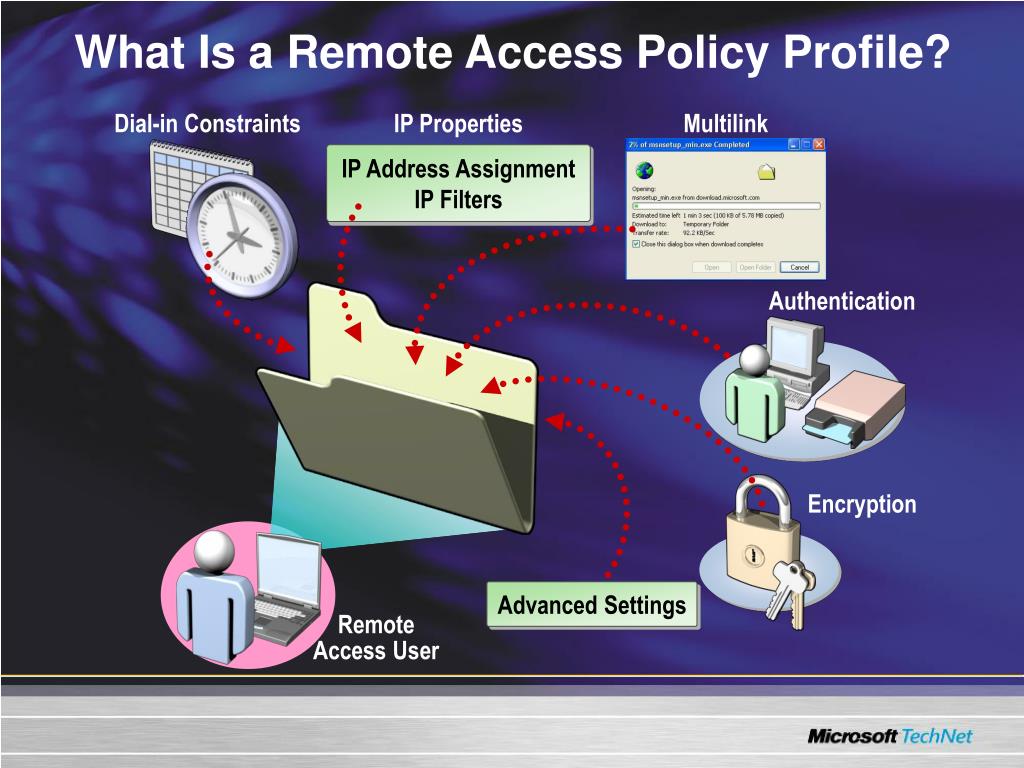
Remote access policies consist of the following elements: conditions, permissions, and profiles. We'll discuss each of these elements in turn, and list how each can be used to control remote access attempts by your network clients.
What is the importance of remote access policy?
A remote access policy is vital to ensure that your organization can maintain its cybersecurity protocols even with all the uncertainty that remote access brings: unknown users (you can't see the person, after all), using potentially unknown devices on unknown networks, to access your corporate data center and all the ...
What is a access policy?
n. Principles or procedures that control the conditions under which individuals have permission and ability to consult a repository's holdings.
What is a VPN policy?
A VPN security policy is a policy that defines. just about everything that anyone would need to know about your VPN. It defines. things like who can use the VPN, what they can use it for, and what it is that. keeps them from using improperly or maliciously.
What are the five elements of a remote access security readiness review?
The review examined cybersecurity at the governance layer and identified five critical pillars key to cybersecurity readiness: culture, people, structure, processes, and resources.
What are some benefits of remote access?
4 Advantages of Remote AccessSuccessful Troubleshooting from Remote Locations. ... Streamline Remote Work for Employees. ... Remote Access Makes Collaboration Easy. ... Logs of All Activity Promote Network Security.
Is IT safe to allow remote access?
Remote access solutions could leave you vulnerable. If you don't have proper security solutions in place, remote connections could act as a gateway for cybercriminals to access your devices and data. Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular.
Is remote access legal?
(a) Remote access generally permitted A person may have remote access to electronic records in actions or proceedings in which that person is a party.
What are the three types of access control?
Three main types of access control systems are: Discretionary Access Control (DAC), Role Based Access Control (RBAC), and Mandatory Access Control (MAC).
What constraints are available for use in a remote access policy?
Once a remote access policy has authorized a connection, it can also set connection restrictions (called constraints) based on the following: Encryption strength. Idle timeout. IP packet filters.
What is a network access policy?
Network policies are sets of conditions, constraints, and settings that allow you to designate who is authorized to connect to the network and the circumstances under which they can or cannot connect.
What security best practices are for connecting to remote systems?
7 Best Practices For Securing Remote Access for EmployeesDevelop a Cybersecurity Policy For Remote Workers. ... Choose a Remote Access Software. ... Use Encryption. ... Implement a Password Management Software. ... Apply Two-factor Authentication. ... Employ the Principle of Least Privilege. ... Create Employee Cybersecurity Training.
What is the remote access domain?
... is the domain in which a mobile user can access the local network remotely, usually through a VPN (Figure 7). ...
What is remote access?
Remote access is any connection made to an organization's internal network and systems from an external source by a device or host. Remote locations can be almost anywhere in the world, from the employee’s home to an off-site office, hotels, transportation hubs, and cafes.
What devices do remote workers use?
The numerous types of mobile devices and the different ways to connect pose challenges for the IT department. Devices can include cell phones, tablets, laptops, and any other device a remote worker relies on to conduct business.
What is telecommuting?
“Telecommuting,” a term coined in the 1970s, has experienced explosive growth in today’s era of mobile connectivity. Now called distributed offices, remote work, telework, mobile work, smart work, and work shifting, many people are finding flexibility and increased productivity conducting business away from a centralized office environment. Researchers have long studied the benefits of remote work - from the successes that remote work had on traffic reduction during the 1984 Los Angeles Olympics to the 2016 findings by a Gallup survey on the increased hours for remote work.
What are the risks of using proprietary information?
The hazards to sensitive or proprietary information through unauthorized or inappropriate use can lead to compliance problems, from statutes such as those found in the Health Insurance Portability and Accountability Act (HIPAA) or Payment Card Industry Data Security Standards (PCI DSS).
Is remote work available?
While remote work is not available to or appropriate for everyone, non-self-employed work at home opportunities have grown by 115 percent since 2005 - especially for non-union, college educated, and high wage workers, according to Global Workplace Analytics .
Is remote access feasible?
There are plenty of advantages to remote access, but there are also instances where remote access is simply not feasible. For example: Organizations with strict, government access restrictions due to sensitive information. Retail and food-service workers. Workers who lack discipline outside of the office.
What is remote access policy?
Remote access policies are an ordered set of rules that define how connections are either authorized or rejected. For each rule, there are one or more conditions, a set of profile settings, and a remote access permission setting. If a connection is authorized, the remote access policy profile specifies a set of connection restrictions. The dial-in properties of the user account also provide a set of restrictions. Where applicable, user account connection restrictions override the remote access policy profile connection restrictions.
How to verify remote access server?
1. Either use the Rqc.exe notification component or create a notification component that provides verification to the remote access server that the remote access client computer complies with network policy requirements. 2. Create a validation script that authorizes the client configuration.
How to enable EAP authentication?
Follow these steps to enable EAP authentication:#N#1.#N#Select Start | Administrative Tools | Internet Authentication Service.#N#2.#N#The IAS management console is displayed. Click to highlight Remote Access Policies in the left column.#N#3.#N#In the right column, select Connections to Microsoft Routing and Remote Access Server .#N#4.#N#Select Action | Properties from the menu, or right-click and select Properties from the context menu. #N#5.#N#The Properties dialog box is displayed. Click the Edit Profile button .#N#6.#N#The Edit Dial-in Profile dialog box is displayed. Select the Authentication tab.#N#7.#N#The authentication methods supported by IAS are displayed, as shown in Figure 5.14. You can enable or disable the non-EAP authentication methods here. You can also change the order in which the selected EAP types are negotiated by moving them up or down in the list, using the Move Up and Move Down buttons.#N#Sign in to download full-size image#N#Figure 5.14. Authentication Methods#N#8.#N#Click the EAP Methods button. A list of the currently enabled EAP types is displayed.#N#9.#N#Click Add and select MD5-Challenge from the list.#N#10.#N#Click OK, then click OK in the EAP types list.#N#11.#N#Click OK to exit the Edit Profile dialog box.#N#12.#N#Click OK to exit the Properties dialog box.
How to delete VPN access policy?
Right-click on Connections to other access servers, and click Delete. Repeat with Connections to Microsoft Routing and Remote Access server. 3. Double-click on the VPN Access Policy in the right pane of the console.
What is PPP protocol?
The official implementation, as used by Microsoft, comes from RFP 1990. Capabilities were added and subsequent modifications to the standard were made leading up to PPP as it exists today. In 1994, a documented standard was proposed for “The PPP Multilink Protocol” in RFC 1717. At the time, other proposals existed to combine streams of data at the bit level (basically a hardware solution). This proposal described a software-based solution for the need to combine multiple streams of data into one. This solution was well-suited to the twin bearer channels of ISDN (2B+D).
Does a web proxy send user credentials to ISA 2004?
The Web Proxy client is able to send user credentials to the ISA 2004 firewall computer when required. In contrast to the Firewall client, which always sends user credentials to the ISA 2004 firewall, the Web Proxy client only sends credentials when asked to provide them. This improves performance, as authentication is only performed when required.
Can you configure remote access policies?
You can also configure one or more Remote Access Policies for precise control of which users can reach the network through remote access. Whether a user is affected by policies depends on the setting you choose in the Dial-in tab of the user’s Properties dialog box:
What is remote access?
Remote access refers to the process of connecting to internal resources from an external source (home, hotel, district, or other public area). The ability to securely and reliably connect to business resources from a remote location increases productivity.
What is LEP password policy?
All user passwords shall be strong and follow guidelines and procedures in the [LEP] Access Control and Password Policy. Staff shall ensure that devices used for work purposes are not shared in a multi-user capacity, violate AUP conditions, or used in any inappropriate activity.
What is remote access in a company name?
Remote access is defined as any connection to [COMPANY NAME]’s internal network from a location outside of any affiliated company offices.
How long do remote users have to log in?
Remote access must be logged in a central database and kept for a period of at least 30 days. Access logs must be reviewed regularly.
What is the purpose of the Company Name policy?
The intent of this policy is to establish guidelines specifically pertaining to remote access to [COMPANY NAME]’s internal network. Preventing unauthorized access to company data from insecure networks is of utmost importance to [COMPANY NAME]. This policy is designed to ensure remote and/or traveling employees have the ability to securely connect to the corporate network without fear of threat and to provide the Company with an additional means of monitoring and controlling access to the internal network.
Is multifactor authentication required for VPN?
And to make it even stronger, we recommend multi-factor authentication as a requirement for VPN access. Restricted use. Remote access privileges shouldn’t be given out in the office like candy, but rather on an as-needed basis.
Do authorized users share login credentials?
Authorized users must protect their login credentials and must not share them with anyone for any reason. All inbound connections to [COMPANY NAME] internal networks must pass through an access control point before the user can reach a login banner.
Is VPN good for remote employees?
The home networks of most remote employees lack the security provided by a large corporate network, making them sitting ducks for hackers. A VPN puts a strong hedge of protection around their connection, keeping the interactions they have with your internal network – from emails to confidential data access – secure.
How to set up a remote access policy?
Here’s a quick checklist to keep in mind as you work on your own remote access policy: 1 Define what a secure password is, how often it should be changed, and how the remote user should protect it. 2 Define what a secure connection is and who’s responsible for providing it. 3 Define what types of hardware a remote user may connect to the company network. 4 Establish a schedule and procedure for software updates. 5 Divide users into subgroups depending on the access each group needs. 6 Monitor and make sure remote users comply with guidelines. 7 Spell out the level of disciplinary action that may be taken if established guidelines are violated.
Why is remote access important?
A remote access policy is important to assure that your organization can maintain its cybersecurity even with all the uncertainty that remote access brings: unknown users (you can’t see the person, after all), using potentially unknown devices, on unknown networks, to access your corporate data center and all the information within .
What is a strict access protocol?
This means that it is less likely for documents to be accessed by third parties or unauthorized personnel. This is a strict access protocol that will ensure that company data is well secured.
How does advanced technology make the road safer?
Advanced technology is helping make the roads safer for drivers Being safe while driving on the road is everyone’s goal. Thanks to technological advancements, you can eliminate your risk of... Read More
Is it bad to give access to third party vendors?
Giving access to third-party vendors is a bad idea. Most recent hacks have come through allowing third party access to sensitive information. Assessing every one of them is very important. Create access restriction policies where they can only access the documents that they are supposed to and nothing more. Don’t be too trusting. Follow up to see what they are accessing and include regular security updates.
What is remote work policy?
A remote work policy — also known as a work from home policy or telecommuting policy — is a set of guidelines that outlines how and when it’s appropriate for employees to work outside the office. These policies often cover who is eligible to work remotely, communication expectations, time-tracking processes, data security rules, ...
What is the option 1 for remote employees?
[Option 1: If your business provides equipment] We will provide remote employees with [ list of equipment, tools and supplies — e.g., laptops, headsets, cellphones, paper, printers] that are essential to their job duties. Equipment supplied by [ Company Name] is to be used for business purposes only.
What are the benefits of remote work?
Remote work can [ list of benefits remote work will bring to your business — e.g., improve productivity, reduce office and parking space, reduce traffic congestion, enhance work/life balance, protect the health and safety of employees during COVID-19 ]. [Optional] This remote work policy is in effect due to COVID-19 and public health guidelines ...
What happens if you fail to fulfill work requirements while working remotely?
Failure to fulfill work requirements or adhere to policies and procedures while working remotely may result in
How many hours can a remote worker work?
For instance, some companies allow their remote employees to work eight hours within a certain window, such as between 7am and 7pm, or be reachable during specified “core hours” based on your business’s headquarters (e.g., 9am-11am CST Monday to Friday).
What are the ground rules for remote work?
Here are 11 ground rules, guidelines and expectations to consider including in your remote work policy: 1. Purpose and scope. Start by explaining why you created the policy and who it applies to.
Why is it important to have a work from home policy?
That’s why it’s important to create a work from home policy that sets expectations for your employees, keeps them on track while working from home and helps mitigate any potential legal problems. Here are 11 ground rules, guidelines and ...
