
What is remote access trojan and how it work?
- Checking client conduct through keyloggers or other spyware.
- Getting to private data, for example, Mastercard and government backed retirement numbers.
- Enacting a framework's webcam and recording video.
- Taking screen captures.
- Appropriating infections and other malware.
- Designing drives.
- Erasing, downloading or adjusting documents and record frameworks.
How to create remote access trojan?
Remote Access Trojan Examples
- Back Orifice. Back Orifice (BO) rootkit is one of the best-known examples of a RAT. ...
- Sakula. Sakula, also known as Sakurel and VIPER, is another remote access trojan that first surfaced in November 2012.
- Sub7. Sub7, also known as SubSeven or Sub7Server, is a RAT botnet. ...
- PoisonIvy. ...
- DarkComet. ...
How to create a trojan (RAT)?
how to create Remote Administration Tool (RAT)
- Remote Access Tool (RAT)
- Proxy
- File Sending Trojan
- Security Disable rs
- Denial Of Service (DOS)
- File Sending Trojans (FTP Trojan)
- Destructive Trojans
What is a remote access trojan?
- Functions of Remote Access Trojan : It can be used to monitor the user by using some spyware or other key-logger. It can be used to activate the webcam.
- Prevention of the Remote Access Trojan : The anti-virus should always be updated. ...
- Advantage of Remote Access Trojans : It can be used to capture screenshots. ...
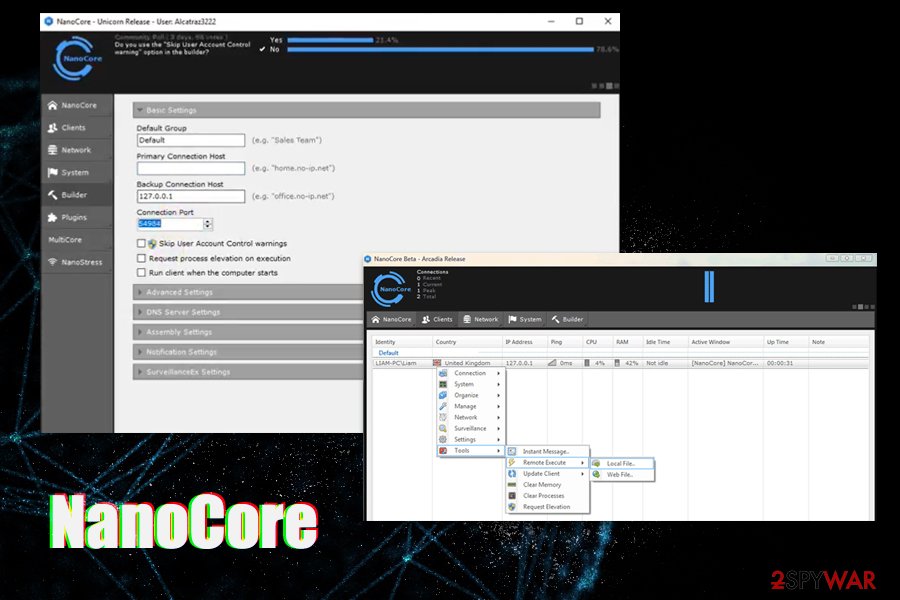
What is the best remote access Trojan?
10 Best Remote Access Software (Remote Control Software) In 2022Comparison of Top Remote Access Tools.#1) NinjaOne (Formerly NinjaRMM)#2) SolarWinds Dameware Remote Support.#3) Atera.#4) Supremo.#5) ManageEngine Remote Access Plus.#6) RemotePC.#7) TeamViewer.More items...•
Are remote access Trojans illegal?
Law enforcement officials say that simply possessing a remote-access tool isn't illegal. In fact, remote-access tools are often used for IT support purposes in corporate environments.
Is remote access Trojan a malware?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Can Norton detect RATs?
Antivirus software like Bitdefender, Kaspersky, Webroot, or Norton, can detect RATs and other types of malware if they infect your devices.
Is TeamViewer a RAT?
The JS script then launches the malware, which installs a version of TeamViewer, a remote administration tool (RAT), modified by the attackers. As in earlier attacks, the attackers use a malicious DLL library to hide the graphical user interface in order to control the infected system without the user's knowledge.
How is RAT malware installed?
RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment. Once the host system is compromised, the intruder may use it to distribute RATs to other vulnerable computers and establish a botnet.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
Is someone using my computer remotely?
Open your Task Manager or Activity Monitor. These utilities can help you determine what is currently running on your computer. Windows – Press Ctrl + Shift + Esc. Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
Can you get a RAT on your phone?
RAT infected Android devices can be remotely zombified by the perpetrator, allowing virtually unlimited access to photos, data and messages on the device. The Dendroid RAT provides full access to infected devices' camera and microphone, and can place calls or listen in on a user's phone conversations or text messages.
Can Trojan hide from antivirus?
Rootkit technologies – that are generally employed by Trojan viruses – can intercept and substitute system functions, in order to make the infected file invisible to the operating system and antivirus programs. Sometimes even the registry branches – where the Trojan is registered – and other system files are hidden.
Can antivirus detect Trojan?
An effective antivirus program searches for valid trust and app behavior, as well as trojan signatures in files in order to detect, isolate and then promptly remove them.
Can Norton remove a Trojan?
Resolution. Norton Antivirus detects and removes Trojan horses. Via LiveUpdate, administrators can download to a computer the latest virus definitions, which contain information that the scan engine needs to find existing and emerging threats on a system.
Is making a computer virus illegal?
No. It is not against the law or a crime to make a computer virus, Trojan, or malware. However, if that virus spreads to other computers intentionally or by mistake, you've violated the law, and you could be held liable for any damages it causes.
Is it illegal to sell malware?
If you sell software without disclosing to the customer that the software contains malware or a crypter then you are exposing yourself to a lawsuit for products liability, invasion of privacy, fraud and misrepresentation, the cost of damages, and possibly criminal liability.
Can Windows Defender detect Trojans?
Although, Windows Defender is not capable of handling all kinds of viruses, malware, trojan, and other security threats. You can trust it for basic Firewall protection, but not beyond based on the antimalware capabilities it offers.
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
What is remote access trojan?
Remote Access Trojans are programs that provide the capability to allow covert surveillance or the ability to gain unauthorized access to a victim PC. Remote Access Trojans often mimic similar behaviors of keylogger applications by allowing the automated collection of keystrokes, usernames, passwords, screenshots, browser history, emails, chat lots, etc. Remote Access Trojans differ from keyloggers in that they provide the capability for an attacker to gain unauthorized remote access to the victim machine via specially configured communication protocols which are set up upon initial infection of the victim computer. This backdoor into the victim machine can allow an attacker unfettered access, including the ability to monitor user behavior, change computer settings, browse and copy files, utilize the bandwidth (Internet connection) for possible criminal activity, access connected systems, and more.
How can remote access Trojans be installed?
Specially crafted email attachments, web-links, download packages, or .torrent files could be used as a mechanism for installation of the software. Targeted attacks by a motivated attacker may deceive desired targets into installing such software via social engineering tactics, or even via temporary physical access of the desired computer.
What is botnet in computer?
Botnets are networks of computers infected by a botnet agent that are under hidden control of a third party. They are used to execute various commands ordered by the attacker. Most common uses of botnets are criminal operations that require distributed resources, such as DDoS attacks on selected targets, spam campaigns, and performing click fraud. Often, the botnet agent is ordered to download and install additional payloads or to steal data from the local computer.
What is browser hijacker?
Browser hijackers, or simply hijackers, are a type of malware created for the purpose of modifying Internet browser settings without the user’s knowledge or consent. Typically, hijackers change the homepage and default search settings. However, some are known to inject advertisements—thus, they are qualified to be called adware, automatically redirecting users to potentially malicious destinations when they visit certain sites, and sometimes making drastic changes to the affected system. Some hijackers also contain keyloggers, which are capable of recording user keystrokes to gather potentially valuable information they enter into websites, such as account credentials.
What is a rogue scanner?
Rogue scanners, also known as fake scanners, fake AV, or rogueware, are pieces of code injected into legitimate sites or housed in fake sites. Their social engineering tactic normally involve displaying fictitious security scan results, threat notices, and other deceptive tactics in an effort to manipulate users into purchasing fake security software or licenses in order to remove potential threats that have supposedly infected their systems. Their warnings were deliberately crafted to closely resemble interfaces of legitimate AV or anti-malware software, further increasing the likelihood that users who see them will fall for the ploy. These malware can target and affect PCs and Mac systems alike. In 2011, known names in the security industry have noted the dramatic decline of rogue scanners, both in detection of new variants and search engine results for their solutions.
What are the different types of POS malware?
POS malware may come in three types: keyloggers, memory dumpers, and network sniffers.
What is POS malware?
Point-of-sale (POS) malware is software specifically created to steal customer data, particularly from electronic payment cards like debit and credit cards and from POS machines in retail stores. It does this by scraping the temporarily unencrypted card data from the POS’s memory (RAM), writing it to a text file, and then either sending it to an off-site server at a later date or retrieving it remotely. It is believed that criminals behind the proliferation of this type of malware are mainly after data they can sell, not for their own personal use. Although deemed as less sophisticated than your average PC banking Trojan, POS malware can still greatly affect not just card users but also merchants that unknowingly use affected terminals, as they may find themselves caught in a legal mess that could damage their reputation.
What is remote access trojan?
Like most other forms of malware, Remote Access Trojans are often attached to files appearing to be legitimate, like emails or software bundles. However, what makes Remote Access Trojans particularly insidious is they can often mimic above-board remote access programs.
What happens if you install remote access Trojans?
If hackers manage to install Remote Access Trojans in important infrastructural areas—such as power stations, traffic control systems, or telephone networks—they can wreak havoc across neighborhoods, cities, and even entire nations.
What Is RAT Software?
One malicious example of remote access technology is a Remote Access Trojan (RAT), a form of malware allowing a hacker to control your device remotely. Once a RAT program is connected to your computer, the hacker can examine the local files, acquire login credentials and other personal information, or use the connection to download viruses you could unwittingly spread along to others.
How does Snort intrusion detection work?
The intrusion detection mode operates by applying threat intelligence policies to the data it collects, and Snort has predefined rules available on their website, where you can also download policies generated by the Snort user community. You can also create your own policies or tweak the ones Snort provides. These include both anomaly- and signature-based policies, making the application’s scope fairly broad and inclusive. Snort’s base policies can flag several potential security threats, including OS fingerprinting, SMB probes, and stealth port scanning.
What is the best way to detect malware?
The best option, especially for larger organizations, is to employ an intrusion detection system, which can be host-based or network-based. Host-based intrusion detection systems (HIDSs), which are installed on a specific device, monitor log files and application data for signs of malicious activity; network-based intrusion detection systems (NIDSs), on the other hand, track network traffic in real time, on the lookout for suspicious behavior. When used together, HIDSs and NIDSs create a security information and event management (SIEM) system. SIEM is an incredibly beneficial part of a strong security regimen and can help to block software intrusions which have slipped past firewalls, antivirus software, and other security countermeasures.
What was the Russian attack on Georgia?
An example of this occurred in 2008, when Russia used a coordinated campaign of physical and cyber warfare to seize territory from the neighboring Republic of Georgia. The Russian government did this using distributed denial-of-service (DDoS) attacks which cut off internet coverage across Georgia, combined with APTs and RATs allowing the government to both collect intelligence about and disrupt Georgian military operations and hardware. News agencies across Georgia were also targeted, many of which had their websites either taken down or radically altered.
How do remote access Trojans evade live data analysis?
One way in which Remote Access Trojans can evade the live data analysis NIDSs provide is by dividing the command messaging sent through the malware across multiple data packets. NIDSs like Zeek, which focus more on application layers, are better able to detect split command messaging by running analyses across multiple data packets. This is one advantage Zeek has over Snort.
How to get rid of a RAT?
Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system. RAT prevention systems are rare because the RAT software can only be identified once it is operating on your system.
What can a hacker do with a RAT?
A hacker with a RAT can command power stations, telephone networks, nuclear facilities, or gas pipelines. RATs not only represent a corporate network security risk, but they can also enable belligerent nations to cripple an enemy country.
What is intrusion detection?
Intrusion detection systems are important tools for blocking software intrusion that can evade detection by antivirus software and firewall utilities. The SolarWinds Security Event Manager is a Host-based Intrusion Detection System. However, there is a section of the tool that works as a Network-based Intrusion Detection System. This is the Snort Log Analyzer. You can read more about Snort below, however, you should know here that it is a widely used packet sniffer. By employing Snort as a data collector to feed into the Snort Log Analyzer, you get both real-time and historic data analysis out of the Security Event Manager.
How does a RAT toolkit work?
Other elements propagate the RAT by sending out links to infected web pages. These are sent to the social media contacts of an infected user.
How does Beast RAT work?
The Beast RAT attacks Windows systems from Windows 95 up to Windows 10. This uses the same client-server architecture that Back Orifice pioneered with the server part of the system being the malware that gets installed surreptitiously on the target computer. Once the server element is operational, the hacker can access the victim computer at will through the client program. The client connects to the target computer at port number 6666. The server is also able to open connections back to the client and that uses port number 9999. Beast was written in 2002 and is still widely in use.
Why do companies use RATs?
RATs can also be used to reroute traffic through your company network to mask illegal activities. Some hacker groups, predominantly in China, have even created a hacker network that runs through the corporate networks of the world and they rent out access to this cybercrime highway to other hackers.
Can antivirus be used to get rid of a RAT?
Antivirus systems don’t do very well against RATs. Often the infection of a computer or network goes undetected for years. The obfuscation methods used by parallel programs to cloak the RAT procedures make them very difficult to spot. Persistence modules that use rootkit techniques mean that RATs are very difficult to get rid of. Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system.
