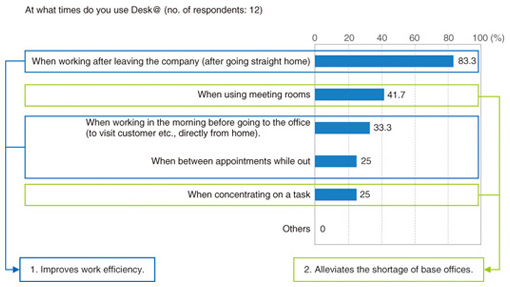
Types of Remote Access: Benefits & Disadvantages
- VPNs: Virtual Private Networks. When employees need to remotely access their company files, a virtual private network (VPN) is often the tool of choice.
- Desktop sharing. Desktop sharing is another way organizations can provide remote access to users. ...
- PAM: Privileged Access Management. To go beyond VPNs and desktop sharing, you need an alternative that can manage identities closer than mere IAM technologies such as Active Directory.
- VPAM: Vendor Privileged Access Management. Many organizations need to provide privileged accounts to two types of users: internal users (employees) and external users (technology vendors and contractors).
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...
How to setup remote access?
Once installed, you can now connect to remote endpoints by following the steps below:
- The software needs to be downloaded on both the local and remote computers.
- Open the software on both the local and remote computers.
- Write down the ITarian ID number and password of the remote computer.
- Click “Start Connection.”
- Enter the ID number and password of the remote computer.
- Click “Connect.”
How to properly secure remote access?
- Windows or Mac login when connecting remotely
- Request permission to connect to the user’s computer
- Automatically blank the remote screen when connected
- Automatically lock remote computer when disconnected
- Lock the remote computer’s keyboard and mouse while in session
- Lock the streamer settings using Splashtop admin credentials
Does Someone have remote access to my computer?
You can detect remote access on your computer by identifying the software programs currently in use and recognizing any abnormalities. If you have ever wondered "Is someone else controlling my computer," you are not alone.

What are the two types of remote access servers?
Remote Access Methods1- Remote Access Server: It's one server in organization network that it is the destination of all remote access connections.2- Remote Access Client: All computers that remote connect to network, called remote access client or remote computer.More items...•
What are three examples of remote access locations?
What Is Remote Access?Queens College.Harvard University Extension School.
What is the most common form of remote access?
remote access virtual private network (VPN)One common method of providing remote access is via a remote access virtual private network (VPN) connection. A VPN creates a safe and encrypted connection over a less secure network, such as the internet.
What is a remote access system?
Remote computer access is the ability to access another computer or network that isn't in your physical presence. Remote computer access allows an employee to access a computer desktop and its files from a remote location. This helps enable an employee who is working from home, for instance, to work effectively.
What is remote GUI?
Remote GUI allows you to access your router's online settings, also known as the graphical user interface (GUI), through a WAN connection. To access your modem remotely, you will enter https:// followed by the modem IP in the URL field of a browser. 1.
What are the benefits of remote access?
Here, we discuss the most common flexible working benefits that can be supported by your remote access strategy.A more productive workforce. ... Better talent acquisition. ... IT support from anywhere. ... Improved security for remote workers. ... Lower overhead cost. ... Business continuity planning.
Why is remote access important?
With remote access, employees can safely work from any device, platform, or network at their home office or abroad. Remote desktop functions allow them to remotely access important files and share their screen for meetings and troubleshooting.
What are the examples of remote assistance?
Examples include file transfer, remote print, chat, session recording, screen sharing, and more. By being able to remotely access a device to provide support, IT support teams, help desks, and managed service providers can resolve support tickets quicker.
What is remote login explain with example?
Remote Login is a process in which user can login into remote site i.e. computer and use services that are available on the remote computer. With the help of remote login a user is able to understand result of transferring result of processing from the remote computer to the local computer. Figure – Remote login.
What is a remote access code on phone?
A remote access code lessens the risk of threats that may disrupt the security of any private device, whether from a household level or from an enterprise point of view. This prevents unwanted threats from an unknown location that may hack and steal any sensitive data or information stored in a particular device.
What are the two types of users that need privileged accounts?
Many organizations need to provide privileged accounts to two types of users: internal users (employees) and external users (technology vendors and contractors). However, organizations that use vendors or contractors must protect themselves against potential threats from these sources.
What are some applications that can be shared on desktop?
There are many applications made possible by desktop sharing including remote support, webinars, and online conferences with audio and visual content (presentation sharing), and real-time global collaboration on projects.
Can anyone log into a desktop sharing tool?
Anyone, anywhere, can log into a desktop sharing tool if they have the credentials, meaning they have access to the whole network as if they are in the building. During a remote support session, if an employee surrenders control of their machine to a remote rep whose account has been compromised, your company’s internal sensitive files could become visible to bad actors and used for nefarious purposes.
Is VPN good for remote access?
VPNs may be good for internal employees, but are not optimal for third-party vendors. Desktop sharing tools may be useful for desktop support and helpdesk, but are not good for complex enterprise remote support. PAM provides improvements over VPN and desktop sharing, but there is only one solution that combines the best of all these types of remote access technologies into one and is purpose-built for vendors and doesn’t include any of the drawbacks: VPAM.
Long-term Remote Access Could Be the Norm for Some Time
Some knowledge workers are trickling back to their actual offices, but many more are still at home and will be for some time. Global Workplace Analytics estimates that 25-30% of the workforce will still be working from home multiple days a week by the end of 2021.
SASE Provides a Simpler, More Secure, Easily Scalable Solution
Cato’s Secure Access Service Edge (or SASE) platform provides a great alternative to VPN for remote access by many simultaneous workers. The platform offers scalable access, optimized connectivity, and integrated threat prevention that are needed to support continuous large-scale remote access.
SASE Supports WFH in the Short-term and Long-term
While some workers are venturing back to their offices, many more are still working from home—and may work from home permanently. The Cato SASE platform is the ideal way to give them access to their usual network environment without forcing them to go through insecure and inconvenient VPNs.
What are the Types of Remote Access?
In the past, remote access was possible by hardwiring to a telephone network. Analog modems and dial-up technology allowed two different devices to interact with one another by calling assigned phone numbers.rThis has changed significantly with broadband technology.Today, remote access is possible via:
What is remote access software?
Remote access software enables users to connect to computers, servers, or networks remotely. There are a few ways to use it:
What is VPN for branch offices?
VPN itself was specifically developed for remote employee access and interconnectivity between branch offices. It provides a way to securely and remotely access resources on company servers with verified login credentials. Remote access works by utilizing software, hardware, and network configurations. .
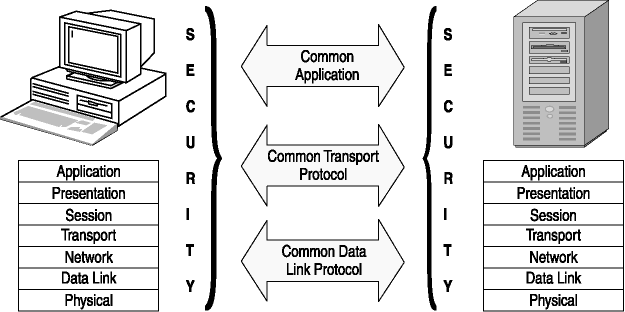
Why do we need remote access protocol?
It also helps keep your server secure and protected against hacks and leaks. There are several protocols for doing this:
How does remote access work?
Remote access works by utilizing software, hardware, and network configurations. . Despite the recent uptick in trend, this isn’t a new concept. In fact, it was even possible to access remote files before the advent of the internet.
Why is it important to shift to remote work?
The shift towards remote work benefits both employee and employer. Businesses don’t have to pay for office space or the associated overhead costs. This allows them to save money and focus on the future success of their business. Employees also save money on commuting and can live in more affordable areas outside of the city.
Why is remote access important?
Remote access also ensures that a company can hire whoever they want without the need for relocation. They can work with the best in the industry, no matter where they live, cutting out geographical restraints for both employees and employers. Another benefit is the easy availability of technical support.
What is remote access protocol?
A remote access protocol is responsible for managing the connection between a remote access server and a remote computer. It’s necessary for desktop sharing and remote access for help desk activities. The primary remote access protocols in use today are the Serial Line Internet Protocol (SLIP), Point-to-Point Protocol (PPP), ...
What is managed services provider?
As a managed services provider (MSP), you likely already work with remote access protocols on a daily basis. But learning how to best explain the various types of remote access protocols and their advantages and disadvantages to customers is critical in helping them understand your decisions—and why they should trust you and your services.
Can you use a RAS modem on a Windows server?
With a RAS setup, you can connect a modem to a Windows 2000 or Windows NT server and configure the modem as dial-out only, dial-up only, or a combination of the two. RAS can only provide LAN access to remote users. It doesn’t let LAN users use the modem to, for example, dial their AOL account.
Is RDP the same as ICA?
RDP offers the same core functions as ICA, although there are some limitations. RDP provides remote access for Windows clients only, while ICA can provide access for numerous platforms. ICA also offers support for automatic client updates, publishing an app to a web browser, and more.
What is remote access?
In fact, Remote access is simply the ability to access a computer or network, at home or in an office, from a remote location. Remote access connection allows users to access a network or computer remotely via an internet connection or telecommunications. This post is dedicated to secure remote access.
What is remote assistant?
The remote assistant can be considered a subset of the remote desktop. When you connect to another computer using the remote desktop, the current user of that computer is forced to sign-out. In other words, if an employee asks you for help with a problem and you use a remote desktop to connect to his computer, it is not possible for both of you to be able to view the desktop at the same time and do the necessary work. In terms of technical support, this is a huge problem. To solve this problem, remote assistant technology was introduced. In remote assistant, technical support person and an employee with a problem are able to connect to a computer at the same time.
What is remote desktop connection?
Remote Desktop Connection (RDC) is a Microsoft technology that allows a local computer to connect to and control a remote PC over a network or the Internet. The host computer can see and interact with the target computer through the target computer’s actual desktop interface—allowing the host user to see exactly what the target user sees. It is done through a Remote Desktop Service (RDS) or a terminal service. Microsoft Windows, Linux, and MacOS have the software available that allows for remote desktop access.
What is the easiest program to use for remote access?
AeroAdmin is probably the easiest program to use for free remote access. There are hardly any settings, and everything is quick and to the point, which is perfect for spontaneous support.
How to access remote computer?
There are a couple of ways to access the remote computer. If you logged in to your account in the host program, then you have permanent access which means you can visit the link below to log in to the same account in a web browser to access the other computer.
How to connect to a host browser?
To connect to the host browser, sign on to Chrome Remote Desktop through another web browser using the same Google credentials or using a temporary access code generated by the host computer.
How to enable remote desktop access to a computer?
To enable connections to a computer with Windows Remote Desktop, you must open the System Properties settings (accessible via Settings (W11) or Control Panel) and allow remote connections via a particular Windows user.
How does remote utility work?
It works by pairing two remote computers together with an Internet ID. Control a total of 10 computers with Remote Utilities.
What is the other program in a host?
The other program, called Viewer, is installed for the client to connect to the host. Once the host computer has produced an ID, the client should enter it from the Connect by ID option in the Connection menu to establish a remote connection to the other computer.
What is the name of the program that allows you to access a Windows computer without installing anything?
Install a portion of Remote Utilities called Host on a Windows computer to gain permanent access to it. Or o just run Agent, which provides spontaneous support without installing anything—it can even be launched from a flash drive.
What are remote hackers?
With the rise of a remote working population, “remote hackers” have been re-emerging as well. These remote hackers take advantage of remote working technologies like video conferencing tools, enterprise VPNs, and other remote access solutions that have become popular during the COVID-19 crisis.
How do remote hackers reach unsuspecting victims?
Remote hackers use various malware deployment methods; the most common (and probably the easiest) way for hackers to reach unsuspecting victims is through phishing campaigns.