Five Remote Access Security Risks And How To Protect Against Them
- Weak remote access policies. Once attackers get access to a virtual private network (VPN), they can often penetrate...
- A deluge of new devices to protect. Global “stay at home” policies have forced many organizations to purchase and...
- Lack of visibility into remote user activity. With the sudden...
- Lack of information. ...
- Password sharing. ...
- Software. ...
- Personal devices. ...
- Patching. ...
- Vulnerable backups. ...
- Device hygiene. ...
- Phishing attacks.
What are the risks of a VPN attack?
1. Weak remote access policies Once attackers get access to a virtual private network (VPN), they can often penetrate the rest of the network like a hot knife through butter. Historically, many companies deployed VPNs primarily for technical people needing access to critical technology assets.
What are the risks of remote access security?
Many remote access security risks abound, but below is a list of the ones that jump out. 1. Lack of information The first risk is a lack of information about traditional network security technologies, such as firewalls and intrusion prevention systems, as those systems may be largely out of the equation now.
Is your VPN secure enough to protect you from remote access attacks?
Even if your VPN is secure, the infected machine can grant the hacker access to your private network. So how do you prevent and solve these remote access risks? By implementing the following solutions. Choosing a firewall that matches the size, scope, and scale of your organization is an essential first step in mitigating remote access risks.
Should you use a VPN when working remotely?
Of course, it is not just employees working remotely who could endanger the security of corporate data and networks. Third parties, such as vendors, contractors, and suppliers, could pose risks by accessing corporate resources in an insecure manner. A VPN is just one way to reduce security risks from third parties.

Is remote access VPN secure?
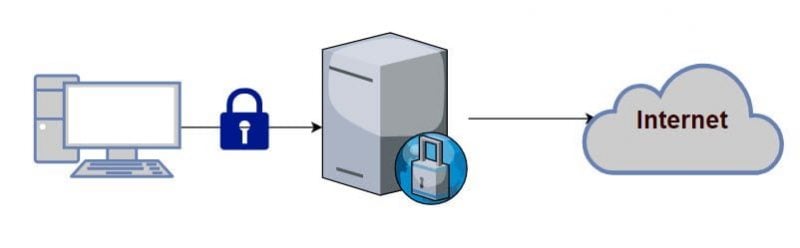
A remote access VPN works by creating a virtual tunnel between an employee's device and the company's network. This tunnel goes through the public internet but the data sent back and forth through it is protected by encryption and security protocols to help keep it private and secure.
What are the dangers of using a VPN?
Why VPN is Not Secure. VPNs are insecure because they expose entire networks to threats like malware, DDoS attacks, and spoofing attacks. Once an attacker has breached the network through a compromised device, the entire network can be brought down.
What are the security risks of remote working?
Top Security Risks of Remote WorkingGDPR and remote working. Remote work means an employer has less control and visibility over employees' data security. ... Phishing Emails. ... Weak Passwords. ... Unsecured Home Devices. ... Unencrypted File Sharing. ... Open Home WiFi Networks.
Is IT safe to allow remote access?
Remote access solutions could leave you vulnerable. If you don't have proper security solutions in place, remote connections could act as a gateway for cybercriminals to access your devices and data. Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular.
Should I leave VPN on all the time?
VPNs offer the best online security, so you should leave your VPN on at all times to protect yourself against data leaks and cyberattacks, while you're using public W-Fi, and against intrusive snoopers such as ISPs or advertisers. So always keep your VPN on. Always use a VPN when you go online.
How can I securely work remotely?
Here are the top remote working security tips to ensure you and your staff are working from home safely.Use antivirus and internet security software at home. ... Keep family members away from work devices. ... Invest in a sliding webcam cover. ... Use a VPN. ... Use a centralized storage solution. ... Secure your home Wi-Fi.More items...
What is the greatest risk that remote access poses to an organization?
The overriding risk of remote access services and software is a hacker gaining deeper access to your organization, exposing you to a host of IT security threats. Once they gain privileged access to your system, it will be difficult to prevent data loss, prevent phishing, protect against ransomware, etc.
Is IT safe and secure for employees to work remotely?
It's not only vital that any device that remote employees use to access company or customer data be equipped with network security systems, such as firewalls, antivirus software, and spam filtering tools, but also that those systems be kept up to date.
Can someone remotely access my computer when IT's off?
Without appropriate security software installed, such as anti-malware tools like Auslogics Anti-Malware, it is possible for hackers to access the computer remotely even if it is turned off.
Can someone remotely access my computer without my knowledge?
"Can someone access my computer remotely without me knowing?" The answer is "Yes!". This could happen when you are connected to the internet on your device.
What happens if you give someone remote access to your computer?
This can be even worse than just conning you out of money, as undetected malware can allow hackers to steal your identity, including your passwords and financial information, over and over again, even if you get new passwords and account numbers.
Can VPN expose bank account?
When you use a VPN, you'll: Stay safe on public WiFi — Unsecured public WiFi networks (like when you're out at the mall or at work) are vulnerable to cyber-attacks. VPNs mask your banking login, password, and any other information you type into your bank's website or app so that hackers can't see or steal your details.
How can you tell if someone is using VPN?
A packet capture that shows a computer sending 100% of its traffic to a single IP is a good indicator that a VPN or proxy is in use. Psiphon is an internet censorship circumvention tool.
Should you use a VPN on your phone?
Should I Run a VPN on My iPhone or Android Smartphone? Yes, You Should! A VPN (virtual private network) is a service that provides a secure Internet connection by using private servers in remote locations. All data traveling between your computer, smartphone or tablet and the VPN server is securely encrypted.
What is the overriding risk of remote access services and software?
The overriding risk of remote access services and software is a hacker gaining deeper access to your organization, exposing you to a host of IT security threats.
How to mitigate remote access risks?
Choosing a firewall that matches the size, scope, and scale of your organization is an essential first step in mitigating remote access risks. Make sure your firewall has built-in antivirus and anti-malware software and high availability programs.
What is Remote Access?
Remote access is simply the ability to access a computer or network, at home or in an office, from a remote location.
What is VPN for business?
Set up a VPN. A VPN is a critical tool to use to securely access sensitive data remotely. There are many kinds of VPNs you should know about and consider using for your company. If you use a business-grade firewall, it will usually have a built-in VPN.
What is shadow IT risk?
On top of that, be aware of employees downloading or installing any information or software without your permission – also known as shadow IT risks.
Can antivirus stop hackers?
Most consumer-ready antivirus products won’t stop sophisticated hackers targeting your organization – which is what most home computers are running.
Is it safe to work remotely?
If any of your employees are working remotely, you’re in danger. But it’s easy to ignore remote access risks when the benefits are so appealing: Your employees may be more productive in their own home without everyday distractions in the office (unnecessary meetings, work gossip, hearing other employees on calls, etc.)
What happens if a VPN fails?
For enterprises that support a large remote workforce connecting via VPN, there is high risk of business interruption if a VPN fails or is incapacitated, such as through a DoS attack. No appliance means no access for anyone who would connect to it.
What are some alternatives to VPN?
One prominent alternative is Secure Access Service Edge (SASE) platforms with embedded Zero Trust Network Access (ZTNA) that alleviate the security dangers and other disadvantages of VPN.
Is VPN good for remote access?
A Better Long-term Solution for Secure Remote Access. VPNs are no longer the only (or best) choice for enterprise remote access. Gartner’s Market Guide for Zero Trust Network Access (ZTNA) projected that by 2023, 60% of enterprises will phase out VPN and use ZTNA instead.
Can the Internet and corporate network be accessed at the same time?
The Internet and corporate network can be accessed at the same time. This provides an opportunity for attackers on the shared public network to compromise the remote computer and use it to gain network access to the internal network.
Can malware be spread through an insecure endpoint?
Insecure endpoints can spread malware to the network –. There is no scrutiny of the security post ure of the connecting device, which could allow malware to enter the network.
Do VPNs provide authentication?
VPNs do provide simple user authentication, but stronger authentication of users and their devices is essential. Without extra authentication safeguards – for example, multi-factor authentication, or verification against an enterprise directory system or a RADIUS authentication server – an attacker can use stolen credentials and gain broad access to the network.
Do VPNs give granular access to specific resources?
VPNs do not provide granular user access to specific resources. When working remotely via VPN, users access the network via a common pool of VPN-assigned IP addresses. This leads to users being able to “see” unauthorized resources on the network, putting them only a password away from being able to access them.
Why do hackers use VPNs?
Hackers often use VPNs to gain access to networks. If your business has many third-party vendors, and each vendor has full access to your network, a hacker now has multiple potential routes to break into and exploit your network using VPN traffic.
Why does VPN speed decrease?
While using VPN software increases security over an unencrypted connection, connection speeds and application performance can decrease due to several factors – such as the time needed to provision and test the VPN, which usually involves other departments such as IT support.
What is VPN for employees?
A Virtual Private Network (VPN) is perfect for internal employees who need to access the server (or section of the server) from anywhere besides the office. In fact, at SecureLink we use VPN client software on our laptops to do just that; if you need to work remotely and need to update something that’s on the server, just use your VPN and you can easily get it done. Generally, this type of network offers high-speed connections that help companies operate efficiently. In addition to allowing employees to work from home or on the road, VPN connections can also give vendors access to internal resources they need in order to support company operations.
What is SecureLink remote access?
With SecureLink, third-party remote access is given not to your entire network, but only specific areas, based on the (much safer) principle of least privilege: vendors can access only the resources they require to get their job done.
How can a hacker access a network?
Let’s face the facts: One of the easiest ways a hacker enters a network is through a third-party connection. Using a checklist to assess VPN risks and the vulnerability of your third parties’ remote access points can help reduce the probability of an attack.
What does P mean in VPN?
If your third-party vendors and VPN users have access to your network, you may believe that your company data and network are safe; after all, the “P” in VPN does stand for “private ”. However, history has proven otherwise.
When do businesses use VPNs?
When a business uses VPNs to provide third-party vendors access to their network, those vendors either have full access to your network (for example, at the start of a job) or they don’t (when you revoke access after the job ends) – unless companies implement strict network segmentation with firewalls and switches, which adds additional complexity.
How to improve VPN security?
Another way to improve VPN security is through perfect forward secrecy (PFS). If PFS is used, encrypted communications and sessions recorded in the past cannot be retrieved and decrypted should long-term secret keys or passwords be compromised.
Why are VPNs important?
VPNs were developed to solve two challenges: the high cost of leased lines for branch offices, and the growing need to enable remote workers to access the corporate network securely. While VPNs provide security by encrypting data and sending it through a “tunnel,” there are limitations to that security.
How does a VPN work?
A VPN involves the transfer of encrypted data wrapped with a header containing routing information. This process enables the data to travel securely over a shared or public network to reach its endpoint.
What are the different types of VPNs?
There are basically four types of VPNs: 1 A firewall-based VPN is equipped with both a firewall and VPN capabilities. This type uses the security provided by firewalls to restrict access to an internal network and provides address translation, user authentication, alarms and logging. 2 A hardware-based VPN provides high network throughput as well as improved performance and reliability, but is also expensive. 3 A software-based VPN provides flexibility in terms of how traffic is managed. This is best for when endpoints are not controlled by the same party and when different firewalls and routers are used. 4 A secure socket layer (SSL) VPN enables users to connect to VPN devices using a web browser. SSL is used to encrypt traffic between the web browser and the VPN device.
Which VPN protocol is best?
Which VPN protocol is best depends on the enterprise and the individual. For those looking for the most secure, OpenVPN is the best. For those looking for support for many devices, PPTP may be the way to go.
What is VPN connection?
From the user’s perspective, the VPN connection is a point-to-point connection between the user’s computer and a corporate server. The nature of the public network is irrelevant to the user because it appears as if the data is being sent over a dedicated private link. As workers become more mobile, VPN connections allow users working at home ...
Which is the most secure VPN?
So how do you choose the most secure VPN? Even though it is open source-based , many view OpenVPN as the most secure VPN protocol. It is stable and reliable, easily configured to run on any port, supports hardware acceleration for improved speeds, is able to traverse firewalls and network address translation (NAT), and uses OpenSSL libraries for encryption. However, it requires client software and cannot be used on iPhones and only on a limited number of Android phones.
What are the risks of using a VPN?
Here are five top security risks that teams must deal with, as well as technology and user education best practices to keep users and data safe: 1. Weak remote access policies. Once attackers get access to a virtual private network (VPN), they can often penetrate the rest of the network like a hot knife through butter.
Why do companies use VPNs?
Historically, many companies deployed VPNs primarily for technical people needing access to critical technology assets. Not so much the case anymore – VPNs are often encouraged for all users as a more secure connection than home or public networks.
What should security teams do if on-premises network and email security mechanisms are no longer available?
Recommendation: If some on-premises network and email security mechanisms are no longer available, security teams should double down on educating users to identify phishing attempts and to choose strong, unique passwords, encouraging the use of a password manager. They should also implement client certificates and multi-factor authentication in order to prevent attackers from gaining access through unsecured devices.
Why is it important to enforce access based on user identity?
Recommendation: It’s critical that companies enforce access based on user identity, allowing specific groups access to only what they need to get their jobs done, and expanding access from there on an as-needed basis.
Why is logging a VPN bad?
Why? Because logging is a gray area where your privacy no longer exists, depending on what gets recorded and how long such data is stored.
Why does global surveillance fail?
Global surveillance fails when the VPN provider can’t share usable logs.
Can a VPN leak change everything?
Well, even if the previous three VPN security risks are not present, leaks can change everything in a second. No matter how good, powerful, and secure protocols a VPN offers, a leak can expose you right away.
Where is NordVPN based?
Some premium services choose a privacy-friendly country as their base to avoid strict data retention laws; for example, NordVPN is based in Panama.
Is VPN safe for free?
Obviously, certain VPN security risks are more common in the case of free VPNs, while some may not even relate to paid VPNs. Let’s see how a VPN that should protect your anonymity may do just the opposite and risk your virtual as well as your physical security.
Is VPN a security risk?
Of course, some consider the third VPN security risk as arguable. We’re sure there are people who wouldn’t consider a VPN provider from a Five Eyes country like the US or Canada as a serious security risk.
Is NordVPN safe?
If you’re in the market for a risk-free VPN, NordVPN is the safest possible provider that can secure your connection right now.
What is the first risk in network security?
The first risk is a lack of information about traditional network security technologies, such as firewalls and intrusion prevention systems, as those systems may be largely out of the equation now.
What is the essence of an organization's network security challenge?
The essence of an organization's network security challenge is users are now, more than ever, making security decisions on the network team's behalf. Teams should think about what they can do to minimize such decisions or at least minimize their effect on the business. Consider the following methods.
Is there a tangible risk to security?
Unless and until technical staff, employees and management are working toward the same goals in terms of security standards, policies and expectations, there will be tangible risks. Most people have already established their baseline in this new normal. However, from what I'm seeing and hearing from clients and colleagues, there are still lots of opportunities to properly mitigate certain threats and vulnerabilities.
Is it time to do more of the same with network security?
Now is not the time to do more of the same with network security. Instead, you've got to figure out how to get your users working for you rather than against you. The same boring messages and dictates are not going to work. You'll have to get creative as you address remote access security.
Why is cybersecurity important in remote work?
Bringing cybersecurity to the top-of-mind for your remote workforce is important in successfully educating employees on the new risks their work environment presents. Conducting training for security best practices, as well as discussing your organization’s cybersecurity standing and vulnerabilities with the entire workforce are both potential ways to combat network threats.
What is the first step in mitigating risk throughout your attack surface?
Documenting policies, protocols, and authorized software is the first step in mitigating risk throughout your attack surface. From there, you can start to enforce changes that will improve security performance across your expanding digital ecosystem. 2. Unsecured networks.
How to prevent unauthorized app use?
Making proactive decisions about your tech stack can go a long way toward preventing unauthorized app use. For example, by making a secure video chatting or collaboration tool available, you reduce the likelihood of employees going out of their way to install their own (less secure) solutions.
What should be protected using multi-factor authentication?
Any machine that is capable of connecting to your network should be protected using multi-factor authentication, automatic session timeouts, and access monitoring to prevent unauthorized users from getting into the data, even if they have the device.
Is IT security playing catch up?
IT security teams are still playing catchup when it comes to securing the remote workforce. We’re committed to making their jobs easier through our BitSight Security Ratings solutions for monitoring, managing, and mitigating cyber risks. Read our research to learn more about the unique risks of work from home-remote office networks and what to do next to mitigate the latest security threats.
Is social engineering easier than phishing?
Social engineering has a new dimension now that employees aren’t in the same physical space. It’s much easier to impersonate a colleague when they’re not sitting next to you, and in the current stressful environment some emotionally driven phishing emails are working better now than ever before.
Can remote workers access sensitive information?
But with remote work and the physical locations of your workforce and sensitive information further apart, the chances of unauthorized users accessing sensitive data through employees’ computers, phones, and tablets increases exponentially .
