
Why choose the right secure remote access protocol for your business?
That’s why choosing the right secure remote access protocol is crucial when you’re planning to add remote access technology to your business. While a Virtual Private Network or VPN is one of the most sought-after remote access solutions at the moment, it can still pose a few security risks for your organization.
Is your remote access solution secure?
While a Virtual Private Network or VPN is one of the most sought-after remote access solutions at the moment, it can still pose a few security risks for your organization. A VPN Access can still be exposed to a bunch of security threats outside of a company’s network.
What are the different types of remote access services?
Some of the most prominent include the following: Virtual private network (VPN) – The most common and well-known form of secure remote access, VPNs typically use the public Internet to connect to a private network resource through an encrypted tunnel.
How to protect your network from remote access?
So, you have a three-layer line of defense working to protect remote access to your network: anti-virus, firewall, and VPN. The network security team should monitor alerts from these defenses constantly. Adopting two-factor authentication for remote access through VPN further boosts your network security.
Which protocol is secure for remote access?
Remote Desktop Protocol (RDP)Remote Desktop Protocol (RDP) is a Microsoft proprietary protocol that enables remote connections to other computers, typically over TCP port 3389. It provides network access for a remote user over an encrypted channel.
How do you secure remote access in networking?
Use virtual private networks (VPN) - Many remote users will want to connect from insecure Wi-Fi or other untrusted network connections. VPNs can eliminate that risk, however VPN endpoint software must also be kept up-to-date to avoid vulnerabilities that can occur from older versions of the software client.
Which is a more secure form of remote access over a network?
Virtual private network (VPN)Virtual private network (VPN) – The most common and well-known form of secure remote access, VPNs typically use the public Internet to connect to a private network resource through an encrypted tunnel.
What is remote access network?
Remote access is the act of connecting to IT services, applications, or data from a location other than headquarters. This connection allows users to access a network or computer remotely via the internet.
What is remote access protocol?
A remote access protocol is responsible for managing the connection between a remote access server and a remote computer. It’s necessary for desktop sharing and remote access for help desk activities. The primary remote access protocols in use today are the Serial Line Internet Protocol (SLIP), Point-to-Point Protocol (PPP), ...
What is PPP protocol?
PPP is a remote access protocol that allows you to implement TCP/IP. It establishes a connection via point-to-point links (i.e., dedicated leased lines and dial-up). PPP is used most often for remote connections to LANs and ISPs. PPP utilizes the Link Control Protocol (LCP), which tests the link between client and PPP host ...
How to use PPTP?
To use PPTP, you’ll have to set up a PPP session between the server and the client, usually over the internet. Once the session is established, you’ll create a second dial-up session. This dial-up session will use PPTP to dial through the existing PPP session.
What is LCP in PPP?
PPP utilizes the Link Control Protocol (LCP), which tests the link between client and PPP host and specifies PPP client configuration, to communicate between host and PPP client. LCP allows PPP to support authentication negotiation, in addition to compression and encryption negotiation between the client and the server, using encryption control protocols (ECPs) and compression control protocols (CCPs). PPP can support multiple network protocols by using protocol-specific network control protocols (NPCs). Because it can run over numerous physical media types and features error-checking functionalities, PPP has almost entirely replaced SLIP.
What is PPTP in a network?
PPTP is a remote access protocol, based on PPP, created by Microsoft. It’s used to establish virtual connections across the internet via PPP and TCP/IP, enabling two networks to use the internet as their WAN link while retaining the security benefits of a private network.
What is take control?
Take Control was created to suit your technicians’ workflows and designed to let you hit the ground running. No training or experience is required, making the process of providing remote support less of a headache. You also have the option of configuring the tool to suit your needs—you can even adopt personalized branding, which helps your customers keep your business top-of-mind.
What is managed services provider?
As a managed services provider (MSP), you likely already work with remote access protocols on a daily basis. But learning how to best explain the various types of remote access protocols and their advantages and disadvantages to customers is critical in helping them understand your decisions—and why they should trust you and your services.
What is secure remote access?
Secure remote access refers to any security policy, solution, strategy or process that exists to prevent unauthorized access to your network, its resources, or any confidential or sensitive data. Essentially, secure remote access is a mix of security strategies and not necessarily one specific technology like a VPN.
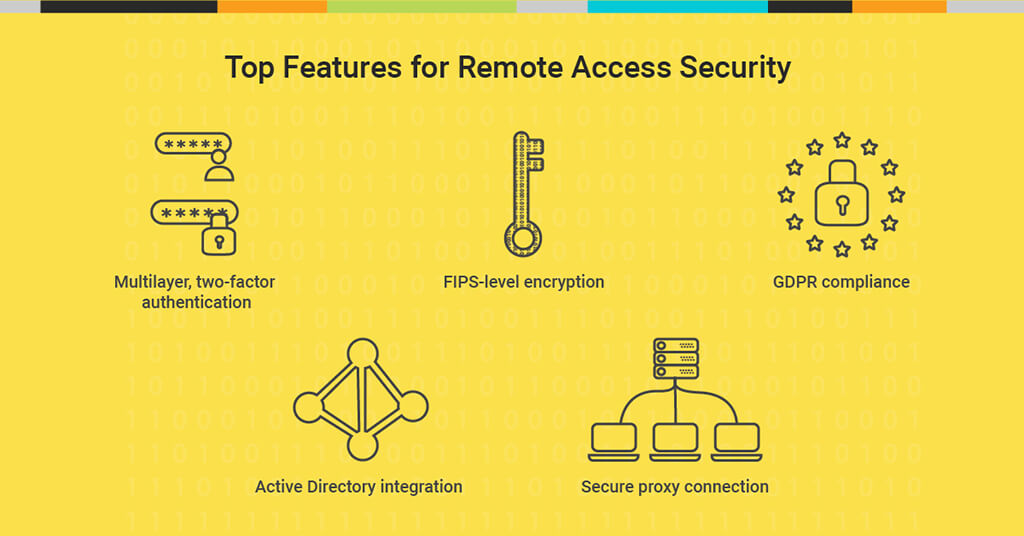
What technologies are used for secure remote access?
Secure remote access is comprised of a multitude of security solutions and technologies. Some of the most prominent include the following:
Secure remote access solution
Enables employees with precise access to the applications and data required to do their job from anywhere.
Why is secure remote access important?
With the work from home shift in the workforce, endpoints are accessing corporate networks from multiple locations. Today, employees’ home networks are often the originating point for network connections, multiplying the risk on both home and corporate networks.
What are the benefits of secure remote access?
While the benefits of secure remote access are numerous, there are four key advantages in which to focus on:
Can secure remote access be achieved without VPN?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
How can AT&T help organizations with secure remote access?
AT&T Cybersecurity is uniquely positioned to help organizations address these immediate challenges with an eye toward the future by helping them balance connectivity, collaboration, and cybersecurity affordably.
What is RDS gateway?
Similar to the recommendation above regarding using SSL/TLS to secure the connection to a remote server, a Remote Desktop Services (RDS) gateway allows for a similar method to be used via a standard online portal. This provides a central access location that users can RDP from to a large number of target servers, as well as the use of remote apps. In addition to permitting access in a secure manner, this also allows for logging of legitimate users as well as potential brute-force attack attempts.
What is the best way to make sure RDP is working?
The first and most effective recommendation is to make sure that both your local workstation and destination server are current on their Windows updates. There have been a considerable number of vulnerabilities discovered over the years in regard to RDP, and these have been addressed regularly through Windows updates.
What is a VPN connection?
If you need more than just RDP access or require more than what just one RDS gateway will allow, then a Virtual Private Network (VPN) connection may be just what you require. These access methods are highly secure and allow for any supported device to communicate as if it were directly attached to your network.
What is the default port for RDP?
The default port for RDP traffic is TCP 3389, and anyone scanning the network deliberately for this port will be able to quickly find any number of servers listening. Changing this port to something less obvious would be tremendously helpful, but can take a considerable amount of time to initially set up.
Can you connect to a server remotely?
There are dozens of different ways to connect remotely to server s, but the recommended method for quite some time has been through the use of remote desktop connections. Unfortunately, while the use of the Remote Desktop Protocol (RDP) is relatively well protected over short distances, it can be vulnerable to attacks if left unsecured on the web. Worse, it’s become an even more lucrative target to exploit with the recent increases in working from home.
Is RDP secure?
In addition, we want to make sure that our RDP sessions are using secure protocols to communicate to and from the servers. This is because while the RDP channel itself is encrypted, it is possible in older versions of RDP to leverage a vulnerability in order to allow unauthorized access via a man-in-the-middle attack. Therefore it is strongly recommended wherever possible to secure your connections via SSL/TLS.
Is it safe to leave your network exposed?
While it is certainly possible to leave your systems directly exposed on the internet and RDP in directly with no security at all, this is a very bad idea. Fortunately there are two very well-used and secure methods that can help to not only keep your network more secure but to log who is attempting to breach it.
How can my staff work from home and access the company network?
In general, VPN solutions provide user experiences that are very close (sometimes the same) as the worker is used to in their office, which means they can be just as productive at home, use all the same apps with the same file access, and require no specialized training.
What types of VPN are there?
There are two main types of VPN technology in use: IPsec and SSL/TLS. We’ll look at both types here from the viewpoint of your organization’s priorities.
Types of Tunneling and Encryption
Tunneling involves using protocols to encapsulate or encrypt data packets so that will pass through the Internet in a secure fashion. Think of encapsulation and tunneling like peas in a pod. The peas are the data packets (unencrypted) and the pod encapsulates or encrypts the peas so they cannot be seen.
Remote Access
Here is a high level example (Figure 1) of how a remote host can connect to an internal corporate network which can be referred to when reviewing the types of remote access solutions: Remote Access Service (RAS), Point-to-Point over Ethernet (PPPoE), Remote Desktop Protocol (RDP), Independent Computing Architecture (ICA), and Secure Shell (SSH).
Network Intrusion & Protection
An Intrusion Detection System (IDS) and Intrusion Prevention System (IPS) are network security appliances that can be host-based, network-based or a combination of both.
Network Security Traps
A honeypot is a computer host that has been set up to attract hackers to learn what tactics they are using to infiltrate a network. It monitors their movements and gives a network administrator insight to where future attacks may come from.
How to secure RDP?
Ananth: There are some built-in, no-cost defenses that can secure RDP. These include: 1 Patching: Keep servers especially up to date. 2 Complex passwords: Also use two-factor authentication, and implement lockout policies. 3 Default port: Change the default port used by RDP from 3389 to something else via the Registry. 4 Windows firewall: Use the built-in Windows firewall to restrict RDP sessions by IP address. 5 Network Level Authentication (NLA): Enable NLA, which is non-default on older versions. 6 Limit RDP access: Limit RDP access to a specific user group. Don't allow any domain admin to access RDP. 7 Tunnel RDP access: Tunnel access via IPSec or Secure Shell (SSH).
What firewall is used to restrict RDP sessions?
Windows firewall: Use the built-in Windows firewall to restrict RDP sessions by IP address.
What is the RDP vulnerability?
Most notably, 2019 gave rise to a vulnerability known as BlueKeep that could allow cybercriminals to remotely take over a connected PC that's not properly patched.
What is RDP brute forcing?
Ananth: One common tactic is RDP brute-forcing, where attackers automate many login attempts using common credentials, hoping one hits. The second involves exploiting a software vulnerability to gain control of an RDP server. For instance, attackers could exploit BlueKeep ( CVE-2019-0708) to gain complete control of a managed service provider's (MSP) unpatched RDP servers.
What is the first step in an attack chain that would likely be used to attack internal data stores and directory services?
Gamblin: Finding and exploiting an RDP vulnerability will be the first step in an attack chain that would likely be used to attack internal data stores and directory services to pivot to either a financial motive, or the ability to disrupt operations.
What are some built-in, no-cost defenses that can secure RDP?
Ananth: There are some built-in, no-cost defenses that can secure RDP. These include: Patching: Keep servers especially up to date. Complex passwords: Also use two-factor authentication, and implement lockout policies. Default port: Change the default port used by RDP from 3389 to something else via the Registry.
How many systems are exposed to the internet via RDP?
Web crawlers like shodan.io make it easy for attackers to quickly identify vulnerable public-facing machines. Worldwide, more than two million systems are exposed to the internet via RDP, of which more than 500,000 are in the US.
Why Is Secure Remote Access Important?
Secure remote access is important for three reasons: to safeguard and protect intellectual property; to increase employee productivity, and to enhance an organization’s competitive advantage. Organizations can confidently deliver on their current goals and innovate to achieve new ones when employees can work securely from everywhere.
What is remote desktop access?
Remote desktop access is an older and still popular method for accessing resources, typically on a corporate LAN. In this case, a user will connect to a physical or virtual computing instance located on the LAN. Popular examples include Remote Desktop Protocol (RDP) and Virtual Network Computing (VNC).
What is a web proxy?
Web Proxies. Web proxies are a popular connection method and are often used in conjunction with secure web gateways (SWGs). Proxy servers terminate the connection between the user and the network, and then send a request to the end destination on the user’s behalf.
Why do people use VPNs?
Organizations, governments, and businesses of all sizes use VPNs for secure remote access to data center resources or corporate local area networks (LAN). Personal VPNs have also become widely popular as they keep users’ locations private, ...
Is Google Chrome secure?
Most web browsers, like Google Chrome, provide some level of security for a secure web browsing experience. However, a successful secure remote access strategy provides organizations more control of the web browsing experience, eliminating reliance solely on web browser vendors for a secure web browsing experience.

Serial Line Internet Protocol (Slip)`
Point-To-Point Protocol
- PPP is a remote access protocol that allows you to implement TCP/IP. It establishes a connection via point-to-point links (i.e., dedicated leased lines and dial-up). PPP is used most often for remote connections to LANs and ISPs. PPP utilizes the Link Control Protocol (LCP), which tests the link between client and PPP host and specifies PPP client configuration, to communicate between h…
Point-To-Point Tunneling Protocol
- PPTP is a remote access protocol, based on PPP, created by Microsoft. It’s used to establish virtual connections across the internet via PPP and TCP/IP, enabling two networks to use the internet as their WAN link while retaining the security benefits of a private network. PPTP is a great option because it’s simple and secure. To use PPTP, you’ll ha...
Windows Remote Access Services
- Windows 2000 and Windows NT let users dial up a server and connect to both the server and the server’s host network. This is referred to as RAS, which is used in smaller networks where a dedicated dial-up router would not be possible or practical. With a RAS setup, you can connect a modem to a Windows 2000 or Windows NT server and configure the modem as dial-out only, di…
Remote Desktop Protocol
- Finally, there is the RDP, which is very similar to the Independent Computing Architecture (ICA) protocol used by Citrix products. RDP is utilized to access Windows Terminal Services, which is a close relative of the product line provided by Citrix WinFrame. RDP offers the same core functions as ICA, although there are some limitations. RDP provides remote access for Windows clients o…