SSL VPNs typically require the installation of a third-party VPN client software package, while the Remote Desktop access client is part of Windows XP. If your users are all using XP, and their needs can be met by providing remote access to a workplace desktop, this may simplify administration, compared with rolling out and maintaining an SSL VPN.
What is the difference between IPsec and SSL VPN?
The new hotness in terms of VPN is secure socket layer (SSL). You can use an SSL VPN to securely connect via a remote access tunnel, a layer 7 connection to a specific application. SSL is typically much more versatile than IPsec, but with that versatility comes additional risk.
What is a remote-access VPN?
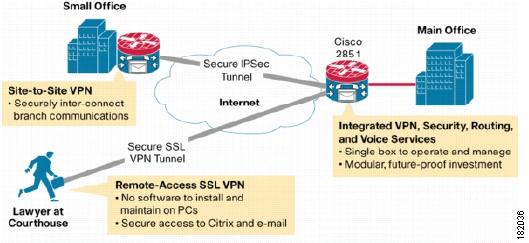
With remote-access VPNs, the device of the remote user is in charge of encrypting and decrypting data that is either sent or received. A remote-access VPN requires a NAS (network access server), or VPN gateway, to authenticate the credentials of any device attempting to sign into the VPN.
What is the difference between RDP and a VPN?
Both RDP and corporate VPN intranets can be used to access resources on a remote network. However, each provides a different level of access. A VPN will allow you to connect to the LAN to use a printer or to access files remotely and download them to your machine.
Do I need an SSL VPN for Remote Desktop Access?
SSL VPNs typically require the installation of a third-party VPN client software package, while the Remote Desktop access client is part of Windows XP. If your users are all using XP, and their needs can be met by providing remote access to a workplace desktop, this may simplify administration, compared with rolling out and maintaining an SSL VPN.
What is SSL VPN remote access?
A secure sockets layer VPN (SSL VPN) enables individual users to access an organization's network, client-server applications, and internal network utilities and directories without the need for specialized software.
Which is better SSL VPN or IPsec VPN?
When it comes to corporate VPNs that provide access to a company network rather than the internet, the general consensus is that IPSec is preferable for site-to-site VPNs, and SSL is better for remote access.
Which type of VPN is more secure?
OpenVPNMany VPN experts recommend OpenVPN as the most secure protocol. It uses 256-bit encryption as a default but also offers other ciphers such as 3DES (triple data encryption standard), Blowfish, CAST-128, and AES (Advanced Encryption Standard).
Is OpenVPN a SSL VPN?
OpenVPN is an SSL VPN and as such is not compatible with IPSec, L2TP, or PPTP. The IPSec protocol is designed to be implemented as a modification to the IP stack in kernel space, and therefore each operating system requires its own independent implementation of IPSec.
Which one is more secure SSL or IPsec?
Once a user is logged into the network, SSL takes the upper hand in security. SSL VPNs work by accessing specific applications whereas IPsec users are treated as full members of the network. It's therefore easier to restrict user access with SSL.
Why would you use IPsec Instead of SSL?
The main difference between IPsec and SSL VPNs is the endpoints for each protocol. While an IPsec VPN allows users to connect remotely to an entire network and all its applications, SSL VPNs give users remote tunneling access to a specific system or application on the network.
What are the primary advantages of IPsec over SSL?
It generally uses cryptographic security services to protect communications. It can be seen that network-level peer and data origin authentication, data integrity, data encryption, and protection are supported by IPsec....Difference between IPSec and SSL:IPSecSSLIPsec is used to secure a Virtual Private Network.SSL is used to secure web transactions.7 more rows•Jul 12, 2022
Which is more secure TLS or IPsec?
If you really need per-user, per-application access control at the gateway, go SSL/TLS. If you need to give trusted user groups homogenous access to entire private network segments or need the highest level of security available with shared secret encryption, go IPsec.
Why use SSL VPN?
One of the benefits of using a VPN with SSL is data privacy and security. Since an SSL VPN uses standard technologies and web browsers, it offers users more secure access to enterprise applications remotely. VPN Unlimited uses SSL/TLS in the KeepSolid Wise that allows users to establish VPN connections even in networks that band VPNs.
What is the difference between SSL and IPsec?
Basically, IPsec doesn’t use TLS for encryption. Another difference between SSL vs IPsec is that the latter does not specify encryption of connections by default, while the former defaults to traffic encryption.
What is IPsec used for?
It is a standard suite of protocols used by IETF (Internet Engineering Task Force). It is used to create a tunnel between two communication points. IPsec takes part in web packet encryption, decryption, and authentication, protecting communications by applying cryptographic security services.
What is SSL tunneling?
Tunneling via SSL uses a client to connect to a backend server.
Why is remote work important?
It’s no wonder - employees that can complete tasks wherever they like it, not just in the office, have been proven to show greater productivity, flexibility, and satisfaction with their jobs. And more and more employers are noticing this, leading to them embracing remote work.
Is SSL better than IPSEC?
Some experts consider SSL to be better for remote access and IPSec to be preferable for site-to-site VPNs. However, corporate VPNs, such as VPN Unlimited for Teams, have to provide access to a company network as well as secure the connection to the internet. To this end, VPN Unlimited uses both SSL/TSL (in KeepSolid Wise to bypass VPN blocking) and IPsec (as part of the IKEv2 protocol). So just use the one that suits your needs at any given moment.
Can you use VPN for remote work?
Still, remote work has certain requirements to be effective. For one, it implies employees accessing their company’s network wherever they work from. To this end, many organizations and individuals use VPNs (Virtual Private Networks) like VPN Unlimited. How do VPNs do it? Using technologies, such as SSL and IPsec. Wait, what was that we just said? Yeah, these can be somewhat puzzling. Take a look at our SSL vs IPsec comparison and figure it out!
How does IPsec work?
IPsec, also known as Internet Protocol Security, defines the official architecture for securing IP network traffic. IPsec specifies ways in which IP hosts can encrypt and authenticate data being sent at the IP network layer. IPsec is used to create a secure tunnel between entities that are identified by their IP addresses.
How does SSL work?
Modern SSL VPNs actually use TLS to encrypt streams of network data being sent between processes. The TLS protocol enables encryption and authentication of connections between programs. These connections are usually defined by the IP addresses of the endpoints, as well as the port numbers of the programs running on those endpoints.
Comparing IPsec vs. SSL VPNs
The choice between an IPsec and SSL VPN should be based on the conditions and requirements of the organization. While there may be philosophical or theoretical preferences for one model or the other, the actual decision should be based on fact-based comparisons of the advantages and disadvantages as they apply to the actual deployment.
How to test your VPN implementations
VPN implementations should be tested with the same degree of thoroughness as any security product. Proper testing should be preceded by research about the VPN implementations being considered. Also like other security systems and services, VPN system testing should never initially be done on production systems or networks.
Authentication and access control
Accepted security best practice is to only allow access that is expressly permitted, denying everything else. This encompasses both authentication, making sure the entity communicating -- be it person, application or device -- is what it claims to be, and access control, mapping an identity to allowable actions and enforcing those limitations.
Defense against attacks
Both SSL/TLS and IPsec support block encryption algorithms, such as Triple DES, which are commonly used in VPNs. SSL/TLS VPNs also support stream encryption algorithms that are often used for web browsing. Given comparable key lengths, block encryption is less vulnerable to traffic analysis than stream encryption.
Client security
Your VPN -- IPsec or SSL/TLS -- is only as secure as the laptops, PCs or mobile devices connected to it. Without precautions, any client device can be used to attack your network.
Client vs. clientless
The primary allure of SSL/TLS VPNs is their use of standard browsers as clients for access to secure systems rather than having to install client software, but there are a number of factors to consider.
Integrating VPN gateways
Server-side issues tend to get lost amid the buzz about clientless savings, but understanding what's involved is essential in VPN product selection, secure system design and cost-effective deployment.
The test of time
Will it always be SSL/TLS VPN vs. IPsec VPN? It's quite likely that IPsec will remain attractive for groups needing the highest degree of security, requiring broader access to IT systems or to rich sets of legacy applications, and, of course, for site-to-site connectivity -- now often under the control of an software-defined WAN rather than a VPN.
What is commercial VPN?
Commercial VPNs are the kind of VPN services that we regularly review at ProPrivacy.com. These kinds of consumer-facing VPNs are completely different to the corporate VPN intranets mentioned above. A commercial VPN is designed to allow its users to gain digital privacy and security online.
Why do companies use VPN?
Companies provide this kind of VPN so that their employees can connect directly to a company IP address provided by the IT department. When the connection to that static IP address is established, the employee can access assets on the local LAN. As a result, they can get hold of files and folders they need to work on from home (or in a hotel, etc).
What is corporate VPN?
When this kind of corporate VPN is used, it directly connects each employee to the company’s network using encryption. This creates a secure tunnel between the remote worker and the company server, so that valuable business assets can be transferred without fear that they might be intercepted using a man-in-the-middle (MITM) attack.
Is a VPN intranet better than a remote desktop?
VPNs and remote desktop tools are both useful in their own right. Which one you need will depend on the level of access to a remote network you require. For many people, a corporate VPN intranet will not be an option because setting one up can be expensive. For those people, RDP will be a better solution.
Is RDP a VPN?
For this reason, many experts recommend using RDP in combination with a commercial VPN. Doing this provides added security and privacy for anybody using a remote desktop tool, by ensuring that the connection to the remote PC is completely encrypted.
Does a VPN hide your IP address?
In addition, this kind of commercial VPN will conceal your IP address from the websites you visit, providing digital privacy by removing the potential for those sites to track you. Depending on the work you do, you may prefer not to have the websites you visit for work tracked by your ISP.
Can a hacker access your data with RDP?
One thing to remember is that when you use RDP, it is possible that the connection it creates contains some potential vulnerabilities. Security researchers agree that with a little persistence a hacker might gain access to your data because of the shoddier RDP connection .
What is a Remote-Access VPN?
Remote-access VPNs are more closely related to the consumer VPNs we use to protect our personal identities and data.
What is a Site-to-Site VPN?
Whereas remote-access VPNs securely connect individual devices to a remote LAN, site-to-site VPNs securely connect two or more LANs in different physical locations. Site-to-site VPNs use the public internet to extend your company’s network across multiple office locations.
What is MPLS VPN?
Unlike internet-based site-to-site site VPNs in which a company uses its own infrastructure, MPLS VPN uses proprietary infrastructure owned by the VPN. This MPLS network, including its cloud, functions as the tunnel by which a company creates virtual connections between office sites.
What is a VPN gateway?
The VPN gateway encrypts the incoming traffic (to you) which is then received by your VPN client. Remote-access VPNs are not just a way for out-of-office employees to remotely access your company’s private network.
How does a VPN gateway work?
The VPN gateway then decrypts your traffic and relays the data to the LAN. Not only is all traffic sent through the virtual tunnel secured, but any traffic you receive from the local network (or its servers) also travels through this tunnel in reverse and is secured.
Why do businesses use VPNs?
VPNs were first used by businesses to extend private networks over the public internet, allowing remote workers to connect to a company’s LAN (local area network).
What is IPSec security?
IPSec secures IP packets one at a time, and in doing so, reliably provides WAN traffic with confidentiality (all bits are encrypted), integrity (no bits were tampered with during transmission), and authentication.
How secure is VPN?
VPN access is protected by a password. It’s essential for users to select strong passwords with combinations of letters and numbers, upper- and lowercase, special characters, and no dictionary words. The most locked-down systems won’t let users choose a weak password. Two-factor authentication (2FA) makes VPNs even more secure. This method requires a one-time code—sent via text message or generated by a mobile app—in addition to the password to log in. Even if a hacker discovers the password, he or she won’t be able to access the VPN without the second code.
What is a VPN for remote work?
For remote work to be effective, employees must have access to their company’s network wherever they travel. A virtual private network (VPN) serves this function. Using a VPN, remote team members can connect directly to the network, performing tasks just as they would while in the office.
Why do VPNs use encryption?
Security is a key factor to consider when implementing remote access. The more outside connections there are to a network, the more opportunities arise for nefarious parties to intercept data being transmitted. That’s why IPsec protocols use encryption. IPsec encryption works by scrambling data in transit so it cannot be deciphered if intercepted. Data can only be read if the user has the correct key to mathematically unscramble it. VPNs also mask a user’s Internet Protocol (IP) address for further security. The VPN assigns a new IP address, hiding the user’s original address and making it harder for an internet service provider to track them.
What is SSL tunnel mode?
This mode can only be used for web-based programs. It’s ideal for email, chat, file sharing, and other browser-based applications. In tunnel mode, by contrast, users can access any applications on the network , ...
How does IPsec work?
IPsec encryption works by scrambling data in transit so it cannot be deciphered if intercepted. Data can only be read if the user has the correct key to mathematically unscramble it. VPNs also mask a user’s Internet Protocol (IP) address for further security.
What is IPsec in a network?
The purpose of IPsec is to give the remote computer direct access to the central network, making it a full member. Remote users have access to any file storage locations, programs, printers, and backups, exactly as if they were in the office. IPsec is therefore a robust system that gives users whatever resources they need, wherever they are located.
Why is SSL better than IPsec?
SSL gives users more specific access than IPsec. Rather than becoming a full member of the network, remote team members are granted access to particular applications. This makes it simple to provide different levels of access to different users. Security is maintained by restricting access to only what’s needed.
