- Functions of Remote Access Trojan :. It can be used to monitor the user by using some spyware or other key-logger. It...
- Examples of a Remote Access Trojan Attack :. Remote Access Trojan can be sent as an attachment or link. It will be sent...
- Prevention of the Remote Access Trojan :. The anti-virus should always be updated. The user should not download from any...
How to create remote access trojan?
Remote Access Trojan Examples
- Back Orifice. Back Orifice (BO) rootkit is one of the best-known examples of a RAT. ...
- Sakula. Sakula, also known as Sakurel and VIPER, is another remote access trojan that first surfaced in November 2012.
- Sub7. Sub7, also known as SubSeven or Sub7Server, is a RAT botnet. ...
- PoisonIvy. ...
- DarkComet. ...
What to do if you get a Trojan?
What to do if You Get a Trojan Virus Tips
- Identify the Trojan. After recognizing a file infected with Trojan horse, it becomes easy to remove. ...
- Disable the function of System restore. If you forget this step, then it will restore the files you delete.
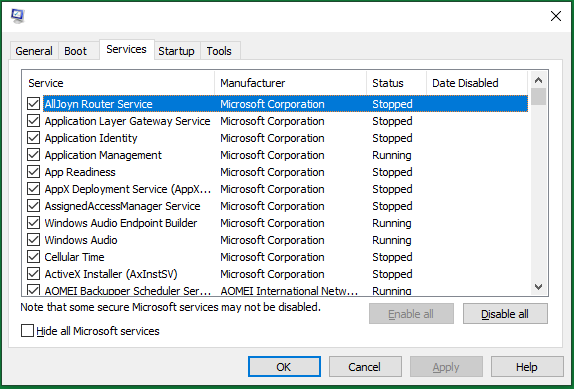
- Restart the Computer. When you restart, press F8 and then select safe mode to start your computer.
- Go to Add or Remove Programs. ...
- Remove extensions. ...
What is remote access and how can I use it?
Windows 10 Fall Creator Update (1709) or later
- On the device you want to connect to, select Start and then click the Settings icon on the left.
- Select the System group followed by the Remote Desktop item.
- Use the slider to enable Remote Desktop.
- It is also recommended to keep the PC awake and discoverable to facilitate connections. ...
How to detect remote access?
What Does a RAT Virus Do?
- Get access to confidential info including usernames, passwords, social security numbers, and credit card accounts.
- Monitor web browsers and other computer apps to get search history, emails, chat logs, etc.
- Hijack the system webcam and record videos.
- Monitor user activity by keystroke loggers or spyware.
- Take screenshots on the target PC.
Is Remote Access Trojan illegal?
Law enforcement officials say that simply possessing a remote-access tool isn't illegal. In fact, remote-access tools are often used for IT support purposes in corporate environments.
How is a Remote Access Trojan executed?
Remote access Trojans are malware programs that use backdoors to control the target machine with administrative privilege. These type of Trojans are downloaded invisibly with a user request for a program such as a game or an email attachment.
What is a Mobile Remote Access Trojan?
A Remote Access Trojan, or RAT, is a type of malware that disguises itself as a file that's either harmless or beneficial to the user—this could be anything from a file to programs and apps. But unlike other types of malware, a RAT doesn't just steal or ruin data and files it was pre-programmed to do.
What is the best Remote Access Trojan?
10 Best Remote Access Software (Remote Control Software) In 2022Comparison of Top Remote Access Tools.#1) NinjaOne (Formerly NinjaRMM)#2) SolarWinds Dameware Remote Support.#3) Atera.#4) Supremo.#5) ManageEngine Remote Access Plus.#6) RemotePC.#7) TeamViewer.More items...•
Is someone using my computer remotely?
Open your Task Manager or Activity Monitor. These utilities can help you determine what is currently running on your computer. Windows – Press Ctrl + Shift + Esc. Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
What are RAT files?
(peshkov) A Remote Access Trojan, otherwise known as a RAT, is a type of spyware that allows a cybercriminal to take control of the computer or other device it's installed on. RATs are malicious software that constitute a major cybersecurity threat.
What is smart RAT switch app?
RAT infected Android devices can be remotely zombified by the perpetrator, allowing virtually unlimited access to photos, data and messages on the device. The Dendroid RAT provides full access to infected devices' camera and microphone, and can place calls or listen in on a user's phone conversations or text messages.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
What does a RAT do to your computer?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
What can NanoCore do?
NanoCore can provide the threat actor with information such as computer name and OS of the affected system. It also opens a backdoor that allows the threat actors to access the webcam and microphone, view the desktop, create internet message windows and offers other options.
Can Remotepc be hacked?
Remote Desktop Protocol (RDP) has been known since 2016 as a way to attack some computers and networks. Malicious cyber actors, hackers, have developed methods of identifying and exploiting vulnerable RDP sessions via the Internet to steal identities, login credentials and install and launch ransomeware attacks.
What is a Remote Access Trojan which is installed by SMS spoofing used for?
Remote Access Trojans are programs that provide the capability to allow covert surveillance or the ability to gain unauthorized access to a victim PC.
How is RAT malware installed?
An attacker must convince the user to install a RAT either by downloading malicious software from the web or running an executable from a malicious email attachment or message. RATs can also be installed using macros in Microsoft Word or Excel documents.
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
What does a RAT do to your computer?
A Remote Access Trojan, otherwise known as a RAT, is a type of spyware that allows a cybercriminal to take control of the computer or other device it's installed on. RATs are malicious software that constitute a major cybersecurity threat.
What is RAT software?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can ac...
What’s the difference between the RAT computer virus and RAT software?
As for functions, there is no difference between the two. Yet, while remote administration tool is for legit usage, RAT connotes malicious and crim...
What are the popular remote access applications?
The common remote desktop tools include but are not limited to TeamViewer, AnyDesk, Chrome Remote Desktop, ConnectWise Control, Splashtop Business...
Remote Access Trojan Definition
Malware developers code their software for a specific purpose, but to gain remote control of a user’s device is the ultimate benefit for an attacker who wants to steal data or take over a user’s computer.
How are Remote Access Trojans Useful to Hackers?
A 2015 incident in Ukraine illustrates the widespread and nefarious nature of RAT programs. Attackers using remote control malware cut power to 80,000 people by remotely accessing a computer authenticated into SCADA (supervisory control and data acquisition) machines that controlled the country’s utility infrastructure.
How Does a Remote Access Trojan Work?
To discover the way RATs work, users can remotely access a device in their home or on a work-related network. RATs work just like standard remote-control software, but a RAT is programmed to stay hidden to avoid detection either from anti-malware software or the device owner.
How to Detect a Remote Access Trojan
Because RATs are programmed to avoid detection, they can be difficult for the average user to identify. Depending on the RAT, users can take several steps to determine if they have a RAT installed on their system. These steps can be used to identify most malware on a system so that eradication steps can be taken to remove it.
What is a RAT trojan?
RAT trojan is typically installed on a computer without its owner’s knowledge and often as a trojan horse or payload. For example, it is usually downloaded invisibly with an email attachment, torrent files, weblinks, or a user-desired program like a game. While targeted attacks by a motivated attacker may deceive desired targets into installing RAT ...
What is a RAT?
A remote access trojan (RAT), also called cree pware, is a kind of malware that controls a system via a remote network connection. It infects the target computer through specially configured communication protocols and enables the attacker to gain unauthorized remote access to the victim. RAT trojan is typically installed on a computer without its ...
What is poison ivy rat keylogger?
PoisonIvy RAT keylogger, also called “Backdoor.Darkmoon”, enables keylogging, screen/ video capturing, system administrating, file transferring, password stealing, and traffic relaying. It was designed by a Chinese hacker around 2005 and has been applied in several prominent attacks including the Nitro attacks on chemical companies and the breach of the RSA SecurID authentication tool, both in 2011.
What does RAT stand for?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can access your system just like he has physical access to your device. So, the user can access your files, use your camera, and even turn off or turn on your machine.
What is the back orifice?
Back Orifice has 2 sequel variants, Back Orifice 2000 released in 1999 and Deep Back Orifice by French Canadian hacking organization QHA. 2. Sakula. Sakula, also known as Sakurel and VIPER, is another remote access trojan that first surfaced in November 2012. It was used in targeted intrusions throughout 2015.
Why do RATs use a randomized filename?
It is kind of difficult. RATs are covert by nature and may make use of a randomized filename or file path structure to try to prevent identification of itself. Commonly, a RAT worm virus does not show up in the lists of running programs or tasks and its actions are similar to those of legal programs.
Can you recover data after a RAT attack?
Luckily, you can still regain your data after malware RAT attacks if you have a backup copy of it. Yet, you have to make the copy before you lost the original files with a reliable and RAT-free tool such as MiniTool ShadowMaker, which is a professional and powerful backup program for Windows computers.
Short bio
Remote Access Trojans are programs that provide the capability to allow covert surveillance or the ability to gain unauthorized access to a victim PC.
History
While the full history of Remote Access Trojans is unknown, these applications have been in use for a number of years to help attackers establish a foothold onto a victim PC. Well-known and long established Remote Access Trojans include the SubSeven, Back Orifice, and Poison-Ivy applications.
Common infection method
Remote Access Trojans can be installed in a number of methods or techniques, and will be similar to other malware infection vectors. Specially crafted email attachments, web-links, download packages, or .torrent files could be used as a mechanism for installation of the software.
Associated families
There are a large number of Remote Access Trojans. Some are more well-known than others. SubSeven, Back Orifice, ProRat, Turkojan, and Poison-Ivy are established programs. Others, such as CyberGate, DarkComet, Optix, Shark, and VorteX Rat have a smaller distribution and utilization.
Remediation
Remote Access Trojans are covert by nature and may utilize a randomized filename/path structure to try to prevent identification of the software.
Aftermath
Remote Access Trojans have the potential to collect vast amounts of information against users of an infected machine. If Remote Access Trojan programs are found on a system, it should be assumed that any personal information (which has been accessed on the infected machine) has been compromised.
Avoidance
As in all cases, never click email or website links from unknown locations or install software at the urging of unknown parties. Using a reputable antivirus and anti-malware solution will help to ensure Remote Access Trojans are unable to properly function, and will assist in mitigating any collection of data.
How Does a Remote Access Trojan Work?
RATS can infect computers like any other type of malware. They might be attached to an email, be hosted on a malicious website, or exploit a vulnerability in an unpatched machine.
The Threat of the RAT
Different attacks require different levels of access to a target system, and the amount of access that an attacker gains determines what they can accomplish during a cyberattack.
How to Protect Against a Remote Access Trojan
RATs are designed to hide themselves on infected machines, providing secret access to an attacker. They often accomplish this by piggybacking malicious functionality on a seemingly legitimate application. For example, a pirated video game or business application may be available for free because it has been modified to include malware.
Prevent RAT Infections with Check Point
Protecting against RAT infections requires solutions that can identify and block malware before it gains access to an organization’s systems.
What is the advantage of remote access?
Advantage of Remote Access Trojans : It can be used to capture screenshots. The attacker can activate the webcam, or they can record video. The RAT can be used to delete the files or alter files in the system. It can also be used to capture screenshots.
What is remote access trojan?
Functions of Remote Access Trojan : It can be used to monitor the user by using some spyware or other key-logger. It can be used to activate the webcam. It can be used to record video. It can be used to delete files, alter files. This Remote Access Trojan can also be used to capture screenshots.
What is the most powerful Trojan?
One of the most powerful Trojans that are popularly used by the attacker or hacker is Remote Access Trojan. This is mostly used for malicious purposes. This Trojan ensures the stealthy way of accumulating data by making itself undetected. Now, these Trojans have the capacity to perform various functions that damages the victim.
Remote Access Trojan Definition
Malware developers code their software for a specific purpose, but to gain remote control of a user’s device is the ultimate benefit for an attacker who wants to steal data or take over a user’s computer.
How are Remote Access Trojans Useful to Hackers?
A 2015 incident in Ukraine illustrates the widespread and nefarious nature of RAT programs. Attackers using remote control malware cut power to 80,000 people by remotely accessing a computer authenticated into SCADA (supervisory control and data acquisition) machines that controlled the country’s utility infrastructure.
How Does a Remote Access Trojan Work?
To discover the way RATs work, users can remotely access a device in their home or on a work-related network. RATs work just like standard remote-control software, but a RAT is programmed to stay hidden to avoid detection either from anti-malware software or the device owner.
How to Detect a Remote Access Trojan
Because RATs are programmed to avoid detection, they can be difficult for the average user to identify. Depending on the RAT, users can take several steps to determine if they have a RAT installed on their system. These steps can be used to identify most malware on a system so that eradication steps can be taken to remove it.
What is a NIDS system?
This is the most efficient option for larger organizations. The intrusion detection system can be either host-based (HIDSs) or network-based (NIDSs). While HIDS is installed on a specific device and monitors log files and application data for signs of malicious activity, NIDS tracks network traffic in real-time seeking suspicious behavior. Used together, the two create a security information and event management system (SIEM), that can help block software intrusions that have slipped past firewalls, antivirus software, and other security solutions.
What is a RAT?
A Remote Access Trojan (RAT) is a type of malware that provides the attacker with full remote control over your system. When a RAT reaches your computer, it allows the hacker to easily access your local files, secure login authorization, and other sensitive information, or use that connection to download viruses you could unintentionally pass on to others.
What percentage of Georgia's internet was affected by the Russian invasion?
Thirty-five percent of Georgia’s Internet networks suffered decreased functionality during the attacks, with the highest levels of online activity coinciding with the Russian invasion of South Ossetia on August 8, 9, and 10. Even the National Bank of Georgia had to suspend all electronic services from August 8–19.
Does Heimdal Antivirus work?
Home and small business networks can often benefit from antivirus software like our Heimdal™ Threat Prevention. If you didn’t know about our product, Heimdal™ Threat Prevention is built to protect its customers from attacks like malware and ransomware traditional antivirus can’t detect. It can block different malware infection sources such as malicious email attachments, infected links you may receive in your email, infected web pages or malicious web apps that appear legitimate at first, but aimed at spreading ransomware. However, please keep in mind that antivirus software will not do much good if you are actively downloading files and installing programs you shouldn’t.
What war did Russia and Georgia fight in 2008?
In this regard, we remember the 2008 war between Russia and Georgia, when Russia used a coordinated campaign of physical and cyber warfare to seize territory from the neighboring Republic of Georgia.
Can remote access Trojans wipe hard drives?
But they don’t stop here. The administrative access Remote Access Trojans provide means cybercriminals can wipe hard drives, download illegal and classified information, or even passing themselves off as somebody else on the Internet. These actions can lead to geopolitical implications.
Is Heimdal RAT good?
RATs are never good news, therefore it is of utmost importance to protect your systems against them. What you should know is that our Heimdal™ Threat Prevention solution is compatible with any antivirus product available on the market that will block threats at their root.
What is botnet hacking?
Essentially, a botnet allows a hacker to utilize your computer resources for super nerdy (and often illegal) tasks, like DDOS attacks, Bitcoin mining, file hosting, and torrenting. Sometimes, this technique is utilized by hacker groups for the sake of cyber crime and cyber warfare.
What is a RAT in cyber security?
Maxim Apryatin/Shutterstock. In most cases, RATs are used like spyware. A money-hungry (or downright creepy) hacker can use a RAT to obtain keystrokes and files from an infected computer. These keystrokes and files could contain bank information, passwords, sensitive photos, or private conversations.
What is a RAT?
A RAT is a type of malware that’s very similar to legitimate remote access programs. The main difference, of course, is that RATs are installed on a computer without a user’s knowledge. Most legitimate remote access programs are made ...
What does remote access do on a PC?
When remote access is enabled, authorized computers and servers can control everything that happens on your PC. They can open documents, download software, and even move the cursor around your screen in real time.
Can a RAT be attached to a file?
Like most malware, RATs piggyback on legitimate-looking files. Hackers can attach a RAT to a document in an email, or within a large software package, like a video game. Advertisements and nefarious webpages can also contain RATs, but most browsers prevent automatic downloads from websites or notify you when a site is unsafe.
Can a hacker use a RAT?
Hackers can also control your computer remotely to perform embarrassing or illegal actions online in your name or use your home network as a proxy server to commit crimes anonymously. A hacker can also use a RAT to take control of a home network and create a botnet.
Is Kaspersky a RAT?
Kaspersky or Malwarebytes have an extensive, ever-expanding database of RATs, so you don’t have to worry about your anti-virus software being out of date or half baked. If you’ve run anti-virus, but you’re still paranoid that there’s a RAT on your PC, then you could always format your computer.